- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
574 Networking courses in Southend-on-Sea delivered Live Online
F5 Networks Developing iRules for BIG-IP
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is intended for system administrators, network administrators and application developers responsible for the customization of traffic flow through a BIG-IP system. This course provides networking professionals a functional understanding of iRules development. The course builds on the foundation of the Administering BIG-IP or Configuring LTM course, demonstrating how to logically plan and write iRules to help monitor and manage common tasks involved with processing traffic on the BIG-IP system. Extensive course labs consist of writing, applying and evaluating the effect of iRules on local traffic. This hands-on course includes lectures, labs, and discussions. Module 1: Setting Up the BIG-IP System Introducing the BIG-IP System Initially Setting Up the BIG-IP System Archiving the BIG-IP System Configuration Leveraging F5 Support Resources and Tools Module 2: Getting Started with iRules Customizing Application Delivery with iRules Triggering an iRule Leveraging the DevCentral Ecosystem Creating and Deploying iRules Module 3: Exploring iRule Elements Introducing iRule Constructs Understanding iRule Events and Event Context Working with iRule Commands Logging from an iRule Using SYSLOG-NG (LOG Command) Working with User-Defined Variables Working with Operators and Data Types Working with Conditional Control Structures (IF and SWITCH) Incorporating Best Practices in iRules Module 4: Developing and Troubleshooting iRules Mastering Whitespace and Special Symbols Grouping Strings Developing and Troubleshooting Tips Using Fiddler to Test and Troubleshoot iRules Module 5: Optimizing iRule Execution Understanding the Need for Efficiency Measure iRule Runtime Efficiency Using Timing Statistics Modularizing iRules for Administrative Efficiency Using Procedures to Modularize Code Optimizing Logging Using High-Speed Logging Commands in an iRule Implementing Other Efficiencies Using Looping Control Structures (WHILE, FOR, FOREACH Commands) Module 6: Securing Web Applications with iRules Integrating iRules into Web Application Defense Mitigating HTTP Version Attacks Mitigating Path Traversal Attacks Using iRules to Defends Against Cross-Site Request Forgery (CSRF) Mitigating HTTP Method Vulnerabilities Securing HTTP Cookies with iRules Adding HTTP Security Headers Removing Undesirable HTTP Headers Module 7: Working with Numbers and Strings Understanding Number Forms and Notation Working with Strings (STRING and SCAN Commands) Combining Strings (Adjacent Variables, CONCAT and APPEND Commands) Using iRule String Parsing Functions (FINDSTR, GETFIELD, and SUBSTR Commands) Module 8: Processing the HTTP Payload Reviewing HTTP Headers and Commands Accessing and Manipulating HTTP Headers (HTTP::header Commands) Other HTTP commands (HTTP::host, HTTP::status, HTTP::is_keepalive, HTTP::method, HTTP::version, HTTP::redirect, HTTP::respond, HTTP::uri) Parsing the HTTP URI (URI::path, URI::basename, URI::query) Parsing Cookies with HTTP::cookie Selectively Compressing HTTP Data (COMPRESS Command) Module 9: Working with iFiles and Data Groups Working with iFiles Introducing Data Groups Working with Old Format Data Groups (MATCHCLASS, FINDCLASS) Working with New Format Data Groups (CLASS MATCH, CLASS SEARCH) Module 10: Using iRules with Universal Persistence, Stream, and Statistics Profiles Implementing Universal Persistence (PERSIST UIE Command) Working with the Stream Profile (STREAM Command) Collecting Statistics Using a Statistics Profile (STATS Command) Collecting Statistics Using iStats (ISTATS Command) Module 11: Incorporating Advanced Variables Reviewing the Local Variable Namespace Working with Arrays (ARRAY Command) Using Static and Global Variables Using the Session Table (TABLE Command) Processing Session Table Subtables Counting ?Things? Using the Session Table

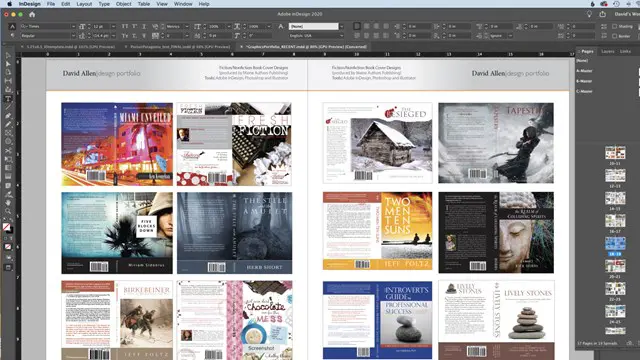
Right Aligned – Nice Work x Form Play
By Right Aligned
In this series we invite globally respected studios to walk us through the processes and methods they employ when working with clients.

Wed 18 Jun 2025 - Light up a Life
By Hospice Income Generation Network
Sharing & Networking - Light up a Life (or name used) appeals, switch-on events, and marketing Session aimed at those working in individual giving, in-memory, events, and marcomms roles THIS SESSION WILL NOT BE RECEORDED

F5 Networks Configuring BIG-IP DNS - Domain Name System (formerly GTM)
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for This course is intended for system and network administrators responsible for installation, setup, configuration, and administration of BIG-IP DNS systems. This course gives networking professionals a functional understanding of the BIG-IP DNS system as it is commonly used. The course covers configuration and ongoing management of the BIG-IP DNS system, and includes a combination of lecture, discussion, and hands-on labs. Module 1: Setting Up the BIG-IP System Introducing the BIG-IP System Initially Setting Up the BIG-IP System Archiving the BIG-IP Configuration Leveraging F5 Support Resources and Tools Provision the BIG-IP System and Confirm Network Configuration Module 2: Introducing the Domain Name System (DNS) and BIG-IP DNS Understanding the Domain Name System (DNS) Reviewing the Name Resolution Process Implementing BIG-IP DNS Using DNS Resolution Diagnostic Tools Module 3: Accelerating DNS Resolution Introducing DNS Resolution with BIG-IP DNS BIG-IP DNS Resolution Decision Flow Configuring BIG-IP DNS Listeners Resolving DNS Queries in the Labs (Lab Zone Records) Load Balancing Queries to a DNS Server Pool Accelerating DNS Resolution with DNS Cache Accelerating DNS Resolution with DNS Express Introducing Wide IPs Using Other Resolution Methods with BIG-IP DNS Integrating BIG-IP DNS into Existing DNS Environments Module 4: Implementing Intelligent DNS Resolutions Introducing Intelligent DNS Resolution Identifying Physical Network Components Identifying Logical Network Components Collecting Metrics for Intelligent Resolution Configuring Data Centers Configuring a BIG-IP DNS System as a Server Configuring a BIG-IP LTM System as a Server Establishing iQuery Communication between BIG-IP Systems Configuring a Non-F5 Server Defining Links and Routers Configuring Wide IP Pools Configuring Wide IPs Managing Object Status Using the Traffic Management Shell (TMSH) Module 5: Using LDNS Probes and Metrics Introducing LDNS Probes and Metrics Types of LDNS Probes Excluding an LDNS from Probing Configuring Probe Metrics Collection Module 6: Load Balancing Intelligent DNS Resolution Introducing Load Balancing on BIG-IP DNS Using Static Load Balancing Methods Round Robin Ratio Global Availability Static Persist Other Static Load Balancing Methods Using Dynamic Load Balancing Methods Round Trip Time Completion Rate CPU Hops Least Connections Packet Rate Kilobytes per Second Other Dynamic Load Balancing Methods Virtual Server Capacity Virtual Server Score Using Quality of Service Load Balancing Persisting DNS Query Responses Configuring GSLB Load Balancing Decision Logs Using Manual Resume Using Topology Load Balancing Module 7: Monitoring Intelligent DNS Resources Exploring Monitors Configuring Monitors Assigning Monitors to Resources Monitoring Best Practices Module 8: Advanced BIG-IP DNS Topics Implementing DNSSEC Setting Limits for Resource Availability Using iRules with Wide IPs Introducing Other Wide IP Types Implementing BIG-IP DNS Sync Groups Module 9: Final Configuration Projects Final Configuration Projects

Wed 25 Jun 2025 - Corporate Fundraising
By Hospice Income Generation Network
Sharing & Networking - Corporate Fundraising Session aimed at corporate fundraisers. THIS SESSION WILL NOT BE RECORDED

Awareness of Safeguarding
By Madeleys First Aid Plus
RQF level 1 Awareness of Safeguarding The RQF Level 1 Awareness of Safeguarding course is designed to provide individuals with a basic understanding of safeguarding principles and practices. It aims to raise awareness about the importance of safeguarding and promote the well-being and protection of vulnerable individuals, such as children, young people, and adults at risk. The course covers the following topics: Introduction to Safeguarding: Definition and importance of safeguarding. Key legislation, policies, and guidance related to safeguarding. Roles and responsibilities of individuals and organizations in safeguarding. Types of Abuse and Neglect: Overview of different types of abuse, including physical, emotional, sexual, and financial abuse. Recognizing signs and indicators of abuse and neglect. Understanding the impact of abuse on individuals' well-being. Vulnerable Groups: Identifying vulnerable groups, such as children, young people, older adults, and individuals with disabilities or mental health issues. Understanding the specific safeguarding concerns and considerations for each group. Reporting and Responding to Safeguarding Concerns: Procedures for reporting safeguarding concerns or disclosures. Understanding the importance of maintaining confidentiality and handling sensitive information appropriately. Responding to safeguarding concerns in a timely and appropriate manner. Promoting Safeguarding and Preventing Abuse: Strategies for promoting a safe and inclusive environment. Recognizing potential risk factors and implementing preventative measures. Understanding the importance of creating a culture of safeguarding within organizations. Multi-Agency Collaboration: Collaboration between different agencies and organizations involved in safeguarding, such as social services, law enforcement, and healthcare. Sharing information and working together to ensure effective safeguarding practices. Case Studies and Scenarios: Reviewing case studies and scenarios to apply safeguarding principles and practices. Analysing potential safeguarding dilemmas and decision-making processes. Personal Responsibilities: Recognizing personal boundaries and limitations when working with vulnerable individuals. Understanding the importance of self-care and managing emotional well-being when dealing with safeguarding issues. It is important to ensure that the course meets local safeguarding guidelines and requirements. Suitability - Who should attend? The RQF Level 1 Awareness of Safeguarding course is suitable for a wide range of individuals who may come into contact with vulnerable individuals or have a general interest in understanding safeguarding principles. Here are some key groups of people who should attend the course: Employees and Staff: The course is relevant for employees and staff members across various sectors and industries, including but not limited to education, healthcare, social services, hospitality, sports and recreation, and community organizations. It helps them develop a basic understanding of safeguarding principles and their responsibilities in ensuring the well-being and protection of vulnerable individuals they may encounter in their work. Volunteers: Individuals who volunteer their time and services in organizations that work with vulnerable individuals should attend the course. It equips them with essential knowledge and awareness of safeguarding issues, helping them provide appropriate support and maintain the safety and dignity of those they interact with. Parents and Caregivers: The course can benefit parents, guardians, and caregivers by providing them with a foundation in safeguarding principles. It helps them recognize potential risks and signs of abuse or neglect, enabling them to create safer environments for the children or vulnerable individuals under their care. Community and Youth Workers: Individuals involved in community work, youth organizations, or youth clubs should attend the course to enhance their understanding of safeguarding. It enables them to promote the well-being and safety of young people and recognize signs of potential abuse or exploitation. Volunteers or Trustees of Charitable Organizations: Individuals serving as volunteers or trustees in charitable organizations that work with vulnerable populations can benefit from the course. It helps them fulfill their responsibilities in safeguarding the individuals the organization serves and ensures they are aware of their legal and ethical obligations. General Public: The course is open to the general public as it provides valuable knowledge and awareness of safeguarding principles. It can benefit individuals who have an interest in understanding the rights and protection of vulnerable individuals in society. It's important to note that the RQF Level 1 Awareness of Safeguarding course provides foundational knowledge and awareness. For individuals who require more in-depth training or who have specific safeguarding roles or responsibilities, higher-level courses may be more suitable. Outcome / Qualification etc. Certification The qualification does not have an expiry date but refresher training and keeping up to date with changes to policies, procedures and new legislation through ongoing CPD is vital. Training Course Content Module 1 Introductions Module 2 Safeguarding legislation and guidance Module 3 Roles and responsibilities Module 4 Abuse and neglect Module 5 Identifying concerns and disclosure Module 6 Making judgements Module 7 Reporting concerns Module 8 Course closure and assessment MODULE 1 INTRODUCTIONS Session content Trainer/Assessor introduction Learner introductions Course syllabus Learning outcomes and assessment criteria Session duration 20 minutes MODULE 2 SAFEGUARDING LEGISLATION AND GUIDANCE Session content Introduction to safeguarding Definitions Assessment framework Safeguarding statistics Safeguarding legislation and guidance Rights of a child/adult at risk Session duration 40 minutes MODULE 3 ROLES AND RESPONSIBILITIES Session content Safeguarding partnerships Local authority safeguarding officer Social care services Multi-agency safeguarding hubs Organisational safeguarding policies Safeguarding lead Session duration 30 minutes MODULE 4 ABUSE AND NEGLECT Session content Definitions Types of abuse and neglect Physical abuse Emotional abuse Sexual abuse Neglect Signs and indicators Parent/carer abuse Radicalisation FGM Forced marriage Modern slavery County line gangs Electronic media abuse - Internet and social networking dangers Session duration 50 minutes MODULE 5 IDENTIFYING CONCERNS AND DISCLOSURE Session content Identifying concerns Being a point of disclosure Recording disclosure information Session duration 20 minutes MODULE 6 MAKING JUDGEMENTS Session content Child development needs Identifying a safeguarding concern Group activity making judgements Session duration 30 minutes MODULE 7 REPORTING CONCERNS Session content Silencing factors Barriers to raising concerns Reporting concerns Importance of sharing concerns Session duration 20 minutes MODULE 8 COURSE CLOSURE AND ASSESSMENT Session content Course summary Assessment paper Course evaluation Course closure Session duration 30 minutes Course delivery details Qualification delivery The qualification has 4 assigned guided learning hours (GLH) and 5 hours total qualification time (TQT). GLH indicates the number of classroom contact hours that the learner will undertake. TQT includes GLH but also takes into account any unsupervised learning and is an estimate of how long the average learner will take to complete the qualification. The minimum classroom contact time of 4 hours should be delivered over a minimum of half a day. The course can be spread over a maximum of 2 weeks, ensuring that each session is a minimum of two hours. The class ratio for this qualification is a maximum of 16 learners to 1 Trainer/Assessor Why choose Madeleys First Aid Plus Founded in 2021 after Louise left 30 years in the NHS as an Advanced practitioner in A&E/ITU, had spent 1.5 years in Covid ITU Won FSB Best start-up business in the West Midlands in May 2023 Now trained 100's of delegates in Physical and Mental Health First Aid Expenses Travel costs and lunch required, there are many cafes and sandwich bars here in Much Wenlock to buy your lunch, you may eat it in the training room. All training material, books, qualification certificates are included in the price Continuing Studies The RQF Level 1 Awareness of Safeguarding course serves as an introductory course that provides individuals with a basic understanding of safeguarding principles. While it is a standalone qualification, individuals who complete the course may choose to progress further in their safeguarding training and education. Here are some potential progression options: RQF Level 2 Award in Safeguarding: This qualification builds upon the knowledge gained in the Level 1 course and provides a more comprehensive understanding of safeguarding principles, policies, and procedures. It covers topics such as risk assessment, responding to safeguarding concerns, and effective communication in safeguarding contexts. Specialized Safeguarding Courses: Individuals who wish to focus on specific areas of safeguarding can pursue specialized courses related to their field of interest. These courses may include Child Protection, Adult Safeguarding, Domestic Abuse Awareness, Online Safety, or Safeguarding in Healthcare. Specialized courses delve deeper into the specific risks, regulations, and best practices associated with safeguarding vulnerable individuals in those particular contexts. Safeguarding Training for Specific Professions: Many professions have specific safeguarding training requirements tailored to their sector. For example, teachers may need to complete safeguarding training specific to the education setting, healthcare professionals may have training focused on safeguarding vulnerable patients, and social workers may have specialized safeguarding training in line with their role. Progression may involve undertaking profession-specific safeguarding courses or qualifications. Safeguarding Leadership and Management Training: Individuals in supervisory or managerial positions may consider pursuing training that focuses on the leadership and management aspects of safeguarding. This can include courses on developing and implementing safeguarding policies and procedures, managing safeguarding incidents, conducting internal investigations, and providing guidance and support to staff. Continued Professional Development (CPD): Engaging in ongoing CPD activities is essential for staying updated with the latest developments in safeguarding practices and policies. Individuals can attend conferences, workshops, or seminars related to safeguarding, child protection, or specific areas of interest within the field. This allows for continued learning and networking with other professionals. Higher Education: Individuals who wish to pursue a more in-depth study of safeguarding can consider higher education programs in social work, psychology, criminology, or related fields. These programs provide comprehensive knowledge and training in safeguarding practices, policies, and research. They may lead to professional certifications or degrees that enhance career opportunities in safeguarding roles. It's important for individuals to research and explore progression options that align with their specific career goals, interests, and local requirements. Different countries or regions may have varying certification or training requirements for safeguarding roles, so it's advisable to check with relevant regulatory bodies or professional associations for specific guidance.

Managing and Troubleshooting PCs - Part 1
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for If you are getting ready for a career as an entry-level information technology (IT) professional or personal computer (PC) service technician, the CompTIA© A+© Certification course is the first step in your preparation. Overview In this course, you will install, configure, optimize, troubleshoot, repair, upgrade, and perform preventive maintenance on personal computers, digital devices, and operating systems. You will:Identify the hardware components of personal computers and mobile digital devices.Identify the basic components and functions of operating systems.Identify networking and security fundamentals.Identify the operational procedures that should be followed by professional PC technicians.Install, configure, and troubleshoot display devices.Install and configure peripheral components.Manage system components.Manage data storage.Install and configure Microsoft Windows.Optimize and maintain Microsoft Windows.Work with other operating systems.Identify the hardware and software requirements for client environment configurations.Identify network technologies.Install and configure networking capabilities.Support mobile digital devices.Support printers and multifunction devices.Identify security threats, vulnerabilities, and controls.Implement security controls.Troubleshoot system-wide issues. In this course, you will acquire the essential skills and information you will need to install, upgrade, repair, configure, troubleshoot, optimize, and perform preventative maintenance of basic personal computer hardware and operating systems. Hardware Fundamentals Topic A: Personal Computer Components Topic B: Storage Devices Topic C: Mobile Digital Devices Topic D: Connection Interfaces Operating System Fundamentals Topic A: PC and Mobile Operating Systems Topic B: PC Operating System Tools and Utilities Networking & Security Fundamentals Topic A: Network Types Topic B: Network Components Topic C: Common Network Services Topic D: Cloud Concepts Topic E: Security Fundamentals Safety & Operational Procedures Topic A: Basic Maintenance Tools and Techniques Topic B: Personal and Electrical Safety Topic C: Environmental Safety and Materials Handling Topic D: Professionalism and Communication Topic E: Organizational Policies and Procedures Topic F: Troubleshooting Theory Supporting Display Devices Topic A: Install Display Devices Topic B: Configure Display Devices Topic C: Troubleshoot Video and Display Devices Installing & Configuring Peripheral Components Topic A: Install and Configure Input Devices Topic B: Install and Configure Output Devices Topic C: Install and Configure Input/Output Devices Topic D: Install and Configure Expansion Cards Managing System Components Topic A: Identify Motherboard Components and Features Topic B: Install and Configure CPUs and Cooling Systems Topic C: Install Power Supplies Topic D: Troubleshoot System Components Managing Data Storage Topic A: Identify RAM Types and Features Topic B: Troubleshoot RAM Issues Topic C: Install and Configure Storage Devices Topic D: Configure the System Firmware Topic E: Troubleshoot Hard Drives and RAID Arrays Installing & Configuring Microsoft Windows Topic A: Implement Client-Side Virtualization Topic B: Install Microsoft Windows Topic C: Use Microsoft Windows Topic D: Configure Microsoft Windows Topic E: Upgrade Microsoft Windows Optimizing & Maintaining Microsoft Windows Topic A: Optimize Microsoft Windows Topic B: Back Up and Restore System Data Topic C: Perform Disk Maintenance Topic D: Update Software Working with Other Operating Systems Topic A: The OS X Operating System Topic B: The Linux Operating System Customized Client Enviroments Topic A: Types of Common Business Clients Topic B: Custom Client Environments Networking Technologies Topic A: TCP/IP Properties and Characteristics Topic B: TCP/IP Topic C: Internet Connections Topic D: Ports and Protocols Topic E: Networking Tools Installing & Configuring Networking Capabilities Topic A: Configure Basic Windows Networking Topic B: Configure Network Perimeters Topic C: Using Windows Networking Features Topic D: Install and Configure SOHO Networks Supporting Mobile Digital Devices Topic A: Install and Configure Exterior Laptop Components Topic B: Install and Configure Interior Laptop Components Topic C: Other Mobile Devices Topic D: Mobile Device Accessories and Ports Topic E: Mobile Device Connectivity Topic F: Mobile Device Synchronization Topic G: Troubleshoot Mobile Device Hardware Supporting Printers & Multifunction Devices Topic A: Printer and Multifunction Technologies Topic B: Install and Configure Printers Topic C: Maintain Printers Topic D: Troubleshoot Printers Security Threats, Vulnerabilities, and Controls Topic A: Common Security Threats and Vulnerabilities Topic B: General Security Controls Topic C: Mobile Security Controls Topic D: Data Destruction and Disposal Methods Implementing Security Controls Topic A: Secure Operating Systems Topic B: Secure Workstations Topic C: Secure SOHO Networks Topic D: Secure Mobile Devices Troubleshooting System-Wide Issues Topic A: Troubleshoot PC Operating Systems Topic B: Troubleshoot Mobile Device Operating Systems and Applications Topic C: Troubleshoot Wired and Wireless Networks Topic D: Troubleshoot Common Security Issues

Communication Strategies
By Nexus Human
Duration 1 Days 6 CPD hours For the better part of every day, we are communicating to and with others. Whether it?s the speech you deliver in the boardroom, the level of attention you give your spouse when they are talking to you, or the look you give the cat, it all means something. This workshop will help participants understand the different methods of communication and how to make the most of each of them. 1 - Getting Started Icebreaker Housekeeping Items The Parking Lot Workshop Objectives 2 - The Big Picture What is Communication? How Do We Communicate? Other Factors in Communication 3 - Understanding Communication Barriers An Overview of Common Barriers Language Barriers Cultural Barriers Differences in Time and Place 4 - Paraverbal Communication Skills The Power of Pitch The Truth about Tone The Strength of Speed 5 - Non-Verbal Communication Understanding the Mehrabian Study All About Body Language Interpreting Gestures 6 - Speaking Like a STAR S = Situation T = Task A = Action R = Result Summary 7 - Listening Skills Seven Ways to Listen Better Today Understanding Active Listening Sending Good Signals to Others 8 - Asking Good Questions Open Questions Closed Questions Probing Questions 9 - Appreciative Inquiry The Purpose of AI The Four Stages Examples and Case Studies 10 - Mastering the Art of Conversation Level One: Discussing General Topics Level Two: Sharing Ideas and Perspectives Level Three: Sharing Personal Experiences Our Top Networking Tips 11 - Advanced Communication Skills Understanding Precipitating Factors Establishing Common Ground Using ?I? Messages 12 - Wrapping Up Words from the Wise Review of Parking Lot Lessons Learned Completion of Action Plans and Evaluations Additional course details: Nexus Humans Communication Strategies training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Communication Strategies course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Unreal Engine Courses London
By Real Animation Works
Face to Face training customised and bespoke. One to One Online or Face to Face
VMware Telco Cloud Infrastructure: Install, Configure, Manage [V2.0]
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Telco cloud system administrators and telco network operations engineers Professionals who work with telco or enterprise and data center networks Designers and operations engineers who manage telco workloads Overview By the end of the course, you should be able to meet the following objectives: Describe the VMware Telco Cloud Infrastructure⢠architecture Describe the VMware Cloud Director architecture List the infrastructure requirements of ETSI NFV Describe the VMware Cloud Director architecture as Virtualized Infrastructure Manager (VIM) Describe the options associated with VMware cloud providers Explain how organizations are supported in VMware Cloud Director Describe the security model in VMware Cloud Director Configure key networking elements of VMware Cloud Director Manage and monitor resources in VMware Cloud Director Enumerate troubleshooting concepts and Day 2 operations using VMware Cloud Director This five-day, hands-on training course provides you with the advanced knowledge, skills, and tools to achieve competency in operating and troubleshooting the VMware Telco Cloud Infrastructure environment. In this course, you are introduced to VMware Cloud Director? as a virtualized infrastructure manager. You will examine ETSI NFV requirements, deployment options, and procedures. You will also deploy virtualized network functions and understand their detailed configuration settings. You will learn how to support organizations as well as set up networking and security using hands-on lab exercises.In addition, you are presented with various types of technical problems in VMware Cloud Director, which you will identify, analyze, and solve through a systematic troubleshooting process. Course Introduction Introductions and course logistics Course objectives Day 0 Operations: VMware Telco Cloud Infrastructure Installation Describe the challenges of the telco cloud Describe the key functions of the telco cloud List the benefits of the VMware Cloud Director based VMware Telco Cloud Infrastructure Describe the VMware Telco Cloud Infrastructure architecture Describe the role of VMware Cloud Director in the VMware Telco Cloud Infrastructure architecture List the VMware Telco Cloud Infrastructure deployment options Describe the VMware Cloud Director architecture List the key VMware components that are part of VMware Cloud Director Describe the key use cases for the VMware Cloud Director based VMware Telco Cloud Infrastructure Day 0 Operations: ETSI NFV Requirements for Cloud Platforms Compare physical and virtual infrastructures List the benefits and challenges of physical infrastructure Describe the types of virtual infrastructure Describe the advantages and components of the NFV infrastructure (NFVI) Explain the role of network virtualization in the NFVI List the requirements of NFVI for VMware Cloud Director Describe the networking options of VMware Cloud Director Describe the key networking use cases Describe requirements of VMware Telco Cloud Automation? for networking Describe the storage options of VMware Cloud Director Describe the key storage use cases Day 1 Operations: Virtualized Infrastructure Manager (VIM) Configuration Explain basic concepts related to VMware Cloud Director Describe the components of the VMware Cloud Director architecture Describe the basic configuration of the VMware Cloud Director architecture Describe virtual data centers or VDCs Explain the role of organization VDCs Describe the relationship between provider VDCs and organization VDCs Describe resources in VMware Cloud Director List the key resource organization Create resource pools Describe how vSAN integrates with VMware Cloud Director Day 1 Operations: Configuring VMware Cloud Director Providers Describe how compute resources are provided to VMware Cloud Director Describe how storage resources are provided to VMware Cloud Director Describe provider VDC requirements and best practices List the requirements of creating VDCs Describe the VNF on-boarding process Create provider VDCs Day 1 Operations: Configuring VMware Cloud Director Organizations Describe VMware Cloud Director organizations Create VMware Cloud Director organizations Navigate through the VMware Cloud Director HTML5 provider portal Describe the VMware Cloud Director organization VDC Navigate through the tenant portal List use cases for a VMware Cloud Director organization VDC List the organization VDC allocation models Describe the types of resources that can be allocated Describe how resources are allocated for an organization Examine the function and requirements of network pools Describe the network types available in VMware Cloud Director (external, organization, and vApp) Create and manage organization VDC networks Describe catalogs Manage an organization?s catalog Populate, share, and publish catalogs Describe vApps Manage access to vApps and catalogs Modify the configuration of vApps and their virtual machines (VMs) Manage organization VDC networking Create affinity and anti-affinity rules Day 1 Operations: Configuring VMware Cloud Director Security Describe role-based access Create custom security roles Describe the directory services in VMware Cloud Director Describe the role of LDAP, SAML, SSL, Kerberos, and OAuth2 with VMware Cloud Director Explain the use of VMware Cloud Director with SSO Day 1 Operations: Configuring VMware Cloud Director Networking List networking options in VMware Cloud Director Describe key networking use cases in VMware Cloud Director Describe the use and placement of VMware NSX© Edge? services gateways in relation to VMware Cloud Director Review routing with the distributed logical router and edge services gateways in combination with VMware Cloud Director Describe firewall management in VMware Cloud Director with edge services gateways and the distributed firewall Describe an overview of VMware NSX-T? Data Center Explain the architecture of NSX-T Data Center Describe VMware Cloud Director supported features of NSX-T Data Center Describe the benefits and challenges of multisite networking List the requirements for multisite networking Describe the benefits and challenges of networking between VDCs List the requirements for networking between VDCs Configure cross-VDC networking Day 2 Operations: VMware Cloud Director Resource Management and Monitoring Identify the key resources that need to be managed with VMware Cloud Director List monitoring options with VMware Cloud Director Explain the resource management and monitoring architecture in VMware Cloud Director Monitor objects from the VMware Cloud Director portal Identify features of VMware vRealize© Operations Manager? Integrate VMware Cloud Director with vRealize Operations Manager Configure VMware vRealize© Operations Management Pack for VMware Cloud Director? Outline the monitoring features of vRealize Operations Manager in VMware Cloud Director Describe the purpose of the vRealize Operations Tenant App for VMware Cloud Director Integrate VMware Cloud Director with the Tenant App Configure the Tenant App for VMware Cloud Director Monitor objects with the Tenant App List the steps to monitor VMware Cloud Director environments with vRealize Operations Manager List the steps to monitor VMware Cloud Director environments with VMware vRealize© Log Insight? List the steps to review historical virtual machine metrics in VMware Cloud Director Examine VMware Cloud Director logs Day 2 Operations: VMware Cloud Director Troubleshooting Identify the features of the VMware Telco Cloud Automation dashboards List the components of the VMware Telco Cloud Automation dashboards Explain the features of fault management in VMware Telco Cloud Director Describe the use of fault management in VMware Cloud Director Describe the use of performance management in VMware Cloud Director Describe the use of logs in VMware Cloud Director Troubleshoot using VMware Cloud Director
![VMware Telco Cloud Infrastructure: Install, Configure, Manage [V2.0]](https://cademy-images-io.b-cdn.net/9dd9d42b-e7b9-4598-8d01-a30d0144ae51/4c81f130-71bf-4635-b7c6-375aff235529/original.png?width=3840)