- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
2093 Other courses in Helensburgh delivered Live Online
InDesign Basic to Essential Training Course
By Real Animation Works
Vectorworks Evening Course face to face One to one
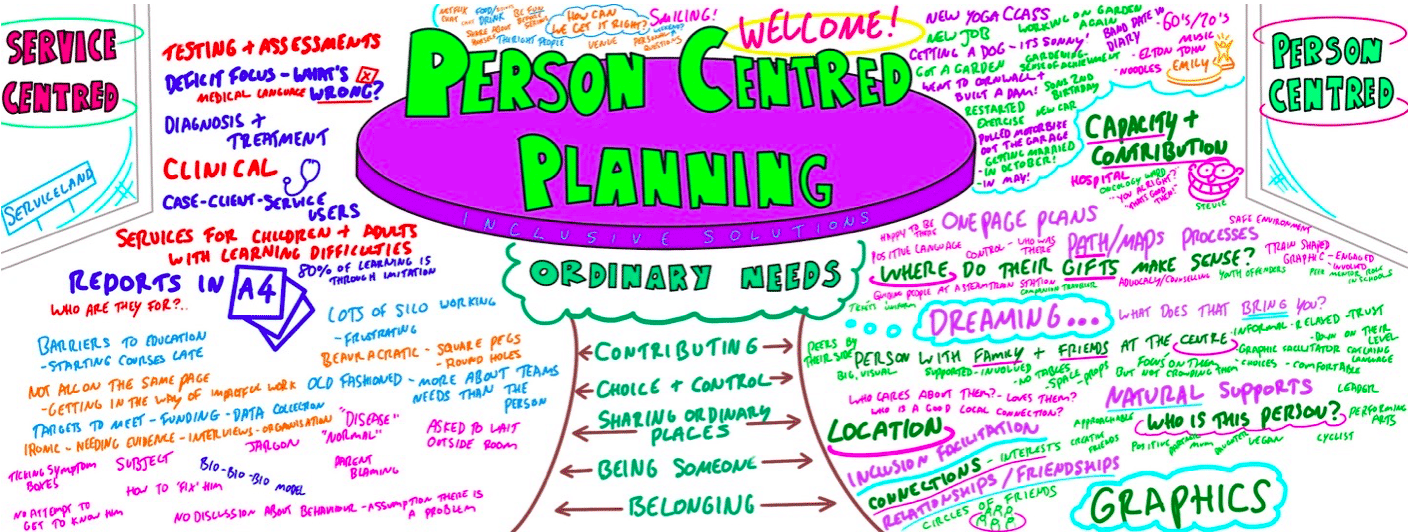
PERSON CENTRED PLANNING TRAINING
By Inclusive Solutions
Person Centred Planning (PCP) is a powerful tool for visioning, future planning and team building. It gets everyone on the same page and creates a progressive, constructive atmosphere so it is especially useful for people who are feeling ‘stuck’ or in a really desperate situation. The PCP processes we teach are called “PATH” and “MAPs”, and are both used for different situations. “To facilitate a group, family, team or organisation in thinking together around a given challenge or issue. Here is an opportunity to experience for real the person centred, futures planning tool – MAP/PATH” (Pearpoint, Forest, O’Brien. 1989). PCP can focus on an individual, with family and friends in the room supporting them, or focus on a group who want to set goals, and realise their potential as a team. PCP focuses on hopes and dreams, so is a very positive approach to planning, and utilises graphic facilitation, making it a very friendly way of working that is accessible to everyone. This unique, hands on PCP training course explores the difference between ‘person-centred thinking’ and ‘service-centred thinking’. Traditionally, we have not always listened deeply enough to the needs of those we are planning for. Often ‘medical model’ thinking dominates our planning for those with the most complex needs. Typically we plan ‘about’ rather than ‘with’ children and adults. We examine this ‘service centred’ approach that most professionals are used to, and question its limitations. This values based approach to inclusion will give participants the ‘theory’ behind why thinking and working in a person centred way is so important, and challenges people to strive for more for the people we are planning around. In addition to the knowledge and theory, this course empowers participants to facilitate their own Person Centred Plans using the PATH or MAPs process and provides the skills to do this effectively. Learning objectives Strengthen understanding of how to think in a person centred way Knowledge of the steps of PATH / MAPs process Ability to facilitate PATH/MAPs process Ability to graphically facilitate a PCP meeting Develop problem solving and planning skills Inclusive Solutions offer: We could provide training for a team of staff, or we could facilitate a PATH or MAP around a disabled person. We can also offer bespoke training packages, please enquire for more details. 1 day “Introduction to PCP” with up to 100 attendees focusing on ‘Person Centred Thinking’ – includes live demonstration of PATH or MAPs Process (for a member of the group / with a student and their family/friends). 2 day “PCP Skills training” – More skills focused, lots of practice. Includes Graphics academy, Process academy and Coaching (Best with under 30 attendees). 2 day “Introduction to PCP with Skills training” – includes live demonstration of PATH or MAPs process, Graphics academy, Process academy and Coaching (Best with under 30 attendees). Half day PATH or MAP for a disabled person, led by two experienced Inclusive Solutions facilitators. Full day PATH or MAP for a team, organisation or group such as a full school staff led by two experienced Inclusive Solutions facilitators. Typical Structure of 2-Day “Introduction to PCP with Skills” Training This course is most useful when delivered over 2 days so we have time to cover the ‘skills’ behind facilitating a PATH or a MAP. Here is an example of what usually happens. If you need us to, we can tailor any of our courses to suit your specific needs. Day 1 AM What makes a good welcome?Service centred thinking and working – what does it involve, how does it make people feel?Reflections on current practices – what is useful and what is harmful?Introduction to underpinning values of person centred thinking and working In depth exploration of the fundamentals of inclusion – encouraging identity, focusing on gifts and capacities Sharing success stories, and personal insight from experienced psychologistsShowcasing a number of practical PCP process in actionIntroduction to the “5 service accomplishments”, or “5 ordinary needs” PM Full PATH process demonstration, led by 2 experienced facilitators – one process facilitator and one graphic facilitatorVolunteers will make notes on what they see the facilitators doing and feedback at the end of the dayFeedback, Q&A Day 2 AM Graphics Academy – we will ease you into the world of graphic facilitation and show you how simple it really is – includes live coaching and graphics tutorial, then participants will practice on each other by facilitating the first 1 or 2 sections of the PATH Process Academy – we will give you some pointers about holding the group, and facilitating in an inclusive way, this is another chance to practice your new graphics skills PM The group is divided up, and volunteers are selected to facilitate PATH meetings The group then run the PATH’s simultaneously with an experienced coaches in the room to guide and to be available for questionsWe reconvene to feedback about the process and digest all we have learntBrief Q&A session and then final reflections
BGP training course description A study of BGP for non engineers working in the Internet. The course starts with a review of the basics of routers and routing tables and then moves on to a simple overview of how BPG works with a focus on BGP metrics influencing the route traffic takes through the Internet. Hands on with routers follow the major sessions to reinforce the theory. Note these hands on sessions are more demonstrations by the trainer but some can be followed along and done by delegates (e.g. looking at Internet routing tables.) What will you learn Explain how routing tables influence Internet traffic. Describe how BGP works. Explain the methods BGP can use to influence Internet traffic. Use traceroute, peeringdb, route collectors and looking glasses to analyse traffic flows. Explain the difference between bi lateral and multilateral peering using a route server. BGP training course details Who will benefit: Non technical staff wishing to know more about BGP. Prerequisites: None. Duration 1 day BGP training course contents Networks, routers and routing tables What is a network, what is a router, routing tables, static routes, routing protocols. When an ISP uses static routes and when they use BGP. IP addresses, subnet masks, groups of IP addresses. IPv6. Hands on: Showing a full routing table. Seeing traceroute being used. Basic BGP What's BGP? BGP versus other routing protocols, ASs, AS numbers. RIPE database, peeringdb. Hands on: Finding AS numbers. Showing simple BGP configuration and routing tables in an EVENG example. How BGP works Simple walk through of BGP incremental updates and how routes change when links go down. Hands on: Showing packets and route changes when a link goes down/comes up. BGP path selection Transit, peering, routing policy and route filtering. Longest matching rule in routing tables, route selection order, Local preference, AS prepend, MEDs. Hands on: Seeing BGP influencing traffic. Looking at peering policies in RIPE and peeringdb. Route servers What are route servers? LINX route servers, route server policy control and communities, What are route collectors, Looking glasses. Hands on: Seeing the LINX route server details in peeringdb, using a looking glass.

Work Breakdown Structures: In-House Training
By IIL Europe Ltd
Work Breakdown Structures: In-House Training It's amazing how often project managers begin the project planning process by making an outlined list of every task they believe will be required to complete a project and then proclaim they have created the work breakdown structure (WBS) for the project. The result is a list of hundreds, or even thousands of tasks, many of them having durations of a few days or a few hours. Essentially, what they have done is create a 'to do' list, which they then use as a 'checklist' to measure progress. This approach leads to, and even encourages, micromanagement of the resources working on the project without consideration of more critical aspects of project management such as: requirements management, risk management, procurement management, estimating, scheduling, executing, and controlling. Further, it makes it impossible to see the big picture, at levels of detail, in keeping with the needs of sponsors, clients, project and functional managers, team leaders, and project performers. Join us for this exciting program and learn how to use the WBS to make better-informed business decisions. What You Will Learn You will learn how to: Describe the need for a project WBS Describe the WBS role in the project Gain practical experience in the development, decomposition, and use of the WBS Determine the appropriate level of detail in the WBS. Explain how the WBS integrates with project requirements, risk, procurement, estimating, scheduling, and overall project execution. Provide the basic tools to enhance efficient re-use of key information in your future projects Foundation Concepts Key definitions History of the WBS Importance of the WBS Overall structure Terminology Other breakdown structures WBS tools WBS & Scope Project scope management processes Specification of the project objectives WBS design based on project deliverable WBS decomposition process and 'The 100% rule' Work Packages and Control Accounts WBS & Risk Risk management planning and WBS Risk identification to enhance the WBS Risk analysis and the WBS Risk responses and updating the WBS Implementing risk response and Monitoring risks and the WBS WBS & Estimating Use of WBS in the estimating process Components and work packages Sizing and algorithmic estimates WBS & Scheduling Component Scheduling - High-Level Milestones WBS activity decomposition WBS elements dependencies Work Package Level Schedules Responsibility assignment matrix WBS & Execution and Control Earned Value Management and tracking of work performance Progress reports, forecasts, and corrective and preventive actions used to manage work performance Necessary information to close out a project

Kick Start Your Career with CompTIA's Data Analysis Certification - Live Classes
5.0(1)By Media Tek Training Solutions Ltd
Get job ready with CompTIA's Data Analysis Certification. Live Classes - Career Guidance - Exam Included.

MS-102T00 Microsoft 365 Administrator Essentials
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for persons aspiring to the Microsoft 365 Administrator role and have completed at least one of the Microsoft 365 role-based administrator certification paths. This course covers the following key elements of Microsoft 365 administration: Microsoft 365 tenant management, Microsoft 365 identity synchronization, and Microsoft 365 security and compliance. In Microsoft 365 tenant management, you learn how to configure your Microsoft 365 tenant, including your organizational profile, tenant subscription options, component services, user accounts and licenses, security groups, and administrative roles. You then transition to configuring Microsoft 365, with a primary focus on configuring Office client connectivity. Finally, you explore how to manage user-driven client installations of Microsoft 365 Apps for enterprise deployments. The course then transitions to an in-depth examination of Microsoft 365 identity synchronization, with a focus on Microsoft Entra Connect and Connect Cloud Sync. You learn how to plan for and implement each of these directory synchronization options, how to manage synchronized identities, and how to implement password management in Microsoft 365 using multifactor authentication and self-service password management. In Microsoft 365 security management, you begin examining the common types of threat vectors and data breaches facing organizations today. You then learn how Microsoft 365?s security solutions address each of these threats. You are introduced to the Microsoft Secure Score, as well as to Microsoft Entra ID Protection. You then learn how to manage the Microsoft 365 security services, including Exchange Online Protection, Safe Attachments, and Safe Links. Finally, you are introduced to the various reports that monitor an organization?s security health. You then transition from security services to threat intelligence; specifically, using Microsoft 365 Defender, Microsoft Defender for Cloud Apps, and Microsoft Defender for Endpoint. Once you have this understanding of Microsoft 365?s security suite, you then examine the key components of Microsoft 365 compliance management. This begins with an overview of all key aspects of data governance, including data archiving and retention, Microsoft Purview message encryption, and data loss prevention (DLP). You then delve deeper into archiving and retention, paying particular attention to Microsoft Purview insider risk management, information barriers, and DLP policies. You then examine how to implement these compliance features by using data classification and sensitivity labels. Prerequisites Completed a role-based administrator course such as Messaging, Teamwork, Security, Compliance, or Collaboration. A proficient understanding of DNS and basic functional experience with Microsoft 365 services. A proficient understanding of general IT practices. A working knowledge of PowerShell. 1 - Configure your Microsoft 365 experience Explore your Microsoft 365 cloud environment Configure your Microsoft 365 organizational profile Manage your tenant subscriptions in Microsoft 365 Integrate Microsoft 365 with customer engagement apps Complete your tenant configuration in Microsoft 365 2 - Manage users, licenses, and mail contacts in Microsoft 365 Determine the user identity model for your organization Create user accounts in Microsoft 365 Manage user account settings in Microsoft 365 Manage user licenses in Microsoft 365 Recover deleted user accounts in Microsoft 365 Perform bulk user maintenance in Microsoft Entra ID Create and manage guest users Create and manage mail contacts 3 - Manage groups in Microsoft 365 Examine groups in Microsoft 365 Create and manage groups in Microsoft 365 Create dynamic groups using Azure rule builder Create a Microsoft 365 group naming policy Create groups in Exchange Online and SharePoint Online 4 - Add a custom domain in Microsoft 365 Plan a custom domain for your Microsoft 365 deployment Plan the DNS zones for a custom domain Plan the DNS record requirements for a custom domain Create a custom domain in Microsoft 365 5 - Configure client connectivity to Microsoft 365 Examine how automatic client configuration works Explore the DNS records required for client configuration Configure Outlook clients Troubleshoot client connectivity 6 - Configure administrative roles in Microsoft 365 Explore the Microsoft 365 permission model Explore the Microsoft 365 admin roles Assign admin roles to users in Microsoft 365 Delegate admin roles to partners Manage permissions using administrative units in Microsoft Entra ID Elevate privileges using Microsoft Entra Privileged Identity Management Examine best practices when configuring administrative roles 7 - Manage tenant health and services in Microsoft 365 Monitor the health of your Microsoft 365 services Monitor tenant health using Microsoft 365 Adoption Score Monitor tenant health using Microsoft 365 usage analytics Develop an incident response plan Request assistance from Microsoft 8 - Deploy Microsoft 365 Apps for enterprise Explore Microsoft 365 Apps for enterprise functionality Explore your app compatibility by using the Readiness Toolkit Complete a self-service installation of Microsoft 365 Apps for enterprise Deploy Microsoft 365 Apps for enterprise with Microsoft Configuration Manager Deploy Microsoft 365 Apps for enterprise from the cloud Deploy Microsoft 365 Apps for enterprise from a local source Manage updates to Microsoft 365 Apps for enterprise Explore the update channels for Microsoft 365 Apps for enterprise Manage your cloud apps using the Microsoft 365 Apps admin center 9 - Analyze your Microsoft 365 workplace data using Microsoft Viva Insights Examine the analytical features of Microsoft Viva Insights Explore Personal insights Explore Team insights Explore Organization insights Explore Advanced insights 10 - Explore identity synchronization Examine identity models for Microsoft 365 Examine authentication options for the hybrid identity model Explore directory synchronization 11 - Prepare for identity synchronization to Microsoft 365 Plan your Microsoft Entra deployment Prepare for directory synchronization Choose your directory synchronization tool Plan for directory synchronization using Microsoft Entra Connect Plan for directory synchronization using Microsoft Entra Connect cloud sync 12 - Implement directory synchronization tools Configure Microsoft Entra Connect prerequisites Configure Microsoft Entra Connect Monitor synchronization services using Microsoft Entra Connect Health Configure Microsoft Entra Connect cloud sync prerequisites Configure Microsoft Entra Connect cloud sync 13 - Manage synchronized identities Manage users with directory synchronization Manage groups with directory synchronization Use Microsoft Entra Connect Sync Security Groups to help maintain directory synchronization Configure object filters for directory synchronization Explore Microsoft Identity Manager Troubleshoot directory synchronization 14 - Manage secure user access in Microsoft 365 Manage user passwords Enable pass-through authentication Enable multifactor authentication Enable passwordless sign-in with Microsoft Authenticator Explore self-service password management Explore Windows Hello for Business Implement Microsoft Entra Smart Lockout Implement conditional access policies Explore Security Defaults in Microsoft Entra ID Investigate authentication issues using sign-in logs 15 - Examine threat vectors and data breaches Explore today's work and threat landscape Examine how phishing retrieves sensitive information Examine how spoofing deceives users and compromises data security Compare spam and malware Examine account breaches Examine elevation of privilege attacks Examine how data exfiltration moves data out of your tenant Examine how attackers delete data from your tenant Examine how data spillage exposes data outside your tenant Examine other types of attacks 16 - Explore the Zero Trust security model Examine the principles and components of the Zero Trust model Plan for a Zero Trust security model in your organization Examine Microsoft's strategy for Zero Trust networking Adopt a Zero Trust approach 17 - Explore security solutions in Microsoft 365 Defender Enhance your email security using Exchange Online Protection and Microsoft Defender for Office 365 Protect your organization's identities using Microsoft Defender for Identity Protect your enterprise network against advanced threats using Microsoft Defender for Endpoint Protect against cyber attacks using Microsoft 365 Threat Intelligence Provide insight into suspicious activity using Microsoft Cloud App Security Review the security reports in Microsoft 365 Defender 18 - Examine Microsoft Secure Score Explore Microsoft Secure Score Assess your security posture with Microsoft Secure Score Improve your secure score Track your Microsoft Secure Score history and meet your goals 19 - Examine Privileged Identity Management Explore Privileged Identity Management in Microsoft Entra ID Configure Privileged Identity Management Audit Privileged Identity Management Control privileged admin tasks using Privileged Access Management 20 - Examine Azure Identity Protection Explore Azure Identity Protection Enable the default protection policies in Azure Identity Protection Explore the vulnerabilities and risk events detected by Azure Identity Protection Plan your identity investigation 21 - Examine Exchange Online Protection Examine the anti-malware pipeline Detect messages with spam or malware using Zero-hour auto purge Explore anti-spoofing protection provided by Exchange Online Protection Explore other anti-spoofing protection Examine outbound spam filtering 22 - Examine Microsoft Defender for Office 365 Climb the security ladder from EOP to Microsoft Defender for Office 365 Expand EOP protections by using Safe Attachments and Safe Links Manage spoofed intelligence Configure outbound spam filtering policies Unblock users from sending email 23 - Manage Safe Attachments Protect users from malicious attachments by using Safe Attachments Create Safe Attachment policies using Microsoft Defender for Office 365 Create Safe Attachments policies using PowerShell Modify an existing Safe Attachments policy Create a transport rule to bypass a Safe Attachments policy Examine the end-user experience with Safe Attachments 24 - Manage Safe Links Protect users from malicious URLs by using Safe Links Create Safe Links policies using Microsoft 365 Defender Create Safe Links policies using PowerShell Modify an existing Safe Links policy Create a transport rule to bypass a Safe Links policy Examine the end-user experience with Safe Links 25 - Explore threat intelligence in Microsoft 365 Defender Explore Microsoft Intelligent Security Graph Explore alert policies in Microsoft 365 Run automated investigations and responses Explore threat hunting with Microsoft Threat Protection Explore advanced threat hunting in Microsoft 365 Defender Explore threat analytics in Microsoft 365 Identify threat issues using Microsoft Defender reports 26 - Implement app protection by using Microsoft Defender for Cloud Apps Explore Microsoft Defender Cloud Apps Deploy Microsoft Defender for Cloud Apps Configure file policies in Microsoft Defender for Cloud Apps Manage and respond to alerts in Microsoft Defender for Cloud Apps Configure Cloud Discovery in Microsoft Defender for Cloud Apps Troubleshoot Cloud Discovery in Microsoft Defender for Cloud Apps 27 - Implement endpoint protection by using Microsoft Defender for Endpoint Explore Microsoft Defender for Endpoint Configure Microsoft Defender for Endpoint in Microsoft Intune Onboard devices in Microsoft Defender for Endpoint Manage endpoint vulnerabilities with Microsoft Defender Vulnerability Management Manage device discovery and vulnerability assessment Reduce your threat and vulnerability exposure 28 - Implement threat protection by using Microsoft Defender for Office 365 Explore the Microsoft Defender for Office 365 protection stack Investigate security attacks by using Threat Explorer Identify cybersecurity issues by using Threat Trackers Prepare for attacks with Attack simulation training 29 - Examine data governance solutions in Microsoft Purview Explore data governance and compliance in Microsoft Purview Protect sensitive data with Microsoft Purview Information Protection Govern organizational data using Microsoft Purview Data Lifecycle Management Minimize internal risks with Microsoft Purview Insider Risk Management Explore Microsoft Purview eDiscovery solutions 30 - Explore archiving and records management in Microsoft 365 Explore archive mailboxes in Microsoft 365 Enable archive mailboxes in Microsoft 365 Explore Microsoft Purview Records Management Implement Microsoft Purview Records Management Restore deleted data in Exchange Online Restore deleted data in SharePoint Online 31 - Explore retention in Microsoft 365 Explore retention by using retention policies and retention labels Compare capabilities in retention policies and retention labels Define the scope of a retention policy Examine the principles of retention Implement retention using retention policies, retention labels, and eDiscovery holds Restrict retention changes by using Preservation Lock 32 - Explore Microsoft Purview Message Encryption Examine Microsoft Purview Message Encryption Configure Microsoft Purview Message Encryption Define mail flow rules to encrypt email messages Add organizational branding to encrypted email messages Explore Microsoft Purview Advanced Message Encryption 33 - Explore compliance in Microsoft 365 Plan for security and compliance in Microsoft 365 Plan your beginning compliance tasks in Microsoft Purview Manage your compliance requirements with Compliance Manager Examine the Compliance Manager dashboard Analyze the Microsoft Compliance score 34 - Implement Microsoft Purview Insider Risk Management Explore insider risk management Plan for insider risk management Explore insider risk management policies Create insider risk management policies Investigate insider risk management activities and alerts Explore insider risk management cases 35 - Implement Microsoft Purview Information Barriers Explore Microsoft Purview Information Barriers Configure information barriers in Microsoft Purview Examine information barriers in Microsoft Teams Examine information barriers in OneDrive Examine information barriers in SharePoint 36 - Explore Microsoft Purview Data Loss Prevention Examine Data Loss Prevention Explore Endpoint data loss prevention Examine DLP policies View DLP policy results Explore DLP reports 37 - Implement Microsoft Purview Data Loss Prevention Plan to implement Microsoft Purview Data Loss Protection Implement Microsoft Purview's default DLP policies Design a custom DLP policy Create a custom DLP policy from a template Configure email notifications for DLP policies Configure policy tips for DLP policies 38 - Implement data classification of sensitive information Explore data classification Implement data classification in Microsoft 365 Explore trainable classifiers Create and retrain a trainable classifier View sensitive data using Content explorer and Activity explorer Detect sensitive information documents using Document Fingerprinting 39 - Explore sensitivity labels Manage data protection using sensitivity labels Explore what sensitivity labels can do Determine a sensitivity label's scope Apply sensitivity labels automatically Explore sensitivity label policies 40 - Implement sensitivity labels Plan your deployment strategy for sensitivity labels Examine the requirements to create a sensitivity label Create sensitivity labels Publish sensitivity labels Remove and delete sensitivity labels Additional course details: Nexus Humans MS-102T00: Microsoft 365 Administrator training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the MS-102T00: Microsoft 365 Administrator course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Awareness of Safeguarding
By Madeleys First Aid Plus
RQF level 1 Awareness of Safeguarding The RQF Level 1 Awareness of Safeguarding course is designed to provide individuals with a basic understanding of safeguarding principles and practices. It aims to raise awareness about the importance of safeguarding and promote the well-being and protection of vulnerable individuals, such as children, young people, and adults at risk. The course covers the following topics: Introduction to Safeguarding: Definition and importance of safeguarding. Key legislation, policies, and guidance related to safeguarding. Roles and responsibilities of individuals and organizations in safeguarding. Types of Abuse and Neglect: Overview of different types of abuse, including physical, emotional, sexual, and financial abuse. Recognizing signs and indicators of abuse and neglect. Understanding the impact of abuse on individuals' well-being. Vulnerable Groups: Identifying vulnerable groups, such as children, young people, older adults, and individuals with disabilities or mental health issues. Understanding the specific safeguarding concerns and considerations for each group. Reporting and Responding to Safeguarding Concerns: Procedures for reporting safeguarding concerns or disclosures. Understanding the importance of maintaining confidentiality and handling sensitive information appropriately. Responding to safeguarding concerns in a timely and appropriate manner. Promoting Safeguarding and Preventing Abuse: Strategies for promoting a safe and inclusive environment. Recognizing potential risk factors and implementing preventative measures. Understanding the importance of creating a culture of safeguarding within organizations. Multi-Agency Collaboration: Collaboration between different agencies and organizations involved in safeguarding, such as social services, law enforcement, and healthcare. Sharing information and working together to ensure effective safeguarding practices. Case Studies and Scenarios: Reviewing case studies and scenarios to apply safeguarding principles and practices. Analysing potential safeguarding dilemmas and decision-making processes. Personal Responsibilities: Recognizing personal boundaries and limitations when working with vulnerable individuals. Understanding the importance of self-care and managing emotional well-being when dealing with safeguarding issues. It is important to ensure that the course meets local safeguarding guidelines and requirements. Suitability - Who should attend? The RQF Level 1 Awareness of Safeguarding course is suitable for a wide range of individuals who may come into contact with vulnerable individuals or have a general interest in understanding safeguarding principles. Here are some key groups of people who should attend the course: Employees and Staff: The course is relevant for employees and staff members across various sectors and industries, including but not limited to education, healthcare, social services, hospitality, sports and recreation, and community organizations. It helps them develop a basic understanding of safeguarding principles and their responsibilities in ensuring the well-being and protection of vulnerable individuals they may encounter in their work. Volunteers: Individuals who volunteer their time and services in organizations that work with vulnerable individuals should attend the course. It equips them with essential knowledge and awareness of safeguarding issues, helping them provide appropriate support and maintain the safety and dignity of those they interact with. Parents and Caregivers: The course can benefit parents, guardians, and caregivers by providing them with a foundation in safeguarding principles. It helps them recognize potential risks and signs of abuse or neglect, enabling them to create safer environments for the children or vulnerable individuals under their care. Community and Youth Workers: Individuals involved in community work, youth organizations, or youth clubs should attend the course to enhance their understanding of safeguarding. It enables them to promote the well-being and safety of young people and recognize signs of potential abuse or exploitation. Volunteers or Trustees of Charitable Organizations: Individuals serving as volunteers or trustees in charitable organizations that work with vulnerable populations can benefit from the course. It helps them fulfill their responsibilities in safeguarding the individuals the organization serves and ensures they are aware of their legal and ethical obligations. General Public: The course is open to the general public as it provides valuable knowledge and awareness of safeguarding principles. It can benefit individuals who have an interest in understanding the rights and protection of vulnerable individuals in society. It's important to note that the RQF Level 1 Awareness of Safeguarding course provides foundational knowledge and awareness. For individuals who require more in-depth training or who have specific safeguarding roles or responsibilities, higher-level courses may be more suitable. Outcome / Qualification etc. Certification The qualification does not have an expiry date but refresher training and keeping up to date with changes to policies, procedures and new legislation through ongoing CPD is vital. Training Course Content Module 1 Introductions Module 2 Safeguarding legislation and guidance Module 3 Roles and responsibilities Module 4 Abuse and neglect Module 5 Identifying concerns and disclosure Module 6 Making judgements Module 7 Reporting concerns Module 8 Course closure and assessment MODULE 1 INTRODUCTIONS Session content Trainer/Assessor introduction Learner introductions Course syllabus Learning outcomes and assessment criteria Session duration 20 minutes MODULE 2 SAFEGUARDING LEGISLATION AND GUIDANCE Session content Introduction to safeguarding Definitions Assessment framework Safeguarding statistics Safeguarding legislation and guidance Rights of a child/adult at risk Session duration 40 minutes MODULE 3 ROLES AND RESPONSIBILITIES Session content Safeguarding partnerships Local authority safeguarding officer Social care services Multi-agency safeguarding hubs Organisational safeguarding policies Safeguarding lead Session duration 30 minutes MODULE 4 ABUSE AND NEGLECT Session content Definitions Types of abuse and neglect Physical abuse Emotional abuse Sexual abuse Neglect Signs and indicators Parent/carer abuse Radicalisation FGM Forced marriage Modern slavery County line gangs Electronic media abuse - Internet and social networking dangers Session duration 50 minutes MODULE 5 IDENTIFYING CONCERNS AND DISCLOSURE Session content Identifying concerns Being a point of disclosure Recording disclosure information Session duration 20 minutes MODULE 6 MAKING JUDGEMENTS Session content Child development needs Identifying a safeguarding concern Group activity making judgements Session duration 30 minutes MODULE 7 REPORTING CONCERNS Session content Silencing factors Barriers to raising concerns Reporting concerns Importance of sharing concerns Session duration 20 minutes MODULE 8 COURSE CLOSURE AND ASSESSMENT Session content Course summary Assessment paper Course evaluation Course closure Session duration 30 minutes Course delivery details Qualification delivery The qualification has 4 assigned guided learning hours (GLH) and 5 hours total qualification time (TQT). GLH indicates the number of classroom contact hours that the learner will undertake. TQT includes GLH but also takes into account any unsupervised learning and is an estimate of how long the average learner will take to complete the qualification. The minimum classroom contact time of 4 hours should be delivered over a minimum of half a day. The course can be spread over a maximum of 2 weeks, ensuring that each session is a minimum of two hours. The class ratio for this qualification is a maximum of 16 learners to 1 Trainer/Assessor Why choose Madeleys First Aid Plus Founded in 2021 after Louise left 30 years in the NHS as an Advanced practitioner in A&E/ITU, had spent 1.5 years in Covid ITU Won FSB Best start-up business in the West Midlands in May 2023 Now trained 100's of delegates in Physical and Mental Health First Aid Expenses Travel costs and lunch required, there are many cafes and sandwich bars here in Much Wenlock to buy your lunch, you may eat it in the training room. All training material, books, qualification certificates are included in the price Continuing Studies The RQF Level 1 Awareness of Safeguarding course serves as an introductory course that provides individuals with a basic understanding of safeguarding principles. While it is a standalone qualification, individuals who complete the course may choose to progress further in their safeguarding training and education. Here are some potential progression options: RQF Level 2 Award in Safeguarding: This qualification builds upon the knowledge gained in the Level 1 course and provides a more comprehensive understanding of safeguarding principles, policies, and procedures. It covers topics such as risk assessment, responding to safeguarding concerns, and effective communication in safeguarding contexts. Specialized Safeguarding Courses: Individuals who wish to focus on specific areas of safeguarding can pursue specialized courses related to their field of interest. These courses may include Child Protection, Adult Safeguarding, Domestic Abuse Awareness, Online Safety, or Safeguarding in Healthcare. Specialized courses delve deeper into the specific risks, regulations, and best practices associated with safeguarding vulnerable individuals in those particular contexts. Safeguarding Training for Specific Professions: Many professions have specific safeguarding training requirements tailored to their sector. For example, teachers may need to complete safeguarding training specific to the education setting, healthcare professionals may have training focused on safeguarding vulnerable patients, and social workers may have specialized safeguarding training in line with their role. Progression may involve undertaking profession-specific safeguarding courses or qualifications. Safeguarding Leadership and Management Training: Individuals in supervisory or managerial positions may consider pursuing training that focuses on the leadership and management aspects of safeguarding. This can include courses on developing and implementing safeguarding policies and procedures, managing safeguarding incidents, conducting internal investigations, and providing guidance and support to staff. Continued Professional Development (CPD): Engaging in ongoing CPD activities is essential for staying updated with the latest developments in safeguarding practices and policies. Individuals can attend conferences, workshops, or seminars related to safeguarding, child protection, or specific areas of interest within the field. This allows for continued learning and networking with other professionals. Higher Education: Individuals who wish to pursue a more in-depth study of safeguarding can consider higher education programs in social work, psychology, criminology, or related fields. These programs provide comprehensive knowledge and training in safeguarding practices, policies, and research. They may lead to professional certifications or degrees that enhance career opportunities in safeguarding roles. It's important for individuals to research and explore progression options that align with their specific career goals, interests, and local requirements. Different countries or regions may have varying certification or training requirements for safeguarding roles, so it's advisable to check with relevant regulatory bodies or professional associations for specific guidance.

Agile Scrum as a Delivery Method - Online Course - Essentials (C-ASDM) for Government and Public Sector
By UK Scrum Academy
Agile is not what you do, Agile is what you become! An introduction to the essentials of Agile Scrum as a delivery method. The same learning objectives as used in central government & public sector digital delivery projects. Agile is not what you do, Agile is what you become! Since 2012, all government departments have been required to use the Agile approach to project management, to build and run new digital services. As you begin your Agile journey, one of your first challenges will be understanding the rules and roles that support Agile delivery, some of the most frequently asked questions are "Which Agile framework is applicable to our business operating model?" or, "Is the Project Manager role equivalent to that of theProduct Owner?" and, "What does a Scrum Master do?" A strong corporate culture not accustomed to the Agile mindset can also be a difficult environment in which to implement Agile methods. In some cases, the company’s culture and practices may reward non-Agile milestones while inadvertently discouraging Agile success. This intensive two-day training course combines PowerPoint presentations, informal discussions and practical exercises to introduce you to Agile Scrum as a Delivery Method, without the impending pressure of having to pass a formal certification examination. Previous experience of Agile delivery is not a pre-requisite to attending this course, although it is assumed delegates have previously attended the Primer course, or have some understanding of Agile Scrum terms and practices. This course, designed by Agile Scrum practitioners and coaches with specialist experience of working on GDS (Government Digital Service) Service Standards compliant government and public sector projects has been accredited by The CPD Certification Service and is now available outside its usual central government and public sector digital delivery setting. Who this course is for Service and Programme Managers If you are a Service Manager or Programm Manager who wants to explore the benefits of transitioning to Agile ways of working and want to understand how your existing business processes and resource landscape will fit into an Agile delivery model, then this course aims to provide you with enough information to enable you to make an informed decision. Career ambitions If you are new to Agile and your intention is to pursue a career either as an Agile Scrum Master or Agile Product Owner, you will hopefully be provided with enough knowledge to enable you to determine which role best suits your Agile career ambitions. Frequently Asked Questions How this course differs from other Agile courses Delegates will learn the 'How', not just the 'What'! This course has been designed by highly experienced Agile practitioners and coaches with specialist real-life experience of working on GDS (Government Digital Service) Service Design Standard projects. Delegates will find that the learning objectives are significantly more detailed than with other Agile courses which only focus on teaching the learning objectives of The Scrum Guide. Delegates must take the certification assessment. No! During enrolment, delegates can opt out of taking the C-ASDM certification assessment. The online Agile Scrum as a Delivery Method – Essentials course quiz is optional Absolutely! Delegates are provided access to the online Agile knowledge quiz which accompanies the Agile Scrum as a Delivery Method – Essentials course. The quiz helps delegates gauge their level of attainment but is entirely optional. Delegates can take the certification assessment without enrolling on the course. Yes! Delegates with existing Agile project delivery experience can choose to take the certification assessment without enrolling on the course. I will receive my certificate as soon as I have completed the course You will initially receive an Assessment Completion report after completing the assessment. The report details the certification status: 'Pass' or 'Fail', and includes information on which questions were answered incorrectly. Your certificate is issued by the CPD Certification Service approximately four-to six-weeks after successfully completing and passing the C-ASDM Certification Assessment. A CPD certification is recognised by employers Yes! CPD certification is recognised by private and public sector employers, and in central government departments as a valuable way to evaluate the skills of an individual, and the quality of the learning activities. Listing your CPD certification as well as the number of CPD Points you have achieved on your CV is essentially showcasing your achievements in continuing your professional development. One CPD Point is equivalent to an hour of training CPD points are units that quantify time, and the quality of learning and development activities. Delegates will earn 3 CPD Points upon successful completion of the C-ASDM Certification Assessment or 13 CPD Points after completing the two-day course. My CPD certificate will expire after three years Your certificate will not expire however, best practice suggests a renewal after three years. You can do this by enrolling on the C-ASDM course to ensure your knowledge of Agile as a Delivery Method is up to date. Service features Two-day Agile Scrum training course The course uses eCommerce and other Business Case examples for context Optional online CPD certification assessment Optional Agile knowledge quiz to help delegates gauge level of attainment Online Retrospective feedback to enable continuous course improvements. Service benefits Delegates will understand the concepts and benefits of Agile Scrum development Scrum team roles and role accountabilities INVEST-compliant User Stories and BDD formatted Acceptance Criteria Agile approach to incremental project delivery Agile artefacts and Agile reports (burn-down & burn-up charts) Agile Events & Scrum rules Comparison: Agile methodologies (Lean, XP, SAFe & Scrum) Use of Kanban for workflow management Government Digital Service (GDS) Service Standards and Service Assessment Be able to communicate the ideals of Agile to stakeholders Service Agenda General knowledge Agile Delivery 101 Scrum process and sprints Applicability of Scrum Agile Manifesto Scrum roles and accountabilities Overview of Scrum roles (Core & Ancillary) Scrum Master role and role responsibilities Scrum Product Owner role and role responsibilities Scrum team Scrum events Sprint Planning Daily Scrums Sprint Reviews Sprint Retrospectives Scrum artefacts Product Backlog Sprint Backlog Increments Scrum Reports Burn-down and Burn-up Charts Scaling Scrum Working with multiple Scrum teams Working with distributed Scrum teams GDS (Government Digital Service) Service Standards Service Assessments Risks and challenges Risks and challenges of transitioning to Agile delivery Frequently asked questions Discussion on frequently asked Agile questions Agile knowledge quiz Examples of the multiple-choice questions in the optional online quiz On-going support Email support No Telephone support No Webchat support No Online support No Community Support Yes! Delegates are offered access to our private online 'Community of Agile Scrum Practitioners'. Delegates who achieve the pass mark for CPD certification are additionally offered access to our private 'Certified Scrum Practitioners’ Guild', a private Slack community of like-minded Agile professionals.

Program Management Skills: Virtual In-House Training
By IIL Europe Ltd
Program Management Skills: Virtual In-House Training Program managers coordinate and give oversight to the efforts of marketing groups, project teams, product delivery, maintenance and support, operations and staff from various functional groups, including suppliers, business partners, and other external bodies. The goal is to ensure that proposed business transformation, through the delivery of complex products and processes, is implemented to realize the organization's strategic benefits and objectives, for which the program was selected. The goals of this course are twofold: To provide participants with key program management principles and techniques, recognized as best practices, to enable more effective program management; and to leverage core elements of the program management life cycle, processes, tools and techniques, to enable program management effectiveness. The participant will learn and apply the principles of program management through discussions, activities, and case study exercises. What You Will Learn At the end of this workshop, you will be able to: Maximize the transformational impact of a program according to the business needs Explain management principles and techniques and apply them within a program context Implement program governance and organization that will produce expected benefits Plan for and manage benefit realization, risks, issues, and quality Manage component projects' interdependencies that are linked to both program and strategic objectives Engage program stakeholders effectively. Improve communication and action planning effectiveness for programs in organizations Getting Started Introductions Course structure Course goals and objectives Foundation Concepts Fundamental definitions and concepts Program challenges and benefits Program best practices and success criterion Stakeholder management Governance: program management office and program boards Standard for Program Management overview Vision, Leadership, and the Business Case What is vision, why, and how? Leadership vs. Management Program business case Program Organization and Governance Program organization Program governance Program board roles and responsibilities Benefits Management Benefits explored Benefits management Benefits realization Program Management Planning Program management plan Program blueprint and roadmap Program component dossier Program tranches Program estimating Program scheduling Program Monitoring and Controlling Program Control - An Overview Program Monitoring and Controlling Monitoring and Controlling Transition Program Risk and Issue Management Risk and issue management overview Program risk management Program issue management Program Quality Management Program quality management overview Program quality management principles Program Stakeholder Management Stakeholder engagement overview Stakeholder engagement planning EI, trust, communication and stakeholder engagement Program Closure and Benefits Sustainment Program closure overview Closing the program Program benefits sustainment Summary What did we learn, and how can we implement this in our work environments?