- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
RESILIA Foundation: Virtual In-House Training
By IIL Europe Ltd
RESILIA™ Foundation: Virtual In-House Training AXELOS RESILIA™: Cyber Resilience Best Practice is designed to help commercial and government organizations around the world prevent, detect, and correct any impact cyber attacks will have on the information required to do business. Adding RESILIA to the existing AXELOS global best practice portfolio, including ITIL® and PRINCE2®, brings a common cyber resilience best practice for security, IT service management, and business. Active cyber resilience is achieved through people, process, and technology. The RESILIA™ Foundation course starts with the purpose, key terms, the distinction between resilience and security, and the benefits of implementing cyber resilience. It introduces risk management and the key activities needed to address risks and opportunities. Further, it explains the relevance of common management standards and best practice frameworks to achieve cyber resilience. Subsequently, it identifies the cyber resilience processes, the associated control objectives, interactions, and activities that should be aligned with corresponding ITSM activities. In the final part of the course, it describes the segregation of duties and dual controls related to cyber resilience roles and responsibilities. What you will Learn At the end of this course, you will be able to: Demonstrate your knowledge of the purpose, benefits, and key terms of cyber resilience Demonstrate your knowledge of the risk management and the key activities needed to address risks and opportunities Demonstrate your knowledge of the purpose of a management system and how best practices and standards can contribute Demonstrate your knowledge of the cyber resilience strategy, the associated control objectives, and their interactions with ITSM activities Demonstrate your knowledge of cyber resilience design, the associated control objectives, and their interactions with ITSM activities Demonstrate your knowledge of cyber resilience transition, the associated control objectives, and their interactions with ITSM activities Demonstrate your knowledge of cyber resilience operation, the associated control objectives, and their interactions with ITSM activities Demonstrate your knowledge of cyber resilience continual improvement, the associated control objectives, and their interactions with ITSM activities Demonstrate your knowledge of the purpose and benefits of segregation of duties and dual controls Course Introduction Course Learning Objectives Course Agenda Activities Course Book Structure RESILIA Certification Introduction to Cyber Resilience What is Cyber Resilience? Defining Cyber Resilience Balancing in Cyber Resilience Characteristics of Cyber Resilience Risk Management Understanding Risk Management: Discussion Defining Risk Management Addressing Risks and Opportunities Managing Cyber Resilience Why and What of Management Systems? Management Systems Common Management Standards and Frameworks Cyber Resilience Strategy What is Strategy? Cyber Resilience Strategy and Activities Security Controls at Cyber Resilience Strategy Interaction Between ITSM Processes and Cyber Resilience Cyber Resilience Design Why Cyber Resilience Design? Cyber Resilience Design Activities Security Controls at Cyber Resilience Design Aligning ITSM Processes with Cyber Resilience Processes Cyber Resilience Transition Why Cyber Resilience Transition? Basics of Cyber Resilience Transition Cyber Resilience Transition: Controls Interaction Between ITSM Processes and Cyber Resilience Cyber Resilience Operation The Purpose of Cyber Resilience Operation Security Controls in Cyber Resilience Operation Interaction Between IT Processes and Cyber Resilience Interaction Between ITSM Functions and Cyber Resilience Cyber Resilience Continual Improvement Continual or Continuous Improvement Maturity Models Continual Improvement Controls The Seven-Step Improvement Process The ITIL CSI Approach Cyber Resilience Roles & Responsibilities Segregating Duties Dual Controls

Telecomms training course description A comprehensive tour of the telecommunications technologies and terminology currently in use, and under development. What will you learn List and describe components of the PSTN. Explain how calls are made over the PSTN Compare analog and digital transmission methods. Describe the technologies within the transport plane. Recognise the benefits of extra features available in today's telephone networks. Telecomms training course details Who will benefit: Anyone new to the Telecommunications industry. Prerequisites: None. Duration 2 days Telecomms training course contents Telephone network architecture Handsets, local loop, distribution points, Local exchanges, main telephone switches, PBXs. Making a call - some basics Telephone call components, how a telephone call works, accessing the local exchange, loop disconnect, DTMF, standards, E.164, PSTN routing, Intelligent Networks, Special Rate Services. Analogue vs Digital Voice characteristics, PSTN bandwidth, analogue signalling, Digital encoding, PCM and the 64k, ADPCM and other voice compression methods. PBXs PABX, Call processing, networking PBXs, PBX facilities, bandwidth, blocking probability and Erlangs, Erlang models, using Erlang tables. Transmission methods Two wire transmission, 64k circuits, Nx64, E1, 2 wire to 4 wire conversion, echo, echo suppression, echo cancellers, twisted pair, coax, fibre optic, power lines, satellite systems, microwave. Signalling Analogue signalling, loop start, earth calling, E&M, AC15. Digital signalling -CAS, robbed bits and E1 slot 16 signalling. Digital signalling CCS, Q.931, SS7, Q.SIG, DPNSS, DASS2. Transport planes PDH, PDH issues, SDH, SDH architecture, SDH standards, SDH bit rates, SDH mulitplexors, DWDM. Networks Circuit Switched Networks, TDM, Packet Switched Networks, Frame Relay, Message Switching, Circuit Switching, STDM, Cell Switching, ATM, ATM cells, ATM traffic parameters, ATM QoS, MPLS. Other network access Modems, modulation, speeds, ISDN, BRI, PRI, xDSL, SDSL, ADSL. Other Services Centrex, VPNs, FeatureNet, CTI, Call Processing Systems, Voice Mail, Automated Attendant Systems, Interactive Voice Response, Call Management Systems, Call Conferencing, Star Services. Mobile communications 3 types of wireless telephone, mobile generations, base stations, cells, GSM, GPRS, 3G, UMTS, WCDMA, 4G, LTE. VoIP overview What is VoIP, VoIP benefits, What is IP? The IP header, Packetising voice, VoIP addressing, H.323, SIP, RTP. Bandwidth requirements.

Professional Sales Programme
By Mpi Learning - Professional Learning And Development Provider
Our suite of modules are based around helping the customer to buy and enabling salespeople to maximise their conversations with their customers.

Complete Maya Beginner to Advanced Training
By ATL Autocad Training London
Why Choose Complete Maya Beginner to Advanced Training? Maya's extensive toolkit includes modeling, animation, simulation, and more, amplifying your versatility and influence in the 3D production pipeline. Click here for more info: Website Beginners or those with basic 3D knowledge. No specific digital media background is required. Duration: 40 hours Training Approach: 1-on-1 Sessions. Schedule: Customize your schedule by pre-booking a convenient hour of your choice, available Monday to Saturday between 9 am and 7 pm Course Structure: I. Introduction to Maya (3 hours) Maya Overview and Applications Interface Navigation and Basic Tools Project Creation and Management II. Basic Polygon Modeling (6 hours) Fundamentals of Polygon Modeling Creating and Editing Basic Shapes Advanced Techniques: Extrusions, Bevels, and NURBS for Organic Shapes III. Intermediate Modeling (6 hours) Advanced Polygon Modeling: Booleans, Deformers, and Surfaces Architectural Model Creation Sculpting Tools for Organic Shapes IV. Texturing and Materials (6 hours) Introduction to Texturing and Material Application Texture Mapping, UV Unwrapping, and Shaders Painting Textures with 3D Paint Tool V. Lighting and Rendering (6 hours) Basic and Advanced Lighting Techniques Realistic Lighting Environments Camera Setup, Composition, and Rendering VI. Animation (9 hours) Keyframe Animation and Animation Curves Character Rigging and Animation Complex Character Rigs, Lip Sync, Facial Animation, Dynamics, and Simulations VII. Rigging (4 hours) Skeleton Creation and Joint Binding Weight Maps and Simple to Complex Rigging Systems VIII. Special Effects (4 hours) Particle Systems, Fluid Dynamics, Fire, and Explosions Advanced Simulations with nCloth and nParticles Paint Effects and Mash Networks IX. Advanced Rendering Techniques (2 hours) Render Layers, Passes, and Global Illumination Mental Ray Rendering and Settings X. Conclusion and Next Steps (1 hour) Course Review, Tips for Further Learning Q&A Session and Feedback Please note that the course outline is flexible and can be tailored based on the learners' needs and proficiency levels. Autodesk Maya Basics to Advanced Level Course: Modeling: Surfaces, Control Vertex, Polygons, Extrusion Techniques, Subdiv Modeling, and More Deformations: Twist, Lattice, Flare, Bend Tools Shapes: Lines, Pen Tools, Surface Manipulation Techniques Animations: Keyframe Setup, Path Animations, Skeletons, IK Handles, Skinning Dynamics and Special Effects: Particle Systems, Fluid Dynamics, Lighting Effects, and Advanced Simulations Texturing and Rendering: Diffuse and Bump Mapping, Reflections, Shaders, Lights, and Camera Techniques Fluid Effects and Ncloth: 2D and 3D Containers, Collision Effects, Wind Simulations, and Gravity Control Rendering: Image and Animation Rendering, Playblast, Resolution Controls, and Output Formats. Advanced Modeling: Master intricate 3D models, including polygon, NURBS, and architectural modeling. Expert Texturing: Create realistic textures, apply shaders, and utilize the 3D paint tool. Complex Animation: Rig characters, perform lip sync, facial animation, and dynamic simulations. Special Effects Mastery: Understand particle systems, fluid dynamics, fire effects, and advanced simulations. Rendering Expertise: Grasp advanced rendering techniques, including layers, passes, and global illumination. Comprehensive Rigging: Develop joints, skeletons, and advanced rigging systems for characters and objects. Fluid Dynamics Proficiency: Manipulate 2D/3D fluid containers, create collision effects, and work with wind/gravity simulations. Advanced Lighting and Camera: Perfect lighting, shadows, and special effects. Master camera setups for diverse visual compositions. Recommended Books: "Introducing Autodesk Maya 2023" by Dariush Derakhshani and Randi L. Derakhshani "Mastering Autodesk Maya 2023" by Todd Palamar "Maya Character Creation: Modeling and Animation Controls" by Chris Maraffi "Maya Secrets of the Pros" by John Kundert-Gibbs and Dariush Derakhshani "The Art of 3D Computer Animation and Effects" by Isaac Victor Kerlow Advanced Maya Training Tailored to You: Elevate your Maya skills with specialized training covering essential areas like modeling, UV mapping, texturing, lighting, camera movement, and rigging. Your learning experience is personalized to match your unique requirements and preferences. Discuss your goals with our trainer, and we'll create a syllabus tailored just for you. Flexible Training Choices: Select between in-person sessions at our UK center or attend live online classes, offering convenience and accessibility. Certified Instructors: Benefit from expert guidance provided by Autodesk Authorized Trainers from London Design Training Course. Hands-On Learning: Our practical approach combines theory with step-by-step demonstrations, allowing ample time for hands-on practice on your computer with Maya. You'll retain all the files you create. Compatibility Across Platforms: Maya training caters to both Windows and Mac users, ensuring compatibility with various versions of Maya. Comprehensive Training Package: Participants receive an e-certificate upon successful completion, validating their Maya training. Lifetime Support: Enjoy a lifetime of email support post-training, ensuring assistance with any queries or challenges that arise. Tailored to Your Version: Training can be adapted to your preferred Maya version, ensuring you learn using the most relevant and up-to-date software features. Download Maya https://www.autodesk.co.uk Highly skilled mentors with practical experience. Cutting-edge facilities ensuring an immersive learning environment. Comprehensive courses spanning diverse design disciplines. Practical projects to enhance your portfolio. Networking avenues within the dynamic design community. Skills attuned to current industry trends. Opportunities for professional growth. Choose from flexible in-person or online classes. Internationally recognized training credentials. Engage in London's thriving art and design scene.

Facilitation Skills for Business Analysts: In-House Training
By IIL Europe Ltd
Facilitation Skills for Business Analysts: In-House Training This course is part of IIL's Business Analysis Certificate Program (BACP), a program designed to help prepare individuals pass the IIBA® Certification exam to become a Certified Business Analysis Professional (CBAP™). Business analysts are communicators who bridge the gap between people with business needs and knowledge and the people who will provide solutions. Business analysts are continuously involved in communications with stakeholders and developers as they create the solution to business problems. They participate in information-gathering sessions including interviewing, joint requirements definition, and Joint Application Design (JAD) workshops which are used to streamline information gathering and get immediate validation from user representatives. The business analyst is also involved with negotiating the solution with the stakeholders, upper-level management, and the developers, mediating among the groups when disagreements take place, and influencing the results of decisions during the solution cycle. This course teaches the methods needed to organize and run information-gathering events. It combines the basics of graphic decision making and modeling with facilitation, communication, and meeting management skills. What you will Learn At the end of this program, you will be able to: Identify the major touch points between key BABOK® Guide knowledge areas and business analysis communication Describe the facilitation skills that are most supportive of those intersections Improve your ability to apply these skills in the context of your business analyst functions Foundation Concepts The role of the Business analyst (BA) An Introduction to the BABOK® Guide Business analyst roles and the product / project life cycle (PLC) Facilitation skills for the business analyst The BABOK® Guide and Communication An introduction to the communication process Addressing basic communications challenges Planning business analysis communication Communication and BABOK® Guide tasks Targeted Elicitation Techniques Synergy between communication and targeted elicitation techniques Preparing for elicitation Cornerstone targeted technique: interviews Other targeted elicitation techniques Related general communication skills Group Elicitation Techniques Synergy between requirements communication and group elicitation techniques Cornerstone group elicitation technique - requirements workshops Other group elicitation techniques Related general communication skills - meeting management best practices Related general communication skills - facilitating best practices Process / Model-Based Elicitation Techniques Synergy between requirements communication and process / model-based elicitation techniques Process / model-based elicitation techniques Related interpersonal skills - problem solving and decision making Investigative Elicitation Techniques Synergy between requirements communication and investigative elicitation techniques Cornerstone investigative elicitation technique - document analysis Other investigative elicitation techniques Summary of elicitation techniques by usage in the requirements process Using Presentations, Structured Walkthroughs, and Influencing Structured walkthroughs, presentations, and influencing within BABOK® Guide tasks Cornerstone technique - structured walkthroughs General communication skill - presenting Related interpersonal skill - influencing Special Facilitation Skills - Negotiating and Mediating Negotiating Mediating

Finance for Non-Finance Professionals in Oil & Gas Petroleum Fiscal Regimes & Applied Finance for Non-Finance Oil & Gas Professionals
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course This separately bookable 3 full-day course is not designed to skill Oil & Gas engineers to be accountants, but to give the participants the confidence and ability to communicate with accountants and finance managers and to improve their own financial decision making. For technical professionals, a high level of single subject matter expertise is no longer sufficient for superior management performance. Oil & Gas technical professionals who wish to succeed in the resources industry are required to develop skills beyond their core functional knowledge. An understanding of financial information and management, and an awareness of the economic theory that drives value creation, are an integral part of the managers required suite of skills. This course can also be offered through Virtual Instructor Led Training (VILT) format. Training Objectives Workshop A: Finance for Non-Finance for Oil & Gas Professionals Attend this industry specific course and benefit from the following: Demystify financial jargon and fully interpret financial statements Understand Balance Sheets and Profit & Loss statements of Oil & Gas companies Discover the crucial distinction between cash flow and profit Understand how to make correct investment decisions using Net present Value and Internal Rate of Return Interpret oil and gas company financial reports using ratio analysis Learn the difference between cash costs and full costing of energy products Learn how to manage working capital for increased shareholder value Workshop B: Petroleum Fiscal Regimes and Applied Finance for Oil & Gas Industry Professionals Attend this advanced Training course to enhance your financial acumen from the following: Build and compare cash flow based models of both production sharing contract projects and royalty regime projects Gain an awareness of the different valuation methods for producing properties and undeveloped acreage Learn the industry specific accounting issues that apply when interpreting oil and gas company financial statements Understand how the physical characteristics of energy assets (e.g. reserves, reservoir quality) are translated into project valuations Learn how the investment analysts value oil and gas stocks and make buy/sell recommendations Target Audience This course is specifically designed for those with a non-finance background training from the Oil & Gas sector and requires only basic mathematical ability as a pre-requisite. It is presented in a manner that reduces the jargon to basic principles and applies them to numerous real-life examples. This course has been researched and developed for Managers, Superintendents, Supervisors, Engineers, Planners, Lawyers, Marketers, Team Leaders and Project Coordinators in the technical and non-technical departments in the Oil and Gas industry. Course Level Basic or Foundation Trainer Your expert course leader has presented over 300 courses and seminars in financial management. He began his career as a graduate in the Corporate Treasury of WMC Ltd having completed a degree in Applied Mathematics and Geology at Monash University. After five years with WMC, he pursued an MBA in finance and accounting at Cornell University in New York. He later gained a PhD in energy policy from the University of Melbourne. He worked for WMC Ltd in Perth as a Senior Financial Analyst in the Minerals Division and subsequently as an Energy Analyst in the Petroleum Division. In April 1997, he established an independent consultancy business providing advice to companies such as Woodside, Shell and Japan Australia LNG (MIMI). He spent many years as a consultant and commercial manager in the North West Shelf Gas project in Western Australia. Since 2006, he has been an Adjunct Fellow at the Macquarie University Applied Finance Centre where he teaches courses in valuation, financial statement modelling, and resources industry investment analysis. His background in geology and mathematics allows him to empathise with those who seek an understanding of finance but are approaching the learning experience with a technical mind. He receives consistently high ratings for his breadth of knowledge of the subject matter. He presents in a lively interactive style using real life examples and cases. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

Cross Border Electricity Trading in Asia - Renewable Energy, Digital Technologies and New Operational Flexibility Solutions
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) This 3 half-day Virtual Instructor Led Training (VILT) course highlights the impact of the introduction of renewable energy, digital technologies and new operational flexibility solutions in the electricity trading market. These advancements facilitate unique opportunities and challenges for cross border trading of electricity. Most countries in Asia, have designed their own portfolio of climate actions with an accelerated penetration of renewable energy (or by importing renewable energy into their local grids). These changes are taking place at unprecedented speed and add further complexity to the operation of electricity trading markets, while presenting new opportunities. The Asian market, can tap into its vast potential of solar, wind and geothermal energy sources. A global, unified vision is emerging to support each of countries' energy needs and decarbonization goals. This VILT course will highlight priorities of each country to achieve its energy goals. The main operational flexibilities of each type of renewable resource are discussed in detail. The course also discusses the main components of Power Purchase Agreements and advancements in digitalization and how digital technologies can influence the energy market and cross border electricity trading. Key Takeaways: New Energy Market Design Cross Border Trading PPAs Mechanisms and Examples of PPAs The Increased Penetration of Renewable Resources in the Power Systems and How It Stimulates Cross Border Trading How Digital Innovation Drives Energy Markets and Cross Border Trading Training Objectives Upon completion of this VILT course, participants will be able to: Be familiar with the global vision of One Sun, One World, One Grid Understand the major trends reshaping the energy markets Learn how innovative digital technologies change the energy markets Understand why sustainable energy markets require a tighter coordination between transmission and distribution system operators Engage with each other to design the energy market of the future Target Audience This VILT course will benefit policy makers and regulators from energy agencies, transmission companies and utilities as well as power system engineers and power system operators from control centre and ISO. Training Methods The VILT will be delivered online in 3 half-day sessions comprising 4 hours per day, including time for lectures, discussion, quizzes and short classroom exercises. Course Duration: 3 half-day sessions, 4 hours per session (12 hours in total). Trainer Your expert course leader is a Utility Executive with extensive global experience in power system operation and planning, energy markets, enterprise risk and regulatory oversight. She consults on energy markets integrating renewable resources from planning to operation. She led complex projects in operations and conducted long term planning studies to support planning and operational reliability standards. Specializing in Smart Grids, Operational flexibilities, Renewable generation, Reliability, Financial Engineering, Energy Markets and Power System Integration, she was recently engaged by the Inter-American Development Bank/MHI in Guyana. She was the Operations Expert in the regulatory assessment in Oman. She is a registered member of the Professional Engineers of Ontario, Canada. She is also a contributing member to the IEEE Standards Association, WG Blockchain P2418.5. With over 25 years with Ontario Power Generation (Revenue $1.2 Billion CAD, I/S 16 GW), she served as Canadian representative in CIGRE, committee member in NSERC (Natural Sciences and Engineering Research Council of Canada), and Senior Member IEEE and Elsevier since the 90ties. Our key expert chaired international conferences, lectured on several continents, published a book on Reliability and Security of Nuclear Power Plants, contributed to IEEE and PMAPS and published in the Ontario Journal for Public Policy, Canada. She delivered seminars organized by the Power Engineering Society, IEEE plus seminars to power companies worldwide, including Oman, Thailand, Saudi Arabia, Malaysia, Indonesia, Portugal, South Africa, Japan, Romania, and Guyana. Our Key expert delivered over 60 specialized seminars to executives and engineers from Canada, Europe, South and North America, Middle East, South East Asia and Japan. Few examples are: Modern Power System in Digital Utilities - The Energy Commission, Malaysia and utilities in the Middle East, GCCIA, June 2020 Assessment of OETC Control Centre, Oman, December 2019 Demand Side management, Load Forecasting in a Smart Grid, Oman, 2019 Renewable Resources in a Smart Grid (Malaysia, Thailand, Indonesia, GCCIA, Saudi Arabia) The Modern Power System: Impact of the Power Electronics on the Power System The Digital Utility, AI and Blockchain Smart Grid and Reliability of Distribution Systems, Cyme, Montreal, Canada Economic Dispatch in the context of an Energy Market (TNB, Sarawak Energy, Malaysia) Energy Markets, Risk Assessment and Financial Management, PES, IEEE: Chicago, San Francisco, New York, Portugal, South Africa, Japan. Provided training at CEO and CRO level. Enterprise Risk methodology, EDP, Portugal Energy Markets: Saudi Electricity Company, Tenaga National Berhad, Malaysia Reliability Centre Maintenance (South East Asia, Saudi Electricity Company, KSA) EUSN, ENERGY & UTILITIES SECTOR NETWORK, Government of Canada, 2016 Connected+, IOT, Toronto, Canada September 2016 and 2015 Smart Grid, Smart Home HomeConnect, Toronto, Canada November 2014 Wind Power: a Cautionary Tale, Ontario Centre for Public Policy, 2010 POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

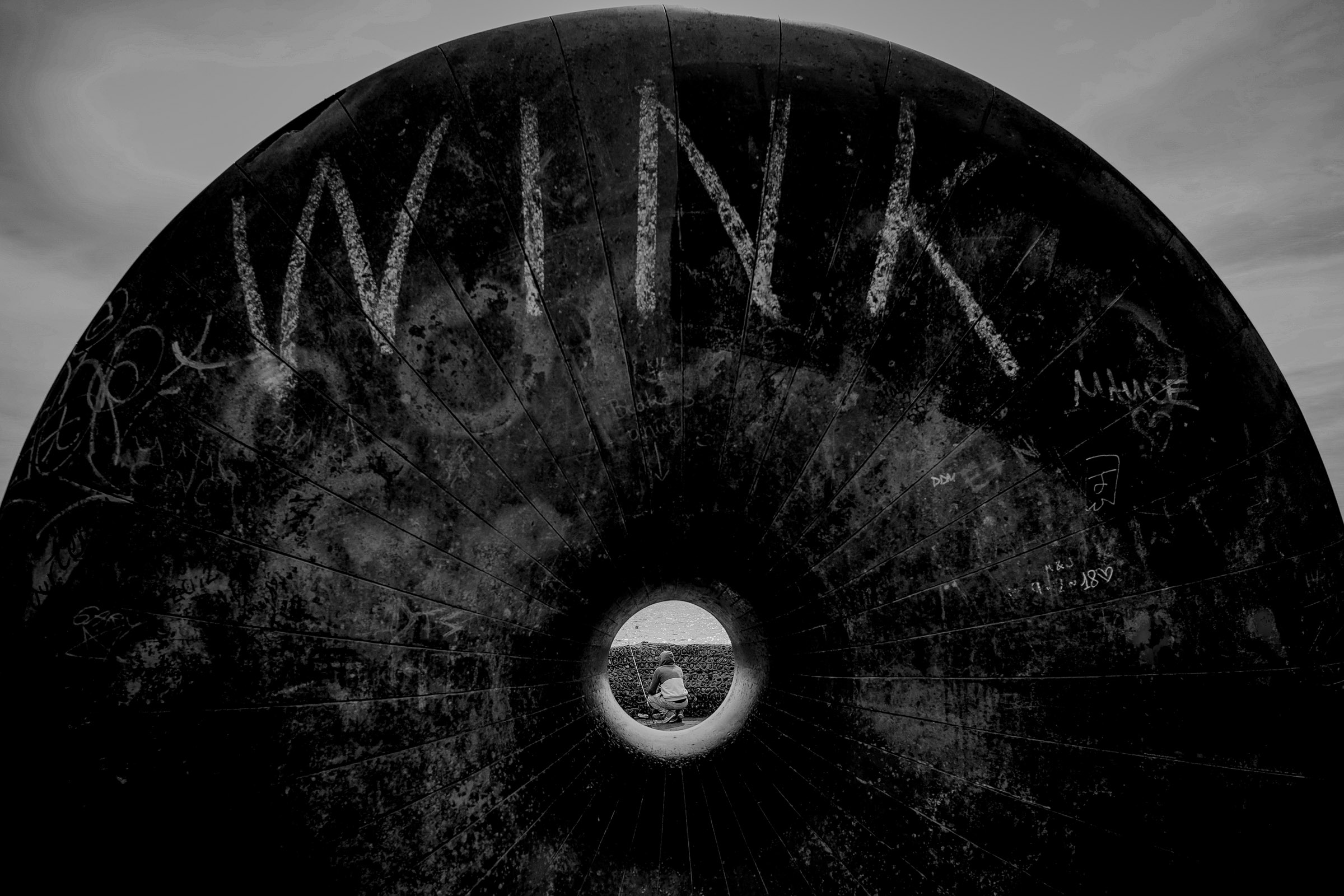
Photography Course | For Beginners
By Gavin Jacob Power | Photographer
The essential course for those starting from zero who want a private lesson guidance. You will leave shooting in manual mode and composing a frame like a pro.
SAFe for Government: In-House Training
By IIL Europe Ltd
SAFe® for Government: In-House Training Transitioning to Lean-Agile practices for building technology-based capabilities is especially challenging in the government context. But issues of legacy governance, contracting, and organizational barriers can be overcome with the right information and strategies. During this course, attendees will learn the principles and practices of the Scaled Agile Framework® (SAFe®), how to execute and release value through Agile Release Trains, and what it means to lead a Lean-Agile transformation of a program inside a government agency. Attendees gain an understanding of the Lean-Agile mindset and why it's an essential foundation for transformation. They'll also get practical advice on building high-performing, multi-vendor Agile teams and programs, managing technology investments in Lean flow, acquiring solutions with Agile contracting, launching the program, and planning and delivering value using SAFe®. Attendees also learn how specific leadership behaviors can drive successful organizational change in government. What you will Learn To perform the role of a SAFe® for Government leader, you should be able to: Transition government programs from traditional software and systems development models to Lean-Agile and DevOps mindsets, principles, and practices using SAFe® Adapt technology strategy, budgeting and forecasting, acquisition, compliance, and governance processes to flow-based practices using emerging government guidelines Organize government programs into one or more Agile Release Trains (ARTs) and execute in Program Increments (PIs) Explore Large Solution coordination in a government and multi-vendor environment Identify and internalize the mindset and leader behaviors essential to successful Lean-Agile transformation Follow success patterns for SAFe® implementations adapted to the government context Build a preliminary outline of next steps to begin and / or accelerate the SAFe® implementation in your program or agency Advancing Lean-Agile in government Embracing a Lean-Agile mindset Understanding SAFe® Principles Creating high-performing Agile teams and programs Planning with cadence and synchronization Delivering value in Program Increments Mapping the path to agency and program agility Leading successful change

