- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
450 Engineering courses delivered Live Online
Online IAM Diploma D23005
By Asset Management Consulting (Asset Management Academy)
Online Asset Management Diploma course. Sit the IAM Diploma anywhere in the world

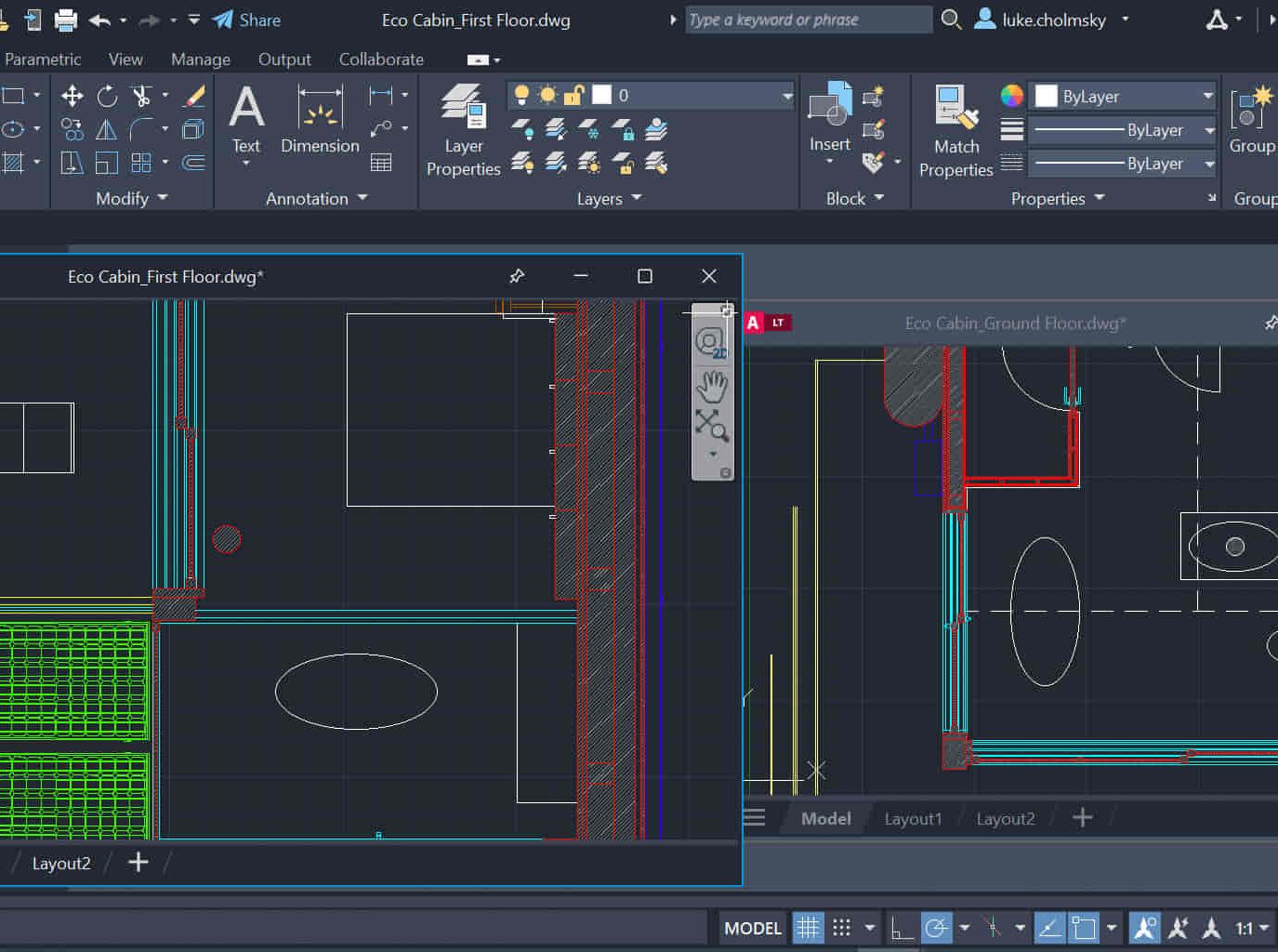
AutoCAD Night Training Course
By ATL Autocad Training London
Why AutoCAD Night Training Course? This Autodesk AutoCAD 2D Evening Course, 10 hours, is perfect for beginners aiming to create 2D plans, elevations, sections. It covers all tools in AutoCAD 2D, making it valuable for both newcomers and those aspiring to enhance their skills. Click here for more info: Website When: Personalized 1-on-1 sessions. Available from Mon to Sat 9 am to 7 pm. Book over the phone, call 02077202581 Duration: 10 hours (Split 10 hrs over as many as days you want) Method: In-person or live online training Course Content: Foundational Shape Construction Manipulating Lines, Arcs, and Polylines Optimizing Object Alignment with Grip Tools Data Management and Backup Protocols File Format Exploration and Understanding Disaster Recovery Strategies Advanced Object Creation Techniques Precision Measurement Unit Handling Dynamic Input Methods Utilizing Inquiry Commands and Measurement Tools Effective Object Visualization and Navigation Zoom, Pan, and Object Manipulation Swift Object Management Strategies Object Transformation and Alteration Techniques Functions for Trimming, Extending, and Offsetting Objects Creating Various Geometric Shapes Object Editing, Joining, and Filleting Stretching and Organizing Objects Layer Management and Customization Configuring Object Properties and Linetypes Designing Layouts and Efficient Page Configurations Scaling Drawing Views and Adding Annotations Text Creation, Styling, and Editing Dimensioning Principles and Customization Implementing Multileaders for Annotations Object Hatching and Editing Techniques Managing Reusable Content: Blocks and Symbols Utilizing Tool Palettes and Working with Groups Understanding Model Space and Paper Space Creating Layouts and Viewports Scaling Viewports and Plotting/PDF Output Managing Multiple Sheet Drawings Optimizing Plotstyles for Printing Creating Custom Drawing Templates To download AutoCAD, visit Autodesk's official website. Advantages: AutoCAD stands as the industry-leading computer-aided design (CAD) software, widely adopted for creating architectural, engineering, and construction drawings. Acquire essential skills applicable across a diverse spectrum of industries. Assessment: Evaluation will occur informally during classes, which comprehensively cover specific topics, complemented by practical drawing exercises to reinforce skills and knowledge. Additionally, we offer longer, independent drawing tasks that encompass multiple acquired skills, evaluated against professional benchmarks. Requirements: Prospective participants should possess basic computer literacy and engagement in professions where CAD is utilized. English Proficiency: Applicants are expected to demonstrate proficiency in both written and spoken English. Why Opt for This Course? Our AutoCAD course is your gateway to mastering the essential skills for creating top-notch technical drawings. Designed with beginners in mind, this course is perfect for individuals who have little to no prior experience with AutoCAD. If your work or studies involve CAD drawings, gaining a solid grasp of the program is crucial for confidence and proficiency. Upon enrollment, students gain access to a free 30 days trial. While classes are conducted using AutoCAD on PC, it's worth noting that the course is compatible with AutoCAD on Mac, albeit with slight interface variations. Who Should Attend? This course caters to those eager to acquire the skills necessary for creating and interpreting drawings produced in AutoCAD. Our diverse system hails from various industries, including engineering, architecture, landscape architecture, construction, electronics, and product design. Why Opt for CAD Training? Practical Learning Experience: Immerse yourself in hands-on training. Personalized One-to-One AutoCAD Classes: Benefit from individualized attention. Expert and Knowledgeable Instructors: Learn from skilled and experienced teachers. Online Training Recordings: Access recorded AutoCAD training sessions online. Best Price Guarantee: Enjoy competitive pricing with a satisfaction guarantee. Pre and Post-Training Support: Receive lifetime free support before and after completing your training. Flexible Schedule: Choose your class timings and dates-weekdays, weekends, or evenings. Tailored Course Content: Customize the AutoCAD course to align with your specific needs. Access Anywhere: Access AutoCAD training and support from any location.
Online IAM Diploma D24001
By Asset Management Consulting (Asset Management Academy)
Online Asset Management Diploma course. Sit the IAM Diploma anywhere in the world. February to March 2024

Fundamentals of Seismic for Non-Geophysicists
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course There are various kinds of geophysical data available. They are separated into seismic and non-seismic (multi-physics) data. Non-seismic or multi-physics data (which includes gravity, magnetics, electrical, electromagnetics, spectral etc - apart from providing complimentary information to seismic) is the main source of information for very shallow subsurface applications such as engineering, mapping pollution, archaeology, geothermal energy, and related areas. This 5 full-day blended course will focus specifically on seismic data which is the main method used in the Oil & Gas industry. In this blended course, participants will be equipped to understand that seismic data represents the movement of the surface, resulting from waves generated by a source, dynamite or vibrator which are reflected by changes in the subsurface rocks. The basic principles of acquisition and processing will be explained and insights into advanced methods, allowing a much more accurate interpretation of seismic data than previously considered possible, will also be provided. This blended course contains an introduction to Machine Learning and its important role in all aspects of seismic acquisition, processing, and interpretation. There is no need to know in detail how the algorithms work internally but it is necessary to know how to use them correctly to achieve optimum results. Training Objectives By attending this course, participants will be able to acquire the following: Obtain an understanding of the strengths and limitations of geophysical methods, specifically seismic, and the costs and risks involved, and how to reduce these. Be able to communicate more effectively with staff in other disciplines. Understand the potential applications of seismic data and know how to formulate the requirements needed for prospect and field evaluation. Gain an awareness of modern seismic technology. Apply the learning in a series of practical, illustrative exercises. Know what types of questions to ask to assess the necessary quality of a seismic project in its role in a sequence of E&P activities Target Audience The blended course is intended for non-geophysicists who have intensive interaction with geophysicists. But it may be of interest to those who want to know about the recent progress made in geophysics, leading to amazing imaging results, which could not be imagined a decade ago. The blended course will bring to the attention of the geologists, petrophysicists and reservoir/petroleum engineers an awareness of how the data they will work with is acquired and processed by the geophysicist. It will introduce the concepts that are of importance in geophysics and thus relevant for non-geophysicists to know and be able to communicate with geophysicists as well as formulate their requests. Course Level Intermediate Trainer Your expert course leader has degree in Geology (University of Leiden), a Master's degree in Theoretical Geophysics (University of Utrecht) and a PhD in Utrecht on 'Full wave theory and the structure of the lower mantle'. This involved forward modelling of P- and S-waves diffracted around the core-mantle boundary and comparison of the frequency-dependent attenuation of the signal with those obtained from major earthquakes observed at long offsets in the 'shadow zone' of the core. These observations were then translated into rock properties of the D' transition zone. After his PhD, he joined Shell Research in The Netherlands to develop methods to predict lithology and pore-fluid based on seismic, petrophysical and geological data. He subsequently worked for Shell in London to interpret seismic data from the Central North Sea Graben. As part of the Quantitative Interpretation assignment, he was also actively involved in managing, processing and interpreting Offshore Seismic Profiling experiments. After his return to The Netherlands, he headed a team for the development of 3D interpretation methods using multi-attribute statistical and pattern recognition analysis on workstations. After a period of Quality Assurance of 'Contractor' software for seismic processing, he became responsible for Geophysics in the Shell Learning Centre. During that period, he was also a part-time professor in Applied Geophysics at the University of Utrecht. From 2001 to 2005, he worked on the development of Potential Field Methods (Gravity, Magnetics) for detecting oil and gas. Finally, he became a champion on the use of EM methods and became involved in designing acquisition, processing and interpretation methods for Marine Controlled Source EM (CSEM) methods. After his retirement from Shell, he founded his own company, specialising in courses on acquisition, processing and interpretation of geophysical data (seismic, gravity, magnetic and electromagnetic data), providing courses to International and National energy companies. In the last couple of years, he became keenly interested in the use of Machine Learning in Geophysics. Apart from incorporating 'Artificial Intelligence' in his courses, he also developed a dedicated Machine Learning course for geophysics. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

Preventive and Predictive Maintenance
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) Preventive and Predictive maintenance are not new concepts. Both have been used across industry all over the world and when done properly, can yield impressive results (cost reductions of 20% or greater and a leap forward in equipment reliability and performance are very achievable). However, for every company using these concepts effectively, there are many others who are not. This 8 half-day Virtual Instructor Led Training (VILT) course has been derived from the Plant Performance Improvement Road Map developed by practitioners that guarantee the reliability of your operations. The VILT training focuses on how to improve profitability of any business by identifying the right maintenance strategy for any equipment. The aim of the VILT training is to help practitioners run programmes that will deliver real benefits as fast as possible with minimum zero wasted effort. The VILT training will also cover the core principles of Reliability Centred Maintenance, Total Productive Maintenance and Six Sigma and the increasingly important role of operations in achieving optimised asset performance. This is a certified course with the option of sitting for a short exam on the final day of the course to give participants the opportunity to gain a Certificate from petroEDGE and the Carcharodon Maintenance Academy. Training Objectives Master the critical skills by acquiring the following: An understanding of how maintenance can add profit The ability to develop improvement programmes that deliver maximum benefit in the shortest time A fundamental understanding of the principles of Preventive, Predictive and other maintenance types A practical understanding of the latest methods of solving problems at root cause level An appreciation of maintenance methodologies such as Reliability Centred Maintenance Strategies for ensuring your company gets value for money from your Contractors How to use the Maintenance Model of Excellence and Plant Performance Improvement Road Map Target Audience This VILT course has been designed for maintenance managers and engineers, reliability professionals, planners, project engineers, operations team members, and functional specialists. Training Methods The VILT course will be delivered online in 8 half-day sessions comprising 4 hours per day, with 2 breaks of 10 minutes per day. Course Duration: 8 half-day sessions, 4 hours per session (32 hours in total). Trainer Your expert course leader is an award-winning consultant and trainer with 30 years' experience in maintenance and reliability improvement. He has worked across five continents, in a wide variety of environments from the world's largest oil refinery to a small drinks production line. He has 10 years of maintenance management experience in the process industry, so he brings a very practical approach to training. He moved into consulting with ABB Eutech as their global maintenance specialist where he led maintenance and reliability best practice panels, delivered a wide range of maintenance improvement projects and trained other consultants. He is a fully qualified CMRP professional, an approved SMRP* Proctor, authorised to conduct CMRP exams and a globally respected maintenance consultant and best practice trainer. He founded his consultancy and training business in 2002 to focus on maintenance and reliability improvement. As part of this, he developed a range of maintenance 'models of excellence' with inputs from authors, international lecturers and some of the world's leading consultants and operators. His work has been recognised as being at the leading edge of industry best practice, winning independent awards such as the UK Chemical Industries Association 'Excellence in Engineering' award. He remains close to the industry as a respected specialist helping operating companies to achieve changes in performance. This ongoing field work enables him to continue to refine and extend best practice and the learning from this is continually fed into his training. His unique experience of facilitating two major turnarounds when the Coronavirus escalated into lockdown have given him a unique insight into how events of this type can disrupt maintenance. Moreover, his involvement in developing management processes and leading a Coronavirus response on a major industrial asset means he can talk with direct experience about how to cope and innovate in this global pandemic. *SMRP refers to Society of Maintenance and Reliability Professionals. PetroEdge is not affiliated with SMRP POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

For the Postgraduate Diploma (PG Dip.) you will study the four modules (60 credits) from the Postgraduate Certificate (PG Cert.) plus an additional three modules (60 credits) from the MA Business of Motorsport Master’s Degree. N.B. The Postgraduate Diploma (PG Dip.) does not include the Executive Project (Dissertation) the final module of the MA.
CertNexus CyberSAFE (CBS-410)
By Nexus Human
Duration 0.5 Days 3 CPD hours This course is intended for This course is designed for all users of computers, mobile devices, networks, and the Internet, to enable them to use technology more securely and minimize digital risks, regardless of technical ability. This course is also designed for you to prepare for the CyberSAFE credential. You can obtain your CyberSAFE certificate by completing the CyberSAFE credential process on the CHOICE platform following the course presentation. Overview In this course, you will identify many of the common risks involved in using conventional computing technology, as well as ways to use it safely, to protect yourself from those risks. You will: Identify security compliance measures. Address social engineering attempts. Secure devices such as desktops, laptops, tablets, smartphones, and more. Use the Internet securely. Welcome to CyberSAFE: Exam CBS-410. Regardless of your computer experience, this class will help you become more aware of technology-related risks and what you can do to protect yourself and your organization from them. This course will help you to:Understand both security and compliance needs and requirements.Recognize and avoid phishing and other social engineering attempts.Recognize and avoid viruses, ransomware, and other malware.Help ensure data security on computers, mobile devices, networks, the Internet, and in the cloud.In this course, you will use discussions, case studies, and the experiences of your instructor and fellow students to explore the hazards and pitfalls of technology and learn how to use that technology safely and securely. Identifying Security Compliance Measures Topic A: Identify Organizational Compliance Requirements and Resources Topic B: Identify Legal Compliance Requirements and Resources Topic C: Identify Industry Compliance Requirements and Resources Recognizing and Addressing Social Engineering Attacks Topic A: Recognize Phishing and Other Social Engineering Attacks Topic B: Defend Against Phishing and Other Social Engineering Attacks Securing Devices Topic A: Maintain Physical Security of Devices Topic B: Use Secure Authentication Methods Topic C: Protect Your Data Topic D: Defend Against Malware Topic E: Use Wireless Devices Securely Using the Internet Securely Topic A: Browse the Web Safely Topic B: Use Email Securely Topic C: Use Social Networks Securely Topic D: Use Cloud Services Securely Topic E: Work from Remote Locations Securely

DevOps Engineering on AWS
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is intended for: DevOps engineers DevOps architects Operations engineers System administrators Developers Overview In this course, you will learn to: Use DevOps best practices to develop, deliver, and maintain applications and services at high velocity on AWS List the advantages, roles and responsibilities of small autonomous DevOps teams Design and implement an infrastructure on AWS that supports DevOps development projects Leverage AWS Cloud9 to write, run and debug your code Deploy various environments with AWS CloudFormation Host secure, highly scalable, and private Git repositories with AWS CodeCommit Integrate Git repositories into CI/CD pipelines Automate build, test, and packaging code with AWS CodeBuild Securely store and leverage Docker images and integrate them into your CI/CD pipelines Build CI/CD pipelines to deploy applications on Amazon EC2, serverless applications, and container-based applications Implement common deployment strategies such as 'all at once,' 'rolling,' and 'blue/green' Integrate testing and security into CI/CD pipelines Monitor applications and environments using AWS tools and technologies DevOps Engineering on AWS teaches you how to use the combination of DevOps cultural philosophies, practices, and tools to increase your organization?s ability to develop, deliver, and maintain applications and services at high velocity on AWS. This course covers Continuous Integration (CI), Continuous Delivery (CD), infrastructure as code, microservices, monitoring and logging, and communication and collaboration. Hands-on labs give you experience building and deploying AWS CloudFormation templates and CI/CD pipelines that build and deploy applications on Amazon Elastic Compute Cloud (Amazon EC2), serverless applications, and container-based applications. Labs for multi-pipeline workflows and pipelines that deploy to multiple environments are also included. Module 0: Course overview Course objective Suggested prerequisites Course overview breakdown Module 1: Introduction to DevOps What is DevOps? The Amazon journey to DevOps Foundations for DevOps Module 2: Infrastructure automation Introduction to Infrastructure Automation Diving into the AWS CloudFormation template Modifying an AWS CloudFormation template Demonstration: AWS CloudFormation template structure, parameters, stacks, updates, importing resources, and drift detection Module 3: AWS toolkits Configuring the AWS CLI AWS Software Development Kits (AWS SDKs) AWS SAM CLI AWS Cloud Development Kit (AWS CDK) AWS Cloud9 Demonstration: AWS CLI and AWS CDK Hands-on lab: Using AWS CloudFormation to provision and manage a basic infrastructure Module 4: Continuous integration and continuous delivery (CI/CD) with development tools CI/CD Pipeline and Dev Tools Demonstration: CI/CD pipeline displaying some actions from AWS CodeCommit, AWS CodeBuild, AWS CodeDeploy and AWS CodePipeline Hands-on lab: Deploying an application to an EC2 fleet using AWS CodeDeploy AWS CodePipeline Demonstration: AWS integration with Jenkins Hands-on lab: Automating code deployments using AWS CodePipeline Module 5: Introduction to Microservices Introduction to Microservices Module 6: DevOps and containers Deploying applications with Docker Amazon Elastic Container Service and AWS Fargate Amazon Elastic Container Registry and Amazon Elastic Kubernetes service Demonstration: CI/CD pipeline deployment in a containerized application Module 7: DevOps and serverless computing AWS Lambda and AWS Fargate AWS Serverless Application Repository and AWS SAM AWS Step Functions Demonstration: AWS Lambda and characteristics Demonstration: AWS SAM quick start in AWS Cloud9 Hands-on lab: Deploying a serverless application using AWS Serverless Application Model (AWS SAM) and a CI/CD Pipeline Module 8: Deployment strategies Continuous Deployment Deployments with AWS Services Module 9: Automated testing Introduction to testing Tests: Unit, integration, fault tolerance, load, and synthetic Product and service integrations Module 10: Security automation Introduction to DevSecOps Security of the Pipeline Security in the Pipeline Threat Detection Tools Demonstration: AWS Security Hub, Amazon GuardDuty, AWS Config, and Amazon Inspector Module 11: Configuration management Introduction to the configuration management process AWS services and tooling for configuration management Hands-on lab: Performing blue/green deployments with CI/CD pipelines and Amazon Elastic Container Service (Amazon ECS) Module 12: Observability Introduction to observability AWS tools to assist with observability Hands-on lab: Using AWS DevOps tools for CI/CD pipeline automations Module 13: Reference architecture (Optional module) Reference architectures Module 14: Course summary Components of DevOps practice CI/CD pipeline review AWS Certification

Management of Value (MoV) Foundation: In-House Training
By IIL Europe Ltd
Management of Value (MoV®) Foundation This interactive MoV® Foundation course provides a modular and case-study-driven approach to learning Management of Value (MoV). The core knowledge is structured and comprehensive; and well-rounded modules cover the methodology and various techniques. A case study is used to help appreciate the relevance of MoV in its practical application. What you will Learn Upon completion of an MoV course candidates should be able to discuss and explain: The main processes and techniques used within MoV and the reasons for using them How MoV may be applied at portfolio, program, project and operational levels The differences in applying MoV at different stages in a project and the expected outputs from a MoV Study at each stage The circumstances under which MoV should be used The concept of value and how value may be improved The main benefits arising from the use of MoV Approaches for implementing MoV How to respond to external and internal influences The principles of embedding MoV into an organization The key topics in document checklists, the toolbox, health check, organizational maturity and individual competence. Upon successful completion of this course, you will be able to: Organize and contribute constructively to a Management of Value (MoV) Study Demonstrate a knowledge of MoV principles, processes, approach and environment Analyse a company, program or project to establish its organizational value; includes identification and weighting of Value Drivers Pass the AXELOS MoV Foundation Examination Introduction to value management and MoV Value and Value Management Capabilities, Outcomes, Benefits and Disbenefits What is Value? What is Management of Value (MoV)? Why use MoV? Where use MoV? When MoV should be used? What using MoV involve? Selected MoV benefits Relationship with other AXELOS Global Best Practices and Models How MoV fits with other AXELOS Global Best Practice Guides MoV principles Align with organization's objectives Focus on functions and required outcomes Balance the variables to maximise value Apply throughout the investment decision Tailor MoV to suit the subject Learn from experience and improve Assign clear roles and responsibilities and build a supportive culture MoV processes Frame the programme or project Gather information Analyse information Process information Evaluate and select Develop Value Improving Proposals Implement and share outputs MoV techniques Function Analysis Function Analysis System Technique (FAST) Traditional (or classic) FAST Technical FAST Customer FAST Value Trees Measuring value Value profiling (a.k.a. value benchmarking) Simple multi-attribute rating technique (a.k.a. SMART) Value index Value metrics Value for money (VfM) ratio Value Engineering / Analysis Common techniques used in MoV Analysis of information Benchmarking Process Mapping Root Cause Analysis Discounted Cash Flow Analysis Generating Ideas Brainstorming Evaluation and option selection Option Selection Matrix Idea selection Allocation to Categories Idea Selection Matrix Weighting techniques Paired Comparisons Points Distribution Developing VIPs Developing Proposals Cost Benefit Analysis Building Decisions Implementing VIPs Implementation Plans Feedback Following up Tracking Benefits Approach to Implementation Generic approach to MoV implementation Plan the MoV activities Understand and articulate value Prioritize value Improve value Quantify value Monitor improvements in value Learn lessons Environmental factors Portfolio Considerations Programme considerations Project considerations Operational Considerations Embedding MoV into an organization Benefits of Embedding MoV into an organization MoV Policy MoV Policy Composition Embedding MoV into an organisation Key steps Suggested MoV Management Structure Overcoming barriers We do it anyway It takes up too much time We can't afford to make the changes What's in it for me? Don't fix it if it ain't broke Fixed returns on investment MoV products Briefing Meeting Agenda (A.1) Communications Checklist (A.2) Equipment list for an Effective Study/Workshop (A.3) Invitation to join the Study Team (A.4) Option Evaluation Matrix (A.5) Plan the Study (A.6) Recording Idea Selection (A.7) Reporting Study outputs (A.8) Scoping the Study (A.9) Study or Workshop Handbook (A.10) Value-Improvement Proposal Forms (A.11) Value Improvement Tracking Report (A.12) MoV toolbox MoV health check and maturity model P3M3 Maturity Model MoV Maturity Model (aligned with P3M3)

CertNexus Certified CyberSec First Responder (CFR-410)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed primarily for cybersecurity practitioners preparing for or who currently perform job functions related to protecting information systems by ensuring their availability, integrity, authentication, confidentiality, and non-repudiation. It is ideal for those roles within federal contracting companies and private sector firms whose mission or strategic objectives require the execution of Defensive Cyber Operations (DCO) or DoD Information Network (DoDIN) operation and incident handling. This course focuses on the knowledge, ability, and skills necessary to provide for the defense of those information systems in a cybersecurity context, including protection, detection, analysis, investigation, and response processes. Overview In this course, you will identify, assess, respond to, and protect against security threats and operate a system and network security analysis platform. You will: Assess cybersecurity risks to the organization. Analyze the threat landscape. Analyze various reconnaissance threats to computing and network environments. Analyze various attacks on computing and network environments. Analyze various post-attack techniques. Assess the organization's security posture through auditing, vulnerability management, and penetration testing. Collect cybersecurity intelligence from various network-based and host-based sources. Analyze log data to reveal evidence of threats and incidents. Perform active asset and network analysis to detect incidents. Respond to cybersecurity incidents using containment, mitigation, and recovery tactics. Investigate cybersecurity incidents using forensic analysis techniques. This course covers network defense and incident response methods, tactics, and procedures that are in alignment with industry frameworks such as NIST 800-61r2 (Computer Security Incident Handling Guide), US-CERT's National Cyber Incident Response Plan (NCIRP), and Presidential Policy Directive (PPD)-41 on Cyber Incident Coordination. It is ideal for candidates who have been tasked with the responsibility of monitoring and detecting security incidents in information systems and networks, and for executing standardized responses to such incidents. The course introduces tools, tactics, and procedures to manage cybersecurity risks, defend cybersecurity assets, identify various types of common threats, evaluate the organization's security, collect and analyze cybersecurity intelligence, and remediate and report incidents as they occur. This course provides a comprehensive methodology for individuals responsible for defending the cybersecurity of their organization. This course is designed to assist students in preparing for the CertNexus CyberSec First Responder (Exam CFR-410) certification examination. What you learn and practice in this course can be a significant part of your preparation. In addition, this course and subsequent certification (CFR-410) meet all requirements for personnel requiring DoD directive 8570.01-M position certification baselines: CSSP Analyst CSSP Infrastructure Support CSSP Incident Responder CSSP Auditor The course and certification also meet all criteria for the following Cybersecurity Maturity Model Certification (CMMC) domains: Incident Response (IR) Audit and Accountability (AU) Risk Management (RM) Lesson 1: Assessing Cybersecurity Risk Topic A: Identify the Importance of Risk Management Topic B: Assess Risk Topic C: Mitigate Risk Topic D: Integrate Documentation into Risk Management Lesson 2: Analyzing the Threat Landscape Topic A: Classify Threats Topic B: Analyze Trends Affecting Security Posture Lesson 3: Analyzing Reconnaissance Threats to Computing and Network Environments Topic A: Implement Threat Modeling Topic B: Assess the Impact of Reconnaissance Topic C: Assess the Impact of Social Engineering Lesson 4: Analyzing Attacks on Computing and Network Environments Topic A: Assess the Impact of System Hacking Attacks Topic B: Assess the Impact of Web-Based Attacks Topic C: Assess the Impact of Malware Topic D: Assess the Impact of Hijacking and Impersonation Attacks Topic E: Assess the Impact of DoS Incidents Topic F: Assess the Impact of Threats to Mobile Security Topic G: Assess the Impact of Threats to Cloud Security Lesson 5: Analyzing Post-Attack Techniques Topic A: Assess Command and Control Techniques Topic B: Assess Persistence Techniques Topic C: Assess Lateral Movement and Pivoting Techniques Topic D: Assess Data Exfiltration Techniques Topic E: Assess Anti-Forensics Techniques Lesson 6: Assessing the Organization's Security Posture Topic A: Implement Cybersecurity Auditing Topic B: Implement a Vulnerability Management Plan Topic C: Assess Vulnerabilities Topic D: Conduct Penetration Testing Lesson 7: Collecting Cybersecurity Intelligence Topic A: Deploy a Security Intelligence Collection and Analysis Platform Topic B: Collect Data from Network-Based Intelligence Sources Topic C: Collect Data from Host-Based Intelligence Sources Lesson 8: Analyzing Log Data Topic A: Use Common Tools to Analyze Logs Topic B: Use SIEM Tools for Analysis Lesson 9: Performing Active Asset and Network Analysis Topic A: Analyze Incidents with Windows-Based Tools Topic B: Analyze Incidents with Linux-Based Tools Topic C: Analyze Indicators of Compromise Lesson 10: Responding to Cybersecurity Incidents Topic A: Deploy an Incident Handling and Response Architecture Topic B: Mitigate Incidents Topic C: Hand Over Incident Information to a Forensic Investigation Lesson 11: Investigating Cybersecurity Incidents Topic A: Apply a Forensic Investigation Plan Topic B: Securely Collect and Analyze Electronic Evidence Topic C: Follow Up on the Results of an Investigation Additional course details: Nexus Humans CertNexus Certified CyberSec First Responder (CFR-410) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the CertNexus Certified CyberSec First Responder (CFR-410) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
