- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Boost Customer Satisfaction: Join us 1 Day Training in Bath
By Mangates
Customer Service Essentials 1 Day Training in Aberdeen

Delivered In-PersonIn-Person training program + more
£595 to £795
Building Better Careers with Soft Skills: 1-Day Workshop in Bath
By Mangates
10 Soft Skills You Need 1 Day Training in Bath

Delivered In-PersonIn-Person training program + more
£595 to £795
Change Management - Change Matters 1 Day Training in Bristol
By Mangates
Change Management - Change Matters 1 Day Training in Bristol

Delivered In-PersonIn-Person training program + more
£595 to £795
Change Management - Change Matters 1 Day Training in Bath
By Mangates
Change Management - Change Matters 1 Day Training in Bath

Delivered In-PersonIn-Person training program + more
£595 to £795
NPORS Excavator as a Crane (N100)
By Dynamic Training and Assessments Ltd
NPORS Excavator as a Crane (N100)

Delivered In-Person in Nottinghamshire or UK WideNottinghamshire or UK WideFlexible Dates
Price on Enquiry
Learn simple breathing and vocal techniques to reduce stress and anxiety in the body, boost the immune system, and build connections for general wellbeing. We play with sound, rhythm and improvisation, learn close vocal harmony arrangements of different genres, and have loads of fun! Come and enjoy the incredible benefits singing in a group has on mental and physical health, and be part of this wonderful growing community. Everyone is welcome!
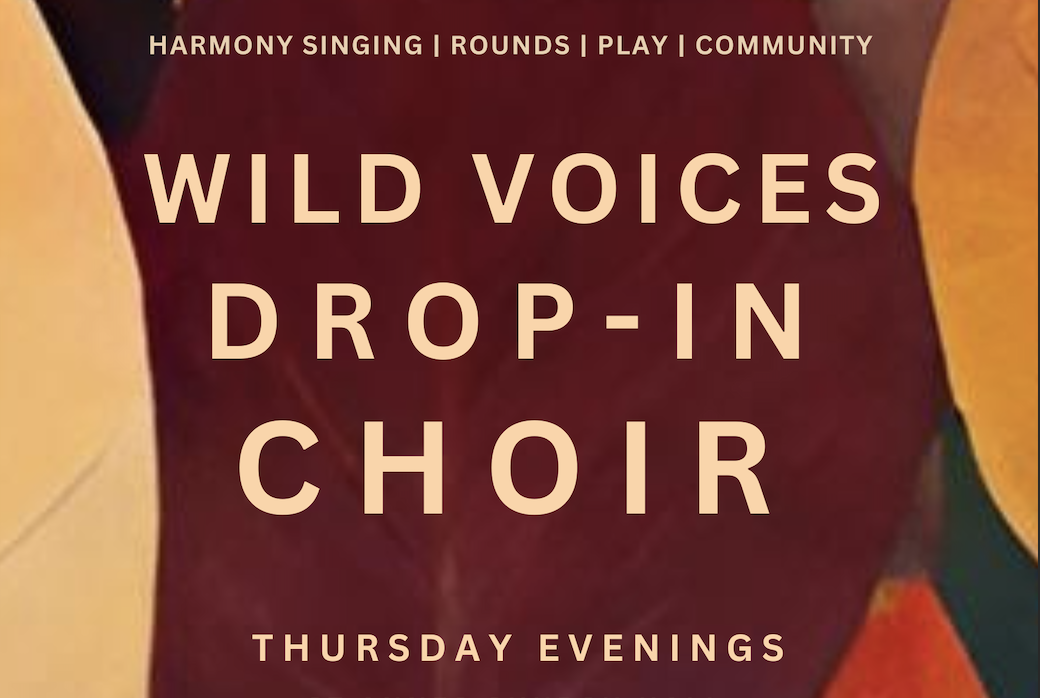
Delivered In-Person in BristolBristol + more
£8 to £10
Search By Location
- AS Courses in London
- AS Courses in Birmingham
- AS Courses in Glasgow
- AS Courses in Liverpool
- AS Courses in Bristol
- AS Courses in Manchester
- AS Courses in Sheffield
- AS Courses in Leeds
- AS Courses in Edinburgh
- AS Courses in Leicester
- AS Courses in Coventry
- AS Courses in Bradford
- AS Courses in Cardiff
- AS Courses in Belfast
- AS Courses in Nottingham

