- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1313 Integration courses in Manchester delivered Online
Ansible for the Absolute Beginner - Hands-On - DevOps
By Packt
Unlock the power of Ansible in DevOps with this in-depth video course. From beginner to expert, this course covers everything you need to know about Ansible, accompanied by hands-on exercises that you can practice right in your browser. No prior experience needed.

Unlock the essentials of auditing with our course, "Business Auditor: Basic Auditing Techniques." Gain expertise in types of audits, planning, internal control, and more. Delve into UK audit standards, technology integration, and explore lucrative career prospects. Elevate your skills and become a proficient auditor today!

Symantec Data Loss Prevention 14.0 - Administration
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for anyone responsible for conf iguring, maintaining, and troubleshooting Symantec Data Loss Prevention. Additionally, this course is intended for technical users responsible for creating and maintaining Symantec Data Loss Prevention policies and the incident response structure. Overview At the completion of the course, you will be able to: Enforce server, detection servers, and DLP Agents as well as reporting, workflow, incident response management, policy management and detection, response management, user and role administration, directory integration, and filtering. This course is designed to provide you with the fundamental know ledge to configure and administer the Symantec Data Loss Prevention Enforce platform. Introduction to Symantec Data Loss Prevention Symantec Data Loss Prevention overview Symantec Data Loss Prevention architecture Navigation and Reporting Navigating the user interface Reporting and analysis Report navigation, preferences, and features Report filters Report commands Incident snapshot Incident Data Access Hands-on labs: Become familiar with navigation and tools in the user interface. Create, filter, summarize, customize, and distribute reports. Create users, roles, and attributes. Incident Remediation and Workflow Incident remediation and w orkf low Managing users and attributes Custom attribute lookup User Risk Summary Hands-on labs: Remediate incidents and configure a user?s reporting preferences Policy Management Policy overview Creating policy groups Using policy templates Building policies Policy development best practices Hands-on labs: Use policy templates and policy builder to configure and apply new policies Response Rule Management Response rule overview Configuring Automated Response rules Configuring Smart Response rules Response rule best practices Hands-On Labs: Create and use Automated and Smart Response rules Described Content Matching DCM detection methods Hands-on labs: Create policies that include DCM and then use those policies to capture incidents Exact Data Matching and Directory Group Matching Exact data matching (EDM) Advanced EDM Directory group matching (DGM) Hands-on labs: Create policies that include EDM and DGM, and then use those policies to capture incident Indexed Document Matching Indexed document matching (IDM) Hands-on labs: Create policies that include IDM rules and then use those policies to capture incidents Vector Machine Learning Vector Machine Learning (VML) Hands-on labs: Create a VML profile, import document sets, and create a VML policy Network Monitor Review of Network Monitor Protocols Traffic filtering Network Monitor best practices Hands-On Labs: Apply IP and L7 filters Network Prevent Network Prevent overview Introduction to Network Prevent (Email) Introduction to Network Prevent (Web) Hands-On Labs: Configure Network Prevent (E-mail) response rules, incorporate them into policies, and use the policies to capture incidents Mobile Email Monitor and Mobile Prevent Introduction to Mobile Email Monitor Mobile Prevent overview Configuration VPN configuration Policy and Response Rule Creation Reporting and Remediation Troubleshooting Network Discover and Network Protect Network Discover and Network Protect overview Configuring Discover targets Configuring Box cloud targets Protecting data Auto-discovery of servers and shares Running and managing scans Reports and remediation Network Discover and Network Protect best practices Hands-on labs: Create and run a filesystem target using various response rules, including quarantining Endpoint Prevent Endpoint Prevent overview Detection capabilities at the Endpoint Configuring Endpoint Prevent Creating Endpoint response rules Viewing Endpoint Prevent incidents Endpoint Prevent best practices Managing DLP Agents Hands-on labs: Create Agent Groups and Endpoint response rules, monitor and block Endpoint actions, view Endpoint incidents, and use the Enforce console to manage DLP Agents Endpoint Discover Endpoint Discover overview Creating and running Endpoint Discover targets Using Endpoint Discover reports and reporting features Hands-on labs: Create Endpoint Discover targets, run Endpoint Discover targets, and view Endpoint Discover incidents Enterprise Enablement Preparing for risk reduction Risk reduction DLP Maturity model System Administration Server administration Language support Incident Delete Credential management Troubleshooting Diagnostic tools Troubleshooting scenario Getting support Hands-on labs: Interpret event reports and traffic reports, configure alerts, and use the Log Collection and Configuration tool Additional course details: Nexus Humans Symantec Data Loss Prevention 14.0 - Administration training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Symantec Data Loss Prevention 14.0 - Administration course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Awakening of the Cosmic Heart, Online Course
By Katarina Heuser
Discover your special powers, receive insights and deep healing together with an abundance of light codes taking your life to the next level!

20345-1 Administering Microsoft Exchange Server 2016/2019
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The audience for this course includes enterprise-level messaging administrators on Exchange Server. IT generalists and helpdesk professionals who want to learn about Exchange Server may also take this course. Students taking this course are expected to have at least two years of experience working in the IT field-typically in the areas of Windows Server administration, network administration, helpdesk, or system administration. They are also expected to have some experience with Exchange Server concepts but previous experience managing Exchange Server is not a requirement. Overview After completing this course, students will be able to: Deploy Exchange Server. Plan and configure storage for Exchange Server. Create and manage various recipient objects in Exchange Server. Perform recipient management and Exchange server management tasks by using Exchange Server cmdlets. Deploy Client Access services in Exchange Server. Manage high availability in Exchange Server. Implement disaster recovery for Exchange Server. Configure and manage message transport in Exchange Server. Configure message security in Exchange Server. Monitor and troubleshoot Exchange Server. Configure Exchange Server role-based access control permissions and configure audit logging for both administrators and users. Implement and manage integration with Exchange Online. This course teaches IT professionals how to administer and support Exchange Server. The course covers how install and configure Exchange Server. It also covers how to manage mail recipients and public folders, including how to perform bulk operations by using Exchange Management Shell. In addition, the course covers how to manage client connectivity, message transport and hygiene, and highly available Exchange Server deployments. It also covers how to implement disaster recovery solutions. Finally, the course covers how to maintain and monitor an Exchange Server deployment and how to administer Exchange Online in a Office 365 deployment. Deploying Microsoft Exchange Server 2016 Overview of Exchange Server Exchange Server architecture Requirements for Exchange Server Deploying Exchange Server Exchange Server Exchange Server Management Tools Lab : Deploying Exchange Server Managing Exchange Server 2016 storage Exchange Server mailbox databases Exchange Server storage Configuring Exchange Server mailbox databases and storage Lab : Configuring Exchange Server storage Managing recipient objects Managing user mailboxes Managing other types of mailboxes Managing other recipients objects Configuring policies and address lists Lab : Managing recipient objects Lab : Configuring address lists and policies Managing recipients and Exchange servers by using Exchange Server cmdlets Overview of the Exchange Management Shell Managing Exchange Servers by using Exchange Management Shell cmdlets Managing Exchange servers by using scripts Lab : Managing Exchange Server and recipient objects by using Exchange Management Shell Implementing client connectivity Configuring client access services Managing client access services Client connectivity in Exchange Server Configuring Outlook on the web Configuring mobile messaging Lab : Configuring client access services Lab : Deploying and configuring client access services on Exchange Server Managing high availability in Exchange Server High availability on Exchange Server Configuring highly available mailbox databases Configuring high availability of Client Access services Lab : Implementing DAGs Lab : Implementing and testing high availability Implementing disaster recovery for Exchange Server Implementing Exchange Server backup Implementing Exchange Server recovery Lab : Backing up Exchange Server data Lab : Restoring Exchange Server data Configuring and managing message transport Overview of message transport Configuring message transport Managing transport rules Lab : Configuring and managing message transport Configuring message security Deploying and managing an Edge Transport server for message security Implementing an antivirus solution for Exchange Server Implementing an antispam solution for Exchange Server Lab : Configuring message security in Exchange Server Monitoring and troubleshooting Exchange Server Monitoring Exchange Server Troubleshooting Exchange Server Lab : Monitoring and troubleshooting Exchange Server Securing and maintaining Exchange Server Securing Exchange Server by using RBAC Configuring audit logging in Exchange Server Maintaining Exchange Server Lab : Securing and maintaining Exchange Server Implementing and managing Exchange Online deployments Overview of Exchange Online and Office 365 Managing Exchange Online Implementing the migration to Exchange Online Managing a hybrid environment Lab : Managing Exchange Online Additional course details: Nexus Humans 20345-1 Administering Microsoft Exchange Server 2016/2019 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the 20345-1 Administering Microsoft Exchange Server 2016/2019 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

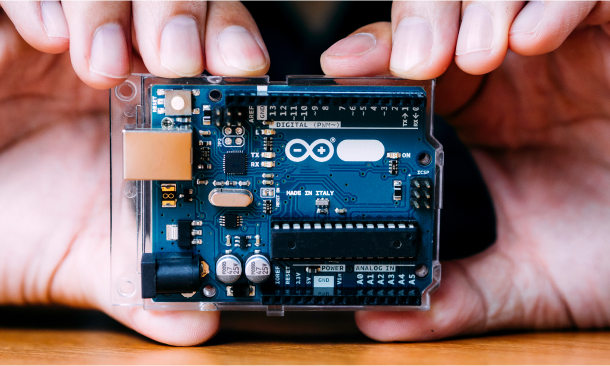
Step into innovation and technology with our groundbreaking course, 'Arduino Interfacing with Sensors in Your Smartphone.' Embark on a journey where creativity meets functionality as you harness the power of Arduino to connect sensors to your smartphone seamlessly. From the thrill of setting up your hardware and software to crafting custom Android apps without coding, this course promises to unlock endless possibilities in mobile technology. Discover the essential components needed to kickstart your Arduino adventure, from hardware requirements to navigating the intricacies of MIT App Inventor. Dive deep into the realms of mobile app development as you explore the Designer and Blocks Editor, laying the foundation for your foray into creating intuitive mobile apps. With our guidance, even those with zero coding experience can craft innovative applications that effortlessly bridge the gap between Arduino and smartphones. Unlock the potential of sensors as you delve into the world of proximity, accelerometer, gyroscope, and magnetometer sensors. Learn how to read analogue sensor data with Arduino and translate it into interactive mobile experiences. Whether you're a budding technologist, a hobbyist seeking to expand your skills, or an entrepreneur with a vision for innovative mobile solutions, this course equips you with the tools and knowledge to turn your ideas into reality. Learning Outcomes: Understand the hardware and software requirements for interfacing Arduino with smartphones. Master MIT App Inventor to design and develop custom Android apps for Arduino projects. Explore various sensors, including proximity, accelerometer, gyroscope, and magnetometer. Learn to create mobile apps without coding, integrating Arduino seamlessly. Gain proficiency in reading analogue sensor data and controlling Arduino remotely via smartphones. Highlights of the Arduino Interfacing with Sensors in Your Smartphone : Unlimited access to the course for a lifetime. Opportunity to earn a certificate accredited by the CPD Quality Standards and CIQ after completing this course. Structured lesson planning in line with industry standards. Immerse yourself in innovative and captivating course materials and activities. Assessments designed to evaluate advanced cognitive abilities and skill proficiency. Flexibility to complete the Course at your own pace, on your own schedule. Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience. Unlock career resources for CV improvement, interview readiness, and job success. Who is this Arduino Interfacing with Sensors in Your Smartphone Course for? Tech enthusiasts eager to explore Arduino and smartphone integration. Hobbyists looking to expand their knowledge in mobile app development. Entrepreneurs seeking to develop innovative mobile solutions. Students interested in learning about sensor interfacing and mobile technology. Engineers and developers aiming to enhance their skills in IoT and mobile connectivity. How is the course assessed? To successfully complete the course you must pass an automated, multiple-choice assessment. The assessment is delivered through our online learning platform. You will receive the results of your assessment immediately upon completion. Will I receive a certificate of completion? Upon successful completion, you will qualify for the UK and internationally-recognised certification and you can choose to make your achievement formal by obtaining your PDF Certificate at a cost of £9 and Hardcopy Certificate for £15. Requirements The Arduino Interfacing with Sensors in Your Smartphone is open to all, with no formal entry requirements. All you need is a passion for learning, a good understanding of the English language, numeracy and IT, and to be over the age of 16. Career Path Mobile App Developer: £25,000 - £70,000 per annum IoT Engineer: £30,000 - £65,000 per annum Software Engineer: £25,000 - £70,000 per annum Electronics Engineer: £25,000 - £55,000 per annum Embedded Systems Developer: £30,000 - £70,000 per annum Technology Consultant: £35,000 - £80,000 per annum Course Curriculum Introduction and Getting Started Introduction 00:03:00 Hardware and Software Requirements Hardware and Software Requirements 00:02:00 Download and Install MIT App Inventor 00:10:00 Download and Install Arduino Pro IDE 00:09:00 Setting Up App Inventor What is App Inventor 00:02:00 Designer and Blocks Editor MIT App Inventor User Interface Explained 00:04:00 First Mobile App to Control Arduino Make your first Mobile App - Blink LED 00:15:00 Code your Arduino - Blink LED 00:05:00 Proximity Sensor Proximity Sensor Mobile App 00:14:00 Light Sensor Mobile App and Arduino Code 00:13:00 Practical Testing 00:03:00 Accelerometer Sensor Accelerometer Sensor Mobile App 00:14:00 Coding Accelerometer Sensor 00:05:00 Gyroscope Sensor Gyroscope Sensor Mobile App and Arduino Code 00:06:00 Magnetometer Sensor Magnetometer Sensor Mobile App and Arduino Code 00:05:00 Make Android App With Zero Experience MIT App Inventor Introduction uuuu 00:03:00 What can you do and system requirements 00:03:00 What is app inventor in More Details 00:02:00 Java Vs App Inventor 00:03:00 Why using App Inventor 00:01:00 App Architecture 00:05:00 Let's Start Making Apps 00:05:00 First App Add Items and Start Programming with Blocks 00:10:00 First App Testing and Running the App using Emulator 00:13:00 Resources you need to visit to Create Better Apps 00:02:00 How to Create a website for your app for free and take credit for it 00:05:00 Android Apps for Arduino with MIT App Inventor without Coding Introduction 00:03:00 App Inventor Overview 00:04:00 An App Challenge 00:01:00 System Requirements 00:01:00 AppInventor Vs Java and C 00:03:00 Why App Inventor Works 00:02:00 App Architecture 00:05:00 Download and Install App Inventor on Your Device 00:09:00 AppInventor UserInterface With Example 00:14:00 Arduino Coding for Led On Off Practical Example 00:09:00 Making an Android App for Led On Off Practical Example 00:12:00 Testing On Off App with Arduino 00:07:00 Make a Login Protected Led Control App 00:14:00 Slider Application to Control Led Brightness 00:15:00 Slider Practical 00:09:00 Practical Connect Bluetooth Module 00:05:00 RGB Led Controller Android Application 00:14:00 RGB LED Arduino Coding 00:12:00 Sensor Readings Arduino Coding 00:09:00 Sensor Readings Android Application 00:17:00 LCD Text Arduino Coding 00:09:00 LCD Text Android Application 00:06:00 Remote Controlled Robot Android Application 00:09:00 Remote Controlled Robot Arduino Coding 00:15:00 Make Money with MIT App Inventor Apps 00:05:00 Reading Analog Sensor with Arduino Introduction 00:02:00 How to read analogue sensors using Arduino 00:02:00 Software Requirements 00:04:00 Wiring Analog Sensors to Arduino 00:09:00 Writing code to collect reading from analogue sensors 00:07:00 Practical Analogue Sensor Testing 00:03:00 Analyse and convert Sensor Reading 00:03:00 Manipulating Sensors Reading 00:06:00 ADC in Arduino Explained 00:14:00
Become An Ethereum Blockchain Developer
By Packt
Discover Ethereum blockchain development with our comprehensive course. From the fundamentals of Solidity to advanced topics such as NFTs and Truffle, we will gain practical skills through hands-on projects. Whether a beginner or an experienced developer, this course equips us with the tools and knowledge to excel in Ethereum blockchain development.
Join the comprehensive Security Guard, CCTV, and Door Supervision course to gain essential skills and knowledge for a successful career in the security industry. Learn security risk analysis, crisis response, CCTV monitoring, and conflict management to ensure safety and compliance. Suitable for aspiring security professionals and those seeking advanced training.

Register on the Ethereum Blockchain DApp using Solidity today and build the experience, skills and knowledge you need to enhance your professional development and work towards your dream job. Study this course through online learning and take the first steps towards a long-term career. The course consists of a number of easy to digest, in-depth modules, designed to provide you with a detailed, expert level of knowledge. Learn through a mixture of instructional video lessons and online study materials. Receive online tutor support as you study the course, to ensure you are supported every step of the way. Get an e-certificate as proof of your course completion. The Ethereum Blockchain DApp using Solidity is incredibly great value and allows you to study at your own pace. Access the course modules from any internet-enabled device, including computers, tablet, and smartphones. The course is designed to increase your employability and equip you with everything you need to be a success. Enrol on the now and start learning instantly! What You Get With The Ethereum Blockchain DApp using Solidity Receive a e-certificate upon successful completion of the course Get taught by experienced, professional instructors Study at a time and pace that suits your learning style Get instant feedback on assessments 24/7 help and advice via email or live chat Get full tutor support on weekdays (Monday to Friday) Course Design The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of Video lessons Online study materials Certification Upon successful completion of the course, you will be able to obtain your course completion e-certificate free of cost. Print copy by post is also available at an additional cost of £9.99 and PDF Certificate at £4.99. Who Is This Course For: The course is ideal for those who already work in this sector or are an aspiring professional. This course is designed to enhance your expertise and boost your CV. Learn key skills and gain a professional qualification to prove your newly-acquired knowledge. Requirements: The online training is open to all students and has no formal entry requirements. To study the Ethereum Blockchain DApp using Solidity, all your need is a passion for learning, a good understanding of English, numeracy, and IT skills. You must also be over the age of 16. Course Content Section 01: What is Blockchain? Introduction to Building an Ethereum Blockchain App 00:02:00 The Beginning of Blockchain 00:05:00 Currency and Cryptocurrency 00:05:00 Why Use the Blockchain? 00:06:00 Blockchain Data and Blocks 00:06:00 Blockchain Immutability 00:03:00 Blockchain Consensus 00:02:00 Building the Blockchain Story 00:03:00 Hashes 00:06:00 What is a Chain of Blocks? 00:04:00 Finding the Nonce 00:05:00 Blockchain Mining 00:03:00 Arriving at Consensus 00:05:00 Public vs. Private Blockchains 00:03:00 Distributed Processing and Blockchain Solutions 00:06:00 Section 02: What is Ethereum? Introduction to Ethereum 00:03:00 Ethereum in Financial Services 00:07:00 Ethereum in Digital Identity Management 00:05:00 Ethereum in Industry Applications 00:06:00 Ethereum in Government 00:03:00 Ethereum Smart Contracts 00:03:00 Ether and the Initial Coin Offering (ICO) 00:06:00 Decentralized Autonomous Organization (DAO) 00:03:00 The Ethereum Ecosystem 00:06:00 Building Blockchain Apps 00:05:00 Section 03: The Ethereum Ecosystem & the Development Lifecycle Parts of the Ethereum Blockchain 00:11:00 Smart Contracts 00:05:00 Smart Contract Languages 00:04:00 What are Virtual Machines? 00:06:00 The Ethereum Virtual Machine (EVM) 00:03:00 Fueling Your Code with Gas 00:05:00 Tools for Ethereum SDLC 00:03:00 Blockchain Client 00:03:00 Writing and Testing Your Code, Part 1 00:05:00 Writing and Testing Your Code, Part 2 00:07:00 Section 04: Ethereum Development Tools Your Ethereum Development Toolbox 00:04:00 Installing Geth Lab (CLI Blockchain Client) 00:04:00 Installing Ganache Lab (Test Blockchain) 00:06:00 Installing Truffle Lab (Development Environment and Testing Framework) 00:06:00 Installing Microsoft Visual Studio Code Lab (IDE) 00:05:00 Section 05: Your Ethereum Wallet What is an Ethereum Wallet? 00:02:00 Types of Ethereum Wallets 00:06:00 Web and Desktop Wallets 00:07:00 Mobile, Hardware, and Paper Wallets 00:09:00 Installing MetaMask 00:05:00 Section 06: Building Your First Ethereum App Preparing Your First Truffle Project 00:07:00 Writing a Simple Smart Contract 00:11:00 Compiling Your Simple Smart Contract 00:10:00 Deploying Code and Invoking Functions 00:09:00 Section 07: Learning about Smart Contracts Smart Contracts Review 00:03:00 What is Supply Chain? 00:07:00 Supply Chain Challenges and Blockchain Solutions 00:07:00 Blockchain Solution Examples 00:04:00 Ethereum Tokens 00:06:00 Your Supply Chain Project 00:08:00 Exploring Solidity 00:11:00 Defining Types of Data 00:05:00 Data Types Lab 00:09:00 Solidity Data Modifiers, Part 1 00:04:00 Solidity Data Modifiers, Part 2 00:06:00 Revisiting Gas 00:06:00 Controlling Flow 00:12:00 Handling Errors 00:05:00 Section 08: Your Supply Chain Smart Contract dApp Designing Your Supply Chain App 00:04:00 What are dApps? 00:06:00 Token Smart Contract Details 00:08:00 Supply Chain Smart Contract Details 00:06:00 Smart Contract Road Map 00:02:00 Token Smart Contract Data Lab, Part 1 00:07:00 Token Smart Contract Data Lab, Part 2 00:09:00 Supply Chain Smart Contract Data Lab, Part 1 00:05:00 Supply Chain Smart Contract Data Lab, Part 2 00:03:00 Token Smart Contract Functions Lab, Part 1 00:05:00 Token Smart Contract Functions Lab, Part 2 00:04:00 Supply Chain Smart Contract Functions Lab, Part 1 00:10:00 Supply Chain Smart Contract Functions Lab, Part 2 00:09:00 Using Events 00:07:00 Implementing Events 00:05:00 More on Ownership 00:08:00 Designing for Security 00:09:00 Implementing Minimal Functionality 00:06:00 Section 09: Testing Ethereum Apps Blockchain dApp Testing 00:10:00 Deploying Your dApp to a Test Blockchain Lab 00:08:00 Writing Tests for Ethereum dApps 00:06:00 Command-Line Testing Lab, Part 1 00:04:00 Command-Line Testing Lab, Part 2 00:11:00 Command-Line Testing Lab, Part 3 00:03:00 JavaScript Testing 00:08:00 Logging and Handling Errors 00:07:00 Logging Activity in Smart Contracts 00:05:00 Fixing Bugs in a dApp 00:05:00 Section 10: Deploying and Maintaining Ethereum Apps Test Blockchains 00:08:00 The Live Blockchain (Mainnet) 00:05:00 Connecting to Multiple Blockchains and Infura Lab 00:05:00 Configuring Truffle and Infura Lab 00:06:00 Funding Your Account Lab 00:04:00 Deploying to the Live Blockchain 00:08:00 Section 11: Integrating Non-Blockchain Apps with Ethereum Blockchain and Database Storage 00:11:00 Execution and Flow in dApps and Traditional Applications 00:05:00 Blockchain Incorporation Design Goals 00:06:00 Integration Considerations for Incorporating Blockchain 00:06:00 Interface Considerations for Incorporating Blockchain 00:04:00 Resources Resources - Ethereum Blockchain DApp Using Solidity 00:00:00

Description A private cloud involves a distinct and secure cloud-based environment where only the specified client can operate the system. With the knowledge of Private Cloud, you can able to work efficiently to deploy, use, and manage VMs, applications, and other IT resources on hardware to your organization. If you want to gain mastery over cloud computing, the course is for you. The course is divided into two parts that deals with the two certifications of MCSE: Exam 70-246 and Exam 70- 247. In the Exam 70-246, you will know the basics of the cloud, cloud services, monitoring and automating responses while in the Exam 70-247 part, you will learn how to work with the cloud. In short, at first, you will learn the basic cloud concept, then you will know how to use the cloud system. Assessment: At the end of the course, you will be required to sit for an online MCQ test. Your test will be assessed automatically and immediately. You will instantly know whether you have been successful or not. Before sitting for your final exam you will have the opportunity to test your proficiency with a mock exam. Certification: After completing and passing the course successfully, you will be able to obtain an Accredited Certificate of Achievement. Certificates can be obtained either in hard copy at a cost of £39 or in PDF format at a cost of £24. Who is this Course for? Private Cloud with System Center 2012 R2 - Complete Video Training is certified by CPD Qualifications Standards and CiQ. This makes it perfect for anyone trying to learn potential professional skills. As there is no experience and qualification required for this course, it is available for all students from any academic background. Requirements Our Private Cloud with System Center 2012 R2 - Complete Video Training is fully compatible with any kind of device. Whether you are using Windows computer, Mac, smartphones or tablets, you will get the same experience while learning. Besides that, you will be able to access the course with any kind of internet connection from anywhere at any time without any kind of limitation. Career Path After completing this course you will be able to build up accurate knowledge and skills with proper confidence to enrich yourself and brighten up your career in the relevant job market. System Center 2012 What is System Center 2012 FREE 00:30:00 Introducing the Cloud Discussion of Cloud Computing 00:19:00 Important Requirements 00:07:00 Working with System Center and the Infrastructure 00:05:00 Maintaining the Cloud Health 00:05:00 How Components are Integrated 00:06:00 Are You in Compliance 00:05:00 Working with the Business Cloud Examining SC 2012 VMM 00:17:00 Working with VMs with the VMM 00:11:00 Creating Clouds for Business 00:16:00 Cloud Services Looking at Service Templates and VMM Profiles 00:22:00 Web Deploy Packages 00:08:00 Server App V Introduction 00:05:00 The Data of the N Tier Application 00:05:00 What's New with VMM R2 00:07:00 Monitoring Overview of Operations Manager 00:20:00 Customize the Monitoring Operations 00:09:00 Monitoring Application Performance 00:14:00 Advanced Monitoring 00:04:00 Using Operations Manager for Applications 00:04:00 Using Operations Manager for the Network 00:11:00 Using Operations Manager for Distributed Applications 00:07:00 What's New in Operations Manager 2012 R2 00:09:00 Automating Responses Looking at Orchestrator 2012 00:08:00 Putting Orchestrator, Operations Manager, and Service Manager Together 00:15:00 What's New with Orchestrator 2012 R2 00:04:00 Managing Problems in the Private Cloud What is Problem Management 00:07:00 Using Custom Rules 00:08:00 Service Management in the Private Cloud Service Manager Introduction 00:10:00 Security Settings 00:09:00 Work Items 00:08:00 Incident Queues and Service Offerings 00:03:00 What's New with Service Manager 2012 R2 00:01:00 Cloud Protection, Recovery, and Compliance Protecting and Recovering Data for the Private Cloud 00:29:00 Overview of the Process Pack for IT GRC 00:14:00 Installing the Process Pack for IT GRC 00:06:00 Implementing an IT GRC Control Management Program 00:06:00 How to Maintain Compliance Through VMM Security Baselines with System Center 00:06:00 What's New with DPM 2012 R2 Advisor 00:03:00 SLAs, Dashboards and Widgets Configuring and Deploying Widgets and Dashboards 00:12:00 Real-Time State Using Visio 00:10:00 System Center Analytics 00:12:00 Service Level Tracking 00:05:00 Viewing SSRS and Excel to View Data 00:04:00 PerformancePoint 00:04:00 Cleaning Up System Center Databases Service Manager Groom Settings 00:08:00 View and Purge Orchestrator Runbook Logs 00:08:00 Understanding the Private Cloud Understanding the Private Cloud FREE 00:09:00 Preparing to Deploy the Cloud 00:06:00 Components of the Private Cloud 00:13:00 System Center 2012 Components 00:13:00 Using Hyper-V with VMM 00:07:00 Using VMM to Deploy the Cloud VMM Architecture 00:16:00 Install and_or Upgrade VMM 00:08:00 Host Groups 00:13:00 Understanding Security 00:06:00 Whats New with VMM R2 00:10:00 Working With the Private Cloud Infrastructure PXE and Update Servers 00:08:00 Bare Metal Hyper-V Host Servers 00:06:00 Configuring the Update Server Role 00:08:00 The Update Baseline 00:10:00 Virtual Applications Dynamic Application Deployment 00:10:00 Server Application Virtualization Overview 00:16:00 Configuring Server App-V Components 00:05:00 Sequencing and Deploying Virtual Apps 00:08:00 Components of the Private Cloud SQL Server Profiles 00:08:00 OS Profiles 00:05:00 Application Profiles 00:04:00 Hardware Profiles 00:07:00 VM Templates 00:05:00 Self-Service User Role 00:10:00 A First Business Unit Cloud What is Private Cloud Computing 00:08:00 Installing and Configuring App Controller 00:05:00 Creating and Managing Services and Service Templates 00:11:00 Changes with App Controller 2012 R2 00:01:00 Private Cloud Infrastructure Operations Manager Components 00:25:00 Upgrading 00:10:00 Notifications 00:07:00 Management Packs 00:15:00 Putting It All Together 00:06:00 What's New in Operations Manager 2012 R2 00:09:00 Monitoring the Private Cloud Using SharePoint 00:04:00 Templates for Monitoring 00:23:00 Watching a Distributed App 00:07:00 Service Management for the Cloud What is Service Manager 00:15:00 Understanding Work Items 00:19:00 Connectors 00:08:00 Notifications 00:03:00 Private Cloud Service Catalog Private Cloud Service Catalog 00:10:00 Service Level Management 00:03:00 Automation in the Private Cloud Planning DPM Deployment 00:11:00 DPM Technologies 00:07:00 Upgrading DPM 00:03:00 Configuring DPM for the Private Cloud 00:13:00 Configuring Application Protection for the Private Cloud 00:11:00 What's New with DPM 2012 R2 00:03:00 Security for the Cloud Orchestrator Architecture 00:08:00 Deployment and Configuration of Orchestrator 00:07:00 Using Runbooks 00:07:00 Using Integration Packs 00:17:00 Certificate and Transcript Order Your Certificates and Transcripts 00:00:00
