- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1399 Network courses in Cardiff delivered Live Online
VMware training course description This five-day VMware course features intensive handson training that focuses on installing, configuring, and managing VMware vSphere 8, which includes VMware ESXi 8 and VMware vCenter 8. This course prepares you to administer a vSphere infrastructure for an organization of any size. This course is the foundation for most VMware technologies in the software-defined data center. What will you learn Install and configure ESXi hosts. Deploy and configure vCenter. Create virtual networks using standard and distributed switches. Configure VMs, templates, clones, and snapshots. Manage virtual machine resource allocation. Migrate virtual machines with vSphere vMotion and vSphere Storage vMotion. VMware training course details Who will benefit: Systems administrators and engineers. Prerequisites: Introduction to data communications & networking. Windows/Linux Administration. Duration 5 days VMware training course contents Course Introduction Introductions and course logistics. Course objectives vSphere and Virtualization Overview Explain basic virtualization concepts, Describe how vSphere fits in the software-defined data center and the cloud infrastructure, Recognize the user interfaces for accessing vSphere, Explain how vSphere interacts with CPUs, memory, networks, storage, and GPUs Installing and Configuring ESXi Install an ESXi host, Recognize ESXi user account best practices, Configure the ESXi host settings using the DCUI and VMware Host Client Deploying and Configuring vCenter Recognize ESXi hosts communication with vCenter, Deploy vCenter Server Appliance, Configure vCenter settings, Use the vSphere Client to add and manage license keys, Create and organize vCenter inventory objects, Recognize the rules for applying vCenter permissions, View vCenter logs and events Configuring vSphere Networking Configure and view standard switch configurations, Configure and view distributed switch configurations, Recognize the difference between standard switches and distributed switches, Explain how to set networking policies on standard and distributed switches Configuring vSphere Storage Recognize vSphere storage technologies, Identify types of vSphere datastores, Describe Fibre Channel components and addressing, Describe iSCSI components and addressing, Configure iSCSI storage on ESXi, Create and manage VMFS datastores, Configure and manage NFS datastores Deploying Virtual Machines Create and provision VMs, Explain the importance of VMware Tools, Identify the files that make up a VM Recognize the components of a VM, Navigate the vSphere, Client and examine VM settings and options, Modify VMs by dynamically increasing resources, Create VM templates and deploy VMs from them, Clone VMs, Create customization specifications for guest operating systems, Create local, published, and subscribed content libraries, Deploy VMs from content libraries, Manage multiple versions of VM templates in content libraries Managing Virtual Machines Recognize the types of VM migrations that you can perform within a vCenter instance and across vCenter instances, Migrate VMs using vSphere vMotion, Describe the role of Enhanced vMotion Compatibility in migrations, Migrate VMs using vSphere Storage vMotion, Take a snapshot of a VM, Manage, consolidate, and delete snapshots, Describe CPU and memory concepts in relation to a virtualized environment, Describe how VMs compete for resources Define CPU and memory shares, reservations, and limits Deploying and Configuring vSphere Clusters Create a vSphere cluster enabled for vSphere DRS and vSphere HA, View information about a vSphere cluster Explain how vSphere DRS determines VM placement on hosts in the cluster, Recognize use cases for vSphere DRS settings, Monitor a vSphere DRS cluster Describe how vSphere HA responds to various types of failures, Identify options for configuring network redundancy in a vSphere HA cluster, Recognize vSphere HA design considerations, Recognize the use cases for various vSphere HA settings, Configure a vSphere HA cluster, Recognize when to use vSphere Fault Tolerance Managing the vSphere Lifecycle Enable vSphere Lifecycle Manager in a vSphere cluster, Describe features of the vCenter Update Planner, Run vCenter upgrade prechecks and interoperability reports, Recognize features of vSphere Lifecycle Manager, Distinguish between managing hosts using baselines and managing hosts using images, Describe how to update hosts using baselines, Describe ESXi images, Validate ESXi host compliance against a cluster image and update ESXi hosts, Update ESXi hosts using vSphere Lifecycle Manager, Describe vSphere Lifecycle Manager automatic recommendations, Use vSphere Lifecycle Manager to upgrade VMware Tools and VM hardware

C)CSA: Cybersecurity Analyst Mile 2
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Security Professionals Incident Handling Professionals Anyone in a Security Operations Center Forensics Experts Cybersecurity Analysts Overview Our Certified Cyber Security Analyst course helps you prepare an organization to create a complete end to end solution for proactively monitoring, preventing, detecting, and mitigating threats as they arise in real time. Do not fool yourself, this course is far more advanced than you may expect. It is fast paced and thorough, so you can enjoy a well-rounded experience. Be ready to dig deep into the details of security analysis for today's needs. When we are done you will be able to setup and deploy state of the art open source and for purchase analysis tools, intrusion detection tools, syslog servers, SIEMs, along with integrating them for the entire company to find and an many cases prevent today's exploits. This course maps to the mile2 Certified Cyber Security Analyst Exam as well as the CompTIA CySA+CS0-001 certification exam. Our Certified Cyber Security Analyst course helps you prepare an organization to create a complete end to end solution for proactively monitoring, preventing, detecting, and mitigating threats as they arise in real time.Do not fool yourself, this course is far more advanced than you may expect. It is fast paced and thorough, so you can enjoy a well-rounded experience. Be ready to dig deep into the details of security analysis for today?s needs.When we are done you will be able to setup and deploy state of the art open source and for purchase analysis tools, intrusion detection tools, syslog servers, SIEMs, along with integrating them for the entire company to find and an many cases prevent today?s exploits.This course maps to the mile2 Certified Cyber Security Analyst Exam as well as the CompTIA CySA+CS0-001 certification exam. Blue Team?Principles Network Architecture?and how it lays the groundwork Defensive Network Security Data Locations?and how they tie together Security?Operations?Center The People, Processes, and Technology Triage and Analysis Digital Forensics Incident Handling Vulnerability Management Automation, Improvement, and Tuning Digital?Forensics Investigative Theory and?Processes Digital Acquisition Evidence Protocols Evidence Presentation Computer Forensics?Laboratory Protocols Processing Techniques Specialized?Artifacts Advanced Forensics for Today?s?Exploitations Malware Analysis Creating the Safe Environment Static Analysis Dynamic Analysis Behavior Based Analysis What is different about?Ransomware? Manual Code Reversing Traffic Analysis Manual Analysis Principles Automated?Analysis Principles Signatures?compared to?Behaviors Application Protocols Analysis Principles Networking Forensics Assessing the Current State of Defense with the?Organization Network Architecture and Monitoring Endpoint Architecture and Monitoring Automation, Improvement, and continuous?monitoring Leveraging SIEM for Advanced Analytics Architectural Benefits Profiling and?Baselining Advanced Analytics Defeating the Red Team with Purple Team tactics Penetration Testing?with full knowledge Reconnaissance Scanning Enumeration Exploitation Lateral Movement Additional course details: Nexus Humans C)CSA: Cybersecurity Analyst Mile 2 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the C)CSA: Cybersecurity Analyst Mile 2 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

macOS Support Essentials 14 Sonoma
By Influential Training
Support Essentials course, macOS Support Essentials,

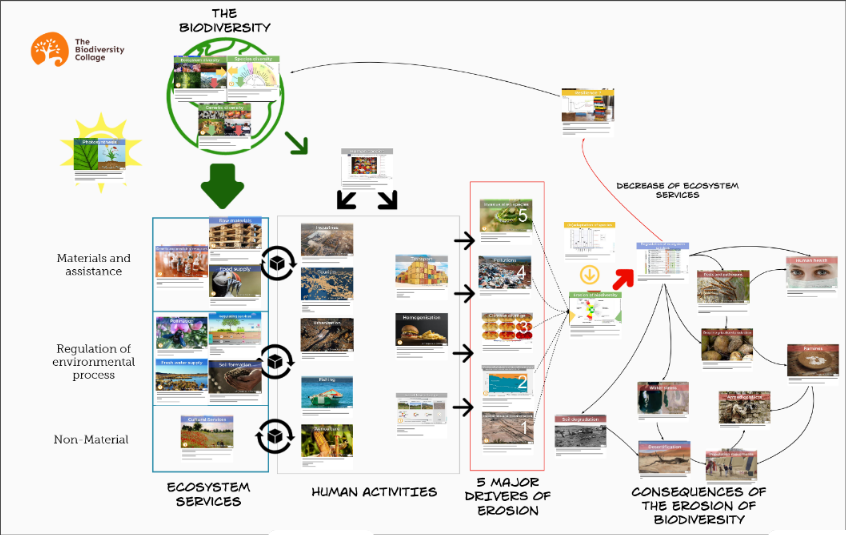
Biodiversity training - Biodiversity collage workshop
By The C Collective
Join a Biodiversity collage workshop to learn about the biodiversity crisis and how to tackle it.
VMware NSX Advanced Load Balancer: Web Application Firewall Security
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Experienced system administrators or network administrators and security professionals Overview By the end of the course, you should be able to meet the following objectives: Describe NSX Advanced Load Balancer architecture Describe the NSX Advanced Load Balancer components and main functions Explain the NSX Advanced Load Balancer key features and benefits Describe NSX Advanced Load Balancer Web Application Firewall architecture Describe the NSX Advanced Load Balancer Web Application Firewall components and main functions Explain the NSX Advanced Load Balancer Web Application Firewall key features and benefits Explain and configure Local Load Balancing constructors such as Virtual Services, Pools, Health Monitors and related components Understand and modify application behavior leveraging Profiles, Policies and DataScripts Configure and customize the NSX Advanced Load Balancer Web Application Firewall Describe and leverage NSX Advanced Load Balancer REST API interfaces and related automation capabilities Describe and configure NSX Advanced Load Balancer Web Application Firewall application and infrastructure monitoring Gather relevant information and perform basic troubleshooting of Web Application Firewall applications leveraging built-in NSX Advanced Load Balancer tooling This three-day course provides comprehensive training on how to configure, maintain and troubleshoot the Web Application Firewall component of the VMware NSX Advanced Load Balancer (Avi Networks) solution as well as provide an understanding of additional security related functionality. This course covers key NSX Advanced Load Balancer (Avi Networks) Web Application Firewall features and functionality offered in the NSX Advanced Load Balancer 18.2 release, including the overall infrastructure, virtual services and application components as well as application troubleshooting and solution monitoring. Access to a software-defined data center environment is provided through hands-on labs to reinforce the skills and concepts presented in the course. Course Introduction Introductions and course logistics Course objectives Introduction to NSX Advanced Load Balancer Introduce NSX Advanced Load Balancer Discuss NSX Advanced Load Balancer use cases and benefits Explain NSX Advanced Load Balancer architecture and components Explain the management, control, data, and consumption planes and their respective functions Introduction to NSX ALB Web Application Firewall Introduce the NSX Advanced Load Balancer Web Application Firewall Discuss NSX Advanced Load Balancer Web Application Firewall use cases and benefits Virtual Services Configuration Concepts Explain Virtual Service components Explain Virtual Service types Explain and configure basic virtual services components such as Application Profiles, Network Profiles, Pools and Health Monitors Attacking and Defending Web Applications Introduce the processes and methodologies used when attacking and defending web applications Introduce the tools used to attack web applications Explain with examples terminology such as Reflected XSS and SQL injection Profiles and Policies Explain and deep dive on Advanced Virtual Service creation Explain and deep dive on Application Profiles and Types such as L4, DNS, Syslog and HTTP Explain and configure advanced application HTTP Profile options Deep dive on Network Profiles and Types Explain and configure SSL Profiles and Certificates Explain and Configure HTTP and DNS policies DDOS Protection Introduce the NSX Advanced Load Balancer rate limiting functionality Explain the NSX Advanced Load Balancer rate limiting functionality Hands on examples of rate limiting in action Customizing Application Delivery with Datascripts Introduce the concept of datascripts to manipulate data Explain the various components and inspection points IWAF Deep Dive Describe the building blocks of the iWAF implementation Explain the various iWAF components Introduce both Positive and Negative security models Explain the iWAF Policies, profiles and rule sets IWAF Core Rule Set Explain the history and rationale of the core rule set Describe the NSX ALB (Avi) Core Rule Set IWAF Custom Rules Describe the power and complexity available via custom rules Explain the rule language Implement various use cases Explain common errors and possible solutions IWAF Operations Describe the iWAF application onboarding process Tuning the iWAF policies Working with iWAF logs and analytics Explaining false positive mitigation tactics IWAF Best Practices Provide guidance on how to get the best results Additional course details:Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware NSX Advanced Load Balancer: Web Application Firewall Security training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware NSX Advanced Load Balancer: Web Application Firewall Security course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Aruba Networks - Scalable WLAN Design And Implementation V8 (SWDI)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Typical candidates for this course are IT professionals who deploy Aruba WLAN with advanced features and individuals who need a basic understanding of AirWave. Overview Upon completion of this course, students will be able to:Explain the integration Mobility Masters and Mobility controllersDescribe redundancy giving the user seamless failoverSetup secure guest access using MultizoneExplain the uses and advantages of clusteringDescribe user mobility in the wireless spectrumIntegrate voice over WiFi and give QOSExplain how roles are assigned to users wireless or wiredLearn to setup remote access using RAPs or VIADescribe how to create a mesh clusterLearn the advantages given to AirGroup when leveraged on an Aruba networkIntegrating wire users into the security given to wireless usersLearn how to use AirWave to monitor the health of the networkLearn how to use AirWave to troubleshoot clientExplain AirWave?s Visual RF feature as well as alerts and triggers This course teaches the knowledge, skills and practical experience required to set up and configure advanced features on Aruba WLAN utilizing the AOS 8.X architecture and features. This course includes lectures and labs which provide the technical understanding and hands-on experience of configuring a redundant Mobility Master with two controllers and two APs. Participants will learn how install a redundant Aruba WLAN network with clustering while using many features like Multizone for guest access, voice optimization and tunneled node. This course includes the AirWave management system and troubleshooting commands. The SWDI course provides the underlying material required to prepare candidates for the Aruba Certified Mobility Professional (ACMP) V8 certification exam. IntroductionMobility Master RedundancyMobility Master and MC OperationsMultizoneIntroduction to MC clustersMobilityRole DerivationRemote AccessVoice OptimizationMeshAdministrationOperationsAirGroupTunneled NodeAirWave IntroductionAirWave Network HealthAirWave Client and Device TroubleshootingAirWave VisualRF, Reports and Alerts

M.D.D DEPRESSION SUPPORT DAILY PACKAGE (DEPRESSION/LONELINESS)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
per week 1 hour session + 15 mins per day for 1 week(6 days) Support emotional uplift intense healing process listening and in-depth analysis a phone call and WhatsApp daily Support network setup 2 weeks support https://relationshipsmdd.com/product/depression-support-daily-package/

Cisco Operating and Implementing Cisco WAN Automation Engine v1.0 (SPWAE)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is designed for: System installers System integrators System administrators Network administrators Solutions designers Overview After taking this course, you should be able to: Explain WAE basics, the purpose of WAE, and its capabilities Understand the Cisco WAE solution implementation Describe the network module configuration process Describe WAE Design software tools, demands creation, BGP modeling, and Failure and Simulation analysis Describe Cisco WAE Design traffic engineering and QoS modeling Explain how to use API with WAE Design and WAE Server Describe the function, components, and processes of Cisco WAE Live The Operating and Implementing Cisco WAN Automation Engine (SPWAE) v1.0 course teaches you, through a combination of lectures and labs, how to install the Cisco© WAN Automation Engine (WAE), builds your confidence with Cisco WAE configuration and basic troubleshooting, and enables you to practice designing and managing bandwidth and traffic engineering.Additionally, you?ll learn the basic knowledge necessary to plan, deploy, configure, and maintain the Cisco WAN Automation Engine solutions. Course Outline WAE Solution and Architecture Overview Implementing a Cisco WAE Solution Network Model Configuration WAE Design Fundamentals Cisco WAE Design Traffic Engineering and Optimization Introducing Cisco WAE API Cisco WAE Live Deployment Additional course details: Nexus Humans Cisco Operating and Implementing Cisco WAN Automation Engine v1.0 (SPWAE) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Cisco Operating and Implementing Cisco WAN Automation Engine v1.0 (SPWAE) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Integrating Linux and Microsoft course description This course is designed for the enterprise-level Linux professional and represents the highest level of professional, distribution-neutral Linux certification within the industry. LPIC-3 300 covers administering Linux enterprise-wide with an emphasis on mixed environments. What will you learn Configure and troubleshoot OpenLDAP. Use OpenLDAP as an authentication backend. Manage software packages. Use Samba - Share configuration - User and group management - Domain integration - Name services - with Linux and Windows clients Integrating Linux and Microsoft course details Who will benefit: Enterprise-level Linux professionals. Prerequisites: Delegates must have an active LPIC-2 certification to receive LPIC-3 certification, but the LPIC-2 and LPIC-3 exams may be taken in any order. Duration 5 days Integrating UNIX and Microsoft course contents OPENLDAP CONFIGURATION OpenLDAP replication Replication concepts, OpenLDAP replication, replication log files, replica hubs, LDAP referrals, LDAP sync replication. Securing the Directory Securing the directory with SSL and TLS, Firewall considerations, Unauthenticated access methods, User/password authentication methods, Maintanence of SASL user DB, certificates. OpenLDAP Server Performance Tuning Measure OpenLDAP performance, Tune software configuration to increase performance, indexes. OPENLDAP AS AN AUTHENTICATION BACKEND LDAP Integration with PAM and NSS Configure PAM to use LDAP for authentication, NSS to retrieve information from LDAP and PAM modules in UNIX. Integrating LDAP with Active Directory and Kerberos Kerberos integration with LDAP, Cross platform authentication, Single sign-on concepts, Integration and compatibility limitations between OpenLDAP and Active Directory. SAMBA BASICS Samba Concepts and Architecture Samba daemons and components, key issues regarding heterogeneous network, Identify key TCP/UDP ports used with SMB/CIFS, Knowledge of Samba3 and Samba4 differences. Configure Samba Samba server configuration file structure, variables and configuration parameters, Troubleshoot and debug configuration problems. Regular Samba Maintenance Monitor and interact with running Samba daemons, Perform regular backups of Samba configuration and state data. Troubleshooting Samba Samba logging, Backup TDB files, Restore TDB files, Identify TDB file corruption, Edit / list TDB file content. Internationalization Internationalization character codes and code pages, differences in the name space between Windows and Linux/Unix with respect to share, names, user/group/computer naming in a non-English environment. SAMBA SHARE CONFIGURATION Linux File System and Share/Service Permissions File / directory permission control, Samba interaction with Linux file system permissions and ACLs, Use Samba VFS to store Windows ACLs. Print Services Printer sharing, integration between Samba and CUPS, Manage Windows print drivers and configure downloading of print drivers, security concerns with printer sharing. SAMBA USER AND GROUP MANAGEMENT Managing User Accounts and Groups User and group accounts, mappings, user account management tools, smbpasswd, file/directory ownership of objects. Authentication, Authorization and Winbind Local password database, password synchronization, passdb backends, Convert between passdb backends, Integrate Samba with LDAP, Winbind service, PAM and NSS. SAMBA DOMAIN INTEGRATION Samba as a PDC and BDC Domain membership and trust relationships, Create and maintain a PDC and BDC with Samba3/4, Add computers to an existing domain, logon scripts, roaming profiles, system policies. Samba4 as an AD compatible Domain Samba 4 as an AD DC, smbclient, how Samba integrates with AD services: DNS, Kerberos, NTP, LDAP. Configure Samba as a Domain Member Server Joining Samba to NT4 and AD domains, obtain a TGT from a KDC. SAMBA NAME SERVICES NetBIOS and WINS WINS concepts, NetBIOS concepts, local master browser, domain master browser, Samba as a WINS server, name resolution, WINS replication, NetBIOS browsing and browser elections, NETBIOS name types. Active Directory Name Resolution DNS for Samba4 as an AD Domain Controller, DNS forwarding with the internal DNS server of Samba4. WORKING WITH LINUX AND WINDOWS CLIENTS CIFS Integration SMB/CIFS concepts, remote CIFS shares from a Linux client, securely storing CIFS credentials, features and benefits of CIFS, permissions and file ownership of remote CIFS shares. Working with Windows Clients browse lists and SMB clients from Windows, Share file/print resources from Windows, the smbclient program, the Windows net utility.

VMware NSX: Troubleshooting and Operations [V4.x]
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Experienced system administrators and network administrators Network and security professionals who work with enterprise networks Overview By the end of the course, you should be able to meet the following objectives: Use the native tools available in NSX to identify and troubleshoot the problems. Use VMware Aria Operations for Logs and VMware Aria Operations for Networks to identify and troubleshoot problems related to the NSX environment. Explain the NSX infrastructure components and the communications between them. Identify, analyze, and troubleshoot problems related to the management, control, and data planes in NSX. Identify, analyze, and troubleshoot problems related to infrastructure preparation and VMware NSX Edge deployments. Identify, analyze, and troubleshoot problems related to logical switching and logical routing. Identify, analyze, and troubleshoot network security problems related to the Distributed firewalls, Gateway firewalls, and Distributed IDS/IPS. Identify, analyze, and troubleshoot problems related to VPN and VMware NSX Advanced Load Balancer. Identify the components and packet flows involved in the NSX datapath and troubleshoot related problems. This five-day, hands-on training course provides the advanced knowledge, skills, and tools to achieve competency in operating and troubleshooting the VMware NSX infrastructure. This course introduces you to workflows of various networking and security constructs along with several operational and troubleshooting tools that help you manage and troubleshoot your VMware NSX environment.In addition, various types of technical problems are presented to you, which you will identify, analyze, and solve through a systematic process. Course Introduction Introduction and course logistics Course objectives NSX Operations and Tools Explain and validate the native troubleshooting tools for NSX Configure syslog, IPFIX, and log collections for the NSX environment Integrate NSX with VMware Aria Operations for Logs and VMware Aria Operations for Networks Validate and review the API methods available to configure the NSX environment Troubleshooting the NSX Management Cluster Describe the NSX Management cluster architecture, components, and communication channels Identify the workflows involved in configuring the NSX Management cluster Validate and troubleshoot the NSX Management cluster formation Troubleshooting Infrastructure Preparation Describe the data plane architecture, components, and communication channels Explain and troubleshoot VMware ESXi transport node preparation issues Explain and troubleshoot NSX Edge deployment issues Troubleshooting Logical Switching Describe the architecture of logical switching List the modules and processes involved in configuring logical switching Explain the importance of VDS in transport nodes Review the architecture and workflows involved in attaching workloads to segments Identify and troubleshoot common logical switching issues Troubleshooting Logical Routing Review the architecture of logical routing Explain the workflows involved in the configuration of Tier-0 and Tier-1 gateways Explain the high availability modes and validate logical router placements Identify and troubleshoot common logical routing issues using both BGP and OSPF Troubleshooting Security Review the architecture of the Distributed Firewall Explain the workflows involved in configuring the Distributed Firewall Review the architecture of the Gateway Firewall Explain the workflows involved in configuring the Gateway Firewall Identify and troubleshoot common Distributed firewall and Gateway Firewall issues Review the architecture and workflows involved in configuring Distributed IDS/IPS Identify and troubleshoot common Distributed IDS/IPS problems. Troubleshooting Services Review the NSX Advanced Load Balancer architecture and components Identify and troubleshoot common NSX Advanced Load Balancer issues Review the IPsec and L2 VPN architecture and components Identify and troubleshoot common IPsec and L2 VPN issues Datapath Walkthrough Verify and validate the path of the packet on the NSX datapath Identify and perform packet captures at various points in the datapath Use NSX CLI and native hypervisor commands to retrieve configurations involved in the NSX datapath Additional course details:Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware NSX: Troubleshooting and Operations [V4.x] training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware NSX: Troubleshooting and Operations [V4.x] course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
![VMware NSX: Troubleshooting and Operations [V4.x]](https://cademy-images-io.b-cdn.net/9dd9d42b-e7b9-4598-8d01-a30d0144ae51/4c81f130-71bf-4635-b7c6-375aff235529/original.png?width=3840)