- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
LTE Backhaul training course description This course provides a concise insight into the LTE backhaul. Key parts of the course are detailed looks at the transport of messages and the S1 and X2 protocols. What will you learn Describe the overall architecture of LTE. Explain how data and signalling messages are transported in LTE. Describe the S1 protocol. Describe the X2 protocol. LTE Backhaul training course details Who will benefit: Anyone working with LTE. Prerequisites: Mobile communications demystified Duration 2 days LTE Backhaul training course contents Introduction In the first section of the course, we review LTE and its hardware and software architecture. Requirements and key features of LTE. LTE Architecture and capabilities of the UE. Architecture of the E-UTRAN, functions of the eNB. EPC architecture, and functions of the MME, SGW, PGW and PCRF. System interfaces and protocol stacks. Example information flows. Dedicated and default bearers. EMM, ECM and RRC state diagrams. Architecture of the radio access network In this section, we look in more detail at the architecture of the evolved UMTS terrestrial radio access network (E-UTRAN). Logical and physical architecture of the E-UTRAN. Numbering, addressing and identification. E-UTRAN functions. E-UTRAN protocol stacks. Timing and frequency synchronisation in LTE. Transport of data and signalling in LTE Here, we look in more detail at the techniques and protocols that are used to transport data and signalling messages across the evolved UMTS terrestrial radio access network and the evolved packet core. Quality of service in LTE. The GPRS tunnelling protocol. Differentiated services Multi-protocol label switching (MPLS). The stream control transmission protocol (SCTP). The S1 application protocol This section gives a detailed account of the signalling procedures in the S1 application protocol, which the MME uses to control the operation of the eNB. The material looks at the procedures, messages and information elements, and relates them to the system-level procedures in which they are used. S1 setup procedure. UE context management procedures. Non access stratum information transport. Procedures for managing the evolved radio access bearer (E-RAB). Paging procedures. Mobility management procedures for S1-based handovers. Procedures in support of self-optimising networks. The X2 application protocol This section gives a detailed account of the signalling procedures in the X2 application protocol, which is used for peer-to-peer communication between eNBs. The material looks at the procedures, messages and information elements, and relates them to the system-level procedures in which they are used. X2 setup procedure. Mobility management procedures for X2-based handovers Procedures in support of self-optimising networks. High level system operation In the final section, we bring our discussions of the S1 and X2 application protocols together by reviewing the system-level operation of LTE. Attach procedure. Transitions between the states of RRC Idle and RRC Connected. Tracking area updates in RRC Idle. Handover procedures in RRC Connected.

LTE Airside training course description This course provides a concise insight into the LTE airside. Key parts of the course are detailed looks at the air interface protocol stack, cell acquisition, transmission and reception of data and of he layer 1 procedures along with layer 2 procedures. What will you learn Explain the RF optimisation flowchart. Describe the importance of Reference Signal Received Power (RSRP). List many of the 3GPP recommended KPIs. Describe the concept of APN AMBR and UE AMBR within LTE. Describe the use of planning and optimisation computer tools. LTE Airside training course details Who will benefit: Anyone working with LTE. Prerequisites: Essential LTE Duration 2 days LTE Airside training course contents Introduction and review of LTE This section describes the requirements of LTE and key technical features, and reviews the system architecture. LTE Architecture, UE, E-UTRAN and EPC. Specifications. OFDMA, SC-FDMA and MIMO antennas This section describes the techniques used in the LTE air interface, notably orthogonal frequency division multiple access (OFDMA) and multiple input multiple output (MIMO) antennas. Communication techniques for fading multipath channels. OFDMA, FFT processing and cyclic prefix insertion. SC-FDMA in the LTE uplink. Multiple antenna techniques including transmit & receive diversity and spatial multiplexing. Introduction to the air interface This section covers the operation of the air interface, the channels that it uses, and the mapping to the time and frequency domains of OFDMA and SC-FDMA. Air interface protocol stack. Logical, transport and physical channels. Frame and slot structure, the resource grid. Resource element mapping of the physical channels and physical signals. LTE spectrum allocation. Cell acquisition This is the first of three sections covering the air interface physical layer. Here, we cover mobile procedures to start low-level communications with the cell, and base station transmission of the corresponding information. Primary/secondary synchronisation signals. Downlink reference signals. The master information block. Physical control format indicator channel. Organisation and transmission of the system information. Data transmission and reception In this section, we cover procedures used for data transmission and reception on the shared channels, and describe in detail the individual steps. Data transmission and reception on the uplink and downlink. Scheduling commands and grants on the PDCCH. DL-SCH and UL-SCH. Physical channel processing of the PDSCH and PUSCH. Hybrid ARQ indicators on the PHICH. Uplink control information on the PUCCH. Uplink demodulation and sounding reference signals. Additional physical layer procedure This section concludes our discussion of the air interface physical layer, by discussing a number of procedures that support its operation. Transmission of the physical random access channel. Contention and non-contention based random access procedures. Discontinuous transmission in idle and connected modes. Uplink power control and timing advance. Air interface layer 2 This section describes the architecture and operation of layer 2 of the air interface protocol stack. MAC protocol, interactions with the physical layer, use for scheduling. RLC protocol, transparent, unacknowledged and acknowledged modes. PDCP, including header compression, security functions and recovery from handover.

VSAT training course description This 2 day training course examines what VSAT is, its usages and users. It then looks at the hardware required for VSAT. What will you learn Explain how VSAT is used Describe the hardware required for VSAT operation. VSAT training course details Who will benefit: Anyone working with VSAT. Prerequisites: None. Duration 2 days VSAT training course contents Introduction History of PMR VSAT Introduction A Brief History Satellite Services Satellite Communications Satellite Footprint Radio Frequency Bands ITU Definitions VSAT Users What is a VSAT? VSATs - Usage VSATs - Users VSAT Hardware Typical System Hardware VSAT ODU and IDU VSAT Station Equipment Diplexer and Feed Horn Typical Waveguide Element Polarisation VSAT Hub Antenna Pointing Outdoor Unit Outdoor (continued) VSAT Network Earth Stations Indoor Unit VSAT Network Earth Stations Indoor Unit Element Hub Station Hub Sub-station Hub Options Hub Options (2) Hub Options (3) Temporary Mount

Negotiation Skills and Techniques for Engineers and Technical Professionals
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course This is a 2 full-day course that is aimed at providing professionals in the Oil & Gas business with a comprehensive set of core negotiating skills. Negotiations take place in many situations e.g. between peers, manager and subordinate, company and trade unions, company and government. The skills learnt on this course will be useful in all of these situations. However, this course puts a focus on the skills needed in commercial negotiations. A particular emphasis is placed on the relationship and negotiations typically carried out between client and contractor, vendor or the provider of services. A mixture of theory, examples and practical exercises are used so that the participants understand the principles and get an opportunity to try them out. The case studies used are real cases encountered in the Oil & Gas industry. Training Objectives Many technical experts find it difficult to move out of their expertise areas and deal with commercial matters. Negotiating to optimise business value is a step further from their comfort zones. All too often negotiations are then left to finance personnel. They bring many strengths to the table but an understanding of engineering trade-offs is not one of them. By the end of this course, the participants will add to their technical know-how a core competence in negotiation skills. They will thus become formidable negotiating opponents. Target Audience The course is intended for middle-managers and technical and other staff who are responsible for contracts, but with limited previous exposure to negotiations, and who will need these skills in the near future. Course Level Intermediate Trainer Your expert course leader is a consultant, manager and engineer with more than 30 years' experience in a broad range of positions. He spent 15 years with the Shell group and during this time, gained extensive negotiating experience with contractors, vendors, service agents, trade unions and purchasers of equipment and products. Over the last 15 years, he has worked with a broad range of multinational businesses across the globe in a wide range of negotiation related roles including: Developing negotiating capability and skillsets Advising on negotiation strategies Establishing Alliances, Joint Ventures and Partnerships, & Remediating Alliances, Joint Ventures and Partnerships He has many years of teaching experience to technical staff - both in a corporate setting, and in an academic setting - for Melbourne University in Melbourne, Australia. Several thousand people from around the world have benefited from his courses. He brings an engineer's practical perspective, and can readily empathize with technical staff making forays into the commercial world of negotiations. He is joint author (with Professor Danny Samson) of Patterns of Excellence ISBN 0273638769, published by Financial Times Management. This has been adopted by a number of blue chip companies as the core text for management development. Corporate Experience: 15 years with Shell in a broad range of international & domestic technical and managerial and change management roles. Consulting Experience: 5 Years with McKinsey Consulting Group 4 Years with Melbourne Business Schoo POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

Natural Gas & LNG Sales Agreements
By EnergyEdge - Training for a Sustainable Energy Future
Enhance your knowledge of natural gas and LNG sales agreements with EnergyEdge course. Enroll now to gain valuable industry knowledge and skills.

Junos Operating System training course description This course provides students with the foundational knowledge required to work with the Junos OS and to configure Junos devices. The course provides a brief overview of the Junos device families and discusses the key architectural components of the software. The course then delves into foundational routing knowledge and configuration examples including general routing concepts, routing policy, and firewall filters. Delegates will gain experience in configuring and monitoring the Junos OS and monitoring basic device operations. This course is based on Junos OS Release 15.1X49. What will you learn Describe the design architecture of the Junos OS. Navigate within the Junos CLI and perform tasks within the CLI operational and configuration modes. Configure and monitor network interfaces. Navigate within the Junos J-Web interface. Identify where you might use firewall filters. Explain basic routing operations and concepts. Identify key factors in Juniper Networks' security. Junos Operating System training course details Who will benefit: This course benefits individuals responsible for configuring and monitoring devices running the Junos OS. Prerequisites: TCP/IP foundation for engineers Duration 3 days Junos Operating System training course contents Junos Operating System Fundamentals The Junos OS Traffic Processing Overview of Junos Devices User Interface Options-The Junos CLI User Interface Options The Junos CLI: CLI Basics The Junos CLI: Operational Mode The Junos CLI: Configuration Mode User Interface Options-The J-Web Interface The J-Web GUI Configuration Lab 1: User Interface Options Initial Configuration Factory-Default Configuration Initial Configuration Interface Configuration Lab 2: Initial System Configuration Secondary System Configuration User Configuration and Authentication System Logging and Tracing Network Time Protocol Archiving Configurations SNMP Lab 3: Secondary System Configuration Operational Monitoring and Maintenance Monitoring Platform and Interface Operation Network Utilities Maintaining the Junos OS Password Recovery System Clean-Up Lab 4: Operational Monitoring and Maintenance Interface Configuration Examples Review of the Interface Configuration Hierarchy Interface Configuration Examples Using Configuration Groups Routing Fundamentals Routing Concepts: Overview of Routing Routing Concepts: The Routing Table Routing Concepts: Routing Instances Static Routing Dynamic Routing Lab 5: Routing Fundamentals Routing Policy Routing Policy Overview Case Study: Routing Policy Lab 6: Routing Policy Firewall Filters Firewall Filters Overview Case Study: Firewall Filters Unicast Reverse-Path-Forwarding Checks Lab 7: Firewall Filters Class of Service CoS Overview Traffic Classification Traffic Queueing Traffic Scheduling Case Study: CoS Lab 8: Class of Service JTAC Procedures Opening a Support Case Customer Support Tools Transferring Files to JTAC Juniper Security Concepts Security Challenges Juniper's Security Focus Appendix A: IPv6 Fundamentals IPv6 Addressing Protocols and Services Configuration

OSPF training course description A detailed hands on examination of OSPF. Hands on sessions are used to reinforce the theory rather than teach specific manufacturer equipment. The course starts with a recap of reading routing tables and then jumps straight in with simple OSPF configuration. OSPF features are then studied and configured before moving onto how OSPF works within an area. Multi area OSPF is then studied before looking at OSPF operation in detail by analysing OSPF packets. Finally areas are covered again in more detail followed by troubleshooting. What will you learn Design OSPF networks. Design IP addressing schemes suitable for route summarisation. Troubleshoot OSPF networks. Describe the operation of OSPF. OSPF training course details Who will benefit: Technical staff working with OSPF. Prerequisites: TCP/IP Foundation for engineers Duration 3 days OSPF training course contents Basic routing and OSPF Reading routing tables, routing protocols, What is OSPF? Process IDs, passive interfaces. Hands on Simple OSPF configuration. OSPF History of OSPF, metrics, costs, convergence, Distance Vector vs. Link state routing protocols, IGPs, classless, OSPF features, load sharing, per packet/destination, OSPF authentication. Hands on Configuring OSPF features. OSPF within an area How OSPF works, LSDB, LSDB benefits and disadvantages, LSA types, Type 1 and 2, LSA propagation, router IDs, hellos, configuring hellos, the exchange protocol. Hands on Investigating OSPF structures. Areas Scalability, why areas? Area IDs, area 0, ABRs, ABR resilience, areas & LSDBs, areas & LSAs, Type 3 LSAs, virtual links. Hands on Multi area OSPF. Redistribution Multiple routing protocols, common scenarios, routing distance, External LSAs, E1 and E2. Type 4 LSAs. OSPF and default routes. Hands on Configuring static route redistribution. Route aggregation Route summarisation. How to aggregate, ABR summarisation, ASBR summarisation. Hands on OSPF address summarisation. OSPF packet formats OSPF packets, protocol stack, OSPF stages, packet flows, packet types, the OSPF header, multicasts, Hello, DDB, LS request, LS update, LS ACK, LSA header, LSA formats, neighbours, neighbour states, DRs, adjacencies, BDRs, DR election. Hands on Analysing OSPF packets, troubleshooting. OSPF network types BMA, NBMA, Point to point links. Hands on Configuring OSPF over Frame Relay. OSPF stub areas LSA types, area types, area architecture, stub areas, default routes, benefits and disadvantages of stub areas, TSSAs, NSSAs, Type 7 LSAs. Hands on Stub and TSSA configuration. The OSPF MIB SNMP overview, MIB 2, the OSPF MIB, OSPF MIB groups, useful objects, OSPF traps. Hands on the OSPF MIB. troubleshooting. Summary RFCs, OSPF design guidelines. OSPF variants (appendix) OSPF on demand, MOSPF, multicast overview, Type 6 LSAs, OSPF for IPv6 (OSPFv3).

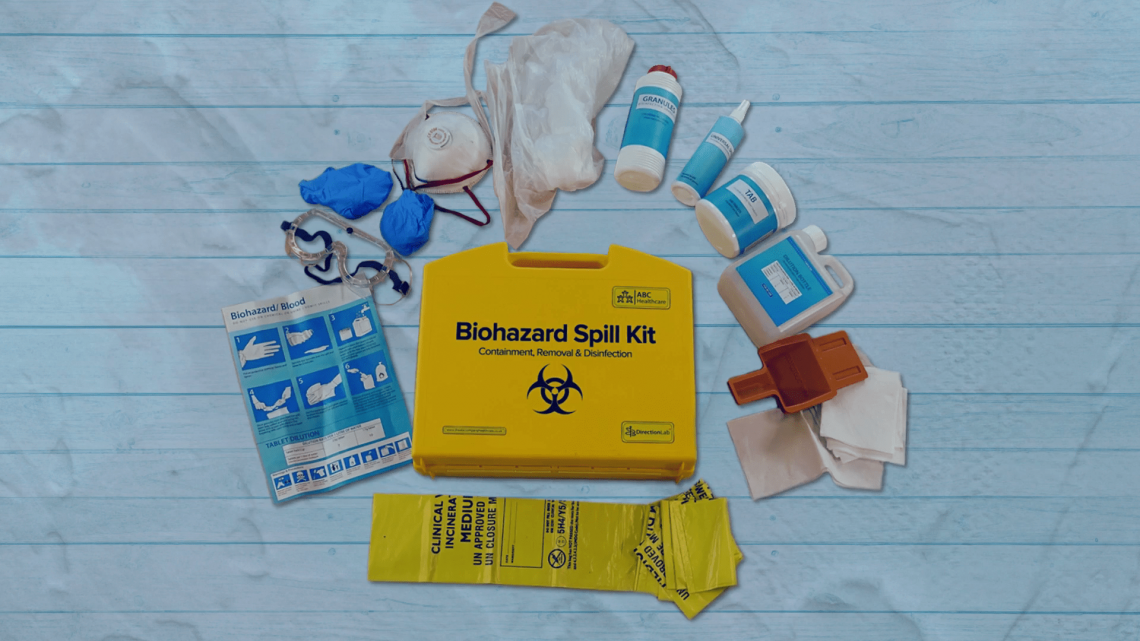
Biohazard Safety: Managing Blood and Body Fluid Spillages Instructor
By Guardian Angels Training
Gain expertise in biohazard safety with our "Biohazard Safety: Managing Blood and Body Fluid Spillages Instructor Training" course. Ideal for healthcare professionals, lab staff, and emergency responders.
Natural Gas Properties & Sulphur Recovery
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) This 5 half-day VILT course will comprehensively cover the technical aspects of gas processing. The scope will be from the wellhead through the typical gas processing plant and discuss gas gathering (pipeline hydraulics), natural gas treating (H2S, CO2 removal), acid gas injection and sulfur recovery. One unique aspect of this training course is the operations and troubleshooting discussions in each module. This VILT course is suited to technical personnel or technical management. Training Objectives After the completion of this VILT course, participants will be able to: Grasp the key specifications of natural gas and liquid products Understand the physical and transport properties of gases and liquids and liquid-vapor phase behavior Explore the various technologies for processing natural gas and to make the specifications Examine the design of the technologies Learn how to diagnose operating problems to keep facilities running reliably Target Audience This VILT course is intended for all surface technical personnel such as process engineers & technologists, facility engineers and production engineers & technologists. This VILT course will greatly benefit but not limited to: Process, petroleum and production engineers Field operators and technicians Personnel involved in gas treatment and processing Managers and Supervisors involved with gas processing operations Course Level Basic or Foundation Intermediate Training Methods The VILT course will be delivered online in 5 half-day sessions comprising 4 hours per day, with 2 breaks of 10 minutes per day. Course Duration: 5 half-day sessions, 4 hours per session (20 hours in total). The maximum number of participants for this course is 20 persons. Case studies and Exercises: This VILT course will use actual case references throughout its duration in various forms. This will allow the application of the participants' newly-acquired knowledge. Case studies also stimulate independent thinking and discussion among the participants Trainer Your expert course leader has written several papers that have been published in both academic and industry journals. He has over 30 years of industry experience, specializing in gas processing (pipeline hydraulics, separation, dehydration, treating, sulphur recovery and refrigeration processes) and also has experience with crude oil dehydration, stabilization and micro-refining topping plants. He has experience with developing new technology and is recently involved in lithium, waste biomass and used motor oil pyrolysis and geothermal projects. He has recognized expertise in thermodynamics and physical and transport properties of fluids. He has consulted for several EPC and operating companies through his company Chem-Pet Process Tech., and currently holds the role of Director of Technology in an integrated engineering and solutions provider to the energy industry. He is currently involved with a small power-based carbon capture project as well as helping clients determine the best options for utilities decisions. He has been involved with CO2 dehydration and CO2 flood gas treating as well as acid gas injection projects for several years. Highlighted Achievements: Developed ORC geothermal model to determine the available power from wells in Alberta Acting on the Technical Advisory Board for E3 Metals, extracting lithium from formation water. Acted as a Subject Matter Expert for assessing the performance of the Plains Midstream Canada, Empress 1 Deep Cut Straddle Plant in a potential litigation. Acted as an Expert Witness for JL Transportation patent defence of a dense phase technology. Process engineer lead on the addition of the new Orloff gas plant for Deltastream. Also troubleshooted the oil battery shipping pump, plate exchanger and FWKO and treater. Evaluated gas processing and sulphur recovery options for new feeds to the Zhaikmunai Zelenovsky Gas Plant, Kazakhstan (with PM Lucas, Serbia). Completed capacity analysis for hydrocarbon dew point versus liquid recovery of three trains at Birchcliff Pouce Coupe facility including amine unit, refrigerated gas plant and acid gas injection. Completed process design for CO2 flue gas dehydration for Husky Energy Inc (with Status Engineering) Provided simulations of EnCana Foster Creek and Christina Lake and Husky McMullen SAGD facilities (with Vista Projects). Performed process engineering for Cenovus Pelican Lake SAGD pilot (with GRB Engineering) Bear Lake heavy oil polymer injection pilot (with GRB Engineering). Lead process engineer on the design of IEC Kerrobert crude oil micro-refinery (topping plant). Provided engineering support and troubleshooting for Enerchem Slave Lake Crude tower and product blending (with Status Engineering). POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

Assessing and Managing Cyber Security Risks for Essential Services Operators
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) This 3 half-day Virtual Instructor Led Training (VILT) course will help participants grasp the idea of real-world risk management and how this relates to the cyber world. The VILT course will cover topics surrounding identifying cyber risks and vulnerabilities, guidance on applying administrative actions, and comprehensive solutions to ensure your organization is adequately secure and protected. The VILT course will guide participants on how to conduct a security risk assessment for their organization, and equip them with the skills to develop a risk compliance assessment plan as well as methods to develop risk management strategies which can improve their organization's security posture. The VILT course has at least a 30% hands-on approach through the use of Table Top Exercises. The VILT course will cover the following modules: Introduction to Risk Assessments (RA) Threat Actors and Their Motivations Threat and Risk Assessment Critical Controls Identification Maturity Assessment Treated Cyber Risk Profile Target Cyber Risk Profile and Strategy Target Audience The VILT course is intended for professionals responsible for organizational information and security system and those involved in operating and maintenance of critical information and IT network & sotware systems. Professionals who are designated as the Single Point of Accountability (SPoA) as well as system auditors will find this course useful. Course Level Basic or Foundation Training Methods The VILT course will be delivered online in 3 half-day sessions comprising 4 hours per day, with 2 x 10 minutes break per day, including time for lectures, discussion, quizzes and short classroom exercises. Course Duration: 3 half-day sessions, 4 hours per session (12 hours in total). This VILT course is delivered in partnership with ENGIE Laborelec. Trainer Your expert course leader is a is specialized in cybersecurity risk management. Before joining ENGIE, she worked for The National Cybersecurity Agency of France (ANSSI) based in Paris (France) and for Deloitte Belgium located in Zaventem (Belgium). She has been involved in cybersecurity projects focusing on the principle of protecting critical infrastructures. Her different experiences in Cyber Security, Anti-Money Laundering and Global Trade Compliance (including Export Control and Customs) gave her the opportunity to use methodologies tackling strategic, operational and financial control issues at all levels of an organization: people, business processes, IT applications and infrastructure, legal and regulatory compliance. She was an EBIOS Risk Manager (RM) trainer while she worked for the French government; EBIOS RM is the French method for assessing and treating digital risks. She also had the opportunity to represent France towards European institutions and other relevant stakeholders for topics related to cybersecurity risk management. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

Search By Location
- training Courses in London
- training Courses in Birmingham
- training Courses in Glasgow
- training Courses in Liverpool
- training Courses in Bristol
- training Courses in Manchester
- training Courses in Sheffield
- training Courses in Leeds
- training Courses in Edinburgh
- training Courses in Leicester
- training Courses in Coventry
- training Courses in Bradford
- training Courses in Cardiff
- training Courses in Belfast
- training Courses in Nottingham