- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
4061 PE courses in Bradford delivered Live Online
CCNP training course description The Implementing and Operating Cisco Enterprise Network Core Technologies (ENCOR) v1.2 course provides the knowledge and skills needed to configure, troubleshoot, and manage enterprise wired and wireless networks. You'll learn to implement security principles within an enterprise network and how to overlay network design using solutions such as SDAccess and SD-WAN. Course content includes 3 days of self-study material. This course helps you prepare for the 350-401 Implementing Cisco Enterprise Network Core Technologies (ENCOR) exam What will you learn Configure, troubleshoot, and manage enterprise wired and wireless networks Implement security principles within an enterprise network Prepare you prepare to take the 350-401 Implementing Cisco Enterprise Network Core Technologies (ENCOR) exam CCNP training course details Who will benefit: Mid-level network engineers, Network administrators, Network support technicians, Help desk technicians. Prerequisites: Implementation of Enterprise LAN networks. Basic understanding of Enterprise routing and wireless connectivity, and Python scripting Duration 5 days CCNP training course content Cisco Enterprise Network Architecture: Access, distribution, core in the hierarchical network. Cisco Switching Paths: Switching mechanisms, TCAM, CAM, process switching, fast switching, and CEF. Implementing Campus LAN Connectivity: Troubleshoot L2 connectivity using VLANs and trunkingBuilding Redundant Switched Topology: STP Implementing Layer 2 Port Aggregation Troubleshoot link aggregation using Etherchannel EIGRP Implement and optimize OSPFv2/v3, including adjacencies, packet types, and areas, summarization, and route filtering for IPv4/v6 Implement EBGP interdomain routing, path selection, and single and dual-homed networkingImplementing Network Redundancy: HSRP and VRRP Implement static and dynamic NAT Virtualization Protocols and TechniquesVPNs and Interfaces: Overlay technologies such as VRF, GRE, VPN, and LISP Wireless Principles: RF, antenna characteristics, and wireless standards.Wireless Deployment: Models available, autonomous AP deployments and cloud-based designs within the centralized Cisco WLC architecture Wireless Roaming and Location ServicesWireless AP Operation: How APs communicate with WLCs to obtain software, configurations, and centralized managementWireless Client Authentication: EAP, WebAuth, and PSK wireless client authentication on a WLC. Troubleshoot wireless client connectivity issues using various available tools Troubleshoot networks using services such as NTP, SNMP, Cisco IP SLAs, NetFlow, and Cisco IOS EEM Explain network analysis and troubleshooting tools, which include show and debug commands, as well as best practices in troubleshootingMulticast Protocols: IGMP v2/v3, PIM DM/SM and RPs Introducing QoS: Concepts and features. Implementing Network Services: Secure administrative access for Cisco IOS devices using CLI access, RBAC, ACL, and SSH, and device hardening concepts to secure devices from less secure applications Using Network Analysis ToolsInfrastructure Security: Scalable administration using AAA and the local database, features and benefits Enterprise Network Security Architecture: VPNs, content security, logging, endpoint security, personal firewalls, and other security features. Automation and Assurance with Cisco DNA Center: Purpose, function, features, and workflow. Intent-Based Networking, for network visibility, proactive monitoring, and application experienceCisco SD-Access Solution: Nodes, fabric control plane, and data plane, VXLAN gatewaysCisco SD-WAN Solution: Components and features of Cisco SD-WAN solutions, including the orchestration, management, control, and data planesBasics of Python Programming: Python components and conditionals with script writing and analysis Network Programmability: NETCONF and RESTCONF APIs in Cisco DNA Center and vManage Labs: Investigate the CAM. Analyze CEF. Troubleshoot VLAN and Trunk Issues. Tuning STP and Configuring RSTP. Configure MSTP. Troubleshoot EtherChannel. Implement Multi-area OSPF. Implement OSPF Tuning. Apply OSPF Optimization. Implement OSPFv3. Configure and Verify Single-Homed EBGP. Implementing HSRP. Configure VRRP. Implement NAT. Configure and Verify VRF. Configure and Verify a GRE Tunnel. Configure Static VTI Point-to-Point Tunnels. Configure Wireless Client Authentication in a Centralized Deployment. Troubleshoot Wireless Client Connectivity Issues. Configure Syslog. Configure and Verify Flexible NetFlow. Configuring Cisco IOS EEM. Troubleshoot Connectivity and Analyze Traffic with Ping, Traceroute, and Debug. Configure and Verify Cisco IP SLAs. Configure Standard and Extended ACLs. Configure Control Plane Policing. Implement Local and Server-Based AAA. Writing and Troubleshooting Python Scripts. Explore JSON Objects and Scripts in Python. Use NETCONF Via SSH. Use RESTCONF with Cisco IOS XE.

Complete Python training course description Python is an agile, robust, expressive, fully objectoriented, extensible, and scalable programming language. It combines the power of compiled languages with the simplicity and rapid development of scripting languages. This course covers Python from the very basics of 'hello world!' through to object oriented programming and advanced topics such as multi threading. Hands on follows all the major sections in order to reinforce the theory. What will you learn Read Python programs. Write Python programs. Debug Python programs. Use Python's objects and memory model as well as its OOP features. Complete Python programming training course details Who will benefit: Anyone wishing to learn Python. Prerequisites: None. Duration 5 days Complete Python programming training course contents Welcome to Python: What is Python? Origins, features. Downloading and installing Python, Python manuals, comparing Python, other implementations. Getting started: Program output, the print statement, "hello world!", Program input, raw_input(), comments, operators, variables and assignment, numbers, strings, lists and tuples, dictionaries, indentation, if statement, while Loop, for loop. range(), list comprehensions. Files, open() and file() built-in functions. Errors and exceptions. Functions, Classes, Modules, useful functions. Python basics: Statements and syntax, variable assignment, identifiers, basic style guidelines, memory management, First Python programs, Related modules/developer tools. Python Objects: Other built-in types, Internal Types, Standard type operators, Standard type built-in functions, Categorizing standard types, Unsupported types. Numbers: Integers, Double precision floating point numbers, Complex numbers, Operators, Built-in and factory functions, Other numeric types. Sequences: strings, lists, and tuples: Sequences, Strings, Strings and operators, String-only operators, Built-in functions, String built-in methods, Special features of strings, Unicode, Summary of string highlights, Lists, Operators, Built-in functions, List type built-in methods, Special features of lists, Tuples, Tuple operators and built-in functions, Tuples special features, Copying Python objects and shallow and deep copies. Mapping and set types: Mapping Type: dictionaries and operators, Mapping type built-in and factory functions, Mapping type built-in methods, Dictionary keys, Set types, Set type operators, Built-in functions, Set type built-in methods. Conditionals and loops: If, else and elif statements, Conditional expressions, while, for, break, continue and pass statements, else statement . . . take two, Iterators and iter(), List comprehensions, Generator expressions. Files and input/output: File objects, File built-in functions [open() and file()], File built-in methods and attributes, Standard files, Command-line arguments, File system, File execution, Persistent storage modules. Errors and exceptions: What are exceptions? Detecting and handling exceptions, Context management, Exceptions as strings, Raising exceptions, Assertions, Standard exceptions, Creating Exceptions, Why exceptions, Exceptions and the sys module. Functions: Calling, creating and passing functions, formal arguments, variable-length arguments, functional programming, Variable scope, recursion, generators. Modules: Modules and files, Namespaces, Importing modules, Module import features, Module built-in functions, Packages, Other features of modules. Object-Oriented Programming (OOP): Classes, Class attributes, Instances, Instance attributes, Binding and method invocation, Static methods and class methods, Composition, Sub-classing and derivation, Inheritance, Built-in functions for classes, and other objects, Customizing classes with special methods, Privacy, Delegation, Advanced features of new-style classes (Python 2.2+), Related modules and documentation. Execution environment: Callable and code Objects, Executable object statements and built-in functions, Executing other programs. 'Restricted' and 'Terminating' execution, operating system interface. Regular expressions: Special symbols and characters, REs and Python, Regular expressions example. Network programming: Sockets: communication endpoints, Network programming in Python, SocketServer module, Twisted framework introduction. Internet client programming: What are internet clients? Transferring files, Network news, E-mail. Multithreaded Programming: Threads and processes Python, threads, and the global interpreter lock, The thread and threading Modules. GUI programming: Tkinter and Python programming, Tkinter Examples, Brief tour of other GUIs. Web programming: Web surfing with Python: creating simple web clients, Advanced Web clients, CGI: helping web servers process client data, Building CGI applications, Using Unicode with CGI, Advanced CGI, Web (HTTP) Servers. Database programming: Python database application programmer's interface (DB-API), ORMs. Miscellaneous Extending Python by writing extensions, Web Services, programming MS Office with Win32 COM, Python and Java programming with Jython.

GPON and FTTx networks training course description Designed to benefit those requiring an in depth knowledge of the principles and applications of Ten Gigabit and Gigabit Passive Optical Networking and Fibre to the X in NG Networks applications and their associated equipment, its flexibility and function within a modern transmission network. Using an effective mix of 'hands on' equipment instruction and correlation to theory based learning the delegate will gain a complete understanding of the equipment and the tasks to be undertaken in a real life situation. What will you learn Compare PON/FTTx systems. Explain network elements and designs. Support applications and network interfaces. List circuit provisioning and bandwidth requirements. Understand upstream & downstream issues. Describe headend & network elements/OLT-ONT. Perform network testing with OTDR test sets. GPON and FTTx networks training course details Who will benefit: Anyone working with GPON and FTTx. Prerequisites: Introduction to data communications and networking. Duration 5 days GPON and FTTx training course contents FTTN, FTTC, FTTH SMF, MMF, Fibre safety and properties (dispersion/attenuation), Fibre reel cables and types, Fibre installation and air blown fibre, Transmitters and receivers - power budget/laser classes. Fibre to the home (FTTH), FTTC (Fibre to the Cabinet), FTTN (Fibre to the node) , FTTD (Fibre to the desk), FFTH topologies and wavelengths, Active or passive optical network. WDM equipment and GPON OSP design Wavelength considerations, WDM/DWDM/CWDM, EDFA optical amplification, AWG (Arrayed Waveguide Grating) splitters , Couplers (splitters) and losses, Optical splitters 1x2, 1x4, 1x8, 1x16, 1x32, 1x64, 2x64. PON variants Gigabit passive optical network (GPON), Gigabit Ethernet passive optical network (GEPON), Time division PON (TDM-PON), Wave Division Multiplexing PON (WDM-PON), 1Gbps, 10Gbps, 40Ggps, 100Gbps FSAN (Full Service Access Network) NGA (Next Generation Access), Strategies for TDM-PON to WDM-PON migration, Architecture of NG-PON (hybrid WDM/TDM PON), Additional services than triple play. GEPON design GPON OSP centralized and distributed design, GPON PON splitters x4 x8 x32, Fibre splice trays /cassette trays & enclosures, GPON field testing and installation verification, GPON physical layer testing, Optical time domain reflectometer (OTDR), Optical power source & meter, Optical return loss (ORL), APON/BPON/GPON/EPON comparisons. GPON ITU-T G.984.1 Reference model, terminology & architecture, Access network system management functions. ONT & OLT functional block examples. FTTx scenarios, 4 switching arrangements for external access network backup. GPON ITU-T G.984.2 Physical layer, Enhancement band, Bit rate and wavelengths, FEC and RAMAN. GPON ITU-T G.984.3 Frame structure, GPON encapsulation method (GEM), GTC adaptation and framing sublayer protocol stack, Status reporting & traffic monitoring DBA (SR-DBA & TM-DBA), Transmission container (T-CONT) types, Downstream & upstream multiplexing, GEM port identifier, Media access control and ONU registration, Extended bandwidth assignment model scheduling architecture, PLOAM & alarm messages, Downstream & Upstream FEC, Process order in a GTC transmit flow. GPON ITU-T G.984.4 and G.988 ONT management and control interface (OMCI) Management interface, Reference model, Typical ONT with SCTE 55-1 or SCTE 55-2 compliancy. GPON ITU-T G.984.5 enhancement band Band options, GPON NGA, Wavelength allocation. GPON ITU-T G.984.6 optical reach extension (G.984.re) Reach extension (RE), OA-based and OEO-based reach extenders, Protection, Reach extender with OTDR blocking filters (BF) and bypass (BYP) filters. GPON ITU-T G.984.7 long reach Quiet Window. 10-GPON ITU-T G.987.1 (XG-PON) Scenarios, reference access network architecture, XG-PON with G-PON through WDM1r, G-PON and XG-PON wavelength allocation, G-PON and XG-PON co-existence with video overlay option, RE migration scenarios. G.989 40Gbps XG-PON2 Functional reference architecture, NG-PON2 system coexistence with legacy systems, Definitions of legacy compatibility terminology. GPON issues and standards GPON components GPON OLT / GPON ONT, GPON management, Operational support systems (OSS), Network management systems (NMS), OMCI (ONT Management control interface), RG (Residential gateway), Data and prioritised voice channel product, GPON broadband-forum standards, Broadband-forum , TR-069 and TR-156, HPNA (home phone network alliance), Powerline carrier (PLC), GPON DLNI G.hn or G.9960, MOCA, FTTH council certification standard for network certification. Fibre-connected home badge, Ethernet in the first mile (EFM), GPON frame synchronization to network timing, Direct clock synchronization interface (BITS), Multiservice access platform (MSAP), Software planning tool, Superconnected cities / voucher scheme. Hands on practical assignments Single and multimode fibre recognition, Fibre Cleaning methods, Checking cleaning with an optical microscope, Optical light source and optical power meter referencing, PON splitter and fibre drum testing with an optical power meter, 6km classroom passive optical network testing with an OTDR at 1310/1550nm, Using decibels (dB's) and decibel milliwats (dBm's), Designing networks up to 20km long using vendor specifications (power budget), Fault finding with a visible fault locator.

EC-Council Computer Hacking Forensic Investigator (CHFI) v10.0
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The CHFI course will benefit: Police and other laws enforcement personnel Defense and Military personnel e-Business Security professionals Systems administrators Legal professionals Banking, Insurance and other professionals Government agencies Overview At the end of this course, you will possess the skills needed to: Understand the fundamentals of computer forensics Understand the computer forensic investigation process Describe in detail different types of hard disks and file systems Understand data acquisition and duplication Counteract anti-forensic techniques Leverage forensic skills in Windows, Linux, and Mac Investigate web attacks Understand dark web forensics Deploy forensic techniques for databases, cloud, and networks Investigate email crimes including malware Perform forensics in mobile and IoT environments Every crime leaves a digital footprint, and you need the skills to track those footprints. In this course, students will learn to unravel these pieces of evidence, decode them and report them. From decoding a hack to taking legal action against the perpetrators, they will become an active respondent in times of cyber-breaches. Computer Forensics in Today?s World 1.1. Understand the Fundamentals of Computer Forensics 1.2. Understand Cybercrimes and their Investigation Procedures 1.3. Understand Digital Evidence 1.4. Understand Forensic Readiness, Incident Response and the Role of SOC (Security Operations Center) in Computer Forensics 1.5. Identify the Roles and Responsibilities of a Forensic Investigator 1.6. Understand the Challenges Faced in Investigating Cybercrimes 1.7. Understand Legal Compliance in Computer Forensics Computer Forensics Investigation Process 2.1. Understand the Forensic Investigation Process and its Importance 2.2. Understand the Pre-investigation Phase 2.3. Understand First Response 2.4. Understand the Investigation Phase 2.5. Understand the Post-investigation Phase Understanding Hard Disks and File Systems 3.1. Describe Different Types of Disk Drives and their Characteristics 3.2. Explain the Logical Structure of a Disk 3.3. Understand Booting Process of Windows, Linux and Mac Operating Systems 3.4. Understand Various File Systems of Windows, Linux and Mac Operating Systems 3.5. Examine File System Using Autopsy and The Sleuth Kit Tools 3.6 Understand Storage Systems 3.7. Understand Encoding Standards and Hex Editors 3.8. Analyze Popular File Formats Using Hex Editor Data Acquisition and Duplication 4.1. Understand Data Acquisition Fundamentals 4.2. Understand Data Acquisition Methodology 4.3. Prepare an Image File for Examination Defeating Anti-forensics Techniques 5.1. Understand Anti-forensics Techniques 5.2. Discuss Data Deletion and Recycle Bin Forensics 5.3. Illustrate File Carving Techniques and Ways to Recover Evidence from Deleted Partitions 5.4. Explore Password Cracking/Bypassing Techniques 5.5. Detect Steganography, Hidden Data in File System Structures, Trail Obfuscation, and File Extension Mismatch 5.6. Understand Techniques of Artifact Wiping, Overwritten Data/Metadata Detection, and Encryption 5.7. Detect Program Packers and Footprint Minimizing Techniques 5.8. Understand Anti-forensics Countermeasures Windows Forensics 6.1. Collect Volatile and Non-volatile Information 6.2. Perform Windows Memory and Registry Analysis 6.3. Examine the Cache, Cookie and History Recorded in Web Browsers 6.4. Examine Windows Files and Metadata 6.5. Understand ShellBags, LNK Files, and Jump Lists 6.6. Understand Text-based Logs and Windows Event Logs Linux and Mac Forensics 7.1. Understand Volatile and Non-volatile Data in Linux 7.2. Analyze Filesystem Images Using The Sleuth Kit 7.3. Demonstrate Memory Forensics Using Volatility & PhotoRec 7.4. Understand Mac Forensics Network Forensics 8.1. Understand Network Forensics 8.2. Explain Logging Fundamentals and Network Forensic Readiness 8.3. Summarize Event Correlation Concepts 8.4. Identify Indicators of Compromise (IoCs) from Network Logs 8.5. Investigate Network Traffic 8.6. Perform Incident Detection and Examination with SIEM Tools 8.7. Monitor and Detect Wireless Network Attacks Investigating Web Attacks 9.1. Understand Web Application Forensics 9.2. Understand Internet Information Services (IIS) Logs 9.3. Understand Apache Web Server Logs 9.4. Understand the Functionality of Intrusion Detection System (IDS) 9.5. Understand the Functionality of Web Application Firewall (WAF) 9.6. Investigate Web Attacks on Windows-based Servers 9.7. Detect and Investigate Various Attacks on Web Applications Dark Web Forensics 10.1. Understand the Dark Web 10.2. Determine How to Identify the Traces of Tor Browser during Investigation 10.3. Perform Tor Browser Forensics Database Forensics 11.1. Understand Database Forensics and its Importance 11.2. Determine Data Storage and Database Evidence Repositories in MSSQL Server 11.3. Collect Evidence Files on MSSQL Server 11.4. Perform MSSQL Forensics 11.5. Understand Internal Architecture of MySQL and Structure of Data Directory 11.6. Understand Information Schema and List MySQL Utilities for Performing Forensic Analysis 11.7. Perform MySQL Forensics on WordPress Web Application Database Cloud Forensics 12.1. Understand the Basic Cloud Computing Concepts 12.2. Understand Cloud Forensics 12.3. Understand the Fundamentals of Amazon Web Services (AWS) 12.4. Determine How to Investigate Security Incidents in AWS 12.5. Understand the Fundamentals of Microsoft Azure 12.6. Determine How to Investigate Security Incidents in Azure 12.7. Understand Forensic Methodologies for Containers and Microservices Investigating Email Crimes 13.1. Understand Email Basics 13.2. Understand Email Crime Investigation and its Steps 13.3. U.S. Laws Against Email Crime Malware Forensics 14.1. Define Malware and Identify the Common Techniques Attackers Use to Spread Malware 14.2. Understand Malware Forensics Fundamentals and Recognize Types of Malware Analysis 14.3. Understand and Perform Static Analysis of Malware 14.4. Analyze Suspicious Word and PDF Documents 14.5. Understand Dynamic Malware Analysis Fundamentals and Approaches 14.6. Analyze Malware Behavior on System Properties in Real-time 14.7. Analyze Malware Behavior on Network in Real-time 14.8. Describe Fileless Malware Attacks and How they Happen 14.9. Perform Fileless Malware Analysis - Emotet Mobile Forensics 15.1. Understand the Importance of Mobile Device Forensics 15.2. Illustrate Architectural Layers and Boot Processes of Android and iOS Devices 15.3. Explain the Steps Involved in Mobile Forensics Process 15.4. Investigate Cellular Network Data 15.5. Understand SIM File System and its Data Acquisition Method 15.6. Illustrate Phone Locks and Discuss Rooting of Android and Jailbreaking of iOS Devices 15.7. Perform Logical Acquisition on Android and iOS Devices 15.8. Perform Physical Acquisition on Android and iOS Devices 15.9. Discuss Mobile Forensics Challenges and Prepare Investigation Report IoT Forensics 16.1. Understand IoT and IoT Security Problems 16.2. Recognize Different Types of IoT Threats 16.3. Understand IoT Forensics 16.4. Perform Forensics on IoT Devices

Certified Data Centre Expert (CDCE)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The primary audience for this course is any IT, facilities or data centre professional, who are involved in the design/build, renovation or relocation of a mission-critical data centre. Overview This 5-day course is designed to prepare participants to analyse a given business case and perform technical evaluation for a project plan and a set of designs for the implementation of a mission critical data centre. The course also engages participants in product evaluations and demonstrates how to select equipment and develop equipment test scripts (IET) and integrated performance and validation testing (IPVT). CDCE© builds upon knowledge gained in CDCP and CDCS courses. Participants who pass the exam will join the industry's elite data centre project design experts. CDCE© is the highest level training in the EPI Design and Build training track under the EPI Data Centre Training Framework. Participants must hold a valid CDCS certificate in order to be able to register for the CDCE class. CDCE© is the premier certification for data centre professionals in the data centre design/build and related fields. Data Centre Life Cycle Data centre lifecycle stages and phases Exercise: Stage/Phase/Milestone/Document mapping Design Preparation Creation of a SON ? Statement Of Need Technology review Conceptual sizing How to calculate for computer room space How to calculate facility space How to calculate incoming power Exercise: Conceptual sizing building and power Analysing capacity of existing facility Analysing investment options Site selection Permits and approvals Exercise: Site selection Conceptual design Budget and project timeline Business case preparation Project delivery structure Project management options Project manager and team Design Planning OSRA?Operational Systems Requirement Analysis TFRA?Technical Facilities Requirement Analysis Operations and maintenance review RFP?Request For Proposal process Vendor selection Design Development Project planning Design development PDR ? Preliminary Design Review Equipment selection FDR/V ? Final Design Review/Validation Exercise: Full design validation of power, cooling, floor plans, fire suppression Design freeze and LLTI Creation of construction documents BOM/BOQ ? Bill Of Material/Bill Of Quantity Exercise: Equipment selection Acquire Requirements of purchase orders Shipping terms FWT/FAT ? Factory Witness Test/Factory Acceptance Test Sequencing Incoming goods inspection and handling Asset management Construct Temporary essential services Erection of the building Permanent essential services Building inspection Snag list COF?Certificate Of Fitness Fit-Out Fit-Out Builders cleaning As-Built Drawings Test & Commissioning IET?Individual Equipment Test IPVT/IST?Integrated Performance Verification Test/Integrated Systems Test Common mistakes with IET/IPVT Deep cleaning Exercise: IET/IPVT scripting Hand-Over Facility hand-over requirements and documents PCC?Practical Completion Certificate DLP?Defect Liability Period Defect Management ICT Systems Installation ICT Systems Testing Hand-Over/DLP Expiry FCC?Final Completion Certificate Retirement Reasons and definitions of retirement Building the business case and project plan Sequencing Transfer of site Demolishing of site Legal matters FCC?Final Completion Certificate Exam: Certified Data Centre Expert (CDCE©) The CDCE© exam is in two parts: Part A is a 90-minute closed book exam, with 60 multiple-choice questions. For Part A, the candidate requires a minimum of 45 correct answers to pass the exam. Part B is a 90-minute closed book exam, with 25 open questions. For Part B the candidate needs to obtain a minimum of 75% to pass. Additional course details: Nexus Humans Certified Data Centre Expert (CDCE) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Certified Data Centre Expert (CDCE) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

CertNexus Certified CyberSec First Responder (CFR-410)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed primarily for cybersecurity practitioners preparing for or who currently perform job functions related to protecting information systems by ensuring their availability, integrity, authentication, confidentiality, and non-repudiation. It is ideal for those roles within federal contracting companies and private sector firms whose mission or strategic objectives require the execution of Defensive Cyber Operations (DCO) or DoD Information Network (DoDIN) operation and incident handling. This course focuses on the knowledge, ability, and skills necessary to provide for the defense of those information systems in a cybersecurity context, including protection, detection, analysis, investigation, and response processes. Overview In this course, you will identify, assess, respond to, and protect against security threats and operate a system and network security analysis platform. You will: Assess cybersecurity risks to the organization. Analyze the threat landscape. Analyze various reconnaissance threats to computing and network environments. Analyze various attacks on computing and network environments. Analyze various post-attack techniques. Assess the organization's security posture through auditing, vulnerability management, and penetration testing. Collect cybersecurity intelligence from various network-based and host-based sources. Analyze log data to reveal evidence of threats and incidents. Perform active asset and network analysis to detect incidents. Respond to cybersecurity incidents using containment, mitigation, and recovery tactics. Investigate cybersecurity incidents using forensic analysis techniques. This course covers network defense and incident response methods, tactics, and procedures that are in alignment with industry frameworks such as NIST 800-61r2 (Computer Security Incident Handling Guide), US-CERT's National Cyber Incident Response Plan (NCIRP), and Presidential Policy Directive (PPD)-41 on Cyber Incident Coordination. It is ideal for candidates who have been tasked with the responsibility of monitoring and detecting security incidents in information systems and networks, and for executing standardized responses to such incidents. The course introduces tools, tactics, and procedures to manage cybersecurity risks, defend cybersecurity assets, identify various types of common threats, evaluate the organization's security, collect and analyze cybersecurity intelligence, and remediate and report incidents as they occur. This course provides a comprehensive methodology for individuals responsible for defending the cybersecurity of their organization. This course is designed to assist students in preparing for the CertNexus CyberSec First Responder (Exam CFR-410) certification examination. What you learn and practice in this course can be a significant part of your preparation. In addition, this course and subsequent certification (CFR-410) meet all requirements for personnel requiring DoD directive 8570.01-M position certification baselines: CSSP Analyst CSSP Infrastructure Support CSSP Incident Responder CSSP Auditor The course and certification also meet all criteria for the following Cybersecurity Maturity Model Certification (CMMC) domains: Incident Response (IR) Audit and Accountability (AU) Risk Management (RM) Lesson 1: Assessing Cybersecurity Risk Topic A: Identify the Importance of Risk Management Topic B: Assess Risk Topic C: Mitigate Risk Topic D: Integrate Documentation into Risk Management Lesson 2: Analyzing the Threat Landscape Topic A: Classify Threats Topic B: Analyze Trends Affecting Security Posture Lesson 3: Analyzing Reconnaissance Threats to Computing and Network Environments Topic A: Implement Threat Modeling Topic B: Assess the Impact of Reconnaissance Topic C: Assess the Impact of Social Engineering Lesson 4: Analyzing Attacks on Computing and Network Environments Topic A: Assess the Impact of System Hacking Attacks Topic B: Assess the Impact of Web-Based Attacks Topic C: Assess the Impact of Malware Topic D: Assess the Impact of Hijacking and Impersonation Attacks Topic E: Assess the Impact of DoS Incidents Topic F: Assess the Impact of Threats to Mobile Security Topic G: Assess the Impact of Threats to Cloud Security Lesson 5: Analyzing Post-Attack Techniques Topic A: Assess Command and Control Techniques Topic B: Assess Persistence Techniques Topic C: Assess Lateral Movement and Pivoting Techniques Topic D: Assess Data Exfiltration Techniques Topic E: Assess Anti-Forensics Techniques Lesson 6: Assessing the Organization's Security Posture Topic A: Implement Cybersecurity Auditing Topic B: Implement a Vulnerability Management Plan Topic C: Assess Vulnerabilities Topic D: Conduct Penetration Testing Lesson 7: Collecting Cybersecurity Intelligence Topic A: Deploy a Security Intelligence Collection and Analysis Platform Topic B: Collect Data from Network-Based Intelligence Sources Topic C: Collect Data from Host-Based Intelligence Sources Lesson 8: Analyzing Log Data Topic A: Use Common Tools to Analyze Logs Topic B: Use SIEM Tools for Analysis Lesson 9: Performing Active Asset and Network Analysis Topic A: Analyze Incidents with Windows-Based Tools Topic B: Analyze Incidents with Linux-Based Tools Topic C: Analyze Indicators of Compromise Lesson 10: Responding to Cybersecurity Incidents Topic A: Deploy an Incident Handling and Response Architecture Topic B: Mitigate Incidents Topic C: Hand Over Incident Information to a Forensic Investigation Lesson 11: Investigating Cybersecurity Incidents Topic A: Apply a Forensic Investigation Plan Topic B: Securely Collect and Analyze Electronic Evidence Topic C: Follow Up on the Results of an Investigation Additional course details: Nexus Humans CertNexus Certified CyberSec First Responder (CFR-410) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the CertNexus Certified CyberSec First Responder (CFR-410) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

EC-Council Certified Ethical Hacker (CEH) v12
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The Certified Ethical Hacking v12 course will significantly benefit security officers, auditors, security professionals, site administrators, and anyone who is concerned about the integrity of the network infrastructure. Overview Information security controls, laws, and standards. Various types of footprinting, footprinting tools, and countermeasures. Network scanning techniques and scanning countermeasures Enumeration techniques and enumeration countermeasures Vulnerability analysis to identify security loopholes in the target organization?s network, communication infrastructure, and end systems. System hacking methodology, steganography, steganalysis attacks, and covering tracks to discover system and network vulnerabilities. Different types of malware (Trojan, Virus, worms, etc.), system auditing for malware attacks, malware analysis, and countermeasures. Packet sniffing techniques to discover network vulnerabilities and countermeasures to defend against sniffing. Social engineering techniques and how to identify theft attacks to audit human-level vulnerabilities and social engineering countermeasures. DoS/DDoS attack techniques and tools to audit a target and DoS/DDoS countermeasures. Session hijacking techniques to discover network-level session management, authentication/authorization, and cryptographic weaknesses and countermeasures. Webserver attacks and a comprehensive attack methodology to audit vulnerabilities in webserver infrastructure, and countermeasures. Web application attacks, comprehensive web application hacking methodology to audit vulnerabilities in web applications, and countermeasures. SQL injection attack techniques, injection detection tools to detect SQL injection attempts, and countermeasures. Wireless encryption, wireless hacking methodology, wireless hacking tools, and Wi-Fi security tools. Mobile platform attack vector, android vulnerability exploitations, and mobile security guidelines and tools. Firewall, IDS and honeypot evasion techniques, evasion tools and techniques to audit a network perimeter for weaknesses, and countermeasures. Cloud computing concepts (Container technology, serverless computing), the working of various threats and attacks, and security techniques and tools. Penetration testing, security audit, vulnerability assessment, and penetration testing roadmap. Threats to IoT and OT platforms and defending IoT and OT devices. Cryptography ciphers, Public Key Infrastructure (PKI), cryptography attacks, and cryptanalysis tools. CEH provides an in-depth understanding of ethical hacking phases, various attack vectors, and preventative countermeasures. It will teach you how hackers think and act maliciously so you will be better positioned to setup your security infrastructure and defend against future attacks. An understanding of system weaknesses and vulnerabilities helps organizations strengthen their system security controls to minimize the risk of an incident. CEH was built to incorporate a hands-on environment and systematic process across each ethical hacking domain and methodology, giving you the opportunity to work towards proving the required knowledge and skills needed to achieve the CEH credential. You will be exposed to an entirely different posture toward the responsibilities and measures required to be secure. Now in its 12th version, CEH continues to evolve with the latest operating systems, tools, tactics, exploits, and technologies. 1 - Introduction to Ethical Hacking Information Security Overview Cyber Kill Chain Concepts Hacking Concepts Ethical Hacking Concepts Information Security Controls Information Security Laws and Standards 2 - 2 - Foot-printing and Reconnaissance Footprinting Concepts Footprinting through Search Engines Footprinting through Web Services Footprinting through Social Networking Sites Website Footprinting Email Footprinting Who is Footprinting DNS Footprinting Network Footprinting Footprinting through Social Engineering Footprinting Tools Footprinting Countermeasures 3 - Scanning Networks Network Scanning Concepts Scanning Tools Host Discovery Port and Service Discovery OS Discovery (Banner Grabbing/OS Fingerprinting) Scanning Beyond IDS and Firewall Draw Network Diagrams 4 - Enumeration Enumeration Concepts NetBIOS Enumeration SNMP Enumeration LDAP Enumeration NTP and NFS Enumeration SMTP and DNS Enumeration Other Enumeration Techniques Enumeration Countermeasures 5 - Vulnerability Analysis Vulnerability Assessment Concepts Vulnerability Classification and Assessment Types Vulnerability Assessment Solutions and Tools Vulnerability Assessment Reports 6 - System Hacking System Hacking Concepts Gaining Access Escalating Privileges Maintaining Access Clearing Logs 7 - Malware Threats Malware Concepts APT Concepts Trojan Concepts Virus and Worm Concepts Fileless Malware Concepts Malware Analysis Countermeasures Anti-Malware Software 8 - Sniffing Sniffing Concepts Sniffing Technique: MAC Attacks Sniffing Technique: DHCP Attacks Sniffing Technique: ARP Poisoning Sniffing Technique: Spoofing Attacks Sniffing Technique: DNS Poisoning Sniffing Tools Countermeasures Sniffing Detection Techniques 9 - Social Engineering Social Engineering Concepts Social Engineering Techniques Insider Threats Impersonation on Social Networking Sites Identity Theft Countermeasures 10 - Denial-of-Service DoS/DDoS Concepts DoS/DDoS Attack Techniques BotnetsDDoS Case Study DoS/DDoS Attack Tools Countermeasures DoS/DDoS Protection Tools 11 - Session Hijacking Session Hijacking Concepts Application Level Session Hijacking Network Level Session Hijacking Session Hijacking Tools Countermeasures 12 - Evading IDS, Firewalls, and Honeypots IDS, IPS, Firewall, and Honeypot Concepts IDS, IPS, Firewall, and Honeypot Solutions Evading IDS Evading Firewalls IDS/Firewall Evading Tools Detecting Honeypots IDS/Firewall Evasion Countermeasures 13 - Hacking Web Servers Web Server Concepts Web Server Attacks Web Server Attack Methodology Web Server Attack Tools Countermeasures Patch Management Web Server Security Tools 14 - Hacking Web Applications Web Application Concepts Web Application Threats Web Application Hacking Methodology Web API, Webhooks, and Web Shell Web Application Security 15 - SQL Injection SQL Injection Concepts Types of SQL Injection SQL Injection Methodology SQL Injection Tools Evasion Techniques Countermeasures 16 - Hacking Wireless Networks Wireless Concepts Wireless Encryption Wireless Threats Wireless Hacking Methodology Wireless Hacking Tools Bluetooth Hacking Countermeasures Wireless Security Tools 17 - Hacking Mobile Platforms Mobile Platform Attack Vectors Hacking Android OS Hacking iOS Mobile Device Management Mobile Security Guidelines and Tools 18 - IoT and OT Hacking IoT Hacking IoT Concepts IoT Attacks IoT Hacking Methodology IoT Hacking Tools Countermeasures OT Hacking OT Concepts OT Attacks OT Hacking Methodology OT Hacking Tools Countermeasures 19 - Cloud Computing Cloud Computing Concepts Container Technology Serverless Computing Cloud Computing Threats Cloud Hacking Cloud Security 20 - Cryptography Cryptography Concepts Encryption Algorithms Cryptography Tools Public Key Infrastructure (PKI) Email Encryption Disk Encryption Cryptanalysis Countermeasures Additional course details: Nexus Humans EC-Council Certified Ethical Hacker (CEH) v.12 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the EC-Council Certified Ethical Hacker (CEH) v.12 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

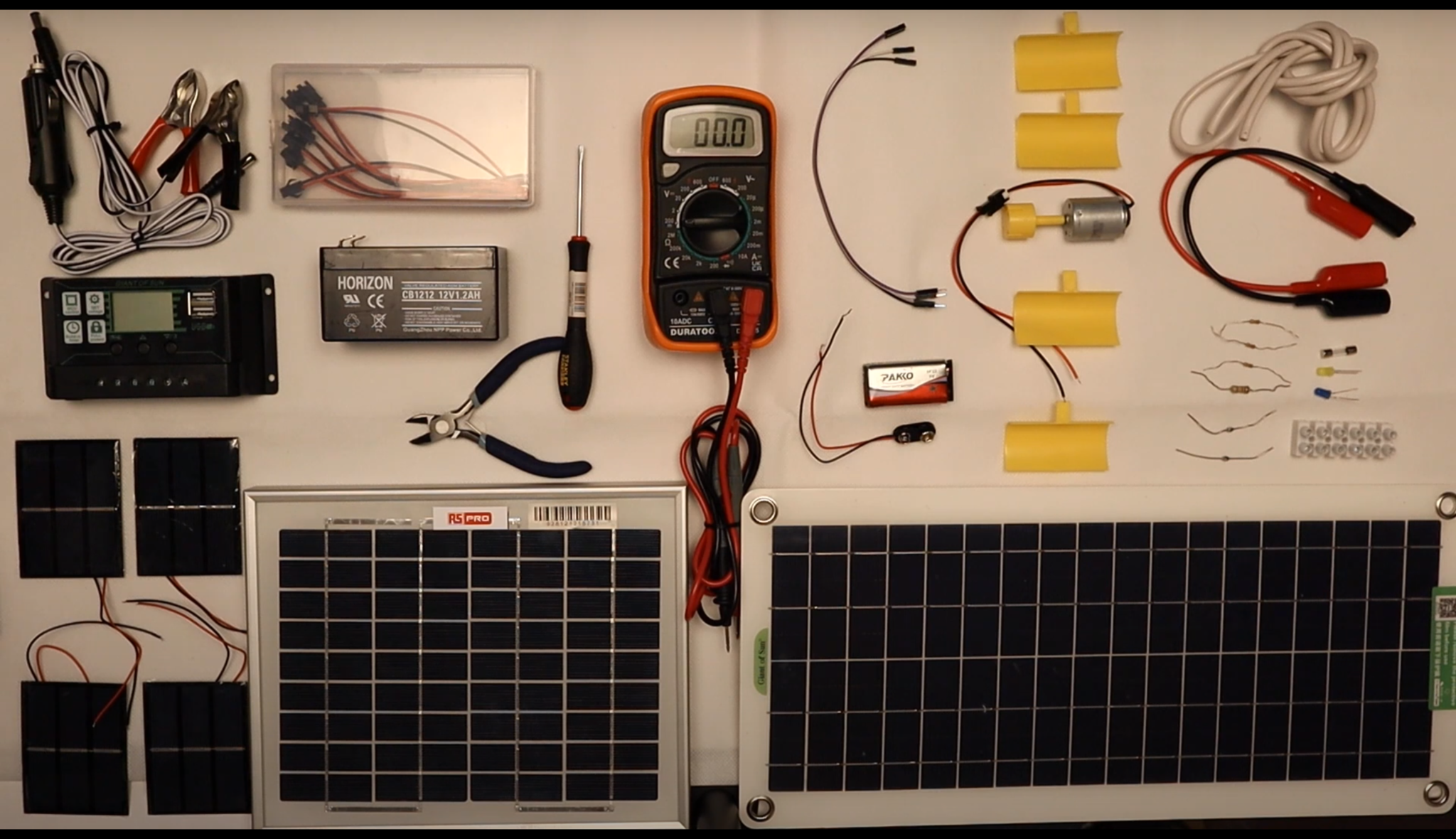
Alternative Energy Technology Course
By Hi-Tech Training
The Alternative Energy Technology Course is a practically based alternative energy course designed to give participants an understanding of alternative energy options and provide them with that practical knowledge and skills to build solar to electric and wind to electric systems at a foundation level. The course is designed to be of benefit to people either working or intending to work as:- Alternative Energy Installers or anyone just wishing to gain practical knowledge of Practical Alternative Energy Systems
EC-Council Certified Cybersecurity Technician (C|CT)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The C|CT is ideal for anyone looking to start their career in cybersecurity or add a strong foundational understanding of the cybersecurity concepts and techniques required to be effective on the job. The course is especially well suited to: Early-career IT professionals, IT managers, career changers, and career advancers Students and recent graduates Overview After completing this course, you will understand: Key concepts in cybersecurity, including information security and network security Information security threats, vulnerabilities, and attacks The different types of malware Identification, authentication, and authorization Network security controls Network security assessment techniques and tools (threat hunting, threat intelligence, vulnerability assessment, ethical hacking, penetration testing, configuration and asset management) Application security design and testing techniques Fundamentals of virtualization, cloud computing, and cloud security Wireless network fundamentals, wireless encryption, and related security measures Fundamentals of mobile, IoT, and OT devices and related security measures Cryptography and public-key infrastructure Data security controls, data backup and retention methods, and data loss prevention techniques Network troubleshooting, traffic and log monitoring, and analysis of suspicious traffic The incident handling and response process Computer forensics and digital evidence fundamentals, including the phases of a forensic investigation Concepts in business continuity and disaster recovery Risk management concepts, phases, and frameworks EC-Council?s C|CT certification immerses students in well-constructed knowledge transfer. Training is accompanied by critical thinking challenges and immersive lab experiences that allow candidates to apply their knowledge and move into the skill development phase in the class itself. Upon completing the program, C|CT-certified professionals will have a strong foundation in cybersecurity principles and techniques as well as hands-on exposure to the tasks required in real-world jobs. Course Outline Information Security Threats and Vulnerabilities Information Security Attacks Network Security Fundamentals Identification, Authentication, and Authorization Network Security Controls: Administrative Controls Network Security Controls: Physical Controls Network Security Controls: Technical Controls Network Security Assessment Techniques and Tools Application Security Virtualization and Cloud Computing Wireless Network Security Mobile Device Security Internet of Things (IoT) and Operational Technology (OT) Security Cryptography Data Security Network Troubleshooting Network Traffic Monitoring Network Log Monitoring and Analysis Incident Response Computer Forensics Business Continuity and Disaster Recovery Risk Management

ICA International Diploma in Managing Sanctions Risk
By International Compliance Association
ICA International Diploma in Managing Sanctions Risk Sanctions are a crucial instrument in the international battle against financial crime proliferation, terrorism and human rights abuses. It's a complex area and those who manage the risk need the right combination of knowledge, capabilities and behaviours to do so effectively. Technical skills - develop a deeper understanding of sanctions architecture, screening and the control framework; enrich your professional skillset Critical thinking - enhance your judgment-making and problem-solving skills Collaboration and communication - ensure a joined-up approach in your management of sanctions cases Flexibility and adaptability - be prepared to respond to fast-changing regimes and rules Leadership - be empowered to make effective decisions quickly and manage resources appropriately This course is awarded in association with Alliance Manchester Business School, the University of Manchester. Through this Level 6- Advanced qualification you will learn: Global sanctions architecture - Sanctions in context How sanctions regimes are implemented Evolving scope of sanctions - A changing tool Sector-based sanctions Identifying higher risk jurisdictions and activities Transparency, control, and ownership Licensing and permissible payments Management of global exposure to unilateral and regional sanctions Developing the control framework Sanctions screening Incident management and holding of sanctioned funds Sanctions lifting and roll back
