- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
15668 Open courses
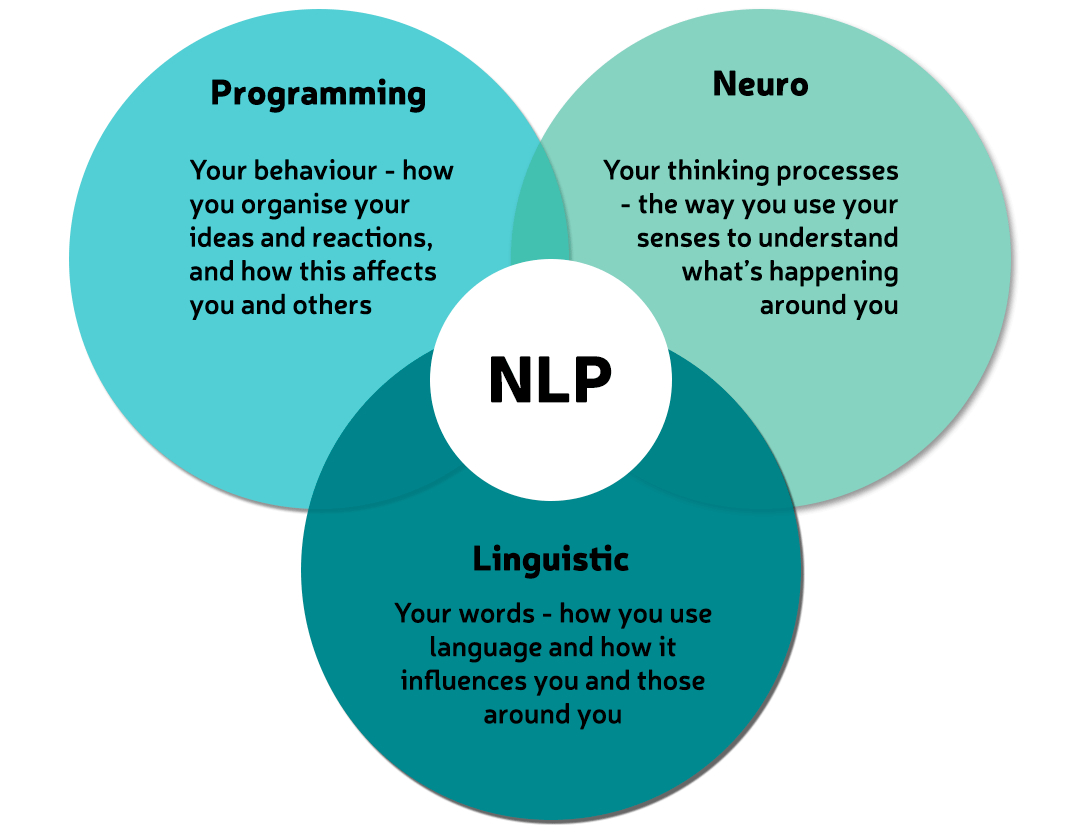
NLP Diploma
By Proactive NLP Ltd
NLP Diploma training & certification with Proactive NLP Ltd is your first step towards self-mastery. Start getting what you want from life.
Level 3 Diploma in Health & Social Care- Ofqual Regulated
By Kingston Open College
Premium Bundle of all Time | Ofqual Regulation + ATHE Awards + CPD Accreditation | Assessment & Tutor Support Included

Autodesk Maya 10 hrs One to One training
By Real Animation Works
Autodesk face to face training customised and bespoke. Certified Tutors.

Level 5 Diploma in Graphic Design - QLS Endorsed
By Kingston Open College
QLS Endorsed + CPD QS Accredited - Dual Certification | Instant Access | 24/7 Tutor Support | All-Inclusive Cost

Level 4 Diploma in Play Therapy - QLS Endorsed
By Kingston Open College
QLS Endorsed + CPD QS Accredited - Dual Certification | Instant Access | 24/7 Tutor Support | All-Inclusive Cost

Easter Break Skateboarding Camp for kids - book now for hours of fun
By Best Foot Forward Skate Academy
Easter Holiday Skatecamp booking now open 🛹 Our skate camps return this April: Date 🗓 - 1st - 12th April Monday-Friday Time 🕘 - 9am-12pm Location📍- Meanwhile Gardens Skatepark, 27 Elkstone Road W10 5NT Price 💷 - £50 per child per morning, with a discounted week pass of 5 days for price of 4 Who can join 🤸🏻♂️🤸♀️ - Boys and Girls aged 5 to 15, 4 year olds who are more experienced on their skateboards can be considered. All abilities welcome but some skateboarding experience ideal in these group settings. All equipment available for those who don't have their own Skateboard, helmets or pads. Bookings are weather dependant as skateboarding in wet conditions is very dangerous, refunds and rescheduling available if sessions cancelled.

Certificate in Corporate Governance
By The Association of Governance, Risk & Compliance
Whether you’re a board member or just curious about corporate governance, this AGRC certificate is for you! Learn what it takes for any firm to build and maintain a robust, dependable, and responsible corporate governance backbone with this self-paced, online certificate delivered by LGCA.

Develop your machine polishing skills. Ideal for those wanting to learn a specific machine polishing style, our Introduction to Machine Polishing for Professionals one-day course is a perfect starting point to get you using machine polishers in a safe, controlled environment. If you already use machines for correction work, it's an opportunity to reset your skills, pick up practical tips and advice, and increase your efficiency with either a different style or one you have used, but were never comfortable with. Develop your technique in a controlled scenario and the ability to make mistakes and learn, with instructor-led training selecting from a huge range of machines, and become proficient in machine polishing all types of surfaces. Learn defect assessment and solutions, lighting, compound technology, machine handling, and efficiency tips for professional results. Our one-day introduction to machine polishing for professionals course is ideal for those who have either; Have never needed to pick up a machine before Have always used only one type of machine Have restricted themselves to entry-level machines and basic techniques, and are now looking to upgrade or improve on a specific style; be it rotary, long throw DA or forced drive. Machines covered on these days could include the Rupes LHR 15/21, Flex XFE, XCE, rotary machines from sleek Flex PE14, through to heavier Makita models, and a further selection from over 23 machines we hold in-house or any machine you choose to bring yourself - just let us know on the day what you would prefer to concentrate on. For those already holding some experience who want to try their hand with different machines whilst improving overall techniques we also run this as a one-day Intermediate course with Flex, or for an overview of several machine types you can look at our Advanced Machine Polishing course over two days. Introduction to Machine Polishing doesn't just concentrate on the hardware though. Also covered in the course are: Surface defects and contamination. Efficiency and productivity methods. Preparation and decontamination stages. 'Reading' the paint. Defect identification. Paint thickness measurements using Magnetic Resonance, Eddy Current, and Ultrasonic gauges. The 'Polish/Don't Polish' decision. Introduction to Pad and Compound types and selection. Finishing techniques. Dressing, Sealant/Wax choices, and presentation. Health and Safety The aim of this course is to make you comfortable with using a machine polisher style over a range of scenarios, to enable you to further practice and perfect the technique required for full competency. Course Length 1 Day (0930-1600) Group Size One-to-One Location UK Detailing Academy, 2 Purlieus Barn, Ewen, Cirencester, GL7 6BY Experience / Qualification Open to all Refreshments or Lunch Refreshments included

Level 3 Law Diploma & UK Employmnet Law Fundamentals
By Kingston Open College
Premium Bundle of all Time | Ofqual Regulation + ATHE Awards + QLS Endorsement | Assessment & Tutor Support Included

Supervising First Aid for Mental Health
By Training Legs First Aid
Supervising first aid for mental health: What will you learn? You’ll be surprised by how much you enjoy this 2-day course. I always make sure the learning process is engaging, interactive and stimulating — so you won’t be bored. Most importantly, the training course gives you a fascinating insight into a subject that’s often brushed under the carpet. This is a safe space to speak. Provided you feel comfortable to do so, there’s plenty of opportunity to open up and share your own experiences. It’s a flexible course, and I’m always happy to tailor the content. If there’s an aspect of mental health or addiction you’d like to know more about, please just ask. Here’s the course content Defining mental health, and understanding the stigma surrounding it Factors which affect mental health Roles and responsibilities of a first aider Outline of advice — What to say to someone with a suspected mental health condition Listening without judgement Knowing when to contact the emergency services Identifying signs of stress, and how stress can be managed Alcohol and drug abuse — Its effects, and the consequences for someone’s work and personal life Applying a first aid action plan How to implement a positive mental health culture in the workplace Identifying signs and symptoms of depression, suicide, psychosis, anxiety, self-harm, eating disorders, PTSD, personality disorders, bipolar and schizophrenia Do bear in mind, this course can’t teach you how to diagnose and treat a mental health condition. That’s the responsibility of a healthcare professional. However, you’ll know where to signpost an individual who needs professional help. You’ll leave with the knowledge and confidence to approach, reassure and support someone when they need it most. Group sessions (min 6 people, max 16): £245 per person

Search By Location
- Open Courses in London
- Open Courses in Birmingham
- Open Courses in Glasgow
- Open Courses in Liverpool
- Open Courses in Bristol
- Open Courses in Manchester
- Open Courses in Sheffield
- Open Courses in Leeds
- Open Courses in Edinburgh
- Open Courses in Leicester
- Open Courses in Coventry
- Open Courses in Bradford
- Open Courses in Cardiff
- Open Courses in Belfast
- Open Courses in Nottingham