- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
11258 Environment courses in Halesowen delivered Online
ICA Specialist Certificate in Financial Crime Risk in Global Banking and Markets
By International Compliance Association
ICA Specialist Certificate in Financial Crime Risk in Global Banking and Markets Gain an understanding of money laundering risks and vulnerabilities in capital markets by exploring the financial market product, customer risk and service risk typologies. The course will examine the specific financial crime risk factors involved in key customer types such as funds and exchanges. It compares the vulnerabilities of major financial markets products, such as derivatives and foreign exchange. You will also learn more about the importance of the CDD process in mitigating these risks. ICA Specialist Certificates, awarded in association with Alliance Manchester Business School, the University of Manchester, will help you quickly gain actionable knowledge to boost your confidence and credibility. Regulatory environment, risks and impacts on the world of corporate banking and financial markets Market abuse, fraud and manipulation, tax evasion, sanctions risk Risk exposure and specific customer typologies Financial markets products and their susceptibility to financial crime The CDD process

55232 Writing Analytical Queries for Business Intelligence
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is intended for information workers and data science professionals who seek to use database reporting and analysis tools such as Microsoft SQL Server Reporting Services, Excel, Power BI, R, SAS and other business intelligence tools, and wish to use TSQL queries to efficiently retrieve data sets from Microsoft SQL Server relational databases for use with these tools. Overview After completing this course, students will be able to: - Identify independent and dependent variables and measurement levels in their own analytical work scenarios. - Identify variables of interest in relational database tables. - Choose a data aggregation level and data set design appropriate for the intended analysis and tool. - Use TSQL SELECT queries to produce ready-to-use data sets for analysis in tools such as PowerBI, SQL Server Reporting Services, Excel, R, SAS, SPSS, and others. - Create stored procedures, views, and functions to modularize data retrieval code. This course is about writing TSQL queries for the purpose of database reporting, analysis, and business intelligence. 1 - INTRODUCTION TO TSQL FOR BUSINESS INTELLIGENCE Two Approaches to SQL Programming TSQL Data Retrieval in an Analytics / Business Intelligence Environment The Database Engine SQL Server Management Studio and the CarDeal Sample Database Identifying Variables in Tables SQL is a Declarative Language Introduction to the SELECT Query Lab 1: Introduction to TSQL for Business Intelligence 2 - TURNING TABLE COLUMNS INTO VARIABLES FOR ANALYSIS: SELECT LIST EXPRESSIONS, WHERE, AND ORDER BY Turning Columns into Variables for Analysis Column Expressions, Data Types, and Built-in Functions Column aliases Data type conversions Built-in Scalar Functions Table Aliases The WHERE clause ORDER BY Lab 1: Write queries 3 - COMBINING COLUMNS FROM MULTIPLE TABLES INTO A SINGLE DATASET: THE JOIN OPERATORS Primary Keys, Foreign Keys, and Joins Understanding Joins, Part 1: CROSS JOIN and the Full Cartesian Product Understanding Joins, Part 2: The INNER JOIN Understanding Joins, Part 3: The OUTER JOINS Understanding Joins, Part 4: Joining more than two tables Understanding Joins, Part 5: Combining INNER and OUTER JOINs Combining JOIN Operations with WHERE and ORDER BY Lab 1: Write SELECT queries 4 - CREATING AN APPROPRIATE AGGREGATION LEVEL USING GROUP BY Identifying required aggregation level and granularity Aggregate Functions GROUP BY HAVING Order of operations in SELECT queries Lab 1: Write queries 5 - SUBQUERIES, DERIVED TABLES AND COMMON TABLE EXPRESSIONS Non-correlated and correlated subqueries Derived tables Common table expressions Lab 1: Write queries 6 - ENCAPSULATING DATA RETRIEVAL LOGIC Views Table-valued functions Stored procedures Creating objects for read-access users Creating database accounts for analytical client tools Lab 1: Encapsulating Data Retrieval Logic 7 - GETTING YOUR DATASET TO THE CLIENT Connecting to SQL Server and Submitting Queries from Client Tools Connecting and running SELECT queries from: Excel PowerBI RStudio Exporting datasets to files using Results pane from SSMS The bcp utility The Import/Export Wizard Lab 1: Getting Your Dataset to the Client Additional course details: Nexus Humans 55232 Writing Analytical Queries for Business Intelligence training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the 55232 Writing Analytical Queries for Business Intelligence course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Dealing with Stress, Anxiety, Depression and Violence in the Workplace
By OnlineCoursesLearning.com
Managing Stress, Anxiety, Depression and Violence in the Workplace Forestalling actual injury in the working environment ought to be a critical worry for all businesses, yet any way to deal with laborer prosperity needs to factor in emotional wellness. Moreover, managers additionally should know that work environment viciousness is a moderately regular event across numerous ventures. In this course, you will figure out how to distinguish pressure, nervousness, gloom and viciousness in the working environment. Regarding Health and Safety law, you will find how to satisfy your legitimate commitments and backing representative prosperity. You Will Learn Why managers need to take mental misery and viciousness in the work environment genuinely The reasons for working environment stress, indications of stress and the side effects of burnout How and why bosses ought to recognize and uphold those enduring work environment stress How businesses can distinguish emotional wellness issues in the working environment and how they can best help those with psychological well-being issues and addictions How bosses can lessen the danger of working environment viciousness and backing casualties of savagery Advantages of Taking This Course On the off chance that you are a business, this course will help you meet your commitments under wellbeing and security law In the event that you are a specialist, this course will make you aware of the threats of work environment push and urge you to look for help if fundamental In the event that you work in a HR job, this course will help you work with chiefs to devise viable pressure the executives arrangements In the event that you are a chief, this course will help you better comprehend a typical issue - mental trouble - that influences a critical minority of your group In the event that you are keen on word related wellbeing and security, this course will furnish you with a complete outline of a few key dangers confronting present day laborers

Root Cause Analysis (RCA) is used to analyse the root causes of focus events with both positive and negative outcomes, but it is most commonly used for the analysis of failures and incidents. Causes for such events can be varied in nature, including design processes and techniques, organizational characteristics, human aspects and external events. RCA can be used for investigating the causes of non-conformances in quality (and other) management systems as well as for failure analysis, for example in maintenance or equipment testing.
Mental Health Skills For Managers
By Starling
Learn how to create a supportive and open environment for mental health and wellbeing at work, helping everyone thrive and perform at their best.
DevOps Foundation©
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for The target audience for the DevOps Foundation course includes Management, Operations, Developers, QA and Testing professionals such as: Individuals involved in IT development IT operations or IT service management. Individuals who require an understanding of DevOps principles. IT professionals working within, or about to enter, an Agile Service Design Environment The following IT roles: Automation Architects, Application Developers, Business Analysts, Business Managers, Business Stakeholders, Change Agents, Consultants, DevOps Consultants, DevOps Engineers, Infrastructure Architect, Integration Specialists, IT Directors, IT Managers, IT Operations, IT Team Leaders, Lean Coaches, Network Administrators, Operations Managers, Project Managers, Release Engineers, Software Developers, Software Tester/QA, System Administrators, Systems Engineers, System Integrators, Tool Providers. Overview The learning objectives for DevOps Foundation include an understanding of: DevOps objectives and vocabulary Benefits to the business and IT Principles and practices including Continuous Integration, Continuous Delivery, testing, security and the Three Ways DevOps relationship to Agile, Lean and ITSM Improved workflows, communication and feedback loops Automation practices including deployment pipelines and DevOps toolchains Scaling DevOps for the enterprise Critical success factors and key performance indicators Real-life examples and results The DevOps Foundation course provides a baseline understanding of key DevOps terminology to ensure everyone is talking the same language and highlights the benefits of DevOps to support organizational success. Learners will gain an understanding of DevOps, the cultural and professional movement that stresses communication, collaboration, integration, and automation to improve the flow of work between software developers and IT operations professionals. This course prepares you for the DevOps Foundation (DOFD) certification. Exploring DevOps Defining DevOps Why Does DevOps Matter? Core DevOps Principles The Three Ways The First Way The Theory of Constraints The Second Way The Third Way Chaos Engineering Learning Organizations Key DevOps Practices Continuous Testing, Integration, Delivery, Deployment Site Reliability & Resilience Engineering DevSecOps ChatOps Kanban Business and Technology Frameworks Agile ITSM Lean Safety Culture Learning Organizations Continuous Funding Culture, Behaviors & Operating Models Defining Culture Cultural Debt Behavioral Models Organizational maturity models Automation & Architecting DevOps Toolchains CI/CD Cloud, Containers, and Microservices AI and Machine Learning Automation DevOps Toolchains Measurement, Metrics, and Reporting The Importance of Measurement DevOps Metrics - Speed, Quality, Stability, Culture Change lead/cycle time Value Driven Metrics Sharing, Shadowing and Evolving DevOps in the Enterprise Roles DevOps Leadership Organizational Considerations Getting Started Challenges, Risks, and Critical Success Factors Additional course details: Nexus Humans DevOps Foundation (DevOps Institute) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the DevOps Foundation (DevOps Institute) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

55348 Administering Microsoft Endpoint Configuration Manager
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is for experienced information technology (IT) professionals, typically described as Enterprise Desktop Administrators (EDAs). These EDAs deploy, manage, and maintain PCs, devices, and applications across medium, large, and enterprise organizations. A significant portion of this audience uses, or intends to use, the latest release of Configuration Manager to manage and deploy PCs, devices, and applications. Overview Describe the features Configuration Manager and Intune include, and explain how you can use these features to manage PCs and mobile devices in an enterprise environment. Analyze data by using queries and reports. Prepare a management infrastructure, including configuring boundaries, boundary groups, and resource discovery, and integrating mobile-device management with Intune. Deploy and manage the Configuration Manager client. Configure, manage, and monitor hardware and software inventory, and use Asset Intelligence and software metering. Identify and configure the most appropriate method to distribute and manage content used for deployments. Distribute, deploy, and monitor applications for managed users and systems. Maintain software updates for PCs that Configuration Manager manages. Implement Endpoint Protection for managed PCs. Configure an operating-system deployment strategy by using Configuration Manager. Manage and maintain a Configuration Manager site. This five-day course describes how to use Configuration Manager and its associated site systems to efficiently manage network resources. In this five-day course, you will learn day-to-day management tasks, including how to manage applications, client health, hardware and software inventory, operating system deployment, and software updates by using Configuration Manager. You also will learn how to optimize Endpoint Protection, manage compliance, and create management queries and reports. Although this course and the associated labs are written for Microsoft Endpoint Configuration Manager and Windows 11, the skills taught will also be backwards compatible with previous editions of System Center Configuration Manager and Windows 10. Prerequisites Networking fundamentals, including common networking protocols, topologies, hardware, media, routing, switching, and addressing. Active Directory Domain Services (AD DS) principles and fundamentals of AD DS management. Installation, configuration, and troubleshooting for Windows-based personal computers. Basic concepts of public key infrastructure (PKI) security. Basic understanding of scripting and Windows PowerShell syntax. Basic understanding of Windows Server roles and services. Basic understanding of the configuration options for iOS and Android Mobile device platforms. 1 - Managing computers and mobile devices in the enterprise Overview of systems management by using enterprise management solutions Overview of the Configuration Manager architecture Overview of the Configuration Manager administrative tools Tools for monitoring and troubleshooting a Configuration Manager site 2 - Analyzing data using queries, reports, and CMPivot Introduction to queries Configuring SQL Server Reporting Services Analyzing the real-time state of a device by using CMPivot 3 - Preparing the Configuration Manager management infrastructure Configuring site boundaries and boundary groups Configuring resource discovery Organizing resources using device and user collections 4 - Deploying and managing the Configuration Manager client Overview of the Configuration Manager client Deploying the Configuration Manager client Configuring and monitoring client status Managing client settings and performing management operations 5 - Managing inventory for PCs and applications Overview of inventory collection Configuring hardware and software inventory Managing inventory collection Configuring software metering Configuring and managing Asset Intelligence 6 - Distributing and managing content used for deployments Preparing the infrastructure for content management Distributing and managing content on distribution points 7 - Deploying and managing applications Overview of application management Creating applications Deploying applications Managing applications Deploying and managing Windows apps 8 - Maintaining software updates for managed PCs The software updates process Preparing a Configuration Manager site for software updates Managing software updates Configuring automatic deployment rules Monitoring and troubleshooting software updates Enabling third-party updates 9 - Implementing Defender Protection for managed PCs Overview of Endpoint Protection in Configuration Manager Configuring, deploying, and monitoring Endpoint Protection policies Configuring and deploying advanced threat policies 10 - Managing compliance and secure data access Overview of Compliance Settings Configuring compliance settings Viewing compliance results Managing resource and data access 11 - Managing operating system deployment An overview of operating system deployment Preparing a site for operating system deployment Deploying an operating system Managing Windows as a service 12 - Managing and maintaining a Configuration Manager site Configuring role-based administration Configuring Remote Tools Overview of Configuration Manager site maintenance and Management Insights Backing up and recovering a Configuration Manager site Updating the Configuration Manager infrastructure 13 - What?s new in Microsoft Endpoint Configuration Manager Whats new in Microsoft Endpoint Manager covering each semi annual release Additional course details: Nexus Humans 55348: Administering Microsoft Endpoint Configuration Manager training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the 55348: Administering Microsoft Endpoint Configuration Manager course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Stress Management
By Mpi Learning - Professional Learning And Development Provider
Stress can affect your ability to think clearly and rationally and to perform well. This session aims to help you better deal with stress by sharing key insights and strategies to reduce stress and optimize your work-life balance, particularly as we face uncertainties in the economy, the workplace and the environment.

Microsoft Office 2013 Certification Bundle with 5 Exams
By Hudson
The Microsoft Office Specialist is a globally recognised qualification. Having a Microsoft Office Specialist certification on your CV demonstrates that you have gained the necessary expertise to competently use Microsoft applications, giving you a competitive advantage when job hunting as well as in the workplace. It will significantly increase your confidence, skills and employability. It will serve to objectively validate your IT skills and assist in your advancement in your chosen career.

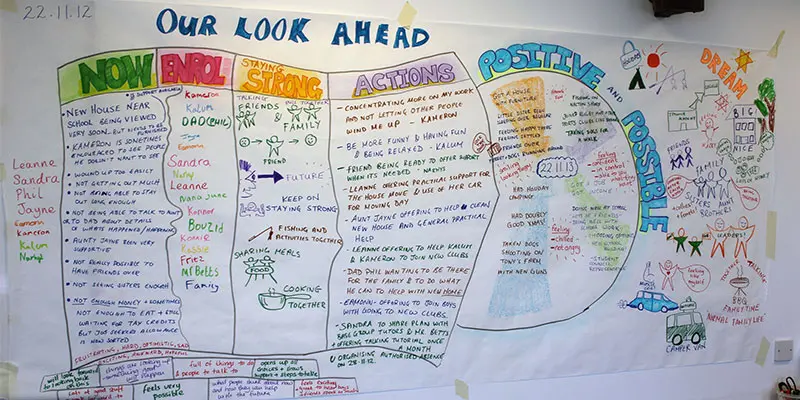
PERSON CENTRED THINKING – EXTREME
By Inclusive Solutions
The Extreme Person Centred Thinking Tools are a set of tools to support dreams, build relationships and connections and promote capacity thinking. The aim of the extreme person centred thinking tools training is not to teach people how to facilitate plans, instead it is about sharing tools that can be used to listen and reflect and creatively involve people in planning their own lives. Online Course now available via Teachable Platform – Person Centred Mindset Learn at your own pace… lots of text and video support Course Category Person Centred Planning Description The Extreme Person Centred Thinking Tools are a set of tools to support dreams, build relationships and connections and promote capacity thinking. The aim of the extreme person centred thinking tools training is not to teach people how to facilitate plans, instead it is about sharing tools that can be used to listen and reflect and creatively involve people in planning their own lives. Many of these tools have been taken from MAPS and PATH, and parts also build on the person centred thinking tools. Testimonials Be the first… Learning Objectives This course will provide participants with an understanding of how to use a range of extreme person centred thinking tools to; Use graphics to facilitate creative conversations Learn from people’s stories and histories Listen to and facilitate dreams and nightmares Think about what is positive and possible Connect people with their communities Facilitate inclusion Who Is It For? Person Centred Planning Facilitators Support Workers / Day Centre Officers / Residential Workers Personal Assistants / Teaching Assistants Families Self Advocates Social Workers CAMHS teams Primary and secondary staff teams SENCOs Local Authority Support Services Course Content The course will introduce participants to a range of tools focused around supporting relationships, realising dreams, connecting people with their communities and capacity thinking. Participants will be coached in using the tools and given the opportunity to practice the tools and their graphic facilitation skills in a safe environment. The course will answer the following questions: How can we use ideas from MAP and PATH in our day to day work? How can I use graphics to facilitate conversations? How can we learn more about the people we support? How can we start to think about connecting people to their communities? If you liked this course you may well like: PERSON CENTRED PLANNING USING PATH AND MAPS