- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
715 ET courses in Cardiff delivered Live Online
BEHAVIORAL INTERVIEWING: BUILDING A CONSISTENT FRAMEWORK AND PROCESS
5.0(4)By Improving Communications Uk
LEARN ABOUT BEHAVIORAL VS. TRADITIONAL INTERVIEWING, AND HOW TO INCORPORATE AND DEVELOP INTERVIEWING SKILLS TO ENSURE THAT YOU FIND THE RIGHT CANDIDATE FOR THE JOB. Behavioral Interviewing means asking candidates questions that will help you to discover how the interviewee acted in specific employment-related situations. Because past performance is a good indicator of how someone will act in the future, this style of interviewing is extremely useful, and the method of choice for recruiting teams. In this session, you will learn about behavioral vs. traditional interviewing, and how you can incorporate and develop your interviewing skills to ensure that you have the right candidate for the job. OBJECTIVES Participants will be able to: Build a consistent framework and process to ensure an unbiased candidate experience; Choose job specifications and determine how success will be measured (skills); Identify characteristics and qualities that will support the required skills; Prepare questions to elicit descriptions of behaviors, attitudes, and skills necessary for the job; Review legal and appropriate interviewing etiquette/guidelines, including social media research; Screen candidates, using resumes and phone interviews; and Conduct successful role-play Behavioral Interviews in class. CLASSES WILL INCLUDE: Workbooks for future reference and study. Workshop / role play with actual interview scenarios to assist in internalizing data. Time for individual questions and concerns to aid in personalizing tactics. Online Format—Behavioral Interviewing is a 4-hour interactive online class for up to six people. Register for this class and you will be sent ONLINE login instructions prior to the class date. Rich has an engaging presentation style. The New Mexico chapter of the International Society for Performance Improvement (NMISPI) gave high marks to his interactive and lively Improving Customer Service workshop. There were opportunities to share ideas and analyze different techniques, and 87% of attendees said that they would recommend this workshop to others. Ildiko OraveczNew Mexico International Society for Performance Improvement
IT System Support Course
By Hi-Tech Training
The IT System Support Technician (Online Virtual Classroom) Course will equip candidates with the skills and knowledge to competently carry out routine customer support to a range of Computer users, communicate effectively with support managers, supporting colleagues and external clients.

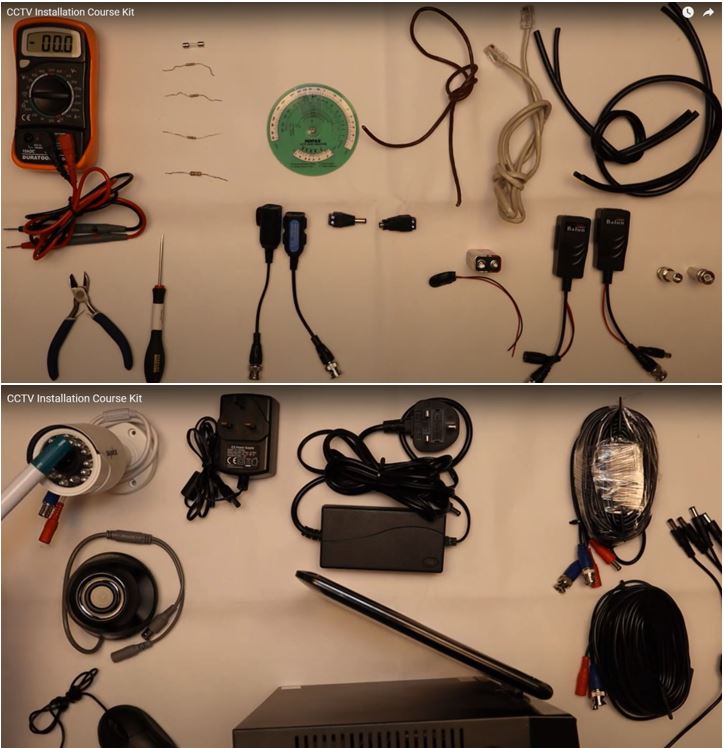
CCTV Installation Course
By Hi-Tech Training
Hi-Tech Training Closed Circuit Television (CCTV) Installation Course is designed to give participants a practical knowledge of the operation and installation of CCTV systems at a foundation level.
Alarm Installation Course
By Hi-Tech Training
The Alarm Installation Course is designed to teach participants how to install an intruder alarm system in domestic, commercial or industrial premises. The Alarm Installation Course simulates the practical installation of many different alarm control panels. The course is designed to equip students with the skills and expertise to competently install a wide variety of Alarm systems on the market.

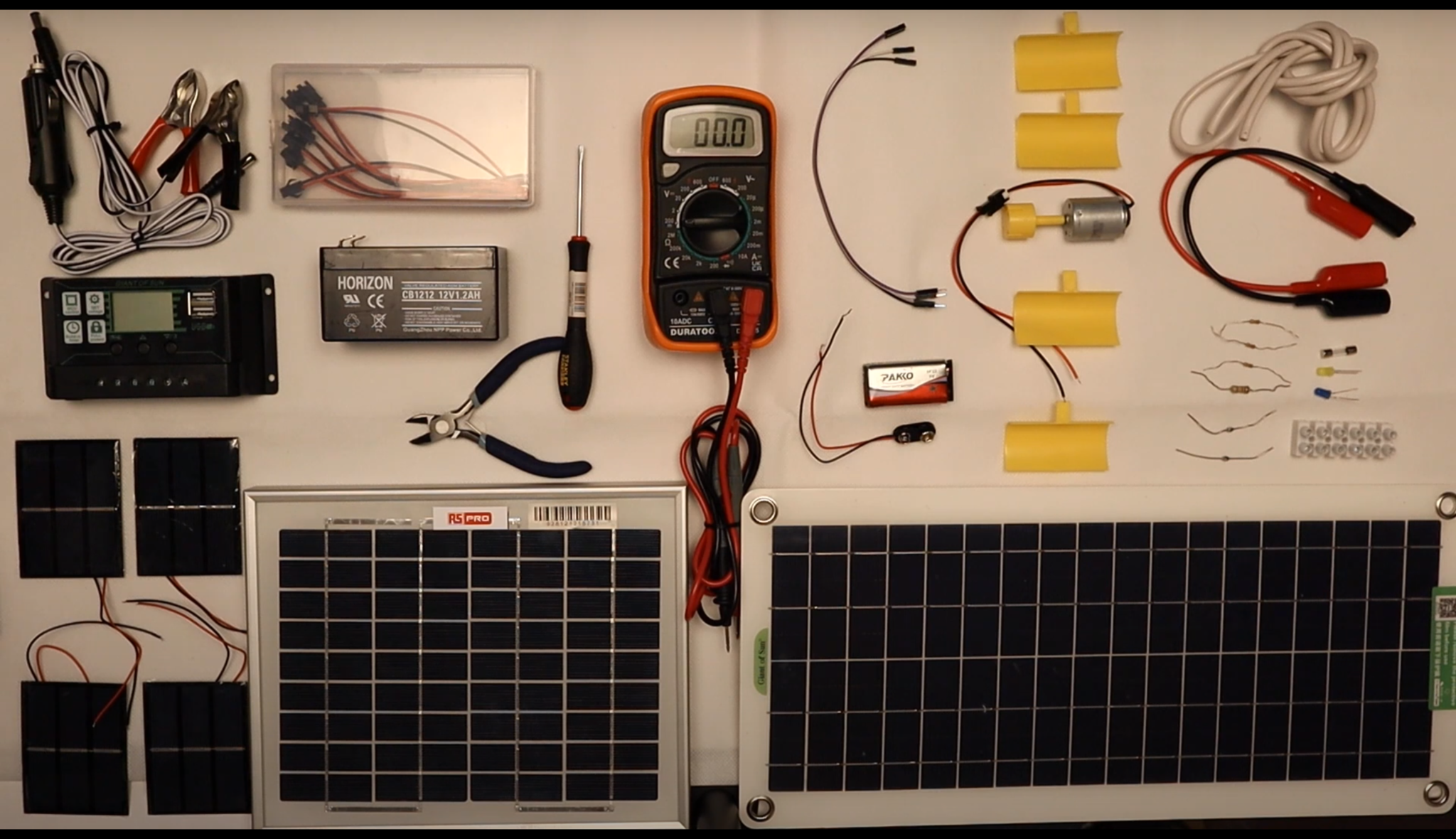
Alternative Energy Technology Course
By Hi-Tech Training
The Alternative Energy Technology Course is a practically based alternative energy course designed to give participants an understanding of alternative energy options and provide them with that practical knowledge and skills to build solar to electric and wind to electric systems at a foundation level. The course is designed to be of benefit to people either working or intending to work as:- Alternative Energy Installers or anyone just wishing to gain practical knowledge of Practical Alternative Energy Systems
Data Protection & Cyber Security Course: Remaining Compliant Against Today's Risks
By DG Legal
The professional working world has changed more rapidly than could have been envisaged at the time of the introduction of GDPR and the Data Protection Act 2018. With more people working from home post-Covid and the ever increasing risk of cyber-attacks, this short course is aimed at taking stock of current practice and risk, as well as considering ICO enforcement action and the implications of hybrid working. It is also a great recap on the rules as they stand and what you need to know to comply. The course will cover: UK GDPR - A timely reminder of the rules ICO enforcement action and what we can learn Data Protection Impact Assessments - when and how to do them Hybrid working and UK GDPR Managing cyber attacks from a UK GDPR perspective Target Audience The online course is suitable for staff of all levels, from support staff to senior partners. Resources Course notes will be provided to all delegates which may be useful for ongoing reference or cascade training. Please note a recording of the course will not be made available. Speaker Matthew Howgate, Consultant, DG Legal Matt is a non-practising solicitor who has considerable experience in regulatory issues and advising on complex issues of compliance and ethics. He is also an expert in data protection, UK GDPR and on the civil legal aid scheme. Matthew is a lead trainer on and co-developed the LAPG Certificate in Practice Management (a training programme for legal managers and law firm owners) as well as regularly providing training on legal aid Supervision, costs maximisation, data protection and security and on general SRA compliance.

MEF Carrier Ethernet training course description The course progresses from a overview of the Carrier Ethernet service and how it works onto looking at the concepts in depth. Service attributes and management follow with the course finishing with studies of practical Carrier Ethernet. What will you learn Discuss and understand key Carrier Ethernet Concepts. Understand tasks related to designing, deploying and maintaining a Carrier Ethernet network. Offer effective solutions to implementing a Carrier Ethernet enterprise network given available customer resources and requirements. Carry out informed discussions using industry Carrier Ethernet 'vocabulary. Pass the MEF CECP 2.0 professional accreditation exam. MEF Carrier Ethernet training course details Who will benefit: Anyone working with Carrier Ethernet Prerequisites: The course attendees need to be conversant with data networks, as well as Ethernet and IP technologies. Duration 5 days MEF Carrier Ethernet training course contents Section One: Introduction to Carrier Ethernet Introduction to Carrier Ethernet: What is Carrier Ethernet? Evolution, advantages, The MEF, MEF specifications; UNI, EVC, OVC, EPL/EVPL, EP-LAN/ EVP-LAN, EP-Tree/EVP-Tree, etc, overview. How Carrier Ethernet Works: Service Frame Handling. Carrier Ethernet at Customer Premises, metro and core. Carrier Ethernet Workings, UNI attributes, Service Attributes (EVC and EVC per UNI attributes), Bandwidth Profiles, service multiplexing, L2 protocol processing; Carrier Ethernet equipment, CPE, aggregation and homing nodes, core equipment; management systems. The Setting Up of a Carrier Ethernet Service: Step 1: Choose service type, EPL/EVPL, EP-LAN/EVP-LAN, EPTree/EVP-Tree, EVLine...; Step 2: CPE tasks, UNI-C tasks (UNI attributes, service attributes (EVC and EVC per UNI) and bandwidth profiles), UNI-N tasks (L2 protocol handling). Step 3: Non-CPE tasks, Access, metro and core connections set up. Section Two: Carrier Ethernet Concepts in depth Carrier Ethernet Definitions in Depth: UNI, UNI I & II, UNI-N and UNI-C, etc.; NNI/ENNI; EVC; OVC, OVC type (P2P, M2M, Rooted MP), OVC end point (root, leaf, trunk), OVC end point map, OVC end point bundling; Service types in detail, EPL/EVPL, EP-LAN/EVP-LAN, EP-Tree/EVP-Tree, EVLine, Access EPL, Access EVPL . Carrier Ethernet Service Frame Handling: Unicast, multicast and broadcast frame delivery, Tagged, untagged and priority; Tagging, C and S-Tags, 802.3, 802.1d, 802.1q, 802.1ad, 802.1ah evolution, VLAN ID translation/preservation. CoS preservation. Other Key Carrier Ethernet Concepts: MTU, MTU at UNI, MTU at ENNI; Physical Layer Attributes, FE, GbE and 10GbE, Service Multiplexing and Bundling Concept and detail, rules and implications; Hairpin Switching Managing Bandwidth in a Carrier Ethernet Network: Token Bucket Algorithm, EIR, CIR, CBS, EBS, Coupling Flag; Frame Colors, recoloring, Color Awareness attribute, Color Forwarding; Bandwidth Profiles, rules and concepts. MEF CoS identifiers, DEI bit (in S-Tag), PCP bit (in C-Tag or S-Tag), or DSCP (in IP header), Multiflow bandwidth concepts; CoS Label/Color Identification. Section Three: Carrier Ethernet Service Attributes Overview: Carrier Ethernet 2.0; Blueprint C Service Attributes: Per UNI, Physical interfaces, Frame format, Ingress/egress Bandwidth Profiles, CEVLAN ID/EVC Map, UNI protection. EVC per UNI, Ingress/egress Bandwidth Profiles, etc.; Per EVC, CEVLAN ID Preservation, CoS ID Preservation, Relationship between SLA and SLP, Class of Service, etc. OVC, ENNI, OVC End Point per UNI and OVC End Point per ENNI, Ingress/egress bandwidth profiles, etc. Section Four: Managing Carrier Ethernet Networks Overview: MEF Service Lifecycle.Carrier Ethernet maintenance: Port, Link & NE failure, Service Protection Technologies, Fault Identification and Recovery, LAG, Active/Standby EVC, Single EVC with transport protection, G.8031, G.8032, MPLS FRR. SOAMs: Connectivity fault management, connectivity Monitoring, Loopback, Linktrace; Performance Management, Frame Delay, Inter Frame Delay Variation, Availability, Frame Loss Ratio, Resiliency, HLI, DMM, DMR, SLM, SLR; Key Concepts, Single vs dual ended, ordered UNI pair calculations. LOAMs: Link discovery, link monitoring, etc. Terminology and Concepts: MEG levels, MIPs. Section Five: Practical Carrier Ethernet Carrier Ethernet Transport Technologies:Layer 1: SDH. Layer 2: Bridging, provider bridging, PBB, PBBTE. Layer 2.5: MPLS VPWS, MPLS VPLS, MPLS-TP. Carrier Ethernet Access Technologies: fiber, SDH, active fiber, PON, GPON, 10G PON, OTN, WDM; copper, PDH, G-SDSL, 10Pass-TS, HFC; packet radio. Optimising mobile backhaul with Carrier Ethernet Key challenges solutions: Market pressure, LTE evolution, elements and architecture (RAN BS, NC, GWIF.), synchronization, bandwidth management. Circuit Emulation over Ethernet: Purpose, needs and applications. Synchronization: Phased, ToD, External Reference source, SynchE ,NTP, IEEE-1588 v2/ PTP, ACR; MEF Service Definitions for emulated circuits. Applying what you know: Practical examples and scenarios, Carrier Ethernet solutions; Practice Scenarios, Given a scenario, determine appropriate Ethernet services

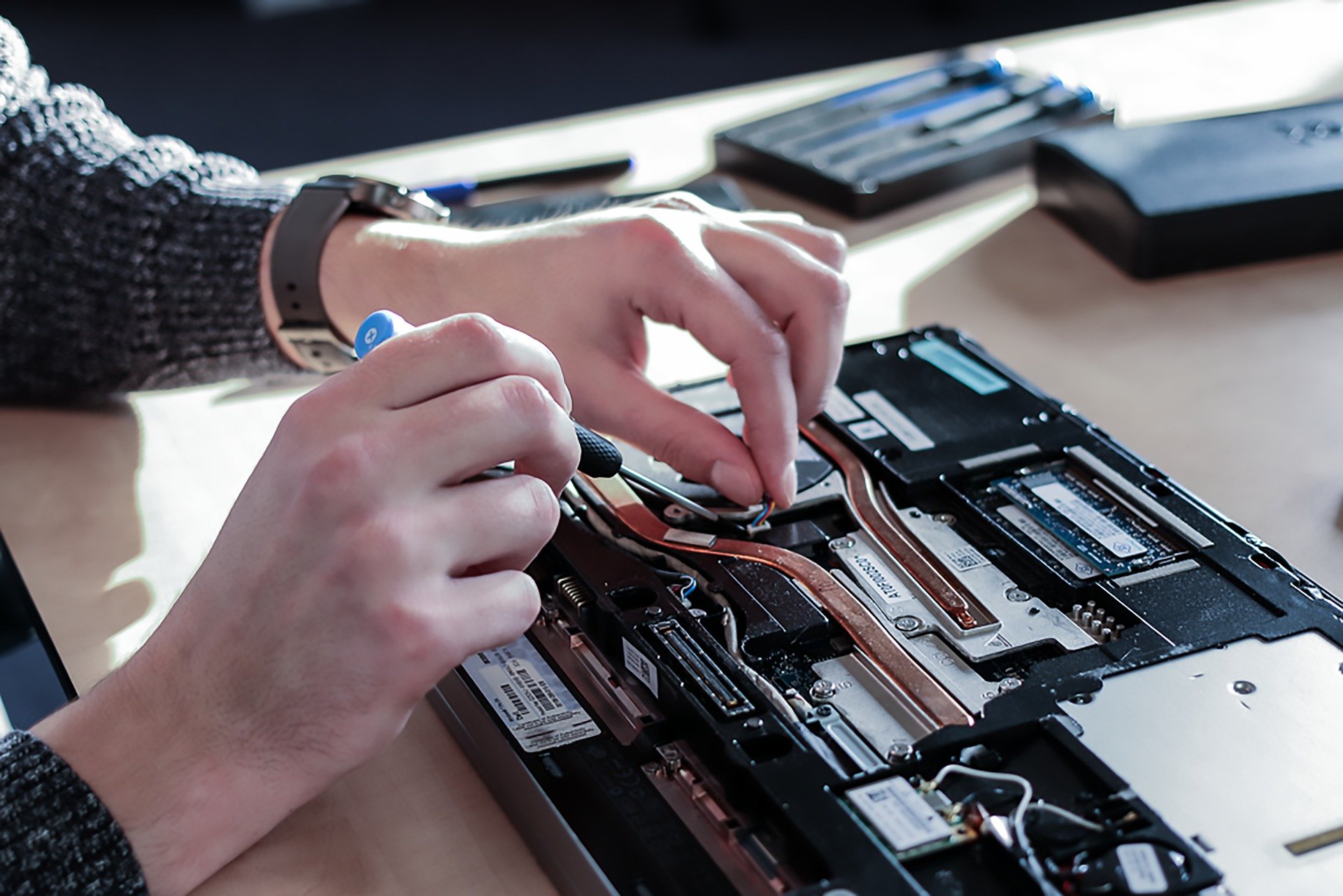
Computer Maintenance and Repair Course
By Hi-Tech Training
The Computer Maintenance & Repair Technician course aims to enable participants to diagnose and repair system level faults in computer-based systems at the foundation level.
Reiki Level 2 Practitioner Online Course
By Margaret Cook - Learn More About Reiki
I am a Reiki Teacher in Manchester and one of the few traditionally trained Reiki Masters in the UK who have been trained by international best-selling Reiki author Penelope Quest. My teaching methods use traditional Reiki techniques perfected over many years and you can be assured of my support during and after your course. I teach all three levels of Reiki courses, level 1 reiki. level 2 reiki and reiki master level 3

EC-Council Certified Ethical Hacker (CEH) v12
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The Certified Ethical Hacking v12 course will significantly benefit security officers, auditors, security professionals, site administrators, and anyone who is concerned about the integrity of the network infrastructure. Overview Information security controls, laws, and standards. Various types of footprinting, footprinting tools, and countermeasures. Network scanning techniques and scanning countermeasures Enumeration techniques and enumeration countermeasures Vulnerability analysis to identify security loopholes in the target organization?s network, communication infrastructure, and end systems. System hacking methodology, steganography, steganalysis attacks, and covering tracks to discover system and network vulnerabilities. Different types of malware (Trojan, Virus, worms, etc.), system auditing for malware attacks, malware analysis, and countermeasures. Packet sniffing techniques to discover network vulnerabilities and countermeasures to defend against sniffing. Social engineering techniques and how to identify theft attacks to audit human-level vulnerabilities and social engineering countermeasures. DoS/DDoS attack techniques and tools to audit a target and DoS/DDoS countermeasures. Session hijacking techniques to discover network-level session management, authentication/authorization, and cryptographic weaknesses and countermeasures. Webserver attacks and a comprehensive attack methodology to audit vulnerabilities in webserver infrastructure, and countermeasures. Web application attacks, comprehensive web application hacking methodology to audit vulnerabilities in web applications, and countermeasures. SQL injection attack techniques, injection detection tools to detect SQL injection attempts, and countermeasures. Wireless encryption, wireless hacking methodology, wireless hacking tools, and Wi-Fi security tools. Mobile platform attack vector, android vulnerability exploitations, and mobile security guidelines and tools. Firewall, IDS and honeypot evasion techniques, evasion tools and techniques to audit a network perimeter for weaknesses, and countermeasures. Cloud computing concepts (Container technology, serverless computing), the working of various threats and attacks, and security techniques and tools. Penetration testing, security audit, vulnerability assessment, and penetration testing roadmap. Threats to IoT and OT platforms and defending IoT and OT devices. Cryptography ciphers, Public Key Infrastructure (PKI), cryptography attacks, and cryptanalysis tools. CEH provides an in-depth understanding of ethical hacking phases, various attack vectors, and preventative countermeasures. It will teach you how hackers think and act maliciously so you will be better positioned to setup your security infrastructure and defend against future attacks. An understanding of system weaknesses and vulnerabilities helps organizations strengthen their system security controls to minimize the risk of an incident. CEH was built to incorporate a hands-on environment and systematic process across each ethical hacking domain and methodology, giving you the opportunity to work towards proving the required knowledge and skills needed to achieve the CEH credential. You will be exposed to an entirely different posture toward the responsibilities and measures required to be secure. Now in its 12th version, CEH continues to evolve with the latest operating systems, tools, tactics, exploits, and technologies. 1 - Introduction to Ethical Hacking Information Security Overview Cyber Kill Chain Concepts Hacking Concepts Ethical Hacking Concepts Information Security Controls Information Security Laws and Standards 2 - 2 - Foot-printing and Reconnaissance Footprinting Concepts Footprinting through Search Engines Footprinting through Web Services Footprinting through Social Networking Sites Website Footprinting Email Footprinting Who is Footprinting DNS Footprinting Network Footprinting Footprinting through Social Engineering Footprinting Tools Footprinting Countermeasures 3 - Scanning Networks Network Scanning Concepts Scanning Tools Host Discovery Port and Service Discovery OS Discovery (Banner Grabbing/OS Fingerprinting) Scanning Beyond IDS and Firewall Draw Network Diagrams 4 - Enumeration Enumeration Concepts NetBIOS Enumeration SNMP Enumeration LDAP Enumeration NTP and NFS Enumeration SMTP and DNS Enumeration Other Enumeration Techniques Enumeration Countermeasures 5 - Vulnerability Analysis Vulnerability Assessment Concepts Vulnerability Classification and Assessment Types Vulnerability Assessment Solutions and Tools Vulnerability Assessment Reports 6 - System Hacking System Hacking Concepts Gaining Access Escalating Privileges Maintaining Access Clearing Logs 7 - Malware Threats Malware Concepts APT Concepts Trojan Concepts Virus and Worm Concepts Fileless Malware Concepts Malware Analysis Countermeasures Anti-Malware Software 8 - Sniffing Sniffing Concepts Sniffing Technique: MAC Attacks Sniffing Technique: DHCP Attacks Sniffing Technique: ARP Poisoning Sniffing Technique: Spoofing Attacks Sniffing Technique: DNS Poisoning Sniffing Tools Countermeasures Sniffing Detection Techniques 9 - Social Engineering Social Engineering Concepts Social Engineering Techniques Insider Threats Impersonation on Social Networking Sites Identity Theft Countermeasures 10 - Denial-of-Service DoS/DDoS Concepts DoS/DDoS Attack Techniques BotnetsDDoS Case Study DoS/DDoS Attack Tools Countermeasures DoS/DDoS Protection Tools 11 - Session Hijacking Session Hijacking Concepts Application Level Session Hijacking Network Level Session Hijacking Session Hijacking Tools Countermeasures 12 - Evading IDS, Firewalls, and Honeypots IDS, IPS, Firewall, and Honeypot Concepts IDS, IPS, Firewall, and Honeypot Solutions Evading IDS Evading Firewalls IDS/Firewall Evading Tools Detecting Honeypots IDS/Firewall Evasion Countermeasures 13 - Hacking Web Servers Web Server Concepts Web Server Attacks Web Server Attack Methodology Web Server Attack Tools Countermeasures Patch Management Web Server Security Tools 14 - Hacking Web Applications Web Application Concepts Web Application Threats Web Application Hacking Methodology Web API, Webhooks, and Web Shell Web Application Security 15 - SQL Injection SQL Injection Concepts Types of SQL Injection SQL Injection Methodology SQL Injection Tools Evasion Techniques Countermeasures 16 - Hacking Wireless Networks Wireless Concepts Wireless Encryption Wireless Threats Wireless Hacking Methodology Wireless Hacking Tools Bluetooth Hacking Countermeasures Wireless Security Tools 17 - Hacking Mobile Platforms Mobile Platform Attack Vectors Hacking Android OS Hacking iOS Mobile Device Management Mobile Security Guidelines and Tools 18 - IoT and OT Hacking IoT Hacking IoT Concepts IoT Attacks IoT Hacking Methodology IoT Hacking Tools Countermeasures OT Hacking OT Concepts OT Attacks OT Hacking Methodology OT Hacking Tools Countermeasures 19 - Cloud Computing Cloud Computing Concepts Container Technology Serverless Computing Cloud Computing Threats Cloud Hacking Cloud Security 20 - Cryptography Cryptography Concepts Encryption Algorithms Cryptography Tools Public Key Infrastructure (PKI) Email Encryption Disk Encryption Cryptanalysis Countermeasures Additional course details: Nexus Humans EC-Council Certified Ethical Hacker (CEH) v.12 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the EC-Council Certified Ethical Hacker (CEH) v.12 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
