- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
2657 Courses in Cardiff
Overview This course is specially designed to increase the fundamental knowledge of business analysts and their roles and functions more efficiently. In this course, participants attain skills and knowledge of efficient ways to approach, the best methods to elaborate the supplies for business system projects.

Overview Learn how to deal with conflict more effectively through one of our training courses and you can save people a lot of time, money, stress, and distraction. We offer a range of market-leading mediation training courses: from half-day to five-day programmes, covering all areas of mediation. This includes workplace mediation, neighbourhood and family conflict, bullying and harassment, and commercial disputes.
Overview This will include lectures, a detailed simulation exercise, and group discussions. Delegates will recognize the elements where their organizations may have the skills and resources to manage a crisis, but the course will help identify where specialist external support may also be required. The course is designed to provide a balanced view of how best to manage specific crisis issues while simultaneously minimizing any negative impact on ongoing business operations. Delegates will develop a list of subjects to address upon returning to their sponsoring organization

Overview Objectives Define brands and understand the opportunities and challenges facing them in highly competitive business landscapes Plan and craft a powerful brand positioning statement that reflects the brand's promise and the expectations of their most valued customers Build a strategic brand and track its growth and sustainability using researched processes Explore the elements of brand equity and the constituents of brand identity to build consistent and sustainable brands Identify various brand strategies to come up with sound actions aligned with the status of existing and new markets and products Master the process for conducting a full brand audit to evaluate brand performance and take remedial actions

Overview This course is meant for legal professionals to enhance their skills in litigation and understand the core areas of the process so that they can deliver great services to their clients. The course will focus on updating the skills in civil procedure with recent case law and legislative reforms to everyday issues.

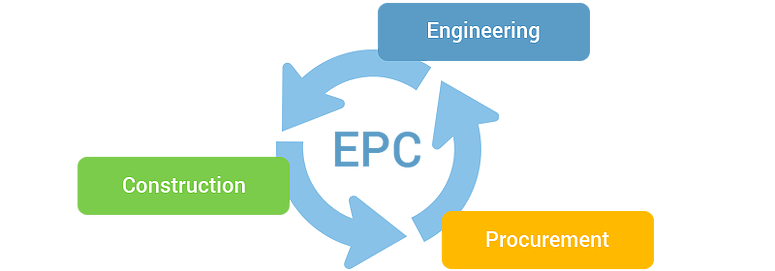
Overview EPC (Engineering, Procurement and Construction) is a very challenging area and is very competitive as well. Companies dealing with large and complex EPC projects are more often get involved in mitigation by complex contract laws and management that lead to huge financial losses. It is very important to Know-how EPC contract laws, and their commercial and financial aspects to gain skills and the ability to deal with complex contract laws and reduces the risk.
Overview Enterprise Content Management System also known as EDRMS Electronic Document and Record Management System is basically a kind of IT-based system which is developed to manage the creation, tracking, storage and disposal of all physical and digital documents and records.

Overview Objective Understand the requirement of Information Security Concepts and Definitions of Information Security Management Systems Deeply Analysing the policies, Standards and procedures How to deliver a balanced ISMS and following its security procedures Analysing the Information risk management Evaluating the organisational responsibilities Understanding the Information security controls Scrutinising Legal framework Techniques of Cryptographic models

Overview In this course participants will learn how to design, implement as well as achieve desired results from the Public Relations as well as Strategic Marketing along with promoting the product and services of their organisations.

Overview This Leadership and Management course is essential reading for anyone wanting to improve their skills and reach their potential as a team leader or manager. The course is fully interactive and prompts you to assess your own leadership or management style and then learn how to develop it further. The course covers key topics such as effective communication, the importance of managing your time well, how to build solid relationships with your team, mental fitness and taking care of your own well-being, and how to better solve workplace problems.

Search By Location
- Courses in London
- Courses in Birmingham
- Courses in Glasgow
- Courses in Liverpool
- Courses in Bristol
- Courses in Manchester
- Courses in Sheffield
- Courses in Leeds
- Courses in Edinburgh
- Courses in Leicester
- Courses in Coventry
- Courses in Bradford
- Courses in Cardiff
- Courses in Belfast
- Courses in Nottingham