- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
43984 Learning courses in Nottingham delivered Online
Level 7 Diploma In Accounting & Finance - Pathway To MSc Accounting & Finance Degree
4.9(261)By Metropolitan School of Business & Management UK
Level 7 Diploma In Accounting & Finance - Pathway To MSc Accounting & Finance Degree Level 7 Diploma in Accounting & Finance (QCF) – 6 - 8 Months Credits: 120 Credits This qualification is designed for learners who wish to pursue a career in the financial services industry, professional accountancy, banking, and finance or management. The qualification equips learners with the essential skills and knowledge needed to pursue high-level careers in all types of organizations in the public and private sector and within industry and commerce, both in the UK and abroad. The Level 7 Diploma in Accounting and Finance qualification also provides learners with the opportunity to work toward a relevant master’s programme with advanced standing. This programme is a Pathway programme to MSc Accounting & Finance Degree Course Details Assessment: Assignments Objectives: contemporary and specialized approaches to accountancy and finance key practical, theoretical and empirical issues, and academic research the complexity of the ever-changing legal framework in which the financial sector operates the latest developments in accountancy and reporting required by local, national and European governments. Accreditation All MSBM courses are accredited by the relevant partners and awarding bodies. Please refer to MSBM accreditation in about us for more details. University Progression University Top-up On completion of this course, students have the opportunity to complete a Master degree programme from a range of UK universities. The top-up programme can be studied online or on campus. The top-up comprises the final 60 credits which consist of either a dissertation or a dissertation and one module. (The course tuition fee listed above does NOT include the top-up fees) University Progression Click here to see University routes and fee information for progression. Entry Requirements For entry onto the Level 7 Diploma in Human Resource Management leading to the MA Human Resource Management qualification, learners must possess: An honours degree in related subject or UK level 6 diploma or equivalent overseas qualification i.e. Bachelors Degree or Higher National Diploma OR Mature learners (over 25) with at least 5 years of management experience if they do not possess the above qualification (this is reviewed on a case by case basis) Workshops Workshops are conducted by live webinars for all students. Visa Requirements There is no Visa requirement for this programme.

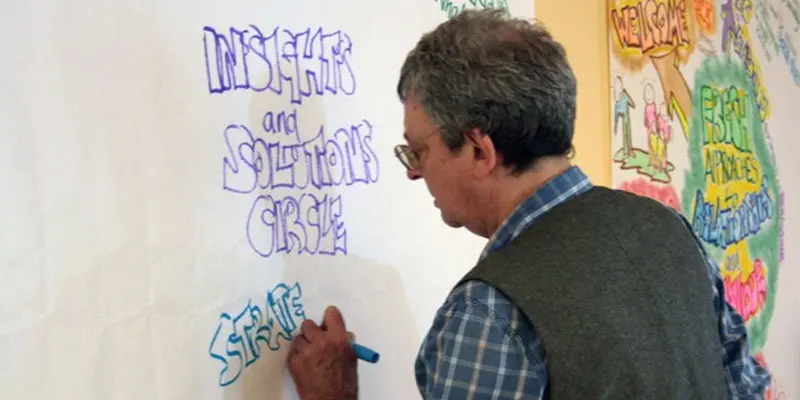
INSIGHTS AND SOLUTIONS CIRCLE
By Inclusive Solutions
This can be introduced in one day but is better offered over a series of twilight or half day workshops with individualised coaching. We will provide background context for this approach and will directly model the process with real live issues facing participants. So bring your most challenging concerns to this training. Course Category Behaviour and Relationships Visioning and Problem Solving Team Building and Leadership Description ‘Insights and Solutions Circle’ a new expanded version of Solution Circle that uses some of the best of the Circle of Adults process. Its a 50 minute process and works really well with families and professionals! Contact us today for a live demo or training… Steps Problem presented Questions asked Theories Shared Strategies listed Dialogue regarding selected strategies Next steps Testimonials Excellent! It was great how we all cam up with ideas and theories including us parents I wish all meeting about my child’s behaviour were like this The whole world is going to be interested in this… The empowerment is great The buzz after the meeting says it all. Learning Objectives Deeper understanding of what is actually happening underneath the presenting behaviour Increased confidence in managing and building relationships with challenging pupils in mainstream schools Learn process for locating richer and wider range of practical strategies to impact on behaviour problems Deeper understanding of yourself and the psychodynamic processes happening between pupils, staff and pupils and families Opportunity to reflect on professional practice Mutual support established with other front line practitioners Who Is It For ? Team Around the Child agencies Parents and Professional working together Families Multi Agency Teams Social workers CAMHS teams Year Managers Primary and secondary staff teams Early Years and School based Practitioners Heads and Deputies SENCOs Advanced Skills Teachers Primary and secondary teachers Local Authority Support Services Course Content This can be introduced in one day but is better offered over a series of twilight or half day workshops with individualised coaching. We will provide background context for this approach and will directly model the process with real live issues facing participants. So bring your most challenging concerns to this training. The course answers the questions: Can we find an alternative to permanent exclusion or special unit or school placement? Cannot understand why a child is behaving as they do? Struggling with a child for whom praise is ineffective? Feeling isolated in your responses to a child’s needs? Worried about where your instinctive reactions are leading you? Cannot seem to get any consensus view of a young person’s behaviour/needs amongst all the family and professionals involved – is everyone pulling in different directions? We will cover: Setting the tone Background and detailed teaching of process Inclusion values underpinning this work Graphic and process facilitation skills Processes modelled and opportunities to try process out with coaching Practical setting up of insights and solutions circles Lessons learned If you liked this you may like: CIRCLES OF ADULTS…
SC-100T00 Microsoft Cybersecurity Architect
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for experienced cloud security engineers who have taken a previous certification in the security, compliance and identity portfolio. Specifically, students should have advanced experience and knowledge in a wide range of security engineering areas, including identity and access, platform protection, security operations, securing data, and securing applications. They should also have experience with hybrid and cloud implementations. Beginning students should instead take the course SC-900: Microsoft Security, Compliance, and Identity Fundamentals. This is an advanced, expert-level course. Although not required to attend, students are strongly encouraged to have taken and passed another associate level certification in the security, compliance and identity portfolio (such as AZ-500, SC-200 or SC-300) before attending this class. This course prepares students with the expertise to design and evaluate cybersecurity strategies in the following areas: Zero Trust, Governance Risk Compliance (GRC), security operations (SecOps), and data and applications. Students will also learn how to design and architect solutions using zero trust principles and specify security requirements for cloud infrastructure in different service models (SaaS, PaaS, IaaS). Prerequisites Highly recommended to have attended and passed one of the associate level certifications in the security, compliance and identity portfolio (such as AZ-500T00 Microsoft Azure Security Technologies, SC-200T00: Microsoft Security Operations Analyst, or SC-300T00: Microsoft Identity and Access Administrator.) Advanced experience and knowledge in identity and access, platform protection, security operations, securing data and securing applications. Experience with hybrid and cloud implementations. 1 - Introduction to Zero Trust and best practice frameworks Zero Trust initiatives Zero Trust technology pillars part 1 Zero Trust technology pillars part 2 2 - Design solutions that align with the Cloud Adoption Framework (CAF) and Well-Architected Framework (WAF) Define a security strategy Cloud Adoption Framework secure methodology Design security with Azure Landing Zones The Well-Architected Framework security pillar 3 - Design solutions that align with the Microsoft Cybersecurity Reference Architecture (MCRA) and Microsoft cloud security benchmark (MCSB) Design solutions with best practices for capabilities and controls Design solutions with best practices for attack protection 4 - Design a resiliency strategy for common cyberthreats like ransomware Common cyberthreats and attack patterns Support business resiliency Ransomware protection Configurations for secure backup and restore Security updates 5 - Case study: Design solutions that align with security best practices and priorities Case study description Case study answers Conceptual walkthrough Technical walkthrough 6 - Design solutions for regulatory compliance Translate compliance requirements into a security solution Address compliance requirements with Microsoft Purview Address privacy requirements with Microsoft Priva Address security and compliance requirements with Azure policy Evaluate infrastructure compliance with Defender for Cloud 7 - Design solutions for identity and access management Design cloud, hybrid and multicloud access strategies (including Azure AD) Design a solution for external identities Design modern authentication and authorization strategies Align conditional access and Zero Trust Specify requirements to secure Active Directory Domain Services (AD DS) Design a solution to manage secrets, keys, and certificates 8 - Design solutions for securing privileged access The enterprise access model Design identity governance solutions Design a solution to secure tenant administration Design a solution for cloud infrastructure entitlement management (CIEM) Design a solution for privileged access workstations and bastion services 9 - Design solutions for security operations Design security operations capabilities in hybrid and multicloud environments Design centralized logging and auditing Design security information and event management (SIEM) solutions Design solutions for detection and response Design a solution for security orchestration, automation, and response (SOAR) Design security workflows Design threat detection coverage 10 - Case study: Design security operations, identity and compliance capabilities Case study description Case study answers Conceptual walkthrough Technical walkthrough 11 - Design solutions for securing Microsoft 365 Evaluate security posture for collaboration and productivity workloads Design a Microsoft 365 Defender solution Design configurations and operational practices for Microsoft 365 12 - Design solutions for securing applications Design and implement standards to secure application development Evaluate security posture of existing application portfolios Evaluate application threats with threat modeling Design security lifecycle strategy for applications Secure access for workload identities Design a solution for API management and security Design a solution for secure access to applications 13 - Design solutions for securing an organization's data Design a solution for data discovery and classification using Microsoft Purview Design a solution for data protection Design data security for Azure workloads Design security for Azure Storage Design a security solution with Microsoft Defender for SQL and Microsoft Defender for Storage 14 - Case study: Design security solutions for applications and data Case study description Case study answers Conceptual walkthrough Technical walkthrough 15 - Specify requirements for securing SaaS, PaaS, and IaaS services Specify security baselines for SaaS, PaaS, and IaaS services Specify security requirements for web workloads Specify security requirements for containers and container orchestration 16 - Design solutions for security posture management in hybrid and multicloud environments Evaluate security posture by using Microsoft Cloud Security Benchmark Design integrated posture management and workload protection Evaluate security posture by using Microsoft Defender for Cloud Posture evaluation with Microsoft Defender for Cloud secure score Design cloud workload protection with Microsoft Defender for Cloud Integrate hybrid and multicloud environments with Azure Arc Design a solution for external attack surface management 17 - Design solutions for securing server and client endpoints Specify server security requirements Specify requirements for mobile devices and clients Specify internet of things (IoT) and embedded device security requirements Secure operational technology (OT) and industrial control systems (ICS) with Microsoft Defender for IoT Specify security baselines for server and client endpoints Design a solution for secure remote access 18 - Design solutions for network security Design solutions for network segmentation Design solutions for traffic filtering with network security groups Design solutions for network posture management Design solutions for network monitoring 19 - Case study: Design security solutions for infrastructure Case study description Case study answers Conceptual walkthrough Technical walkthrough Additional course details: Nexus Humans SC-100T00 Microsoft Cybersecurity Architect training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the SC-100T00 Microsoft Cybersecurity Architect course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

I Have an Opportunity: Believe in Delegation All Over Again
By IIL Europe Ltd
I Have an Opportunity: Believe in Delegation All Over Again Through a new definition of delegation vs. dumping, this video will show you how to truly motivate your employees by making them believe in the word 'opportunity' again. This and other IIL Learning in Minutes presentations qualify for PDUs. Some titles, such as Agile-related topics may qualify for other continuing education credits such as SEUs, or CEUs. Each professional development activity yields one PDU for one hour spent engaged in the activity. Some limitations apply and can be found in the Ways to Earn PDUs section that discusses PDU activities and associated policies. Fractions of PDUs may also be reported. The smallest increment of a PDU that can be reported is 0.25. This means that if you spent 15 minutes participating in a qualifying PDU activity, you may report 0.25 PDU. If you spend 30 minutes in a qualifying PDU activity, you may report 0.50 PDU.

PfMP Exam Prep: In-House Training
By IIL Europe Ltd
PfMP® Exam Prep: In-House Training This is an intensive PfMP® Exam preparation course. This learning experience guides you through the multi-faceted discipline of portfolio management by focusing on the related technical, leadership, and business skills required to navigate it in the real world. First and foremost, this is an intensive PfMP® exam preparation course. Over the course, we go beyond exam prep to provide selected practice in applying key portfolio management skills, tools, and techniques. This learning experience guides you through the multi-faceted discipline of portfolio management by focusing on the related technical, leadership, and business skills required to navigate it in the real world. The journey zooms in and out between governance context and specific operational activities. The ultimate goal is practical application, with the bonus of certification along the way. What You Will Learn By the end of this program, you will be able to: Align and manage the portfolio, strategically, to satisfy organizational objectives and priorities, through benefit realization Articulate and emulate the role of a portfolio manager Apply the principles and skills of a portfolio manager to your real-world environment Study and prepare for the PfMP® Examination Apply for the certification, per the PMI PfMP Handbook and pass the initial panel review on your application Getting Started Course Overview Details of the PfMP® Certification process Foundation Concepts Projects, program, and portfolios A portfolio management process Strategy and value The role of the portfolio manager The role of key stakeholders Life cycle management The Portfolio Life Cycle Overview of Life Cycle Portfolio Management Information System (PMIS) Governance within the Portfolio Life Cycle Strategic Management Strategy concepts Supporting documentation and the strategic plan Planning and optimization Organizational risk appetite Managing strategic change Governance Management Overview and Guiding Principles The Concept of Governance Effective Design Factors Governance Roles Capacity and Capability Management Overview and Guiding Principles Capacity Management and Planning Supply and Demand (Management and Optimization) Organization Capabilities (Assessment and Development) Performance Management (Reporting, Analytics, and Balance) Stakeholder Engagement The Importance of Stakeholders Overview and Guiding Principles Definition and Identification Analysis and Planning Communications Approaches and Management Value Management Overview (Guiding Principles, Definition, and Components) Negotiating Expected Value Maximizing Value Assuring Value Realizing Value Measuring and Reporting Value A Look at Tools Risk Management Overview and Guiding Principles Portfolio Risk Planning Portfolio Risk Identification Portfolio Risk Assessment Portfolio Risk Response Examination Content Outline (ECO) Overview Structure Strategic Tasks Mapping Governance Tasks Mapping Performance Tasks Mapping Risk Tasks Mapping Communication Tasks Mapping List of Knowledge and Skills Exam Prep and Practice Overview Documenting experience Submitting the application Preparing to sit for the exam

Capacity Planning, Forecasting & Budgets
By Mpi Learning - Professional Learning And Development Provider
Understanding how to plan for capacity, be able to forecast and manage budgets is a critical skill in today's leadership and management environment. This programme will not only support your understanding but will also help you to practically put the learning into practice.

Finance for Non-Finance Professionals in Oil & Gas Petroleum Fiscal Regimes & Applied Finance for Non-Finance Oil & Gas Professionals
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course This separately bookable 3 full-day course is not designed to skill Oil & Gas engineers to be accountants, but to give the participants the confidence and ability to communicate with accountants and finance managers and to improve their own financial decision making. For technical professionals, a high level of single subject matter expertise is no longer sufficient for superior management performance. Oil & Gas technical professionals who wish to succeed in the resources industry are required to develop skills beyond their core functional knowledge. An understanding of financial information and management, and an awareness of the economic theory that drives value creation, are an integral part of the managers required suite of skills. This course can also be offered through Virtual Instructor Led Training (VILT) format. Training Objectives Workshop A: Finance for Non-Finance for Oil & Gas Professionals Attend this industry specific course and benefit from the following: Demystify financial jargon and fully interpret financial statements Understand Balance Sheets and Profit & Loss statements of Oil & Gas companies Discover the crucial distinction between cash flow and profit Understand how to make correct investment decisions using Net present Value and Internal Rate of Return Interpret oil and gas company financial reports using ratio analysis Learn the difference between cash costs and full costing of energy products Learn how to manage working capital for increased shareholder value Workshop B: Petroleum Fiscal Regimes and Applied Finance for Oil & Gas Industry Professionals Attend this advanced Training course to enhance your financial acumen from the following: Build and compare cash flow based models of both production sharing contract projects and royalty regime projects Gain an awareness of the different valuation methods for producing properties and undeveloped acreage Learn the industry specific accounting issues that apply when interpreting oil and gas company financial statements Understand how the physical characteristics of energy assets (e.g. reserves, reservoir quality) are translated into project valuations Learn how the investment analysts value oil and gas stocks and make buy/sell recommendations Target Audience This course is specifically designed for those with a non-finance background training from the Oil & Gas sector and requires only basic mathematical ability as a pre-requisite. It is presented in a manner that reduces the jargon to basic principles and applies them to numerous real-life examples. This course has been researched and developed for Managers, Superintendents, Supervisors, Engineers, Planners, Lawyers, Marketers, Team Leaders and Project Coordinators in the technical and non-technical departments in the Oil and Gas industry. Course Level Basic or Foundation Trainer Your expert course leader has presented over 300 courses and seminars in financial management. He began his career as a graduate in the Corporate Treasury of WMC Ltd having completed a degree in Applied Mathematics and Geology at Monash University. After five years with WMC, he pursued an MBA in finance and accounting at Cornell University in New York. He later gained a PhD in energy policy from the University of Melbourne. He worked for WMC Ltd in Perth as a Senior Financial Analyst in the Minerals Division and subsequently as an Energy Analyst in the Petroleum Division. In April 1997, he established an independent consultancy business providing advice to companies such as Woodside, Shell and Japan Australia LNG (MIMI). He spent many years as a consultant and commercial manager in the North West Shelf Gas project in Western Australia. Since 2006, he has been an Adjunct Fellow at the Macquarie University Applied Finance Centre where he teaches courses in valuation, financial statement modelling, and resources industry investment analysis. His background in geology and mathematics allows him to empathise with those who seek an understanding of finance but are approaching the learning experience with a technical mind. He receives consistently high ratings for his breadth of knowledge of the subject matter. He presents in a lively interactive style using real life examples and cases. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

The Facilitation Skills course offers quality training for aspiring facilitators who want to expand their knowledge of the framework required for effective facilitation. It covers essential topics such as dealing with difficult people, building consensus, and addressing group dysfunction. Throughout the course, learners will develop crucial skills in active listening, conflict solving and communication, and will be introduced to a wide range of intervention techniques to fast track their career. There are no entry requirements for this training program. Learning Objectives: Develop the key skills and practical knowledge to create an inclusive and harmonious environment for all Understand the basic principles of conflict management and conflict resolution Sharpen your skills in communication, leadership and people management Discover a wide range of intervention techniques and consensus-building strategies Who is this Course for? Facilitation Skills is perfect for anyone trying to learn potential professional skills. As there is no experience and qualification required for this course, it is available for all students from any academic background. Requirements Our Facilitation Skills is fully compatible with any kind of device. Whether you are using Windows computer, Mac, smartphones or tablets, you will get the same experience while learning. Besides that, you will be able to access the course with any kind of internet connection from anywhere at any time without any kind of limitation. CPD Certificate from Course Gate At the successful completion of the course, you can obtain your CPD certificate from us. You can order the PDF certificate for £9 and the hard copy for £15. Also, you can order both PDF and hardcopy certificates for £22. Career path This course opens a new door for you to enter the relevant job market and also gives you the opportunity to acquire extensive knowledge along with required skills to become successful. You will be able to add our qualification to your CV/resume which will help you to stand out in the competitive job industry. Course Curriculum Module One: Getting Started Facilitation Skills 00:01:00 Module Two: Understanding Facilitation Understanding Facilitation 00:09:00 Understanding Facilitation Case Study 00:01:00 Module Three: Process vs. Content Process vs. Content 00:06:00 Process vs. Content Case Study 00:01:00 Module Four: Laying the Groundwork Laying the Groundwork 00:06:00 Laying the Groundwork Case Study 00:01:00 Module Five: Tuckman and Jensen"s Model of Team Development Tuckman and Jensen's Model of Team Development 00:07:00 Tuckman and Jensen's Model of Team Development Case Study 00:01:00 Module Six: Building Consensus Building Consensus 00:09:00 Building Consensus Case Study 00:01:00 Module Seven: Reaching a Decision Point Reaching a Decision Point 00:04:00 Reaching a Decision Point Case Study 00:01:00 Module Eight: Dealing with Difficult People Dealing with Difficult People 00:03:00 Dealing with Difficult People Case Study 00:01:00 Module Nine: Addressing Group Dysfunction Addressing the Group Dysfunction Case Study 00:01:00 Addressing the Group Dysfunction Case Study 00:01:00 Module Ten: About Intervention About Intervention 00:06:00 About Intervention Case Study 00:01:00 Module Eleven: Intervention Techniques Intervention Techniques 00:03:00 Intervention Techniques Case Study 00:01:00 Closing 00:01:00 Certificate and Transcript Order Your Certificates or Transcripts 00:00:00

Register on the Leadership and Management today and build the experience, skills and knowledge you need to enhance your professional development and work towards your dream job. Study this course through online learning and take the first steps towards a long-term career. The course consists of a number of easy to digest, in-depth modules, designed to provide you with a detailed, expert level of knowledge. Learn through a mixture of instructional video lessons and online study materials. Receive online tutor support as you study the course, to ensure you are supported every step of the way. Get a certificate as proof of your course completion. The Leadership and Management is incredibly great value and allows you to study at your own pace. Access the course modules from any internet-enabled device, including computers, tablets, and smartphones. The course is designed to increase your employability and equip you with everything you need to be a success. Enrol on the now and start learning instantly! What You Get With The Leadership and Management Receive a digital certificate upon successful completion of the course Get taught by experienced, professional instructors Study at a time and pace that suits your learning style Get instant feedback on assessments 24/7 help and advice via email or live chat Get full tutor support on weekdays (Monday to Friday) Course Design The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of Video lessons Online study materials Certification After the successful completion of the final assessment, you will receive a CPD-accredited certificate of achievement. The PDF certificate is for £9.99, and it will be sent to you immediately after through e-mail. You can get the hard copy for £15.99, which will reach your doorsteps by post. Who Is This Course For: The course is ideal for those who already work in this sector or are aspiring professionals. This course is designed to enhance your expertise and boost your CV. Learn key skills and gain a professional qualification to prove your newly-acquired knowledge. Requirements: The online training is open to all students and has no formal entry requirements. To study the Leadership and Management, all you need is a passion for learning, A good understanding of English, numeracy, and IT skills. You must also be over the age of 16.

