- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1177 Memory courses
Overview The Computer Programming Specialist Certificates course covers fundamental concepts of computer programming, including basic terms, computer anatomy, software development, networking, internet security, application basics, web browsing, file management, and more. Participants will gain the necessary skills to become proficient in computer programming. Learning Outcomes: Develop a strong understanding of basic computer terms, the anatomy of a PC, and how a PC works. Gain knowledge about different types of software, operating systems, and legal issues related to computer programming. Learn about networking basics, internet concepts, internet security, and the role of computers in the workplace. Understand the basics of application development and working with various applications. Acquire skills in web browsing, managing web pages, and working with bookmarks. Learn how to manage files and folders, customize computer settings, and perform basic tasks on a computer. Familiarize yourself with printing techniques, file compression, and maintaining data security. Why buy this Computer Programming Specialist Certificate? Unlimited access to the course for a lifetime. Opportunity to earn a certificate accredited by the CPD Quality Standards and CIQ after completing this course. Structured lesson planning in line with industry standards. Immerse yourself in innovative and captivating course materials and activities. Assessments designed to evaluate advanced cognitive abilities and skill proficiency. Flexibility to complete the Course at your own pace, on your own schedule. Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience. Unlock career resources for CV improvement, interview readiness, and job success. Certification After studying the course materials of the Computer Programming Specialist Certificate there will be a written assignment test which you can take either during or at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £5.99. Original Hard Copy certificates need to be ordered at an additional cost of £9.60. Who is this course for? Aspiring software developers seeking foundational knowledge. Individuals interested in a career shift to technology sectors. University students supplementing their IT or Computer Science degrees. Entrepreneurs needing coding skills for tech startups. Hobbyists eager to create personal digital projects. Prerequisites This Computer Programming Specialist Certificate does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Computer Programming Specialist Certificate was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Career path Software Developer: £25,000 - £70,000 Per Annum Database Administrator: £30,000 - £60,000 Per Annum Systems Analyst: £35,000 - £65,000 Per Annum Web Developer: £24,000 - £50,000 Per Annum IT Project Manager: £40,000 - £80,000 Per Annum Data Analyst: £26,000 - £60,000 Per Annum Course Curriculum Module 01 Basic Terms 00:15:00 Types of Computers 00:15:00 Anatomy of a PC 00:30:00 How a PC Works 00:15:00 CPU and Memory 00:30:00 Input Devices 00:15:00 Output Devices 00:15:00 Secondary Storage Devices 00:30:00 The Basics 00:15:00 Operating Systems and Applications 00:30:00 How is Software Built 00:15:00 Types of Software 00:15:00 Legal Issues 00:15:00 Module 02 Basic Terms 00:15:00 Advanced Terms 00:15:00 Networking Basics 00:15:00 Basic Internet Concepts 00:30:00 Internet Security 00:30:00 Computers in the Workplace 00:15:00 Tele-Commuting 00:15:00 The Electronic World 00:15:00 Ergonomics 00:15:00 Safety and the Environment 00:15:00 Being Proactive 00:15:00 Identifying Yourself 00:15:00 Protecting Your Data 01:00:00 Understanding Malware 00:15:00 Protecting Against Malware 00:15:00 Module 03 Application Basics 00:30:00 Basic Applications 01:00:00 Working with a Window 01:00:00 Working with WordPad 01:00:00 Working With Applications 01:00:00 Basics of Web Browsers 01:00:00 Browsing the Web 00:15:00 Working with Bookmarks 01:00:00 Working With Web Pages 01:00:00 Printing Web Pages 01:00:00 Module 04 First Steps 00:30:00 Basic Tasks 01:00:00 Using the Desktop 00:15:00 Customizing Your Computer 00:15:00 Printing 00:15:00 The Basics of Files and Folders 00:10:00 Managing Files and Folders, Part I 01:00:00 Managing Files and Folders, Part II 00:15:00 Viewing File or Folder Properties 00:30:00 Working With Files and Folders 00:30:00 Compressed Files 00:05:00 Assignment Assignment - Computer Programming Specialist Certificate 00:00:00

Course Overview Won't it be great if you could recover your lost data from your device or ensure that the hackers cannot reach you? What about tracking the hacker and get back the data they have stolen from you? Digital security has become one of the greatest concerns today. Learn how you can secure your device and find out black hat hacker criminals from this Digital Forensics for Pentesting Course and ensure data security. In this Digital Forensics for Pentesting Course, you will learn the importance of digital forensic investigation, the basics of cybersecurity, pentesting and digital forensic. You'll understand the functions of Malware and how to track them back. This course is ideal for understanding how digital devices can be hacked and how to prevent them. You will be able to understand digital forensic investigation steps with easily understandable and bite-sized lessons. Learning Outcomes Get a clear understanding of what digital forensic investigation is Be able to produce professional and legal digital forensic reports Learn to utilise various forensic tools for digital forensic investigation Properly handle digital media during the investigation Recover deleted data from various devices and operating systems Be able to track hackers malicious movement Who is this course for? This course will be helpful for anyone who wants to learn about pentesting and interested in digital forensic investigation. You will learn how to understand digital forensic investigation step by step from this course. Entry Requirement This course is available to all learners, of all academic backgrounds. Learners should be aged 16 or over to undertake the qualification. Good understanding of English language, numeracy and ICT are required to attend this course. Certification After you have successfully completed the course, you will be able to obtain an Accredited Certificate of Achievement. You can however also obtain a Course Completion Certificate following the course completion without sitting for the test. Certificates can be obtained either in hardcopy at the cost of £39 or in PDF format at the cost of £24. PDF certificate's turnaround time is 24 hours, and for the hardcopy certificate, it is 3-9 working days. Why choose us? Affordable, engaging & high-quality e-learning study materials; Tutorial videos/materials from the industry-leading experts; Study in a user-friendly, advanced online learning platform; Efficient exam systems for the assessment and instant result; The UK & internationally recognized accredited qualification; Access to course content on mobile, tablet or desktop from anywhere anytime; The benefit of career advancement opportunities; 24/7 student support via email. Career Path Digital Forensics for Pentesting Course is a useful qualification to possess and would be beneficial for any related profession or industry such as: Digital Forensic Investigators Pentesters Data Security Officers White Hat Hackers Course Overview Course Overview 00:06:00 Building Your Forensics Lab Environment Using VirtualBox Lab - Installing CSI Linux 00:13:00 Lab - Creating a Kali Live (Forensic Mode) VM Using VirtualBox 00:06:00 Lab - Create a Virtual Install Kali Image Using VirtualBox 00:07:00 Lab - Create Virtual Install of Windows 10 Using VirtualBox 00:08:00 Install Additional Tool Using Katoolin3 00:10:00 Using Kali Forensic Mode and Autopsy Lab - Simulate Creating a Disk Image for a Forensic Analysis 00:11:00 Lab - Examining a forensic Disk Image Using Autopsy 00:12:00 Digital Forensics Case Management Lab -Digital Forensics Using Autopsy Part I 00:11:00 Lab - Digital Forensics Using Autopsy Part II 00:07:00 Lab - Installing the WebMap-Nmap Dashboard 00:12:00 Open-source intelligence (OSINT) Lab - Conducting OSINT Using CSI Linux Investigator 00:08:00 Lab - Find Social Media Accounts Using Sherlock 00:07:00 Computer Forensics Attaching an External USB Device in Kali 00:07:00 Lab - Memory Forensics Using the Volatility Framework 00:18:00 Lab - Acquiring a Forensic Copy of the Windows Registry 00:15:00 Lab - Analyzing the Windows Registry for Evidence 00:14:00 Using Shodan to Search for Vulnerable devices Lab - Preparing CSI Investigator to Use Shodan 00:05:00 Lab - Using Shodan to Find Vulnerable Devices 00:16:00 Lab - Using Shodan to Search for Vulnerable Databases 00:08:00 Stenography Lab - Using the EXIFtool to Read and Write EXIF Tags 00:11:00 Using the EXIFtool to Read and Write EXIF Tags 00:10:00 Network forensics Using Wireshark Overview of Wireshark 3.2 00:11:00 Wireshark Capture Options 00:07:00 Wireshark Toolbar Icons 00:04:00 Lab - Capturing a 3-way TCP Handshake Using Wireshark 00:05:00 Lab - Installing a Wireless Adapter in Kali 00:09:00 Lab - Hacking a Wireless Network Using Kali Linux 00:14:00 Capturing Wireless Traffic Using Wireshark 00:05:00 Practice What You Have learned Lab - CTF Lab Build for HA: Forensics 00:11:00 Lab - Capture flag #1 00:12:00 Lab - Capture flag #2 00:10:00 Lab - Capture flag #3 00:20:00 Lab - Capture flag #4 00:09:00 Certificate and Transcript Order Your Certificates and Transcripts 00:00:00

If you are looking for a new and challenging career in the area of computer programming or you just want to learn about this anyway, then our Diploma in Computer Programming course will give you the skills you need. Description: Computer Programming is regularly the primary port of call for anybody hoping to move into a full-time role in programming advancement. A comprehension of a scripting language will likewise offer many open doors for advancement as it gives understanding and information on how frameworks are constructed and executed within associations. This course is for learners with next to zero prior programming background, however a desire to comprehend computational ways to deal with critical thinking. This course starts by introducing the student to basic concepts and terminology of software development and helps them gain the skills that are required for writing and designing a program. It also gives a review of the software development process along with an introduction to programming constructs and approaches. If you want to learn computer programming, yet don't have any detailed knowledge, you'll appreciate this programming course. You will gain in depth knowledge and get up-to-date information in this field of your interest. Who is the course for? Beginners who are new to the world of programming. Individuals who want to master computer programming. Computer Programmers of a different language. Students. Entry Requirement: This course is available to all learners, of all academic backgrounds. However, an educational background or experience in business communications will be an advantage. Learners should be aged 16 or over to undertake the qualification. Good understanding of English language, numeracy and ICT are required to attend this course. Assessment: At the end of the course, you will be required to sit an online multiple-choice test. Your test will be assessed automatically and immediately so that you will instantly know whether you have been successful. Before sitting for your final exam you will have the opportunity to test your proficiency with a mock exam. Certification: After you have successfully passed the test, you will be able to obtain an Accredited Certificate of Achievement. You can however also obtain a Course Completion Certificate following the course completion without sitting for the test. Certificates can be obtained either in hard copy at a cost of £39 or in PDF format at a cost of £24. PDF certificate's turnaround time is 24 hours and for the hardcopy certificate, it is 3-9 working days. Why choose us? Affordable, engaging & high-quality e-learning study materials; Tutorial videos/materials from the industry leading experts; Study in a user-friendly, advanced online learning platform; Efficient exam systems for the assessment and instant result; The UK & internationally recognised accredited qualification; Access to course content on mobile, tablet or desktop from anywhere anytime; The benefit of career advancement opportunities; 24/7 student support via email. Career Path: Diploma in Computer Programming is a useful qualification to possess, and would be beneficial for the following professionals: Software developer. Information systems specialist. PC specialist. Mid-range programmer. UNIX/Linux programmer. Computer Fundamentals Basic Terms 00:15:00 Types of Computers 00:15:00 Anatomy of a PC 00:30:00 How a PC Works 00:15:00 CPU and Memory 00:30:00 Input Devices 00:15:00 Output Devices 00:15:00 Secondary Storage Devices 00:30:00 The Basics 00:15:00 Operating Systems and Applications 00:30:00 How is Software Built 00:15:00 Types of Software 00:15:00 Legal Issues 00:15:00 COMPUTER PROGRAMMING 101 COMPUTER PROGRAMMING 101 01:00:00 WHAT IS COMPUTER PROGRAMMING AND WHY SHOULD I CARE? 00:30:00 What a Programmer Does 01:00:00 COMPUTER PROGRAMMING AT A GLANCE COMPUTER PROGRAMMING AT A GLANCE 01:00:00 UNDERSTANDING THE LANGUAGE OF THE COMPUTER 00:30:00 Choosing a Language 00:30:00 BASIC PROGRAMMING LANGUAGE BASIC Programming Language 01:00:00 Getting Started with BASIC Programming Language 01:00:00 BASIC Overview of BASIC Components 01:00:00 BASIC Special Variables 01:00:00 BASIC Probability Functions 01:00:00 Filtering the Data Set or Splitting the Data Set 01:00:00 DATA Blocks 01:00:00 DELETE Statement 01:00:00 FORNEXT Statement 01:00:00 IF. . . THEN Statement 01:00:00 JOB STATISTICS AT A GLANCE Computer Programming 01:00:00 Employment Outlook 00:15:00 How to Find A Great Job After Graduation 01:00:00 Additional Supporting Material Fundamentals of Computer-Programming with C+ 00:00:00 Refer A Friend Refer A Friend 00:00:00 Mock Exam Mock Exam- Diploma in Computer Programming 00:20:00 Final Exam Final Exam- Diploma in Computer Programming 00:20:00 Certificate and Transcript Order Your Certificates and Transcripts 00:00:00

Visual Analytics Best Practice
By Tableau Training Uk
This course is very much a discussion, so be prepared to present and critically analyse your own and class mates work. You will also need to bring a few examples of work you have done in the past. Learning and applying best practice visualisation principles will improve effective discussions amongst decision makers throughout your organisation. As a result more end-users of your dashboards will be able to make better decisions, more quickly. This 2 Day training course is aimed at analysts with good working knowledge of BI tools (we use Tableau to present, but attendees can use their own software such as Power BI or Qlik Sense). It is a great preparation for taking advanced certifications, such as Tableau Certified Professional. Contact us to discuss the Visual Analytics Best Practice course Email us if you are interested in an on-site course, or would be interested in different dates and locations This Tableau Desktop training intermediate course is designed for the professional who has a solid foundation with Tableau and is looking to take it to the next level. Attendees should have a good understanding of the fundamental concepts of building Tableau worksheets and dashboards typically achieved from having attended our Tableau Desktop Foundation Course. At the end of this course you will be able to communicate insights more effectively, enabling your organisation to make better decisions, quickly. The Tableau Desktop Analyst training course is aimed at people who are used to working with MS Excel or other Business Intelligence tools and who have preferably been using Tableau already for basic reporting. The course includes the following topics: WHAT IS VISUAL ANALYSIS? Visual Analytics Visual Analytics Process Advantages of Visual Analysis Exercise: Interpreting Visualisations HOW DO WE PROCESS VISUAL INFORMATION? Memory and Processing Types Exercise: Identifying Types of Processing Cognitive Load Exercise: Analysing Cognitive Load Focus and Guide the Viewer Remove Visual Distractions Organise Information into Chunks Design for Proximity Exercise: Reducing Cognitive Load SENSORY MEMORY Pre-attentive Attributes Quantitatively-Perceived Attributes Categorically-Perceived Attributes Exercise: Analysing Pre-attentive Attributes Form & Attributes Exercise: Using Form Effectively Colour & Attributes Exercise: Using Colour Effectively Position & Attributes Exercise: Using Position Effectively ENSURING VISUAL INTEGRITY Informing without Misleading Gestalt Principles Visual Area Axis & Scale Colour Detail Exercise: Informing without Misleading CHOOSING THE RIGHT VISUALISATION Comparing and Ranking Categories Comparing Measures Comparing Parts to Whole Viewing Data Over Time Charts Types for Mapping Viewing Correlation Viewing Distributions Viewing Specific Values DASHBOARDS AND STORIES Exercise: Picking the Chart Type Exercise: Brainstorming Visual Best Practice Development Process for Dashboards and Stories Plan the Visualisation Create the Visualisation Test the Visualisation Exercise: Designing Dashboards and Stories This training course includes over 20 hands-on exercises to help participants “learn by doing” and to assist group discussions around real-life use cases. Each attendee receives an extensive training manual which covers the theory, practical applications and use cases, exercises and solutions together with a USB with all the materials required for the training. The course starts at 09:30 on the first day and ends at 17:00. On the second day the course starts at 09:00 and ends at 17:00. Students must bring their own laptop with an active version of Tableau Desktop 10.5 (or later) pre-installed. What People Are Saying About This Course "Steve was willing to address questions arising from his content in a full and understandable way"Lisa L. "Really enjoyed the course and feel the subject and the way it was taught was very close to my needs"James G. "The course tutor Steve was incredibly helpful and taught the information very well while making the two days very enjoyable."Bradd P. "The host and his courses will give you the tools and confidence that you need to be comfortable with Tableau."Jack S. "Steve was fantastic with his knowledge and knowhow about the product. Where possible he made sure you could put demonstrations in to working practice, to give the audience a clear understanding."Tim H. "This was a very interesting and helpful course, which will definitely help me produce smarter, cleaner visualisations that will deliver more data-driven insights within our business."Richard A. "Steve is very open to questions and will go out of his way to answer any query. Thank you"Wasif N. "Steve was willing to address questions arising from his content in a full and understandable way"Lisa L. "Really enjoyed the course and feel the subject and the way it was taught was very close to my needs"James G.

Embarking on a journey through the art of 'Accupressure Massage,' this course offers an oasis of tranquillity and skill. Imagine yourself mastering the ancient techniques of acupressure massage, an art revered for its therapeutic benefits. With searches for 'acupressure massage near me' rising, our course is a timely answer to this growing interest. Envision the soothing touch of acupressure foot massage, bringing relief and relaxation. As you progress, the mysteries of acupressure back massage unfold, revealing techniques that alleviate deep-seated tension. Furthermore, the course introduces the unique skills of acupressure chair massage, catering to the needs of those seeking quick yet effective relief. The curriculum also delves into the delicate techniques of acupressure face massage, a sought-after skill for enhancing wellness and beauty. Learning Outcomes Mastery of basic to advanced acupressure techniques, applicable in various settings. Proficiency in identifying and utilizing the 10 'Go To' potent acupressure points for maximum therapeutic effect. Ability to devise powerful point combinations to address common ailments, enhancing treatment efficacy. Skills in delivering specialized acupressure massages, including foot, back, chair, and face massages. Knowledge of integrating acupressure into holistic health practices, expanding therapeutic options. Why buy this Acupressure Massage course? Unlimited access to the course for a lifetime. Opportunity to earn a certificate accredited by the CPD Quality Standards and CIQ after completing this course. Structured lesson planning in line with industry standards. Immerse yourself in innovative and captivating course materials and activities. Assessments designed to evaluate advanced cognitive abilities and skill proficiency. Flexibility to complete the Course at your own pace, on your own schedule. Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience. Unlock career resources for CV improvement, interview readiness, and job success. Certification After studying the course materials of the Accupressure Massage there will be a written assignment test which you can take either during or at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £5.99. Original Hard Copy certificates need to be ordered at an additional cost of £9.60. Who is this Acupressure Massage course course for? Individuals seeking to learn a holistic approach to wellness and relaxation. Practitioners in the massage and spa industry aiming to expand their service offerings. Healthcare professionals interested in incorporating alternative therapies into their practice. Entrepreneurs looking to start a wellness business centered on acupressure massage. Enthusiasts keen on acquiring a new skill for personal health benefits or to assist family and friends. Prerequisites This Accupressure Massage does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Accupressure Massage was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Career path Acupressure Therapist: £25,000 - £35,000 Per Annum Wellness Spa Practitioner: £20,000 - £30,000 Per Annum Holistic Health Consultant: £30,000 - £45,000 Per Annum Massage Therapy Instructor: £25,000 - £40,000 Per Annum Spa Manager: £28,000 - £50,000 Per Annum Self-Employed Massage Therapist: £20,000 - £60,000 (varies based on client base and location) Per Annum Course Curriculum Getting Started Introduction 00:01:00 Download the summary of this section from the resources here 00:04:00 What is Traditional Chinese Medicine and why is it so incredible? 00:06:00 The meridians and the points in more detail 00:02:00 How to perform acupressure correctly. 00:04:00 Your 10 'Go To' Potent Acupressure Points Welcome To Section 2! 00:01:00 The Master Point Of The Head 00:02:00 The Energy Booster Point 00:02:00 The Cooling Point. 00:01:00 The Nausea Point 00:02:00 The Happiness Point 00:04:00 The Chill Out point 00:03:00 The Gynaecological Point 00:02:00 The Neck and Shoulder Tension Reliever Point 00:01:00 Look how much you can already do! 00:03:00 Powerful Point Combinations For Common Ailments Welcome To Section 3! 00:01:00 How to do acupressure for better emotional and physical health 00:05:00 Acne, Eczema and other skin disorders 00:08:00 Hay fever ( Allergic Rhinitis) 00:05:00 Arthritis 00:07:00 Asthma/Breathing problems 00:06:00 Poor Energy Levels 00:01:00 Using acupressure to help with emotional wellbeing 00:05:00 Colds and Flus 00:08:00 Constipation 00:01:00 Diarrhea 00:01:00 Insomnia 00:06:00 Well, don't I feel like such a fool! 00:02:00 Eyestrain/Red Eyes/Blurred Vision/Dry Eyes 00:03:00 Hot Flashes/Menopausal Symptoms 00:03:00 Hangovers 00:02:00 Stomach ache/Digestive issues 00:02:00 Menstrual Irregularities/Pain/PMS 00:03:00 Smoking Cessation 00:02:00 Earaches/Tinnitus/Water in the ear. 00:02:00 Memory/Concentration 00:03:00 Congratulations! 00:01:00 Resources Resources - Accupressure Massage 00:00:00 Assignment Assignment - Accupressure Massage 00:00:00

Architecting with Google Compute Engine
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Cloud Solutions Architects, DevOps Engineers. Individuals using Google Cloud Platform to create new solutions or to integrate existing systems, application environments, and infrastructure with a focus on Google Compute Engine. Overview Configure VPC networks and virtual machines Administer Identity and Access Management for resources Implement data storage services in GCP Manage and examine billing of GCP resources Monitor resources using Stackdriver services Connect your infrastructure to GCP Configure load balancers and autoscaling for VM instances Automate the deployment of GCP infrastructure services Leverage managed services in GCP This class introduces participants to the comprehensive and flexible infrastructure and platform services provided by Google Cloud Platform, with a focus on Compute Engine. Through a combination of presentations, demos, and hands-on labs, participants explore and deploy solution elements, including infrastructure components such as networks, systems, and application services. This course also covers deploying practical solutions including securely interconnecting networks, customer-supplied encryption keys, security and access management, quotas and billing, and resource monitoring. Introduction to Google Cloud Platform List the different ways of interacting with GCP Use the GCP Console and Cloud Shell Create Cloud Storage buckets Use the GCP Marketplace to deploy solutions Virtual Networks List the VPC objects in GCP Differentiate between the different types of VPC networks Implement VPC networks and firewall rules Design a maintenance server Virtual Machines Recall the CPU and memory options for virtual machines Describe the disk options for virtual machines Explain VM pricing and discounts Use Compute Engine to create and customize VM instances Cloud IAM Describe the Cloud IAM resource hierarchy Explain the different types of IAM roles Recall the different types of IAM members Implement access control for resources using Cloud IAM Storage and Database Services Differentiate between Cloud Storage, Cloud SQL, Cloud Spanner, Cloud Firestore and Cloud Bigtable Choose a data storage service based on your requirements Implement data storage services Resource Management Describe the cloud resource manager hierarchy Recognize how quotas protect GCP customers Use labels to organize resources Explain the behavior of budget alerts in GCP Examine billing data with BigQuery Resource Monitoring Describe the Stackdriver services for monitoring, logging, error reporting, tracing, and debugging Create charts, alerts, and uptime checks for resources with Stackdriver Monitoring Use Stackdriver Debugger to identify and fix errors Interconnecting Networks Recall the GCP interconnect and peering services available to connect your infrastructure to GCP Determine which GCP interconnect or peering service to use in specific circumstances Create and configure VPN gateways Recall when to use Shared VPC and when to use VPC Network Peering Load Balancing and Autoscaling Recall the various load balancing services Determine which GCP load balancer to use in specific circumstances Describe autoscaling behavior Configure load balancers and autoscaling Infrastructure Automation Automate the deployment of GCP services using Deployment Manager or Terraform Outline the GCP Marketplace Managed Services Describe the managed services for data processing in GCP Additional course details: Nexus Humans Architecting with Google Compute Engine training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Architecting with Google Compute Engine course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Advanced Training Course in Child Counselling at QLS Level 6
By Lead Academy
Quality Guarantee: Promising training excellence, satisfaction gurantee Accredited by CPD UK & Quality License Scheme Tutor Support Unlimited support via email, till you complete the course Recognised Certification: Accepted by thousands of professional bodies Start Anytime With 1 year access to the course materials Online Learning Learn from anywhere, whenever you want This course at a glance Eligible to apply for the insurance Accredited by International Practitioners of Holistic Medicine (IPHM) Accredited by CPD UK Endorsed by Quality Licence Scheme Understand the importance of bonding Recognise the importance of social and emotional development Learn about the innate reflexes of newborn babies Identify the benefits of testing at milestones Discover the importance of unconditional love Understand various forms of communication - active and passive voice and pre-linguistic form of communication Understand the importance of opportunities in the development of the skills Recognise the importance of body language and opportunities in the development of the skills Understand the importance of cognitive development and the main psychological theories Identify the appropriate opportunities for cognitive development Why Advanced Child Counselling Course right for you? Whether you are self-taught and you want to fill in the gaps for better efficiency and productivity, this Advanced Training in Child Counselling at QLS level 6 course will set you up with a solid foundation to become a confident child counsellor and develop more advanced skills. This comprehensive course is the perfect way to kickstart your career in the field of child psychology. This course will give you a competitive advantage in your career, making you stand out from all other applicants and employees. As one of the leading course providers and most renowned e-learning specialists online, we're dedicated to giving you the best educational experience possible. This course is crafted by industry expert, to enable you to learn quickly and efficiently, and at your own pace and convenience. Advanced Child Counselling Course Details Accredited by International Practitioners of Holistic Medicine (IPHM) is a leading accredited organisation that certifies and regulates alternative therapists, healers, and training providers around the world. After completing the IPHM accredited course you will be eligible to apply for the insurance. CPD certificates are accepted by thousands of professional bodies and government regulators here in the UK and around the world. Many organisations look for employees with CPD requirements, which means, that by doing this course, you would be a potential candidate in your respective field. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. Course Curriculum Introduction About the Course & the Instructor Definition of Counselling The Counselling Relationship Psychology of Growth and Development The Development Cycle Parent, Child, Teacher Relationships The Complexities of Growth Introduction - Psychological Development Therapeutic Language Conflict and Stress Behavioural Therapies Working with Children The Use of Language Memory Psychological Issues Grief and Bereavement Exploring Grief and Letting Go Dysfunctional Families What is Co-Dependency Child Bullying and Child Abuse Psychological Study of Education Transformation Using Newly Found Skills Recovery - The Therapeutic Process Moving on - Emotional Intimacy Working as a Counsellor Setting Up a Practice Child Psychology What is 'Child Psychology'. The Role of Child Psychologist Where do Child Psychologists Work Why Do We Need to Learn Theories Developmental Theories: How Environment Impacts Us Environmental & Socio-Cultural Factors in Development 'Attachment' Factor in Newborns Socio-Cultural Factors in Child's Development Family & Schooling Factors in Development The Role of Parenting in Child's Development Relationship Breakdown in the Family Schooling Environment Counselling Young Children Cognitive and Emotional Development Language & Cognitive Development Emotions & Feelings Socialising With Others Thank You and Good Bye! Child Behaviour and Development Babies from Birth to One Year The Importance of Bonding The Social and Emotional Development: From Birth to 1 Yr The Innate Reflexes of Newborn Babies The Benefits of Testing at 'Milestones' Stages and Sequences of Social and Emotional Development The Importance of Social and Emotional Development The Ages and Stages that Children go Through The Main theories in Developmental Psychology The Importance of Positive Role Models The Barriers to Achieving the 'Milestones' The Importance of Unconditional Love Language and Linguistic Skills Development Forms of Communication What is 'Pre-linguistic' form of Ccommunication The Active and the Passive Communication The Importance of Opportunities in Development of the Skills The Importance of Body Language Cognitive Development The Importance of Cognitive Development The Main Psychological Theories in Cognitive Development The Appropriate Opportunities for Cognitive Development The Unconscious Mind: Id, Ego and Superego. Psychoanalytical Theory Thank You and Good Bye! Who should take this course? This comprehensive course is suitable for anyone looking to improve their job prospects or aspiring to accelerate their career in this sector and want to gain in-depth knowledge of child psychology. Entry Requirements There are no academic entry requirements for this course, and it is open to students of all academic backgrounds. As long as you are aged seventeen or over and have a basic grasp of English, numeracy and ICT, you will be eligible to enrol. Assessment Method On successful completion of the Advanced Training in Child Counselling at QLS level 6 course, you will be required to sit an online multiple-choice assessment. The assessment will be evaluated automatically and the results will be given to you immediately. For a comprehensive learning experience, you can join our Counselling Skills - 10 Courses Complete Bundle and gain expertise in various counselling techniques and theories, including cognitive-behavioral therapy, person-centered therapy, and solution-focused brief therapy. With these courses, you will be equipped to provide effective counselling services to individuals from diverse backgrounds and with different mental health needs. Certification Endorsed Certificate from Quality Licence Scheme After successfully passing the MCQ exam you will be eligible to order the Endorsed Certificate by Quality Licence Scheme. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. It will give you a competitive advantage in your career, making you stand out from all other applicants and employees. There is a Quality Licence Scheme endorsement fee to obtain an endorsed certificate which is £65. Certificate of Achievement from Lead Academy After successfully passing the MCQ exam you will be eligible to order your certificate of achievement as proof of your new skill. The certificate of achievement is an official credential that confirms that you successfully finished a course with Lead Academy. Certificate can be obtained in PDF version at a cost of £12, and there is an additional fee to obtain a printed copy certificate which is £35. FAQs What Is Child Counselling? Child counselling is a sort of therapy designed for young children, teenagers, and adolescents suffering from one or more mental diseases. It also helps young people who have been traumatised or who live in a dysfunctional or stressful home setting. How To Be a Counsellor ? Here are some essential steps to consider: Obtain a relevant education Pursue a master's degree Participate in internship programs Obtain required certifications or licence Consider specialisation Search for opportunities to start your career Is Counselling A Good Career? A rewarding career for individuals who have a passion for helping others. It offers various career opportunities such as child, psychological, family counselling and many more. How long does it take to become a juvenile counsellor? The clinical training is a full-time doctorate program that spans four years. It entails teaching, supervision, and training in psychoanalysis, as well as a paid training post (at NHS Band 6) in a mental health service. But if you wish to become a child psychologist besides a counsellor as well then read our How to become a child psychologist in UK blog.

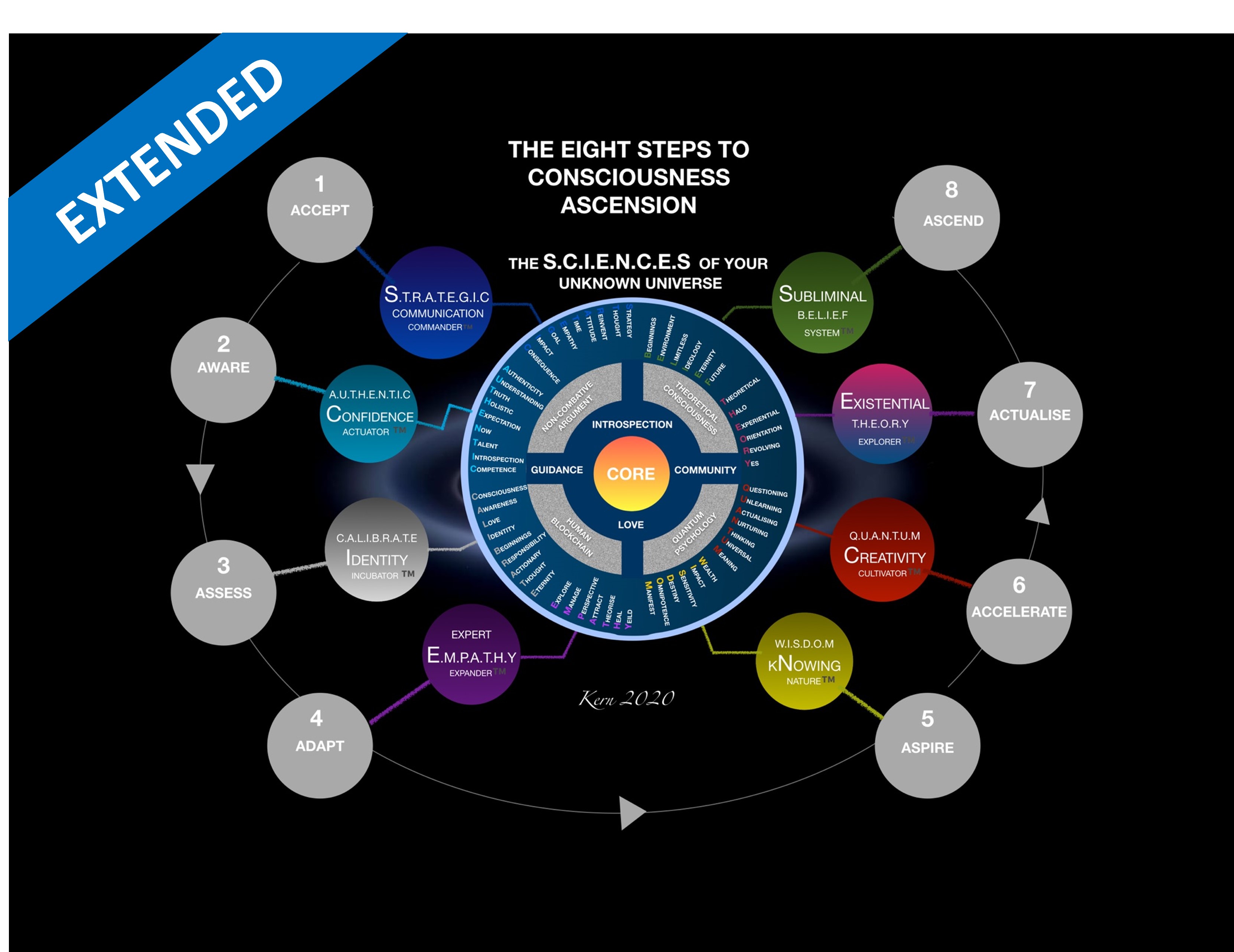
S.C.I.E.N.C.E.S Of Your Unknown Universe - Extended
By Council For Human Development Swiss Association
The S.C.I.E.N.C.E.S Extended Program is a 6-month powerful personal development training tool incl. 12 individual coaching sessions, based around Neuroplastic Mental Acceleration (NMA): encompassing the eight steps to ascension, spread over 60 x 30 minute training sessions: Accept, Aware, Assess, Adapt, Aspire, Accelerate, Actualise, Ascend. The program is designed to provide mental well-being & acceleration by promoting fluid intelligence (the brain’s ability to learn new skills) though activating neuroplasticity - synaptogenisis & neurogenisis.
[vc_row][vc_column][vc_column_text] Description: Women have more rights than ever these days, and females around the world are helping to change the way we live for the better. This women empowerment course is not only a celebration of women's equal rights and the power of women but is also an exploration of women and leadership in the workplace and beyond. The key to achieving great success is owning your sense of self and having the confidence to pursue your dreams. This Women's Self Development & Empowerment Course is designed to help women in business develop their voice and the skills they need to inspire and empower others. Through confidence-building exercises and professional mentoring techniques, you will learn how to train your mind for success. You will also explore the topic of women and leadership and how to make your mark in competitive industries like journalism. If you're an entrepreneur, motivational speaker or are interested in a career in life coaching, enrol in this life-changing masterclass today and help celebrate International Women's Day every day. Who is the course for? Women professionals, Trainers, and Individuals who want to be expert in positive self-development. Any woman who wants to know to manage their life and self-development. Entry Requirement: This course is available to all learners, of all academic backgrounds. Learners should be aged 16 or over to undertake the qualification. Good understanding of English language, numeracy and ICT are required to attend this course. Assessment: At the end of the course, you will be required to sit an online multiple-choice test. Your test will be assessed automatically and immediately so that you will instantly know whether you have been successful. Before sitting for your final exam, you will have the opportunity to test your proficiency with a mock exam. Certification: After you have successfully passed the test, you will be able to obtain an Accredited Certificate of Achievement. You can however also obtain a Course Completion Certificate following the course completion without sitting for the test. Certificates can be obtained either in hard copy at the cost of £39 or in PDF format at the cost of £24. PDF certificate's turnaround time is 24 hours, and for the hardcopy certificate, it is 3-9 working days. Why choose us? Affordable, engaging & high-quality e-learning study materials; Tutorial videos/materials from the industry leading experts; Study in a user-friendly, advanced online learning platform; Efficient exam systems for the assessment and instant result; The UK & internationally recognized accredited qualification; Access to course content on mobile, tablet or desktop from anywhere anytime; The benefit of career advancement opportunities; 24/7 student support via email. Career Path: Women's Self Development & Empowerment course will be useful and would be beneficial for every kind of occupations and careers for women like: Businessmen Entrepreneur Life Coach Manager Mentor Supervisor Team Leader Top Executive. [/vc_column_text][/vc_column][/vc_row] Personal Development of Women Did you know? motivational phrase sign on old wood with blurred background 00:15:00 Development of the Self, Voice and Mind: The Female Secrets 00:15:00 Development of the Self, Voice and Mind: behind the Scene of Women's Issues 01:00:00 Development of Self, Voice and Mind: The knowing women 00:15:00 Development of Self, Voice and Mind: A Woman's Systematic Approach 01:00:00 Development of Self, Voice and Mind: The Basics of Everything 00:30:00 The Development of Self, Voice and Mind: Adopting a Winning Attitude 00:30:00 Development of the Self, Voice and Mind in Visionary Action 00:30:00 How to Find Your Voice: The Development of the Self, Voice and Mind 00:30:00 Keep That Memory in Mind in Development of Self and Voice 00:30:00 Character: a Central Element in the Development of Self, Voice and Mind 01:00:00 The Development of Self, Voice and Mind: A Holistic Approach 00:30:00 Self-development is the Key to Sure-Shot Success in Development of Self, Voice and Mind 00:30:00 Understand Self to Transform Mind in Development of Voice and Mind 02:20:00 New Medical Breakthroughs in Development of Self, Voice and Mind 01:00:00 Finding your voice in Development of Self and Mind 00:30:00 Women and Leadership Module One - Getting Started 01:00:00 Module Two - Women and the Workforce 01:00:00 Module Three - The Leadership Gap 01:00:00 Module Four - Barriers to Women's Leadership 01:00:00 Module Five - Traits of Women's Management 01:00:00 Module Six - Benefits of Women's Leadership 01:00:00 Module Seven - Nurture Women's Leadership 01:00:00 Module Eight - Actively Recruit Women 01:00:00 Module Nine - Encourage Networking Opportunities 01:00:00 Module Ten - Pair Women with Mentors 01:00:00 Module Eleven - Create Educational Opportunities 01:00:00 Module Twelve - Wrapping Up 01:00:00 Women Leadership Diploma- Activities 00:00:00 Women and Journalism The Secret Significance of Journalism 01:00:00 Imperfections of the Existing WomanâJournalist 01:00:00 The Roads towards Journalism 01:00:00 The Aspirant 01:00:00 Style 01:00:00 The Outside Contributor 01:00:00 The Search for Copy 01:00:00 The Art of Corresponding with an Editor 00:30:00 Notes on the Leading Types of Papers 00:30:00 Woman's Sphere in Journalism 01:00:00 Conclusion 00:15:00 Mock Exam Mock Exam- Women's Self Development & Empowerment 00:30:00 Final Exam Final Exam- Women's Self Development & Empowerment 00:30:00 Certificate and Transcript Order Your Certificates and Transcripts 00:00:00

Critical Thinking & Decision Making with Stress Management - QLS Endorsed
By Imperial Academy
2 QLS Endorsed Courses | CPD Certified | Free PDF & Hard Copy QLS Certificates | 180 CPD Points | Lifetime Access

Search By Location
- Memory Courses in London
- Memory Courses in Birmingham
- Memory Courses in Glasgow
- Memory Courses in Liverpool
- Memory Courses in Bristol
- Memory Courses in Manchester
- Memory Courses in Sheffield
- Memory Courses in Leeds
- Memory Courses in Edinburgh
- Memory Courses in Leicester
- Memory Courses in Coventry
- Memory Courses in Bradford
- Memory Courses in Cardiff
- Memory Courses in Belfast
- Memory Courses in Nottingham