- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Engineering courses in London
We couldn't find any listings for your search. Explore our online options and related educators below to see if they help you.
Know someone teaching this? Help them become an Educator on Cademy.
Online Options
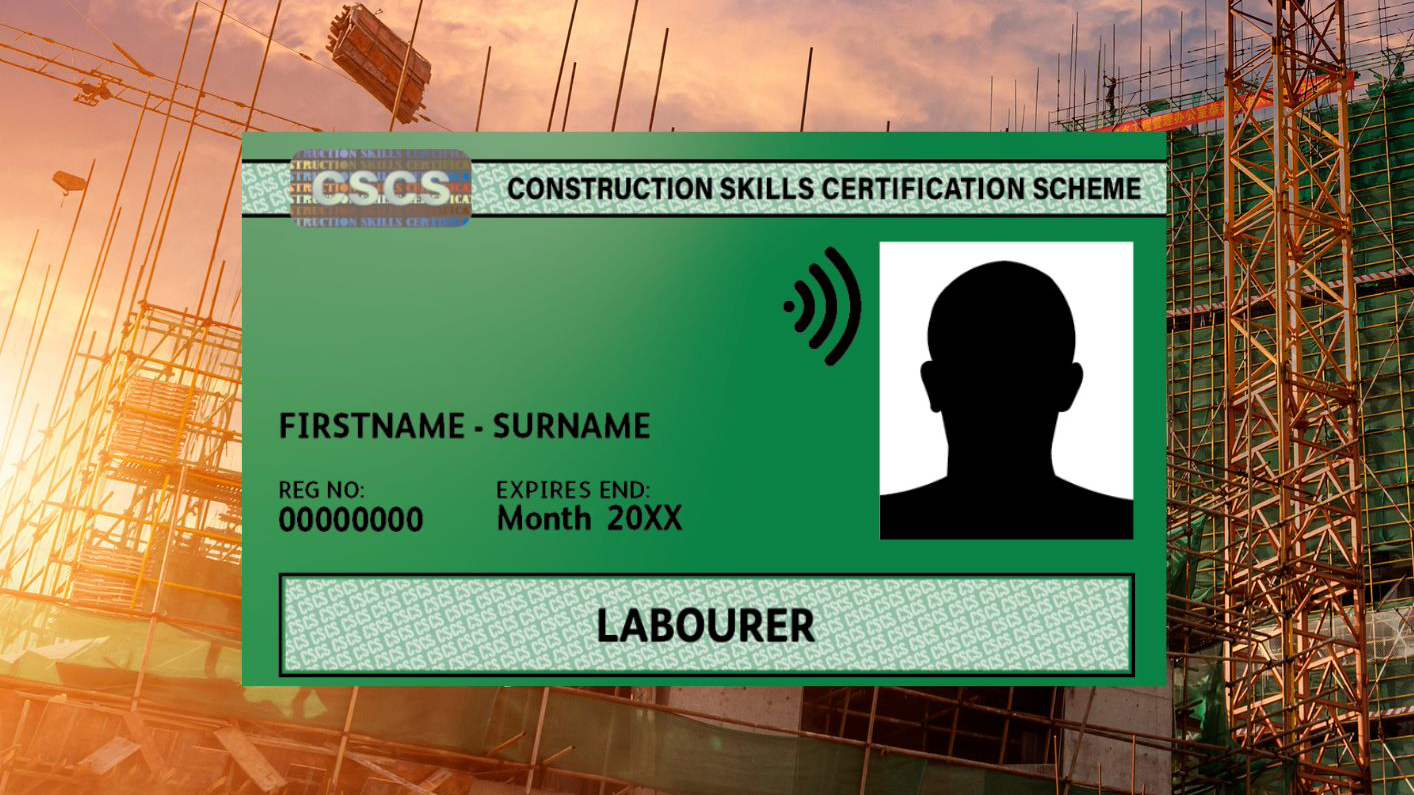
Show all 3203Health & Safety Awareness (for Green CSCS)
By SMC Safety Solutions
This one-day course is a must for anyone considering or already working within a construction or civil engineering environment. This course provides Health and Safety awareness and is endorsed by Build UK as a standard training for all operatives on site. Aims To give a clear understanding of Regulations & Legislation that applies to construction work and is an ideal refresher for any operative that has previously completed training in Health & Safety. Course Content • Accident prevention • Health & Safety law • Control and management of the site and your how your role fits in with this • Risk assessments and method statements • Performing safely on site • Reporting unsafe acts to prevent an accident • Individual & employee responsibilities • What to do if you think anyone’s Health and Safety is being put at risk Assessment At the end of this course, all delegates will have a clear understanding of the requirements of Health and Safety Legislation and their responsibilities to comply with them. Candidates will need to complete a multiple-choice exam at the end of the CITB course. They will also need to engage and interact with others throughout the day. Certificate This certification for this course is valid for 5 years and is endorsed by Build UK as a standard training for all operatives. The certificate is part of CSCS Green Card requirements. To remain certified in this area, you will need to retake the course before the expiry date or have completed an NVQ2 or higher in your skills set. Instructions Please note all Health & Safety Awareness courses with the venue “Remote Learning” will be delivered by a tutor over a video call. This training will be delivered and assessed in English language; therefore, a good standard is required to complete the course. Further attendee information will be sent in a separate email, please check your inbox.
2year Masters program with Experience certificate and Chartered Engineering status
By JP Jacobs International University
Mep Design Engineering

Site Management Safety Training Scheme (SMSTS) 5 day course
By SMC Safety Solutions
This five-day course is a must for anyone who is considering or already working in a role with site manager responsibilities. This course covers all relevant legislation affecting safe working in the building, construction, and civil engineering industries. It is endorsed by Build UK as the standard training for all construction managers. Aims To give a clear understanding of health, safety, welfare, and environmental legislation that affects your management role. It highlights the need for risk assessment in the workplace, the implementation of the necessary control measures and adequate communication to sustain a health and safety culture within the workforce. Course Content To give a clear understanding of health, safety, welfare, and environmental legislation that affects your management role. It highlights the need for risk assessment in the workplace, the implementation of the necessary control measures and adequate communication to sustain a health and safety culture within the workforce. Course Content • Health, safety, welfare and environmental legislation affecting your daily work • New guidance and industry best practice • Duties and responsibilities with regards to health, safety, welfare, and the environment • Safe working Prerequisites This course is for you if you’re considering, or already have management responsibilities for planning, organising, monitoring, controlling and administering groups of staff e.g. site manager. Assessment At the end of this course, all delegates will have a clear understanding of controlling health and safety on site from a manager’s role. Certificate The certification for this course is valid for 5 years and is endorsed by Build UK as a standard training for all site managers. To remain certified in this area, you will need to take a refresher course before the expiry date on your certificate, otherwise the full course will need to be retaken. Instructions Please note all online Site Management Safety Training Scheme courses with the venue “Online” will be delivered by a tutor over a video call. This training will be delivered and assessed in English language; therefore, a good standard is required to complete the course. Further attendee information will be sent in a separate email, please check your inbox.

We have an extensive range of PLC training courses available covering all PLC manufacturers and levels of expertise from the complete novice to the advanced. ALL of our training courses can be tailoured to your own requirements. ALL our courses will be based on the relevant software and hardware. We aim to make ALL our courses as practical as possible, leading to ‘real world’ skills and not just theoretical skills. No prior knowledge is required for this course as it starts from scratch and assumes no previous experience, you will reach the skilled level where you can look at becoming a programmer, get into engineering maintenance in an industrial environment, fault find or make amendments to programs, this is the course for you. The ‘Typical’ 10 day level 3 course usually covers 2 or 3 of the major manufacturers, Siemens S7, Allen Bradley and Mitsubishi (This can be amended to other manufacturers if you have a particular requirement). The course aims to be 90% practical, as we believe the easiest way to learn is to do it! Every student works on their own dedicated training rig and computer, enabling you to get the most from the course. A full set of course notes and a USB drive full of other manuals is provided at the end of the course. We can also cover a wide range of manufacturers including : Siemens Step 5 PLC Training (Using Step 5, Quadriga or Others) Allen Bradley PLC 3; 5 Training (AB6200 Software) RSLogix 5 PLC Training SLC PLC Training (RSLogix 500) ControlLogix PLC Training (RS Logix5000) MicroLogix PLC Training (RSLogix 500) S7-200 PLC Training (Step 7 Micro) S7-300 PLC Training (Step 7 or TIA Portal) S7-400 PLC Training (Step 7 or TIA Portal) Kuhnke PLC Training (Kubes) Omron PLC Training (Syswin) Modicon PLC Training (ProWorx and Others) Mitsubishi PLC Training (Medoc, GX Developer, GPP & Others) Toshiba PLC Training GE Fanuc PLC Training GEM 80 PLC Training Telemecanique PLC Training Most other PLC manufacturer training undertaken. We also cover a wide range of SCADA Systems to enable engineers to modify and add to existing screens, fault find through systems, set up communications etc.

We have an extensive range of PLC training courses available covering all PLC manufacturers and levels of expertise from the complete novice to the advanced. ALL of our training courses can be tailoured to your own requirements. ALL our courses will be based on the relevant software and hardware. We aim to make ALL our courses as practical as possible, leading to ‘real world’ skills and not just theoretical skills. No prior knowledge is required for this course as it starts from scratch and assumes no previous experience, you will reach the skilled level where you can look at becoming a programmer, get into engineering maintenance in an industrial environment, fault find or make amendments to programs, this is the course for you. The ‘Typical’ 5 day course usually covers 2 or 3 of the major manufacturers, Siemens S7, Allen Bradley and Mitsubishi (This can be amended to other manufacturers if you have a particular requirement). The course aims to be 90% practical, as we believe the easiest way to learn is to do it! Every student works on their own dedicated training rig and computer, enabling you to get the most from the course. A full set of course notes and a USB drive full of other manuals is provided at the end of the course. We can also cover a wide range of manufacturers including : Siemens Step 5 PLC Training (Using Step 5, Quadriga or Others) Allen Bradley PLC 3 & 5 Training (AB6200 Software) RSLogix 5 PLC Training SLC PLC Training (RSLogix 500) ControlLogix PLC Training (RS Logix5000) MicroLogix PLC Training (RSLogix 500) S7-200 PLC Training (Step 7 Micro) S7-300 PLC Training (Step 7 or TIA Portal) S7-400 PLC Training (Step 7 or TIA Portal) Kuhnke PLC Training (Kubes) Omron PLC Training (Syswin) Modicon PLC Training (ProWorx and Others) Mitsubishi PLC Training (Medoc, GX Developer, GPP & Others) Toshiba PLC Training GE Fanuc PLC Training GEM 80 PLC Training Telemecanique PLC Training Most other PLC manufacturer training undertaken. We also cover a wide range of SCADA Systems to enable engineers to modify and add to existing screens, fault find through systems, set up communications etc.

Mechanical Engineering, Engineering Management & Engineering Calculus
By Imperial Academy
Level 3 - Three QLS Endorsed Diploma | QLS Hard Copy Certificate Included | Plus 10 CPD Courses | Lifetime Access

Study flexibly online with NMA for a BSc (Hons) Motorsport Engineering and open the door to an exciting career in motorsport. Study around work and family and choose your own start date. This course will teach you the specialist skills required by this competitive global industry.

Construction Engineering, Architecture, Civil Engineering & Structural Engineering
4.7(47)By Academy for Health and Fitness
***24 Hour Limited Time Flash Sale*** Construction Engineering, Architecture, Civil Engineering & Structural Engineering Admission Gifts FREE PDF & Hard Copy Certificate| PDF Transcripts| FREE Student ID| Assessment| Lifetime Access| Enrolment Letter Are you a professional feeling stuck in your career, struggling to keep up with the ever-changing demands of the industry? Or perhaps you're a beginner, unsure of where to start or how to break into your desired field. Whichever stage you're in, our exclusive Construction Engineering, Architecture, Civil Engineering & Structural Engineering Bundle provides unique insights and tools that can help you achieve your goals. Designed to cater to the needs of both seasoned professionals and aspiring newcomers, our Construction Engineering, Architecture, Civil Engineering & Structural Engineering bundle is a comprehensive program that will equip you with the essential skills and knowledge you need to succeed. Whether you're looking to advance in your current role or embark on a new career journey, this bundle has everything you need to take your professional life to the next level. But that's not all. When you enrol in Construction Engineering, Architecture, Civil Engineering & Structural Engineering Online Training, you'll receive 30 CPD-Accredited PDF Certificates, Hard Copy Certificates, and our exclusive student ID card, all absolutely free. Courses Are Included In this Construction Engineering, Architecture, Civil Engineering & Structural Engineering Career Bundle: Course 01: Construction Management Course 02: LEED V4 - Building Design and Construction Course 03: Read Construction & Structural Drawing Like Expert Course 04: Construction Industry Scheme (CIS) Course 05: CDM - Construction Design and Management Course 06: Construction Site Management Course 07: Construction Project Management Course 08: Construction Cost Estimation Course 09: Architecture Course 10: Landscape Architecture Course 11: Revit Architecture Advanced Interior Design Training Course 12: Revit Architecture Advanced Exterior Design Course Course 13: WELL Building Standard Course 14: Civil Engineering Level 3 Course 15: Solidworks Foundation Training Course 16: CAD Design Course: Assemblies, Modelling And Civil Drawings Course 17: AutoCAD VBA Programming Course 18: AutoCAD Plugin Development Using VB.NET and Windows Forms Course 19: Autocad Electrical Design Course 20: Interior Design Professional Diploma Course 21: Bricklaying Course 22: Land Surveying Course 23: Building Surveyor Training Course 24: Quantity Surveyor Diploma Course 25: Property Law and Legislation Course 26: COSHH (Control of Substances Hazardous to Health) Training Course 27: Asbestos Awareness & Safety Course 28: Construction Site Safety Training Course 29: Fire Safety Training Course Course 30: Advanced Electrical Safety With Construction Engineering, Architecture, Civil Engineering & Structural Engineering, you'll embark on an immersive learning experience that combines interactive lessons with voice-over audio, ensuring that you can learn from anywhere in the world, at your own pace. And with 24/7 tutor support, you'll never feel alone in your journey, whether you're a seasoned professional or a beginner. Don't let this opportunity pass you by. Enrol in Construction Engineering, Architecture, Civil Engineering & Structural Engineering today and take the first step towards achieving your goals and dreams. Why buy this Construction Engineering, Architecture, Civil Engineering & Structural Engineering? Free CPD Accredited Certificate upon completion of Construction Engineering, Architecture, Civil Engineering & Structural Engineering Get a free student ID card with Construction Engineering, Architecture, Civil Engineering & Structural Engineering Lifetime access to the Construction Engineering, Architecture, Civil Engineering & Structural Engineering course materials Get instant access to this Construction Engineering, Architecture, Civil Engineering & Structural Engineering course Learn Construction Engineering, Architecture, Civil Engineering & Structural Engineering from anywhere in the world 24/7 tutor support with the Construction Engineering, Architecture, Civil Engineering & Structural Engineering course. Start your learning journey straightaway with our Construction Engineering, Architecture, Civil Engineering & Structural Engineering Training! Construction Engineering, Architecture, Civil Engineering & Structural Engineering premium bundle consists of 30 precisely chosen courses on a wide range of topics essential for anyone looking to excel in this field. Each segment of Construction Engineering, Architecture, Civil Engineering & Structural Engineering is meticulously designed to maximise learning and engagement, blending interactive content and audio-visual modules for a truly immersive experience. Certification You have to complete the assignment given at the end of the Construction Engineering, Architecture, Civil Engineering & Structural Engineering course. After passing the Construction Engineering, Architecture, Civil Engineering & Structural Engineering exam You will be entitled to claim a PDF & Hardcopy certificate accredited by CPD Quality standards completely free. CPD 300 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This Construction Engineering, Architecture, Civil Engineering & Structural Engineering course is ideal for: Students seeking mastery in Construction Engineering, Architecture, Civil Engineering & Structural Engineering Professionals seeking to enhance Construction Engineering, Architecture, Civil Engineering & Structural Engineering skills Individuals looking for a Construction Engineering, Architecture, Civil Engineering & Structural Engineering-related career. Anyone passionate about Construction Engineering, Architecture, Civil Engineering & Structural Engineering Requirements This Construction Engineering, Architecture, Civil Engineering & Structural Engineering doesn't require prior experience and is suitable for diverse learners. Career path This Construction Engineering, Architecture, Civil Engineering & Structural Engineering bundle will allow you to kickstart or take your career in the related sector to the next stage. Certificates CPD Accredited Digital certificate Digital certificate - Included CPD Accredited Hard copy certificate Hard copy certificate - Included If you are an international student, then you have to pay an additional 10 GBP for each certificate as an international delivery charge.

Engineering Management: Electrical Engineering & Mechanical Engineering - CPD Certified
4.8(9)By Skill Up
25 Courses Diploma | CPD Certified | 250 CPD Points | Free PDF & Transcript Certificate | Lifetime Access

Do you want to prepare for your dream job but strive hard to find the right courses? Then, stop worrying, for our strategically modified Engineering Management for Electrical Technician bundle will keep you up to date with the relevant knowledge and most recent matters of this emerging field. So, invest your money and effort in our 33 course mega bundle that will exceed your expectations within your budget. The Engineering Management for Electrical Technician related fields are thriving across the UK, and recruiters are hiring the most knowledgeable and proficient candidates. It's a demanding field with magnitudes of lucrative choices. If you need more guidance to specialise in this area and need help knowing where to start, then StudyHub proposes a preparatory bundle. This comprehensive Engineering Management for Electrical Technician bundle will help you build a solid foundation to become a proficient worker in the sector. This Engineering Management for Electrical Technician Bundle consists of the following 30 CPD Accredited Premium courses - Course 01:Power Electronics for Electrical Engineering Course 02:Engineering Management Course 03:Electric Circuits for Electrical Engineering Course 04:Trigonometry for Electrical Engineering Course 05:Electrical Technician Course 06:Electronic & Electrical Devices Maintenance Course 07:Sustainable Energy and Development Diploma Course 08:Environment Management Course 09:Project Management Essential Skills Level 3 Course 10:Functional Skills IT Course 11:Delegation Skills Course 12:Effective Communication Skills Course 13:Domestic Plumbing, Installations and Repair Diploma Course 14:Level 3 Heating, Ventilation & Air Conditioning (HVAC) Technician Course 15:Domestic Appliance Repairing Course Course 16:Gas Safety Course 17:Fire Safety | Online Course Course 18:Environmental Engineering Course 19:Car Maintenance & Life Skills Course 20:Motorbike Repairing and Maintenance Diploma Course 21:Domestic Gas Engineer Course 22:Level 2 Domestic Gas Course Course 23:Oil and Gas Management Course 24:Domestic Gas Engineer Course 25:Electronic & Electrical Devices Maintenance & Troubleshooting Course 26:Light Current Systems for Electrical Engineering Course 27:Electrical Machines for Electrical Engineering Course 28:Energy Engineer and Consultant Diploma Course 29:Basic Automotive Engineering: Onboard Diagnostics Course 30:Car Mechanic and Repair Training 3 Extraordinary Career Oriented courses that will assist you in reimagining your thriving techniques- Course 01: Career Development Plan Fundamentals Course 02: CV Writing and Job Searching Course 03: Interview Skills: Ace the Interview Learning Outcome This tailor-made Engineering Management for Electrical Technician bundle will allow you to- Uncover your skills and aptitudes to break new ground in the related fields Deep dive into the fundamental knowledge Acquire some hard and soft skills in this area Gain some transferable skills to elevate your performance Maintain good report with your clients and staff Gain necessary office skills and be tech savvy utilising relevant software Keep records of your work and make a report Know the regulations around this area Reinforce your career with specific knowledge of this field Know your legal and ethical responsibility as a professional in the related field This Engineering Management for Electrical Technician Bundle resources were created with the help of industry experts, and all subject-related information is kept updated on a regular basis to avoid learners from falling behind on the latest developments. Certification After studying the complete training you will be able to take the assessment. After successfully passing the assessment you will be able to claim all courses pdf certificates and 1 hardcopy certificate for the Title Course completely free. Other Hard Copy certificates need to be ordered at an additional cost of •8. CPD 330 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Ambitious learners who want to strengthen their CV for their desired job should take advantage of the Engineering Management for Electrical Technician bundle! This bundle is also ideal for professionals looking for career advancement. Requirements To participate in this course, all you need is - A smart device A secure internet connection And a keen interest in Engineering Management for Electrical Technician Career path Upon completing this essential Bundle, you will discover a new world of endless possibilities. These courses will help you to get a cut above the rest and allow you to be more efficient in the relevant fields.

Search By Location
- Engineering Courses in London
- Engineering Courses in Birmingham
- Engineering Courses in Glasgow
- Engineering Courses in Liverpool
- Engineering Courses in Bristol
- Engineering Courses in Manchester
- Engineering Courses in Sheffield
- Engineering Courses in Leeds
- Engineering Courses in Edinburgh
- Engineering Courses in Leicester
- Engineering Courses in Coventry
- Engineering Courses in Bradford
- Engineering Courses in Cardiff
- Engineering Courses in Belfast
- Engineering Courses in Nottingham