- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1052 Engineer courses in Tynemouth delivered Live Online
AUTOCAD Training for Both MAC and PC Users
By Real Animation Works
Face to Face Training Customised and Bespoke.

EC-Council Certified Network Defender (C|ND) v.2
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Network Administrators Network security Administrators Network Security Engineer Network Defense Technicians CND Analyst Security Analyst Security Operator Anyone who involves in network operations Overview A dedicated focus on IoT security Network virtualization practices for the remote workforce Enhanced Cloud Security & IoT and Operational Technology (OT) Modules Introduction to threat intelligence In-depth Attack Surface Analysis Certified Network Defender (CND) is a vendor-neutral, hands-on, instructor-led comprehensive network security certification training program. It is a skills-based, lab intensive program based on the security education framework and work role task analysis presented by the National Infocomm Competency Framework (NICF) as well as a job-task analysis and cybersecurity education framework by the National Initiative of Cybersecurity Education (NICE). The course has also been mapped to global job roles and to the Department of Defense (DoD) job roles for system/network administrators. The program prepares network administrators how to identify what parts of an organization need to be reviewed and tested for security vulnerabilities and how to reduce, prevent, and mitigate risks in the network. CND covers the protect, detect, respond and predict approach to network security. Course Outline Network Attacks and Defense Strategies Administrative Network Security Technical Network Security Network Perimeter Security Endpoint Security-Windows Systems Endpoint Security-Linux Systems Endpoint Security- Mobile Devices Endpoint Security-IoT Devices Administrative Application Security Data Security Enterprise Virtual Network Security Enterprise Cloud Network Security Enterprise Wireless Network Security Network Traffic Monitoring and Analysis Network Logs Monitoring and Analysis Incident Response and Forensic Investigation Business Continuity and Disaster Recovery Risk Anticipation with Risk Management Threat Assessment with Attack Surface Analysis Threat Prediction with Cyber Threat Intelligence

Red Hat Performance Tuning: Linux in Physical, Virtual, and Cloud (RH442)
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for Senior Linux system administrators responsible for maximizing resource utilization through performance tuning. Overview Analyze and tune for resource-specific scenarios Applying tuning profiles with the tuned tool Tune in virtual environments (hosts and guests) Trace and profile system events and activities Tune resource limits and utilization using systemd-integrated cgroups Gather performance metrics and benchmarking data Red Hat© Enterprise Performance Tuning is designed to teach senior Linux© system administrators the methodology of performance tuning for Red Hat Enterprise Linux. This course discusses system architecture with an emphasis on understanding the implications of system architecture on system performance, methods for testing the effects of performance adjustments, open source benchmarking utilities, methods for analyzing system and networking performance, and tuning configurations for specific application loads. Prerequisites Become a Red Hat Certified Engineer (RHCE©), or demonstrate equivalent experience 1 - Introduction to performance tuning Understand the basic principles of performance tuning and analysis. 2 - Collecting, graphing, and interpreting data Gain proficiency in using basic analysis tools and in evaluating data. 3 - General tuning Learn basic tuning theory and mechanisms used to tune the system. 4 - Hardware profiling Understand and analyze hardware. 5 - Software profiling Analyze CPU and memory performance of applications. 6 - Mail server tuning Learn about basic storage tuning using an email server as an example. 7 - Large memory workload tuning Understand memory management and tuning. 8 - HPC workload tuning HPC workload tuning 9 - File server tuning Understand storage and network tuning in the context of a file server application. 10 - Database server tuning Tune memory and network performance using a database application as an example. 11 - Power usage tuning Tune systems with power consumption in mind. 12 - Virtualization tuning Tune ?host? and ?guest? for efficient virtualization.

Cisco Implementing Secure Solutions with Virtual Private Networks v1.0 (SVPN)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for professionals in the following job roles: Network security engineer CCNP Security candidate Channel Partner Overview After taking this course, you should be able to: Introduce site-to-site VPN options available on Cisco router and firewalls Introduce remote access VPN options available on Cisco router and firewalls Review site-to-site and remote access VPN design options Review troubleshooting processes for various VPN options available on Cisco router and firewalls The Implementing Secure Solutions with Virtual Private Networks (SVPN) v1.0 course teaches you how to implement, configure, monitor, and support enterprise Virtual Private Network (VPN) solutions. Through a combination of lessons and hands-on experiences you will acquire the knowledge and skills to deploy and troubleshoot traditional Internet Protocol Security (IPsec), Dynamic Multipoint Virtual Private Network (DMVPN), FlexVPN, and remote access VPN to create secure and encrypted data, remote accessibility, and increased privacy. Course Outline Introducing VPN Technology Fundamentals Implementing Site-to-Site VPN Solutions Implementing Cisco Internetwork Operating System (Cisco IOS©) Site-to-Site FlexVPN Solutions Implement Cisco IOS Group Encrypted Transport (GET) VPN Solutions Implementing Cisco AnyConnect VPNs Implementing Clientless VPNs Lab Outline Explore IPsec Technologies Implement and Verify Cisco IOS Point-to-Point VPN Implement and Verify Cisco Adaptive Security Appliance (ASA) Point-to-Point VPN Implement and Verify Cisco IOS Virtual Tunnel Interface (VTI) VPN Implement and Verify Dynamic Multipoint VPN (DMVPN) Troubleshoot DMVPN Implement and Verify FlexVPN with Smart Defaults Implement and Verify Point-to-Point FlexVPN Implement and Verify Hub and Spoke FlexVPN Implement and Verify Spoke-to-Spoke FlexVPN Troubleshoot Cisco IOS FlexVPN Implement and Verify AnyConnect Transport Layer Security (TLS) VPN on ASA Implement and Verify Advanced Authentication, Authorization, and Accounting (AAA) on Cisco AnyConnect VPN Implement and Verify Clientless VPN on ASA

The Online NLP Practitioner Training
By Ely Wellbeing
•The Online NLP Practitioner Training is a comprehensive program that will provide you with the tools and techniques you need to overcome your chronic pain and mental health conditions. • The program includes a printable digital copy of the NLP Practitioner Manual, access to the video recording of the training, ‘live’ online demonstrations of the techniques in action on yourself, online support for one year by way of group calls, and assistance set up your business website. • This program is perfect for anyone who wants to achieve positive change in their lives! Whether you’re a self-starter who is interested in self-development or a professional who is seeking career development and job fulfilment.

SCM212 SAP Core Interface and Supply Chain Integration
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for The primary audience for this course are Application Consultants, Business Process Architects, Business Process Owners/Team Leads/Power Users, Data Consultants/Managers, and Solution Architects. Overview Students will set up and deliver their own master data from SAP ERP to SAP SCM (APO), and make any necessary master data enhancements to ensure proper planning results in APO.Students will complete the modeling of their supply chain by creating APO master data that is necessary to activate a fully functional Supply Chain in APO. In this course, students learn how to set up and configure the standard interface between the SAP ERP system and SAP SCM with focus on SAP APO. Integration for Supply Chain Modeling Integrating SAP ERP and SAP SCM Configuring an Integration Model Using Monitoring and Error-Processing Tools Setting Up Incremental Data Transfers for Master Data Changes Organizing Integration Models Performing Routine Operations with Background Processing Supply Chain Locations Managing Locations Integrating Plant Data Integrating MRP Areas Managing Transportation Zones Integrating Customers as Locations Integrating Vendors as Locations Integrating Factory Calendars and Time Streams Supply Chain Products Integrating Products Maintaining Product Data External Procurements Relationships Integrating Purchasing Information Records Integrating Scheduling Agreements Network Modeling Creating Means of Transportation Creating Transportation Lanes Supply Chain Resources Integrating Production Resources Creating Supply Chain Management (SCM)-Specific Resources Integrating Capacity Variants Integrating Setup Groups and Matrices Manufacturing Process Modeling Preparing Integration of Master Data Mapping Bill of Materials (BOM) Fields Mapping the Routings Fields Integrating Production Master Data Transferring a Master Recipe to a Production Process Model (PPM) Transferring Characteristics and Classes Quota Arrangement Creating Quota Arrangements Supply Chain Modeling Creating an SAP liveCache Model Creating a Version in SAP SCM Using the Supply Chain Engineer (SCE) Transactional Data Integration Integrating Transactional Data Supply Chain Subcontracting Preparing Master Data for Subcontracting

Study online for the Master’s Advanced Motorsport Engineering and boost your motorsport career. With the ability to fit your studies around your existing career and family, the MSc is flexible and affordable. Start on any date and study when and where suits you!

C)SLO-Certified Security Leadership Officer Mile 2
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for C - Level Managers IT Managers Cyber Security Personelle Engineers Information Systems Owners ISSO's CISSP Students ISO's Overview Upon completion, the Certified Security Leadership Officer candidate be able to competently take the C)SLO exam. You will be versed in implementing strong security controls and managing an organization with an industry acceptable security posture. Certified Security Leadership Officerÿ course is designed for mid and upper-level managers.ÿ If you are an engineer, this course will increase your knowledge in the leading information system security teams. Plus, the C)SLO will give you an essential understanding of current security issues, best practices, and technology. With this knowledge you will then be prepared to manage the security component of an information technology project. As a Security Leadership Officer, you will be the bridge between cybersecurity and business operations. Course Outline Security Management Risk Management Encryption Information Security Access Control Concepts Incident Handling and Evidence Operations Security Network Security Additional course details: Nexus Humans C)SLO-Certified Security Leadership Officer Mile 2 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the C)SLO-Certified Security Leadership Officer Mile 2 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Oracle Database 12c - Backup and Recovery Workshop
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Database Administrators Data Warehouse Administrator Support Engineer Technical Consultant Technical Administrator Overview Describe Oracle Database backup methods and recovery operations that can be used to resolve database failure. Describe the Oracle Database architecture components related to backup and recovery operations. Plan effective backup and recovery procedures. Configure the database for recoverability. Use Recovery Manager (RMAN) to create backups and perform recovery operations. Use the Data Recovery Advisor to diagnose and repair failures. Use Oracle Flashback Technologies to recover from human error. Perform an encrypted database backup and restore. Perform tablespace point-in-time recovery. Describe additional high availability features such as Oracle Data Guard. This Oracle Database 12c: Backup and Recovery Workshop will teach you how to evaluate your own recovery requirements. You'll develop appropriate strategies for backup, restore and recovery procedures from provided scenarios. This Oracle Database 12c: Backup and Recovery Workshop will teach you how to evaluate your own recovery requirements. You'll develop appropriate strategies for backup, restore and recovery procedures from provided scenarios. Additional course details: Nexus Humans Oracle Database 12c - Backup and Recovery Workshop training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Oracle Database 12c - Backup and Recovery Workshop course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

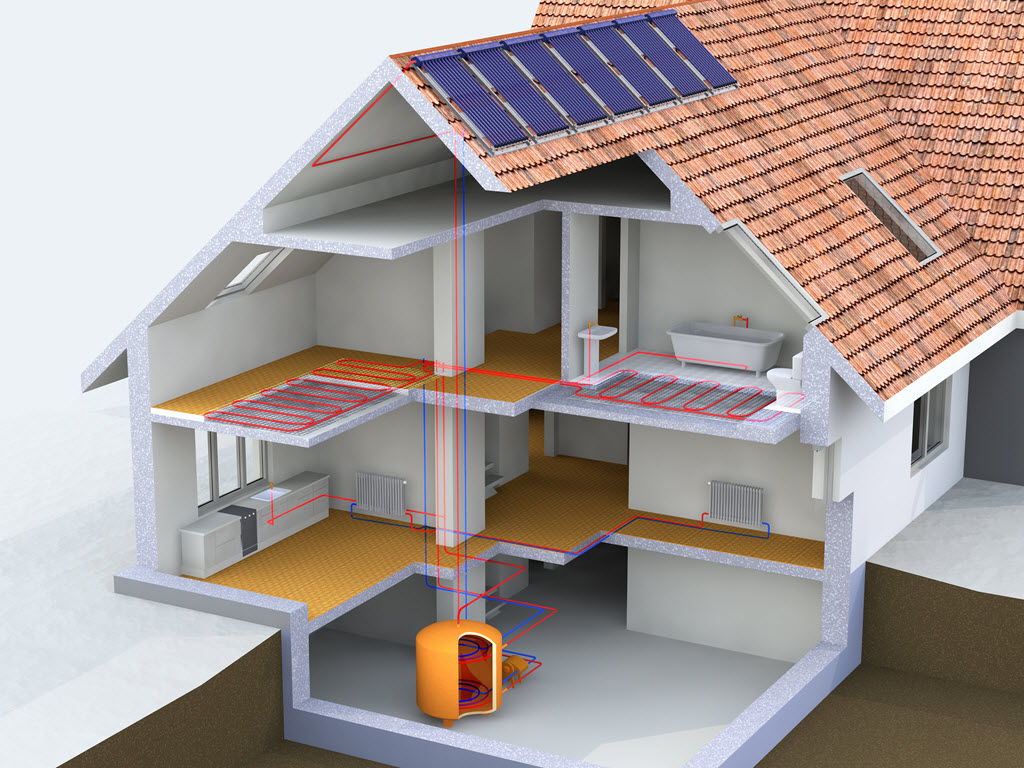
For new users and the curious. Hello, For new users and the curious. IMPORTANT: Firstly, once you are signed up, send us your requests on what you would like to see within the demonstration and learn on the course. We will then cater for your needs and answer them during the session. This is designed to be an introduction into how to start a room by room survey using the Heat Engineer app, then sending this survey to the online dashboard. We will then go through the different steps to complete this heat loss report. Optional pages will also be worked through and shown. Examples of how to select the flow temperature and the heat source (heat pumps and boilers) will be presented once the heat loss result is completed.