- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
2159 Other courses in Liverpool delivered Live Online
Business Relationship Management Professional (BRMP): Virtual In-House Training
By IIL Europe Ltd
Business Relationship Management Professional (BRMP)®: Virtual In-House Training Business Relationship Management (BRM) embodies a set of competencies (knowledge, skills, and behaviors) to foster an effective business value-producing relationship between a service provider and its business partners. The BRM Discipline rests on solid research-based foundations verified and enhanced over a decade of successful implementations in leading organizations across the world. Proven to be equally effective for shared services including Human Resources, Finance, Legal, external service providers and others, BRM practices have enjoyed widespread adaptation in IT. The Business Relationship Management Professional (BRMP) training and certification program provides a foundational understanding of business relationship management (BRM) for individuals at every experience level, with the training and certification designed to provide a solid baseline level of knowledge. In other words, this course provides the 'why' and the 'what' - 'why' business relationship management is important to your organization and 'what' a BRM capability does to add value to your organization. This interactive course, with discussions, partnering activities, and periodic knowledge checks, will provide you with the opportunity to apply learning to your unique organizational situations, creating solutions that you can use immediately upon returning to your workplace. This practical knowledge will allow you to demonstrate immediate value in your role, as well as prepare you for the BRMP Certification exam.

MENTAL HEALTH – UNDERSTANDING AND MEETING NEEDS
By Inclusive Solutions
In this course we explore Mental Health and address how such needs can be met in mainstream classrooms. Course Category Behaviour and Relationships Meeting Emotional Needs Description This is our lead workshop/training day on understanding mental health, behaviour and relationship work in schools other settings and is both a values primer and a practical guide to successful innovative strategies for improving behaviour and strengthening relationships for challenging children and young people of all ages. Not just another day on ‘Behaviour Management’ – Our Mental Health Day goes well beyond a rewards and sanctions approach to ‘behaviour’. We will be focused on those young people for whom rewards and punishments do not always work and who confuse the adults who work with them. We aim to take a relationships-based approach and to give those attending an opportunity to think more deeply about why young people do the things they do and what our part as adults is in creating, sustaining and changing these behaviours. The day gives those present opportunities to reflect on their attitudes and practice in relation to children’s behaviour and relationship building. If your usual approaches to managing tackling mental health needs aren’t working with particular individuals then take a tour through this range of cutting edge strategies for bringing about positive behaviour change, and for meeting challenging emotional needs Learning Objectives reinforce and affirm good practice re-energise, stimulate and challenge thinking about inclusion of challenging pupils and children increased understanding of mental health increased confidence in managing challenging pupils in mainstream schools access to a wider range of practical strategies to impact on behaviour problems opportunity to reflect on professional attitudes and behaviour towards mental health in families and pupils Who Is It For ? Anyone concerned with understanding and meeting emotional and mental health needs Course Content Circle of Courage – belonging-achievement-generosity – independence – model for understanding mental health Compass of Anxiety – understanding and going deeper Active listening – Listening to the person underneath the behaviour Involving other children and young people in solutions and interventions - Circles of friends: peer support, counselling and mediation Team Problem Solving – Solution Circles: a 30 minute group problem solving process to get Teams ‘unstuck’ and to generate positive first action steps Restorative justice and restitution: principles and practice of this approach to repairing harm and restoring relationships without reliance on punishment Understanding the effects of Separation, Loss, Trauma and Neglect on children’s learning and relationships in school and what adults can do to reach and support these children

VoIP and IP Telephony training course description A concise overview course for management covering voice communications using IP networks. The course focuses on how VoIP works at a simplified level enabling delegates to recognise the key decisions to be made when implementing VoIP. What will you learn Describe the key buzzwords used in the VoIP arena. Explain how VoIP and IPT work (at a simplified level). Describe the issues of providing a converged architecture. Recognise the key decisions to be made when implementing VoIP VoIP and IP Telephony training course details Who will benefit: Anyone, although the course is particularly aimed at non-technical personnel needing some knowledge of VoIP. Prerequisites: Network fundamentals Duration 1 day VoIP and IP Telephony training course contents Introduction What is VoIP, brief review of IP, brief review of telephones, voice and signalling. VoIP issues Bandwidth, Delay, Jitter. Voice coding and compression, packetising voice, comparison of techniques, MOS.IP performance and QoS. The need for QoS, prioritising voice. Architectures Hard phones, soft phones, video phones, desktop, backbone, gateway, integrating analog phones and PCs, carriers, Softswitches. VoIP protocol stack RTP, RTCP. H.323 vs SIP, other signalling protocols. H.323 Architecture, Call setup, Gatekeepers. SIP Comparison with H.323, SIP proxy, proxy servers, redirect servers, location servers. MGCP and MegaCo Carrier networks, PSTN breakout, SS7 gateways, MGCP, Megaco. IP PBXs Integrating IP into 'normal' PBXs, IP PBXs, Asterisk. UM, other telephony applications.

Existential Dialogue 2025: "Opening" with Dr. Yaqui Martinez
By Therapy Harley Street
I want to discuss the existential-phenomenological challenges of viewing the human condition and explore alternatives for openness. We aim to explore the lived experiences on irregular perceptions of reality with an open mind. Each Saturday includes: a live dialogue between Prof. Ernesto Spinelli and an International Existential Therapist; a moment to share your thoughts and feelings with the teachers; and a final integration facilitated by Bárbara Godoy. This series of ten dialogues set out to explore the multifaceted dimentions and complexities associated with Existential Therapies. It attempts to engage with various interpretations of insanity through the lens of patients often painful, confounding, and deeply unsettling life experiences. Opening- between Prof. Ernesto Spinelli and Dr. Yaqui Martinez “From my early days studying psychology, I never felt comfortable with psychopathological nosologies. They seemed exaggerated to me and demonstrated the intense human desire to classify all possible expressions of our existence. Likewise, I have not been comfortable with the tendency to promote dualistic perspectives that compartmentalize our reality into separate aspects where one is not only different from the other but even in opposition, such as the sane/insane dichotomy. During this dialogue, I want to talk with Ernesto about the difficulties involved, from an existential-phenomenological perspective, in viewing the human condition from this position. Perhaps we can ask ourselves together what advantages they offer and what alternatives for openness we can propose.” Dr. Yaqui Martinez. Dr. Yaqui A. Martínez-Robles is a psychologist with Masters, PhD and PsyD in Psychotherapy. He has training in Gestalt Therapy; Music Therapy; Transpersonal Psychology and Holotropic Breathwork (with the Grof Transpersonal Training Association); Narrative and postmodern therapies and Social Constructionism; and in Psychedelic-Assisted Therapy (with the Integrative Psychiatry Institute and MAPS-Multidisciplinary Association for Psychedelic Studies). He is the author of four books, and co-author of another two, focused on the existential perspective. He has participated with chapters in several books and with articles in several journals. Yaqui is the founder of the Circle of Studies in Existential Therapy, in Mexico City and in Medellin, Colombia,. He teaches existential-phenomenological psychology and therapy in Mexico and different countries of South America. He is the current president of the Latin American Association of Existential Psychotherapy (ALPE). He works in private practice as an existential-phenomenological therapist and coach, in modalities one-on-one, couples and groups. Prof. Ernesto Spinelli was Chair of the Society for Existential Analysis between 1993 and 1999 and is a Life Member of the Society. His writings, lectures and seminars focus on the application of existential phenomenology to the arenas of therapy, supervision, psychology, and executive coaching. He is a Fellow of the British Psychological Society (BPS) as well as an APECS accredited executive coach and coaching supervisor. In 2000, he was the Recipient of BPS Division of Counselling Psychology Award for Outstanding Contribution to the Profession. And in 2019, Ernesto received the BPS Award for Distinguished Contribution to Practice. His most recent book, Practising Existential Therapy: The Relational World 2nd edition (Sage, 2015) has been widely praised as a major contribution to the advancement of existential theory and practice. Living up to the existential dictum that life is absurd, Ernesto is also the author of an on-going series of Private Eye novels. Date and Time: Saturday 19 June from 2 pm to 3 pm – (UK time) Individual Dialogue Fee: £70 Venue: Online Zoom FULL PROGRAMME 2025: 25 January “Knots” with Prof. Ernesto Spinelli and Bárbara Godoy 22 February “Healing” with Dr. Michael Guy Thompson and Prof. Ernesto Spinelli 22 March “Difference” with Prof. Tod DuBose and Prof. Ernesto Spinelli 12 April “Polarisation” with Prof. Kirk Schneider and Prof. Ernesto Spinelli 3 May “Character” with Prof. Robert Romanyshyn and Prof. Ernesto Spinelli 21 June “Opening” with Dr. Yaqui Martinez and Prof. Ernesto Spinelli 19 July “Meaning” with Dr. Jan Resnick and Prof. Ernesto Spinelli 25 October “Invention” with Dr. Betty Cannon and Prof. Ernesto Spinelli 15 November “Hallucination” with Prof. Simon du Plock and Prof. Ernesto Spinelli 13 December “Hysteria” with Bárbara Godoy and Prof. Ernesto Spinelli Read the full programme here > Course Organised by:

EC-Council Computer Hacking Forensic Investigator (CHFI) v10.0
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The CHFI course will benefit: Police and other laws enforcement personnel Defense and Military personnel e-Business Security professionals Systems administrators Legal professionals Banking, Insurance and other professionals Government agencies Overview At the end of this course, you will possess the skills needed to: Understand the fundamentals of computer forensics Understand the computer forensic investigation process Describe in detail different types of hard disks and file systems Understand data acquisition and duplication Counteract anti-forensic techniques Leverage forensic skills in Windows, Linux, and Mac Investigate web attacks Understand dark web forensics Deploy forensic techniques for databases, cloud, and networks Investigate email crimes including malware Perform forensics in mobile and IoT environments Every crime leaves a digital footprint, and you need the skills to track those footprints. In this course, students will learn to unravel these pieces of evidence, decode them and report them. From decoding a hack to taking legal action against the perpetrators, they will become an active respondent in times of cyber-breaches. Computer Forensics in Today?s World 1.1. Understand the Fundamentals of Computer Forensics 1.2. Understand Cybercrimes and their Investigation Procedures 1.3. Understand Digital Evidence 1.4. Understand Forensic Readiness, Incident Response and the Role of SOC (Security Operations Center) in Computer Forensics 1.5. Identify the Roles and Responsibilities of a Forensic Investigator 1.6. Understand the Challenges Faced in Investigating Cybercrimes 1.7. Understand Legal Compliance in Computer Forensics Computer Forensics Investigation Process 2.1. Understand the Forensic Investigation Process and its Importance 2.2. Understand the Pre-investigation Phase 2.3. Understand First Response 2.4. Understand the Investigation Phase 2.5. Understand the Post-investigation Phase Understanding Hard Disks and File Systems 3.1. Describe Different Types of Disk Drives and their Characteristics 3.2. Explain the Logical Structure of a Disk 3.3. Understand Booting Process of Windows, Linux and Mac Operating Systems 3.4. Understand Various File Systems of Windows, Linux and Mac Operating Systems 3.5. Examine File System Using Autopsy and The Sleuth Kit Tools 3.6 Understand Storage Systems 3.7. Understand Encoding Standards and Hex Editors 3.8. Analyze Popular File Formats Using Hex Editor Data Acquisition and Duplication 4.1. Understand Data Acquisition Fundamentals 4.2. Understand Data Acquisition Methodology 4.3. Prepare an Image File for Examination Defeating Anti-forensics Techniques 5.1. Understand Anti-forensics Techniques 5.2. Discuss Data Deletion and Recycle Bin Forensics 5.3. Illustrate File Carving Techniques and Ways to Recover Evidence from Deleted Partitions 5.4. Explore Password Cracking/Bypassing Techniques 5.5. Detect Steganography, Hidden Data in File System Structures, Trail Obfuscation, and File Extension Mismatch 5.6. Understand Techniques of Artifact Wiping, Overwritten Data/Metadata Detection, and Encryption 5.7. Detect Program Packers and Footprint Minimizing Techniques 5.8. Understand Anti-forensics Countermeasures Windows Forensics 6.1. Collect Volatile and Non-volatile Information 6.2. Perform Windows Memory and Registry Analysis 6.3. Examine the Cache, Cookie and History Recorded in Web Browsers 6.4. Examine Windows Files and Metadata 6.5. Understand ShellBags, LNK Files, and Jump Lists 6.6. Understand Text-based Logs and Windows Event Logs Linux and Mac Forensics 7.1. Understand Volatile and Non-volatile Data in Linux 7.2. Analyze Filesystem Images Using The Sleuth Kit 7.3. Demonstrate Memory Forensics Using Volatility & PhotoRec 7.4. Understand Mac Forensics Network Forensics 8.1. Understand Network Forensics 8.2. Explain Logging Fundamentals and Network Forensic Readiness 8.3. Summarize Event Correlation Concepts 8.4. Identify Indicators of Compromise (IoCs) from Network Logs 8.5. Investigate Network Traffic 8.6. Perform Incident Detection and Examination with SIEM Tools 8.7. Monitor and Detect Wireless Network Attacks Investigating Web Attacks 9.1. Understand Web Application Forensics 9.2. Understand Internet Information Services (IIS) Logs 9.3. Understand Apache Web Server Logs 9.4. Understand the Functionality of Intrusion Detection System (IDS) 9.5. Understand the Functionality of Web Application Firewall (WAF) 9.6. Investigate Web Attacks on Windows-based Servers 9.7. Detect and Investigate Various Attacks on Web Applications Dark Web Forensics 10.1. Understand the Dark Web 10.2. Determine How to Identify the Traces of Tor Browser during Investigation 10.3. Perform Tor Browser Forensics Database Forensics 11.1. Understand Database Forensics and its Importance 11.2. Determine Data Storage and Database Evidence Repositories in MSSQL Server 11.3. Collect Evidence Files on MSSQL Server 11.4. Perform MSSQL Forensics 11.5. Understand Internal Architecture of MySQL and Structure of Data Directory 11.6. Understand Information Schema and List MySQL Utilities for Performing Forensic Analysis 11.7. Perform MySQL Forensics on WordPress Web Application Database Cloud Forensics 12.1. Understand the Basic Cloud Computing Concepts 12.2. Understand Cloud Forensics 12.3. Understand the Fundamentals of Amazon Web Services (AWS) 12.4. Determine How to Investigate Security Incidents in AWS 12.5. Understand the Fundamentals of Microsoft Azure 12.6. Determine How to Investigate Security Incidents in Azure 12.7. Understand Forensic Methodologies for Containers and Microservices Investigating Email Crimes 13.1. Understand Email Basics 13.2. Understand Email Crime Investigation and its Steps 13.3. U.S. Laws Against Email Crime Malware Forensics 14.1. Define Malware and Identify the Common Techniques Attackers Use to Spread Malware 14.2. Understand Malware Forensics Fundamentals and Recognize Types of Malware Analysis 14.3. Understand and Perform Static Analysis of Malware 14.4. Analyze Suspicious Word and PDF Documents 14.5. Understand Dynamic Malware Analysis Fundamentals and Approaches 14.6. Analyze Malware Behavior on System Properties in Real-time 14.7. Analyze Malware Behavior on Network in Real-time 14.8. Describe Fileless Malware Attacks and How they Happen 14.9. Perform Fileless Malware Analysis - Emotet Mobile Forensics 15.1. Understand the Importance of Mobile Device Forensics 15.2. Illustrate Architectural Layers and Boot Processes of Android and iOS Devices 15.3. Explain the Steps Involved in Mobile Forensics Process 15.4. Investigate Cellular Network Data 15.5. Understand SIM File System and its Data Acquisition Method 15.6. Illustrate Phone Locks and Discuss Rooting of Android and Jailbreaking of iOS Devices 15.7. Perform Logical Acquisition on Android and iOS Devices 15.8. Perform Physical Acquisition on Android and iOS Devices 15.9. Discuss Mobile Forensics Challenges and Prepare Investigation Report IoT Forensics 16.1. Understand IoT and IoT Security Problems 16.2. Recognize Different Types of IoT Threats 16.3. Understand IoT Forensics 16.4. Perform Forensics on IoT Devices

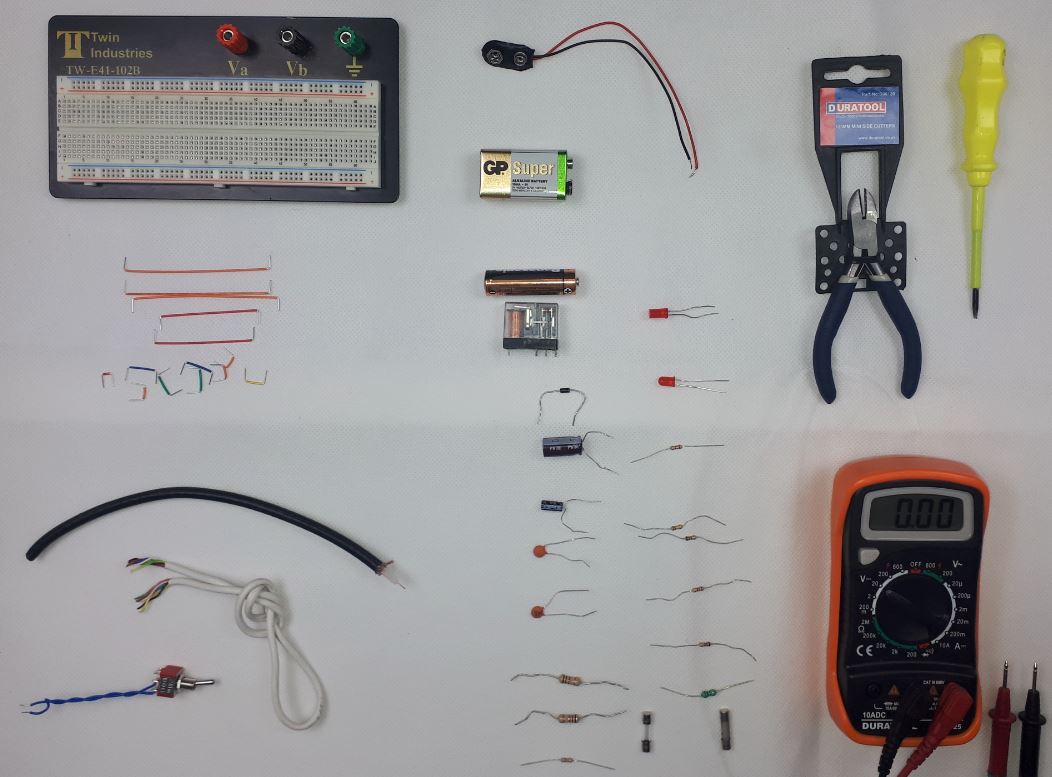
Preliminary Electronic Security Course
By Hi-Tech Training
The Preliminary Electronic Security Course is an introductory (or revision) course designed to provide participants who have no previous Electrical or Electronics experience with the background skills required to attend the CCTV Installation Course, Access Control Course or Fire Alarm Foundation Course. The course gives both an introduction to electronics and electronic security and shows how the two fields merge together. Ideal for a beginner wishing to learn more about this fascinating area. A large practical content is guaranteed. The day will be an excellent learning experience with a skilled instructor. It is a great introduction to the other courses we provide.
Kerberos for engineers training course description This hands on course covers the details of Kerberos, from installation and administration through to how it all works including the protocols. What will you learn Describe what Kerberos is. Explain how Kerberos works. Install Kerberos. Configure Kerberos. Troubleshoot Kerberos. Kerberos for engineers training course details Who will benefit: Engineers interested in security. Prerequisites: TCP/IP foundation for engineers Duration 2 days Kerberos for engineers training course contents What is Kerberos? Single Sign On, The protocol, the standard, history, v4, v5, RFCs, Linux, Windows. Kerberos concepts and technology AAA, Authentication, Authorization, Accounting. Kerberos vs LDAP and directories. Privacy, integrity. Kerberos realms, principles, instances. Keys, salts, passwords. Key Distribution Centre, Authentication server, ticket granting server. Tickets. Installation and administration of Kerberos Installing Kerberos, creating realms, testing. DNS and Kerberos, Kerberos clients. Hands on Windows and Linux Kerberos. Kerberos protocols The Needham-Schroeder protocol, Kerberos v4. Authentication server, ticket granting server, Kerberos v5, encryption options, ticket options, other protocol features and extensions. Related protocols: GSSAPI, SPNEGO. Hands on Using Wireshark to 'see' Kerberos. Troubleshooting Kerberos Approach, debugging tools, errors and solutions. Hands on Kerberos troubleshooting. Kerberos security concerns Kerberos attacks, protocol security issues. Dictionary attacks, brute force attacks, replay attacks, MITM attacks, security solutions, protecting the KDC, firewalls, NAT and Kerberos. Hands on Kerberos logging. Software which uses Kerberos Kerberos logins, Kerberos and web based applications, Directory services. Advanced Kerberos issues Cross realm authentication, Windows issues, Windows and UNIX interoperability, Hands on Using a Windows DC for UNIX clients.

Peering demystified training course description A concise overview course covering The Internet and peering. Particular emphasis is placed on the structure of the Internet, how IXs benefit the Internet, IX architectures, peering and the technical buzzwords behind the IX services. What will you learn Describe the structure of the Internet Explain the role of RIPE, ARIN and IXs in the Internet Explain how IXs connect ISPs and the benefits of using IXs. Describe peering from a technical perspective including the role of BGP and AS's. Peering demystified training course details Who will benefit: Non technical staff working for Internet companies. Prerequisites: None. Duration 1 day Peering demystified training course contents IP and routers IP as glue. What is a router? How routers join networks, benefits and disadvantages of routers, default gateways, routing tables, routing protocols. Addressing IP address format, rules of IP addressing, where to get IP addresses. Subnetting and groups of IP addresses. The Internet What is the Internet? The big picture, IP basics, registering IP addresses, DNS and registering domain names, whois, The IAB, IANA, ICANN, RIPE and other Internet organisations. ISPs Top ISPs, Tier 1, Tier 2 and Tier 3 ISPs, backbone providers, circuit providers, content providers, virtual ISPs, the internal network of ISPs. Customer connections to ISPs (DSL, Leased lines, MPLSâ¦) ISP to ISP connections: Peering points Public peering versus private peering, NAPs, Internet Exchanges, Metropolitan Area Exchanges, LINX, other major peering points, the geography of the Internet. BGP and ASNs. How to peer. IRRs. IX architecture Ethernet switching.

Project Communication Skills (Virtual)
By IIL Europe Ltd
Project Communication Skills (Virtual) Communication is the single most critical project success factor. When effective, projects get executed on time, within budget, and with objectives being met. But that isn't all. Strong communication also nurtures healthy team relationships. And in today's highly diverse world, where projects are often fast-paced, complex, and virtual, that is more important than ever. Strong communication skills foster cultural awareness, trust, and empathy. Together, they contribute greatly to project success-and ultimately, to future project success. In this course, participants will actively explore best communication practices from a variety of perspectives: in-person, virtual, electronic, and via formal project documentation. In order to be transformative, however, those perspectives will be filtered further through the lens of their formal, personalized assessment. It is a powerful tool which identifies individuals' internal needs and priorities. It translates those into descriptive profiles and reports, gifting users with valuable information about themselves and others. Paired with the course's real-world activities, it will provide uniquely strategic opportunities for communicating effectively and meaningfully-and with less conflict, both personally and professionally. What you will Learn At the end of this program, you will be able to: Identify basic elements of communication and explain how they affect teams Explore how your assessment style impacts you and how you communicate with people of other styles Infer how your style impacts the way(s) you send and interpret emails and instant messages Analyze real world email and instant messaging practices to determine how they affect communication and relationships Explore best practices for formal project communications and presentations Analyze how your assessment style and global diversity can contribute to both strong team communication and conflict Identify solutions for virtual team work communication challenges Foundation Concepts Communication as a foundation skill Elements of communication Communicating across media Targeting your audience How communication impacts team performance The Assessment Framework Overview of the assessment's approach Exploring assessment report Increasing your effectiveness with other assessment styles Email and Instant Messages Preferred communications and assessment styles The email brands we create Assessment styles and email Emotion and email Email guidelines and best practices Anatomy of an email The seven deadly email sins Instant messages and other interfaces Project Communications and Presentations Communicating across the project lifecycle Project templates Structuring a presentation Delivering a presentation Interpersonal and Team Communication Skills Communication styles and techniques Managing conflict in a project environment Styles and conflict Communication and global team leadership Virtual Communication Leading global virtual teams Virtual processes and technology Virtual team leadership

Project Communication Skills: Virtual In-House Training
By IIL Europe Ltd
Project Communication Skills: Virtual In-House Training Communication is the single most critical project success factor. When effective, projects get executed on time, within budget, and with objectives being met. But that isn't all. Strong communication also nurtures healthy team relationships. And in today's highly diverse world, where projects are often fast-paced, complex, and virtual, that is more important than ever. Strong communication skills foster cultural awareness, trust, and empathy. Together, they contribute greatly to project success-and ultimately, to future project success. In this course, participants will actively explore best communication practices from a variety of perspectives: in-person, virtual, electronic, and via formal project documentation. In order to be transformative, however, those perspectives will be filtered further through the lens of their formal, personalized assessment. It is a powerful tool which identifies individuals' internal needs and priorities. It translates those into descriptive profiles and reports, gifting users with valuable information about themselves and others. Paired with the course's real-world activities, it will provide uniquely strategic opportunities for communicating effectively and meaningfully-and with less conflict, both personally and professionally. What You Will Learn At the end of this program, you will be able to: Identify basic elements of communication and explain how they affect teams Explore how your assessment style impacts you and how you communicate with people of other styles Infer how your style impacts the way(s) you send and interpret emails and instant messages Analyze real world email and instant messaging practices to determine how they affect communication and relationships Explore best practices for formal project communications and presentations Analyze how your assessment style and global diversity can contribute to both strong team communication and conflict Identify solutions for virtual team work communication challenges Getting Started Foundation Concepts Communication as a foundation skill Elements of communication Communicating across media Targeting your audience How communication impacts team performance The Assessment Framework Overview of the assessment's approach Exploring assessment report Increasing your effectiveness with other assessment styles Email and Instant Messages Preferred communications and assessment styles The email brands we create Assessment styles and email Emotion and email Email guidelines and best practices Anatomy of an email The seven deadly email sins Instant messages and other interfaces Project Communications and Presentations Communicating across the project lifecycle Project templates Structuring a presentation Delivering a presentation Interpersonal and Team Communication Skills Communication styles and techniques Managing conflict in a project environment Styles and conflict Communication and global team leadership Virtual Communication Leading global virtual teams Virtual processes and technology Virtual team leadership
