- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1358 Network courses delivered Live Online
Climate science workshop - Climate Fresk
By The C Collective
Join a Climate Fresk Climate science workshop to learn about the causes and effects of climate change through a fun and collaborative experience.

VMware training course description This five-day VMware course features intensive handson training that focuses on installing, configuring, and managing VMware vSphere 8, which includes VMware ESXi 8 and VMware vCenter 8. This course prepares you to administer a vSphere infrastructure for an organization of any size. This course is the foundation for most VMware technologies in the software-defined data center. What will you learn Install and configure ESXi hosts. Deploy and configure vCenter. Create virtual networks using standard and distributed switches. Configure VMs, templates, clones, and snapshots. Manage virtual machine resource allocation. Migrate virtual machines with vSphere vMotion and vSphere Storage vMotion. VMware training course details Who will benefit: Systems administrators and engineers. Prerequisites: Introduction to data communications & networking. Windows/Linux Administration. Duration 5 days VMware training course contents Course Introduction Introductions and course logistics. Course objectives vSphere and Virtualization Overview Explain basic virtualization concepts, Describe how vSphere fits in the software-defined data center and the cloud infrastructure, Recognize the user interfaces for accessing vSphere, Explain how vSphere interacts with CPUs, memory, networks, storage, and GPUs Installing and Configuring ESXi Install an ESXi host, Recognize ESXi user account best practices, Configure the ESXi host settings using the DCUI and VMware Host Client Deploying and Configuring vCenter Recognize ESXi hosts communication with vCenter, Deploy vCenter Server Appliance, Configure vCenter settings, Use the vSphere Client to add and manage license keys, Create and organize vCenter inventory objects, Recognize the rules for applying vCenter permissions, View vCenter logs and events Configuring vSphere Networking Configure and view standard switch configurations, Configure and view distributed switch configurations, Recognize the difference between standard switches and distributed switches, Explain how to set networking policies on standard and distributed switches Configuring vSphere Storage Recognize vSphere storage technologies, Identify types of vSphere datastores, Describe Fibre Channel components and addressing, Describe iSCSI components and addressing, Configure iSCSI storage on ESXi, Create and manage VMFS datastores, Configure and manage NFS datastores Deploying Virtual Machines Create and provision VMs, Explain the importance of VMware Tools, Identify the files that make up a VM Recognize the components of a VM, Navigate the vSphere, Client and examine VM settings and options, Modify VMs by dynamically increasing resources, Create VM templates and deploy VMs from them, Clone VMs, Create customization specifications for guest operating systems, Create local, published, and subscribed content libraries, Deploy VMs from content libraries, Manage multiple versions of VM templates in content libraries Managing Virtual Machines Recognize the types of VM migrations that you can perform within a vCenter instance and across vCenter instances, Migrate VMs using vSphere vMotion, Describe the role of Enhanced vMotion Compatibility in migrations, Migrate VMs using vSphere Storage vMotion, Take a snapshot of a VM, Manage, consolidate, and delete snapshots, Describe CPU and memory concepts in relation to a virtualized environment, Describe how VMs compete for resources Define CPU and memory shares, reservations, and limits Deploying and Configuring vSphere Clusters Create a vSphere cluster enabled for vSphere DRS and vSphere HA, View information about a vSphere cluster Explain how vSphere DRS determines VM placement on hosts in the cluster, Recognize use cases for vSphere DRS settings, Monitor a vSphere DRS cluster Describe how vSphere HA responds to various types of failures, Identify options for configuring network redundancy in a vSphere HA cluster, Recognize vSphere HA design considerations, Recognize the use cases for various vSphere HA settings, Configure a vSphere HA cluster, Recognize when to use vSphere Fault Tolerance Managing the vSphere Lifecycle Enable vSphere Lifecycle Manager in a vSphere cluster, Describe features of the vCenter Update Planner, Run vCenter upgrade prechecks and interoperability reports, Recognize features of vSphere Lifecycle Manager, Distinguish between managing hosts using baselines and managing hosts using images, Describe how to update hosts using baselines, Describe ESXi images, Validate ESXi host compliance against a cluster image and update ESXi hosts, Update ESXi hosts using vSphere Lifecycle Manager, Describe vSphere Lifecycle Manager automatic recommendations, Use vSphere Lifecycle Manager to upgrade VMware Tools and VM hardware

Introduction to Virtualization course description A comprehensive tour of virtualization. The course concentrates on the actual technologies involved as opposed to any one vendor solution. What will you learn Explain the concepts of virtualization. Partition servers. Create Virtual Machines. Introduction to Virtualization course details Who will benefit: Anyone looking for an introduction to Virtualization. Prerequisites: None. Duration 2 days Introduction to Virtualization course contents Virtualization Concepts What is Virtualisation? What are virtual machines (VMs)? Virtualisation Landscape. Network Virtualisation. Suitability for Organisations. Advantages of deploying Virtualisation. Downsides of deploying Virtualisation. Overview of Virtualisation products. Hypervisors What is a hypervisor? Difference between type 1 and 2 hypervisors. Available hypervisors. Hypervisors and device drivers. Hands on: Installing Oracle VirtualBox on Windows. Creating/Importing/Configuring VMs. Virtualization Hosts Hardware and resource requirements. Installation of the hypervisor. Hands on: Installing Hyper-V role into Windows Server. Creating/Importing/Configuring VMs. Virtual Machines Creating virtual machines. Resource requirements. Settings. Installation of the guest OS. Additional tools/ extensions for hypervisor integration. VM files and their uses. Virtual hard disk and their formats. Hardware pass through. Hands on: Connecting to VMWare ESXi via WebGUI and using ESXi to create/import/configure VMs. VM Snapshots/Checkpoints What is a snapshot? How to use them and how they impact performance? Creating/deleting/merging of snapshots. Hands on: Using ESXi to create/manage snapshots. Command Line use on the Hypervisor Interacting with the hypervisor through the command line. Simple commands to configure the hypervisor and VMs. Simple scripts. Hands on: Connecting to VMWare ESXi via PowerCLI to manipulate VMs and snaphshots. Virtualization Storage Different types of storage: local vs remote. Local and remote storage technologies. Configuring storage. Hands on: Using ESXi to deploy VMs on remote NFS storage. Virtual Networking How is networking done in virtualization environments. What is a virtual switch and vNIC and what are their performance characteristics? NIC teaming and trunking in the virtual world. Port groups and isolation. Physical NICs and their use in virtual switches. Hands on: Using ESXi to create and configure vswitches and networking. Templates and clones What is a template? What is a clone? When to use templates and clones to optimize VM deployment. Migrating/Importing VMs What is migration? Migrating compute and storage. Importing VMs from files or physical machines. Hands on: Using VMWare vCenter Server to clone/ template/migrate VMs, tag resources, create local user accounts and assign permissions. VMs and Backups Taking backups of your VMs. Restoring your VMs from backups. Virtualization and Licensing Different licensing models and costs. Containerization Concepts What is a container and how is it different from a virtual machine. When to use containers. Docker and Kubernetes

Implementing Aruba OS-CX Switching, Rev. 20.21
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Typical candidates for this course are IT Professionals who will deploy and manage networks based on HPE's ArubaOS-CX switches. Overview After you successfully complete this course, expect to be able to: Use NetEdit to manage switch configurations Use the Network Analytics Engine (NAE) to implement scripting solutions to provide for proactive network management and monitoring Compare and contrast VSX, VSF, and backplane stacking Explain how VSX handles a split-brain scenario Implement and manage a VSX fabric Define ACLs and identify the criteria by which ACLs select traffic Configure ACLs on AOS-CX switches to select given traffic Apply static ACLs to interfaces to meet the needs of a particular scenario Examine an ACL configuration and determine the action taken on specific packets Deploy AOS-Switches in single-area and multi-area OSPF systems Use area definitions and summaries to create efficient and scalable multiple area designs Advertise routes to external networks in a variety of OSPF environments Promote fast, effective convergence during a variety of failover situations Use virtual links as required to establish non-direct connections to the backbone Implement OSFP authentication Establish and monitor BGP sessions between your routers and ISP routers Advertise an IP block to multiple ISP routers Configure a BGP router to advertise a default route in OSPF Use Internet Group Management Protocol (IGMP) to optimize forwarding of multicast traffic within VLANs Describe the differences between IGMP and IGMP snooping Distinguish between PIM-DM and PIM-SM Implement PIM-DM and PIM-SM to route multicast traffic Implement Virtual Routing Forwarding (VRF) policies to contain and segregate routing information Create route maps to control routing policies Understand the use of user roles to control user access on AOS-CX switches Implement local user roles on AOS-CX switches and downloadable user roles using a ClearPass solution Implement 802.1X on AOS-CX switch ports Integrate AOS-CX switches with an Aruba ClearPass solution, which might apply dynamic role settings Implement RADIUS-based MAC Authentication (MAC-Auth) on AOS-CX switch ports Configure captive portal authentication on AOS-CX switches to integrate them with an Aruba ClearPass solution Combine multiple forms of authentication on a switch port that supports one or more simultaneous users Configure dynamic segmentation on AOS-CX switches This course teaches you the advanced skills necessary to implement and operate enterprise level Aruba campus switching solutions. You will build on the skills you learned at the Associate level to configure and manage modern, open standards-based networking solutions using Aruba's OS-CX routing and switching technologies. In this course, participants learn about ArubaOS-CX switch technologies including: securing port access with Aruba's dynamic segmentation, redundancy technologies such as Multiple Spanning Tree Protocol (MSTP), link aggregation techniques including Link Aggregation Protocol (LACP) and switch virtualization with Aruba?s Virtual Switching Extension (VSX) and Aruba's Virtual Switching Framework (VSF). This course is approximately 50% lecture and 50% hands-on lab exercises. Introduction to Aruba Switching Switches overview Architectures NetEdit Overview Centralized configuration Switch groups/templates AOS-CX mobile App Network Analytics Engine (NAE) Overview Configuration Core NAE feature lab sflow, local mirror, remote mirror VSX VSF vs. VSX: access and Agg/core design Stacking review VSF and uni/multi packet forwarding Stack fragments / split brain VSX Overview: roles, control, data, management planes VSX components (ISL, Keepalive, VSX LAG, Active Gateway, Active-Forwarding, Link Delay) Split Brain scenario Upstream Connectively Options (ROP single VRF, SVIs with multiple VRF, VSX Lag SVIs with multiple VRFs) Upstream/Downstream unicast traffic flow (South-North and North-South) VSX Configuration: VSX and Active Gateway VSX firmware updates ACLs Overview: types, components MAC ACL, Standard ACL, Extended ACL, Classifier-based Policies Configuration: wildcard bits, logging, pacl, vacl, racl Advanced OSPF Review basic OSPF Multi area: setup and aggregation Area-Types Stub, Totally Stub, NSSA, Totally NSSA External routes OSPF tuning: costs, bfd, gr, auth, vrrp, virt link BGP Overview: i/e bgp, as numbers Best path selection Configuration: route announcement Route filtering to prevent transit as IGMP Overview Querier Snooping Unknown multicasts Multicast Routing: PIM Overview PIM DM 802.1X Authentication Overview: roles, requirements, coa, accounting Dynamic port configuration: avp, acl, qos, VLAN Port-based vs. user-based: examples Radius service tracking, critical VLAN MAC Authentication Overview: Use cases Radius-based MAC Auth Dynamic Segmentation Leverage dynamic segmentation features Configure tunneled-node on AOS-CX switches Describe when and how to configure PAPI enhanced security, high availability, and fallback switching for tunneled-node Quality of Service Overview VoQ (Virtual Output Queue) QOS: queueing, QOS marks, dot1p, dscp Trust levels QOS configuration: port, VLAN, policies Interaction with user roles Queue configuration Rate limiters LLDP-MED Additional Routing Technologies VRF - Management VRF PBR MDNS PIM SM Capitve Portal Authentication Overview of guest solutions Built-in web auth ClearPass redirect with CPPM

AUCWB-CT - Administering and Using the Cisco Webex Boards
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for The primary audience for this course is as follows: WebEx Board Power Users Network Video Administrators Collaboration Administrators Network Video Engineer Voice/UC/Collaboration/Communications Engineer Collaboration Tools Engineer Collaboration Sales/Systems Engineer DesignHTMLPreview Overview Overview of Cisco WebEx Boards Setting up and configuring WebEx Board Using WebEx Teams Board Troubleshooting WebEx Team Boards WebEx Teams API This is a one-day instructor-led course that teaches the students how to Administer and Use a WebEx Team Board for Collaboration Teams. Overview of Cisco WebEx Board Introducing the WebEx Board WebEx Board Capabilities WebEx Board Considerations WebEx Board 55 WebEx Board 70 WebEx Board 85 Setting up and Configuring WebEx Board Unpacking WebEx Boards Mounting options for the WebEx Board Webex Board Touch 10 Support Audio Arrays for Webex Board Cisco WebEx Board Pen WebEx Board Easy Installation WebEx Board Activation WebEx Board Registration to Cloud WebEx Board Registration to CUCM Software Updates Setting up email for annotation and White boarding Using the WebEx Board as a Digital Signage Setup Branding on the WebEx Boards Reset to Factory Default User Interface -Device Settings -Call Quality -Check health and Services -Check Camera Using the WebEx Board Using the WebEx Board as Standalone Conference unit Using the WebEx Board with WebEx Teams app Pairing WebEx Teams app with the WebEx Board Making Calls with the WebEx Board Whiteboarding with the WebEx Board Collaborating with WebEx Board Using Wireless sharing Using WebEx Board attach to a WebEx teams space WebEx Board Companion Mode Troubleshooting the WebEx Board On-Screen Diagnostics Camera Check Media Quality Web Interface Web Interface ? Diagnostics Web Interface ? Monitoring Calls Web Interface ? Call Control Web Interface ? System Logs Web Interface ? Call Logs Troubleshooting Registration Troubleshooting Connectivity Labs Installing WebEx Teams Application Setup WebEx Board Configuring WebEx Board Configure advanced settings Configuring Conferences with WebEx Boards Making calls with WebEx Boards Joining Spaces With WebEx Boards Whiteboarding WebEx Board Sessions Annotating WebEx Board sessions Monitor WebEx Board Sessions Troubleshooting WebEx Board Sessions

macOS Support Essentials 14 Sonoma
By Influential Training
Support Essentials course, macOS Support Essentials,

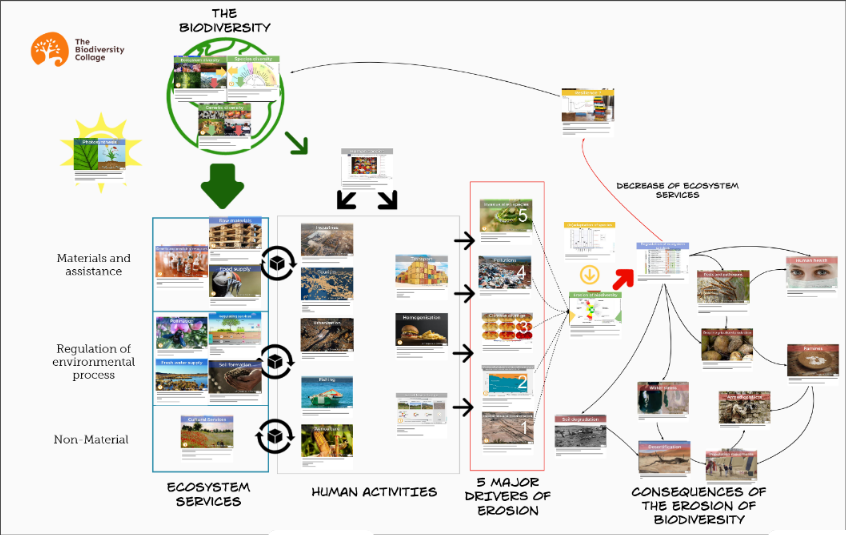
Biodiversity training - Biodiversity collage workshop
By The C Collective
Join a Biodiversity collage workshop to learn about the biodiversity crisis and how to tackle it.
Cisco Securing the Web with Cisco Web Security Applicance v3.0 (SWSA)
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Security architects System designers Network administrators Operations engineers Network managers, network or security technicians, and security engineers and managers responsible for web security Cisco integrators and partners Overview After taking this course, you should be able to: Describe Cisco WSA Deploy proxy services Utilize authentication Describe decryption policies to control HTTPS traffic Understand differentiated traffic access policies and identification profiles Enforce acceptable use control settings Defend against malware Describe data security and data loss prevention Perform administration and troubleshooting This course shows you how to implement, use, and maintain Cisco© Web Security Appliance (WSA), powered by Cisco Talos, to provide advanced protection for business email and control against web security threats. Through a combination of expert instruction and hands-on practice, you?ll learn how to deploy proxy services, use authentication, implement policies to control HTTPS traffic and access, implement use control settings and policies, use the solution?s anti-malware features, implement data security and data loss prevention, perform administration of Cisco WSA solution, and more.This course helps you prepare to take the exam, Securing the Web with Cisco Web Security Appliance (300-725 SWSA). Describing Cisco WSA Technology Use Case Cisco WSA Solution Cisco WSA Features Cisco WSA Architecture Proxy Service Integrated Layer 4 Traffic Monitor Data Loss Prevention Cisco Cognitive Intelligence Management Tools Cisco Advanced Web Security Reporting (AWSR) and Third-Party Integration Cisco Content Security Management Appliance (SMA) Deploying Proxy Services Explicit Forward Mode vs. Transparent Mode Transparent Mode Traffic Redirection Web Cache Control Protocol Web Cache Communication Protocol (WCCP) Upstream and Downstream Flow Proxy Bypass Proxy Caching Proxy Auto-Config (PAC) Files FTP Proxy Socket Secure (SOCKS) Proxy Proxy Access Log and HTTP Headers Customizing Error Notifications with End User Notification (EUN) Pages Utilizing Authentication Authentication Protocols Authentication Realms Tracking User Credentials Explicit (Forward) and Transparent Proxy Mode Bypassing Authentication with Problematic Agents Reporting and Authentication Re-Authentication FTP Proxy Authentication Troubleshooting Joining Domains and Test Authentication Integration with Cisco Identity Services Engine (ISE) Creating Decryption Policies to Control HTTPS Traffic Transport Layer Security (TLS)/Secure Sockets Layer (SSL) Inspection Overview Certificate Overview Overview of HTTPS Decryption Policies Activating HTTPS Proxy Function Access Control List (ACL) Tags for HTTPS Inspection Access Log Examples Understanding Differentiated Traffic Access Policies and Identification Profiles Overview of Access Policies Access Policy Groups Overview of Identification Profiles Identification Profiles and Authentication Access Policy and Identification Profiles Processing Order Other Policy Types Access Log Examples ACL Decision Tags and Policy Groups Enforcing Time-Based and Traffic Volume Acceptable Use Policies, and End User Notifications Defending Against Malware Web Reputation Filters Anti-Malware Scanning Scanning Outbound Traffic Anti-Malware and Reputation in Policies File Reputation Filtering and File Analysis Cisco Advanced Malware Protection File Reputation and Analysis Features Integration with Cisco Cognitive Intelligence Enforcing Acceptable Use Control Settings Controlling Web Usage URL Filtering URL Category Solutions Dynamic Content Analysis Engine Web Application Visibility and Control Enforcing Media Bandwidth Limits Software as a Service (SaaS) Access Control Filtering Adult Content Data Security and Data Loss Prevention Data Security Cisco Data Security Solution Data Security Policy Definitions Data Security Logs Performing Administration and Troubleshooting Monitor the Cisco Web Security Appliance Cisco WSA Reports Monitoring System Activity Through Logs System Administration Tasks Troubleshooting Command Line Interface

Cisco Securing Cisco Networks with Snort Rule Writing Best Practices v2.1 (SSFRULES)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is for technical professionals to gain skills in writing rules for Snort-based Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS). The primary audience includes: Security administrators Security consultants Network administrators System engineers Technical support personnel using open source IDS and IPS Channel partners and resellers Overview After taking this course, you should be able to: Describe the Snort rule development process Describe the Snort basic rule syntax and usage Describe how traffic is processed by Snort Describe several advanced rule options used by Snort Describe OpenAppID features and functionality Describe how to monitor the performance of Snort and how to tune rules The Securing Cisco Networks with Snort Rule Writing Best Practices (SSFRules) v2.1 course shows you how to write rules for Snort, an open-source intrusion detection and prevention system. Through a combination of expert-instruction and hands-on practice, this course provides you with the knowledge and skills to develop and test custom rules, standard and advanced rules-writing techniques, how to integrate OpenAppID into rules, rules filtering, rules tuning, and more. The hands-on labs give you practice in creating and testing Snort rules. Course Outline Introduction to Snort Rule Development Snort Rule Syntax and Usage Traffic Flow Through Snort Rules Advanced Rule Options OpenAppID Detection Tuning Snort

C)CSA: Cybersecurity Analyst Mile 2
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Security Professionals Incident Handling Professionals Anyone in a Security Operations Center Forensics Experts Cybersecurity Analysts Overview Our Certified Cyber Security Analyst course helps you prepare an organization to create a complete end to end solution for proactively monitoring, preventing, detecting, and mitigating threats as they arise in real time. Do not fool yourself, this course is far more advanced than you may expect. It is fast paced and thorough, so you can enjoy a well-rounded experience. Be ready to dig deep into the details of security analysis for today's needs. When we are done you will be able to setup and deploy state of the art open source and for purchase analysis tools, intrusion detection tools, syslog servers, SIEMs, along with integrating them for the entire company to find and an many cases prevent today's exploits. This course maps to the mile2 Certified Cyber Security Analyst Exam as well as the CompTIA CySA+CS0-001 certification exam. Our Certified Cyber Security Analyst course helps you prepare an organization to create a complete end to end solution for proactively monitoring, preventing, detecting, and mitigating threats as they arise in real time.Do not fool yourself, this course is far more advanced than you may expect. It is fast paced and thorough, so you can enjoy a well-rounded experience. Be ready to dig deep into the details of security analysis for today?s needs.When we are done you will be able to setup and deploy state of the art open source and for purchase analysis tools, intrusion detection tools, syslog servers, SIEMs, along with integrating them for the entire company to find and an many cases prevent today?s exploits.This course maps to the mile2 Certified Cyber Security Analyst Exam as well as the CompTIA CySA+CS0-001 certification exam. Blue Team?Principles Network Architecture?and how it lays the groundwork Defensive Network Security Data Locations?and how they tie together Security?Operations?Center The People, Processes, and Technology Triage and Analysis Digital Forensics Incident Handling Vulnerability Management Automation, Improvement, and Tuning Digital?Forensics Investigative Theory and?Processes Digital Acquisition Evidence Protocols Evidence Presentation Computer Forensics?Laboratory Protocols Processing Techniques Specialized?Artifacts Advanced Forensics for Today?s?Exploitations Malware Analysis Creating the Safe Environment Static Analysis Dynamic Analysis Behavior Based Analysis What is different about?Ransomware? Manual Code Reversing Traffic Analysis Manual Analysis Principles Automated?Analysis Principles Signatures?compared to?Behaviors Application Protocols Analysis Principles Networking Forensics Assessing the Current State of Defense with the?Organization Network Architecture and Monitoring Endpoint Architecture and Monitoring Automation, Improvement, and continuous?monitoring Leveraging SIEM for Advanced Analytics Architectural Benefits Profiling and?Baselining Advanced Analytics Defeating the Red Team with Purple Team tactics Penetration Testing?with full knowledge Reconnaissance Scanning Enumeration Exploitation Lateral Movement Additional course details: Nexus Humans C)CSA: Cybersecurity Analyst Mile 2 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the C)CSA: Cybersecurity Analyst Mile 2 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
