- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1209 Courses in Bristol
4G training course description This course is designed to give the delegate an understanding of the technologies used within a 3G UMTS mobile network. During the course we will investigate the UMTS air interface and the use of Wideband-Code Division Multiple Access (WCDMA) to facilitate high speed data access, together with HSPA to offer mobile broadband services. We will describe the use of soft handover rather than hard handover procedures and soft capacity sharing. The course includes a brief exploration of the UMTS protocol stack and the use of PDP Context and QoS support features. What will you learn Explain the 3G UMTS architecture. Describe the role of a Drifting & Serving RNC. Explain the use of ARQ & HARQ for mobile broadband. Describe how IMS integrates into the architecture. Describe the use of Media Gateway Controllers. Identify the temporary identities used within 3G UMTS. 4G training course details Who will benefit: Anyone working within the telecommunications area, especially within the mobile environment. Prerequisites: Mobile communications demystified Telecommunications Introduction Duration 2 days 4G training course contents LTE Introduction The path to LTE, 3GPP. LTE to LTE advanced. LTE Architecture The core, Access, roaming. Protocols: User plane, Control plane. Example information flows. Bearer management. Spectrum allocation. LTE technologies Transmission, reception, OFDMA, multiple antenna, MIMO. LTE Air interface Air interface protocol stack. Channels, Resource Grid, cell acquisition. Up and downlink controls. Layer 2 protocols. Cell acquisition Power on, selecting networks and cells. RRC connection. Attach procedure. Mobility management Roaming, RRC_IDLE, RRC_CONNECTED, cell reselection, handover, interoperation with UMTS and GSM networks. Voice and text IMS, QoS, policy and charging.

Total QoS training course description An advanced technical hands on course focusing on Quality of Service issues in IP networks. What will you learn Explain the difference between Integrated services and differentiated services. Explain how DiffServ works. Explain how RSVP works. Design networks supporting QoS. Total QoS training course details Who will benefit: Network administrators. Network operators. Prerequisites: TCP/IP Foundation for engineers Duration 3 days Total QoS training course contents What is QoS QoS and CoS, throwing bandwidth at the problem, Best effort services, Differentiated services, Integrated services, guarantees, the need for QoS, IETF working groups. Application issues Video, Voice, other applications, Jitter, delay, packet loss. Flows, per flow and per aggregate QoS, Stateful vs. stateless QoS, applications vs. network QoS. 'Traditional' IP QoS The TOS field and precedence, the obsolete OSPF use of the TOS field, TCP congestion avoidance. Queuing Where to use queuing, FIFO, Priority queuing, Custom queuing, Weighted Fair Queuing, CBWFQ, PQWFQ, LLQ, RED and WRED. DiffServ Architecture, DSCP, CU, packet classification and marking, meters and conditioners, Bandwidth brokers and COPS, Per Hop Behaviours, best effort PHB, Assured Forwarding PHB, Expedited forwarding PHB, Network Based Application Recognition (NBAR). Layer 2 issues Fragmentation and interleaving, compression (codecs, MPEG formats, header compressionâ¦), 802.1p, Subnet bandwidth management, Bandwidth allocators and requestor modules, the use of MPLS, traffic engineering, traffic shaping. RSVP What is RSVP? architectures, paths, path messages, reservations, traffic specifications, tear downs, guaranteed and controlled load, token buckets, Call Admission Control in voice networks, gatekeepers. Other issues Policy based routing, the Resource Allocation Protocol, QoS management tools, baselining networks, design issues, QoS in IPv6, QoS and multicasts.

DWDM training course description A concise overview of Wave Division Multiplexing (WDM) with both Coarse Wave Division Multiplexing (CWDM) and Dense Wave Division Multiplexing (DWDM) being covered. The course starts with a review of the relevant elements of fibre transmission and multiplexing before then studying WDM components and architectures. Reliability, resilience and management are then followed by WDM services and futures. What will you learn Explain the benefits of WDM. Describe Dispersion and four way mixing. Describe the different WDM equipment components. Describe different WDM architectures. Explain How DWDM works. DWDM training course details Who will benefit: Anyone working with CWDM/DWDM. Prerequisites: Telecommunications Introduction Duration 2 days DWDM training course contents Fibre communications review Optical transmission, Fibre characteristics, Fibre component parts. Multi Mode Fibre (MMF). Single Mode Fibre (SMF). Fibre connections. Lasers. Attenuations, dispersion, optical signal noise ratios (OSNR) and their effects. Channel Spacing and Signal Direction. Limiting factors to single wavelength. WDM overview Multiplexing, TDM, WDM benefits. WDM standards. CWDM vs. DWDM. Four Wave Mixing (FWM). Impact and countermeasures to FWM on WDM. CWDM ITU G.694.2, channels, channel spacing. DWDM ITU G.694.1, channels, channel spacing. WDM Equipment Components Equipment components and building blocks. Optical Terminal Multiplexers (OTM). Optical Add/Drop Multiplexers (OADM). Adding versus dropping. Optical Amplifiers. Erbium Doped Fibre Amplifiers (EDFA). Transponders and Combiners. WDM/DWDM Hubs. Optical and Electrical Cross Connects (OXCs/DXCs). Types of Cross Connects (Transparent/Opaque). Advantages and disadvantages of various Optical cross connects. WDM Architectures WDM network sections. Point-to-Point, Optical switches, mesh, ring and star topology. Example of combined WDM and other technology network. Wavelength converting transponders, 1R, 2R, 3R. Protection for WDM Sub 50ms failover. Equipment protection. Card protection. Y cable, Splitter protection. Far end laser control. Line protection. OMSP 1+1, OMSP 1:1, OMSP 1: N. Self healing optical ring. Sub Network Connection Protection (SNCP). Automatically Switched Optical Networks (ASON). WDM Management Options In band management. Out of band management. The Optical Supervisory Channel (OSC). OSC capabilities. WDM services WDM Access. Bit rates, Transparent Networks. Modulation, DQPSK. SDH over WDM. Migrating from SDH to DWDM. Ethernet over WDM, IP over WDM. Optical Transport Networks G.709, 'digital wrapper', Optical Channel Payload Unit (OPU), Optical Channel Transport Unit ( OTU), Optical Channel Data Unit (ODU). OTU1, OTU2, OTU3, OTU4. WDM Futures All optical amplification, Raman amplification, distributed, lumped. Bit rates. Solitons. Coherent technologies.

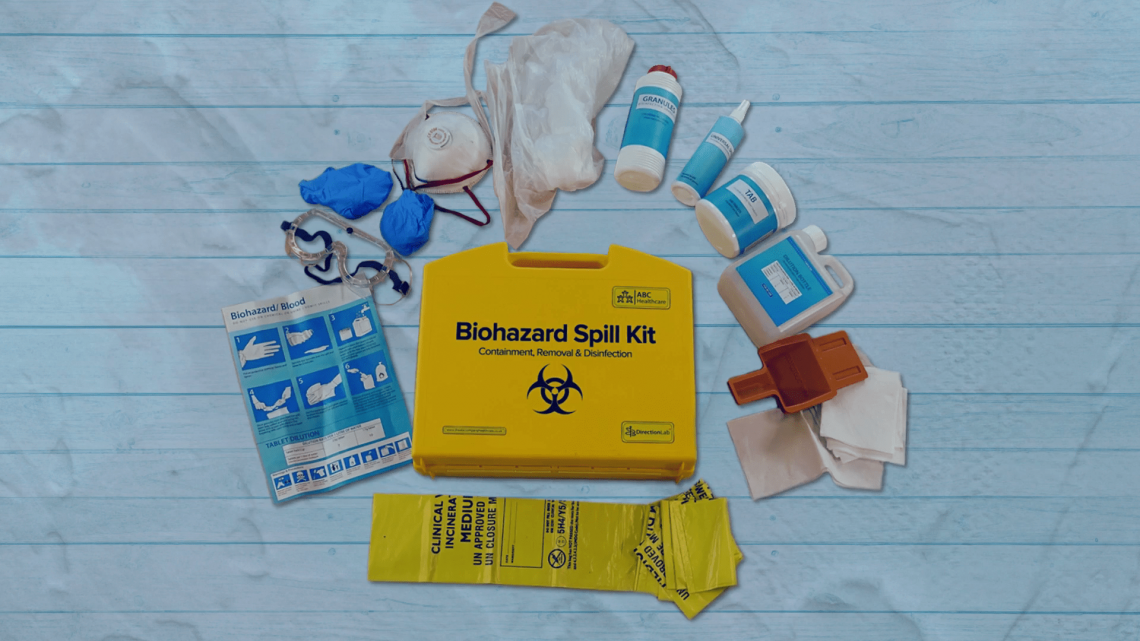
Biohazard Safety: Managing Blood and Body Fluid Spillages Instructor
By Guardian Angels Training
Gain expertise in biohazard safety with our "Biohazard Safety: Managing Blood and Body Fluid Spillages Instructor Training" course. Ideal for healthcare professionals, lab staff, and emergency responders.
Peripheral Intravenous Cannulation (Peripheral vascular access device)
By Guardian Angels Training
Gain the knowledge and skills to safely insert and manage peripheral IV cannulas with our training course for healthcare professionals. Ideal for nurses, medical personnel, and other practitioners.

The Level 3 International Foundation Diploma for Higher Education Studies (L3IFDHES) is usually a one-year pre-university qualification that provides students with an entry route to an overseas university. The L3IFDHES prepares students with the essential English language skills, key transferable study skills, cultural knowledge, and chosen specialisms that universities feel bridges the gap between high school and undergraduate study. In January 2023 we offer pathways in business and higher finance. With agreements in place with over 70 universities across the globe, students’ can progress with confidence to a higher education course for further study. Entry Requirements For entry onto the NCC Education Level 3 International Foundation Diploma for Higher Education Studies (L3IFDHES) qualification students must have successfully completed secondary school education. Students must also meet the English language entry requirements of: • IELTS minimum score of 4.5 or above OR • GCE ‘O’ Level English D7 or above Alternatively, a student can take the free NCC Education Higher English Placement Test which is administered by our Accredited Partner Centre’s.

Leading SAFe: In-House Training
By IIL Europe Ltd
Leading SAFe®: In-House Training During this course, attendees gain the knowledge necessary to lead a Lean-Agile enterprise by using the Scaled Agile Framework® (SAFe®) and its underlying principles derived from Lean, systems thinking, Agile development, product development flow, and DevOps. Participants in the class gain insights into mastering business agility to thrive in competitive markets. They discuss how to establish team and technical agility and organize and re-organize around the flow of value. Attendees also learn and practice the skills to support and execute PI Planning events and coordinate multiple Agile Release Trains (ARTs). Class participants will explore the importance of adopting a customer-centric mindset and Design-Thinking approach to Agile Product Delivery. Learners will also understand how to implement a Lean Portfolio Management function within their enterprise. What you will Learn After attending this class, attendees should be able to: Lead the transformation to business agility with SAFe® Become a Lean-Agile leader Understand customer needs Design Thinking Enable Agile Product delivery Implement Lean Portfolio Management Thrive in the digital age with business agility Become a Lean-Agile leader Establish Team and Technical Agility Build solutions with Agile Product Delivery Explore Lean Portfolio Management Lead the change Become a Certified SAFe® Agilist

NETCONF and YANG training course description An introduction to NETCONF and YANG. The course progresses from what they are, why they are needed, and how to configure them onto a more detailed analysis of how NETCONF works and how to read YANG models. What will you learn Recognise the limits and problems of SNMP and the CLI. Describe the relationship between NETCONF and YANG. Configure NETCONF on network devices. Use NETCONF to configure devices. Read YANG models. NETCONF and YANG training course details Who will benefit: Network engineers. Prerequisites: Network management technologies Duration 1 day NETCONF and YANG training course content What are NETCONF and YANG? Network management and configuration issues. What is NETCONF? What is YANG? Protocols, data models, architecture. Hands on Configuring NETCONF on network devices, using NETCONF. NETCONF NETCONF layers, Secure transport: SSH, Messages: rpc, Operations, Content. Base operations: <get>, <get-config>, <edit-config>, <copy-config>, <delete-config>, <lock>,<unlock>, <close-session>, <kill-session> NETCONF datastores: :candidate, :startup, running. Hands on Retrieving a configuration with NETCONF, Editing a configuration with NETCONF. NETCONF more details NETCONF traffic flows, NETCONF capabilities, hello, capabilities exchange., Filtering data, atomic transactions, validating configurations. Hands on Using NETCONF. YANG YANG models, IETF standard YANG models, tree diagrams, an example: YANG interface management, Module header, Imports and includes, Containers, Lists, leaves, Data types, typedef, Instance data, XML. Hands on Reading YANG data models, creating a configuration instance.

Conflict Resolution Skills: In-House Training
By IIL Europe Ltd
Conflict Resolution Skills: In-House Training Many organizations have assumed that workplace conflict is always destructive. So, they have often believed that conflict is best dealt with by managers or even via policies and procedures. After all, conflict creates workplace stress and leads to many performance problems, generating very real organizational costs! However, savvy organizations have embraced the fact that when conflict is understood and harnessed, it can be leveraged to add value to teams and even enhance performance. With the right knowledge, skills, training, and practice, conflict can be productive and make organizations better! In this highly interactive course, learners will discover the connection between individual conflict response and team-empowering conflict resolution skills. Participants will explore conflict's visceral dynamics and the nuanced behaviors we individually engage in to communicate and respond to conflict. Learners will apply techniques for transforming unproductive conflict responses into productive ones. Additionally, learners will use a systematic method that prepares them to objectively dissect real-world conflict, while practicing many strategies for resolving it. They will also develop proactive conflict approach plans, which they can transfer back to their own workplaces. What you will Learn At the end of this program, you will be able to: Recognize the organizational costs of conflict Explain our physical and mental responses to conflict Communicate proactively and effectively with different types of people during conflict Replace unproductive conflict responses with productive ones Use the Conflict Resolution Diagram (CRD) process and conflict resolution approaches Relate team stages of development to shifts in conflict Develop a proactive conflict approach for your organization Create a conflict resolution plan for a real-world scenario Getting Started Introductions and social agreements Course goal and objectives Opening activities Conflict Facilitation Readiness Conflict responses and perceptions Conflict basics Conflict and organizations Dynamics of conflict Conflict Styles and Communication A look at the color energies model Conflict through the color energies and DiSC® lens Communication with opposite color energies Individual Response to Conflict The anatomy of conflict Recognizing unproductive conflict responses 4 steps to productive conflict Choosing productive conflict responses Team Performance and Conflict High-performing team relationships Conflict and project team performance Conflict Resolution Diagram (CRD) and process Conflict Facilitation - Preparation Recognizing context and stakeholder needs Using team conflict resolution approaches Preparing for Crucial Conversations® Conflict Facilitation - Clarity Exposing assumptions and biases Defining the conflict and using the CRD Conflict Facilitation - Action Proactive conflict management Conflict facilitation practice Summary and Next Steps Review Personal action plans

Search By Location
- Management Courses in London
- Management Courses in Birmingham
- Management Courses in Glasgow
- Management Courses in Liverpool
- Management Courses in Bristol
- Management Courses in Manchester
- Management Courses in Sheffield
- Management Courses in Leeds
- Management Courses in Edinburgh
- Management Courses in Leicester
- Management Courses in Coventry
- Management Courses in Bradford
- Management Courses in Cardiff
- Management Courses in Belfast
- Management Courses in Nottingham