- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
3132 Development courses in Nottingham delivered Live Online
FAA Level 1 Award In Awareness Of First Aid For Mental Health (RQF) Classroom (4.5 hour course), Virtual (2 x 2 ½ hour sessions) Gives learners a good awareness of Mental Health First Aid Gives learners the skills to start that difficult conversation Course Contents: What is Mental Health? Why people develop mental health conditions What the role of a mental health first aider is Knowing how to provide advice and practical support Knowing how to recognise and manage stress Recognising a range of mental health conditions: Depression Anxiety Psychosis Eating disorders Suicide Self-harm Benefits of this course: 37% of all work-related ill-health is due to mental health problems Problems with mental health cover 45% of all working days lost A whopping 12.8 million working days, or 49, 042 years, were lost due to mental health problems in 2018/19 602,000 workers suffered from work-related stress, depression or anxiety in 2018/19 One in four people will have a mental health problem at some point during their lives Whether work is causing or aggravating mental health problems, employers have a legal responsibility towards their employees Work-related mental health issues must to be assessed to measure the levels of risk to staff Where a risk is identified, steps must be taken to remove it or reduce it as far as reasonably practicable This half day course gives people a good awareness of mental health in the workplace For a more complete introduction, see our full day First Aid for Mental Health or two day Supervising First Aid for Mental Health courses Accredited, Ofqual regulated qualification This Awareness of Mental Health First Aid Course is a nationally recognised, Ofqual regulated qualification accredited by First Aid Awards. This means that you can be rest assured that your Mental Health First Aid Certificates fulfil the upcoming legal requirements and are a very good way to make sure you and your employees have a supporting workplace to deal with staff's mental health conditions. The Ofqual Register number for this course is 603/3768/0

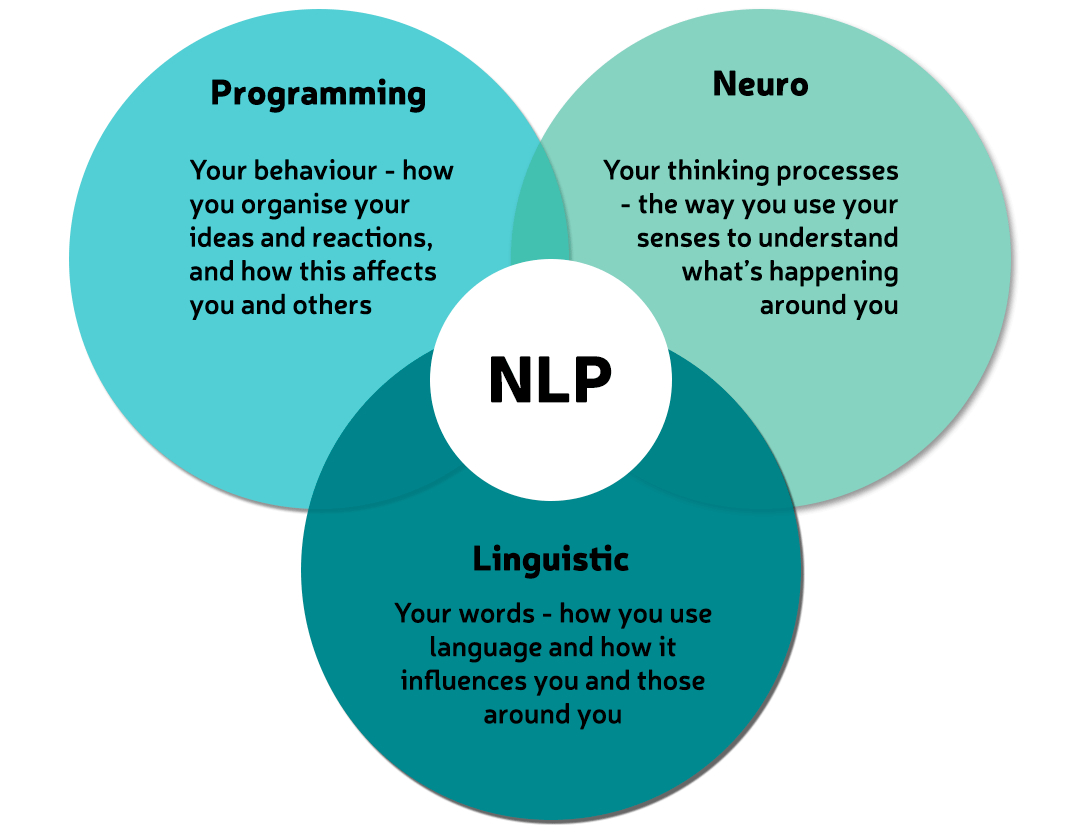
What is NLP?
By Proactive NLP Ltd
What is NLP? Join proactivenlp.com on this virtual workshop and find out how NLP can start changing your life by saying goodbye to the negatives and welcoming in all the positives you want.
CompTIA Cloud+
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for IT professionals who wish to develop cloud computing skills to enable them to move IT workloads to the cloud and integrate products and services from different providers and industries. Their focus is to ensure that cloud deployments are secure, that automation and orchestration are used effectively to bring business value from the cloud, and that costs are controlled through effective management of cloud vendors. This course is also designed for students who are preparing to take the CompTIA Cloud+ certification exam CV0-003, or who plan to use Cloud+ as the foundation for more advanced cloud certifications or career roles. Overview In this course, you will deploy, test, secure, manage, optimize, and troubleshoot a cloud solution. You will: - Prepare to deploy cloud solutions - Deploy a pilot project - Test a pilot project deployment - Design a secure network for cloud deployment - Determine CPU and memory sizing for cloud deployments - Determine storage requirements for cloud deployments - Plan Identity and Access Management for cloud deployments - Analyze workload characteristics to ensure successful migration to the cloud - Secure systems to meet access requirements - Maintain cloud systems - Implement backup, restore, and business continuity measures - Analyze cloud systems for required performance - Analyze cloud systems for anomalies and growth forecasting - Troubleshoot deployment, capacity, automation, and orchestration issues - Troubleshoot connectivity issues - Troubleshoot security issues In this course, you will learn how to implement, maintain, and deliver cloud technologies including network, storage, and virtualization technologies to create cloud solutions. 1 - PREPARING TO DEPLOY CLOUD SOLUTIONS Describe Interaction of Cloud Components and Services Describe Interaction of Non-cloud Components and Services Evaluate Existing Components and Services for Cloud Deployment Evaluate Automation and Orchestration Options Prepare for Cloud Deployment 2 - DEPLOYING A PILOT PROJECT Manage Change in a Pilot Project Execute Cloud Deployment Workflow Complete Post-Deployment Configuration 3 - TESTING PILOT PROJECT DEPLOYMENTS Identify Cloud Service Components for Testing Test for High Availability and Accessibility Perform Deployment Load Testing Analyze Test Results 4 - DESIGNING A SECURE AND COMPLIANT CLOUD INFRASTRUCTURE Design Cloud Infrastructure for Security Determine Organizational Compliance Needs 5 - DESIGNING AND IMPLEMENTING A SECURE CLOUD ENVIRONMENT Design Virtual Network for Cloud Deployment Determine Network Access Requirements Secure Networks for Cloud Interaction Manage Cloud Component Security Implement Security Technologies 6 - PLANNING IDENTITY AND ACCESS MANAGEMENT FOR CLOUD DEPLOYMENTS Determine Identity Management and Authentication Technologies Plan Account Management Policies for the Network and Systems Control Access to Cloud Objects Provision Accounts 7 - DETERMINING CPU AND MEMORY SIZING FOR CLOUD DEPLOYMENTS Determine CPU Size for Cloud Deployment Determine Memory Size for Cloud Deployment 8 - DETERMINING STORAGE REQUIREMENTS FOR CLOUD DEPLOYMENTS Determine Storage Technology Requirements Select Storage Options for Deployment Determine Storage Access and Provisioning Requirements Determine Storage Security Options 9 - ANALYZING WORKLOAD CHARACTERISTICS TO ENSURE SUCCESSFUL MIGRATION Determine the Type of Cloud Deployment to Perform Manage Virtual Machine and Container Migration Manage Network, Storage, and Data Migration 10 - MAINTAINING CLOUD SYSTEMS Patch Cloud Systems Design and Implement Automation and Orchestration for Maintenance 11 - IMPLEMENTING BACKUP, RESTORE, DISASTER RECOVERY, AND BUSINESS CONTINUITY MEASURES Back Up and Restore Cloud Data Implement Disaster Recovery Plans Implement Business Continuity Plans 12 - ANALYZING CLOUD SYSTEMS FOR PERFORMANCE Monitor Cloud Systems to Measure Performance Optimize Cloud Systems to Meet Performance Criteria 13 - ANALYZING CLOUD SYSTEMS FOR ANOMALIES AND GROWTH FORECASTING Monitor for Anomalies and Resource Needs Plan for Capacity Create Reports on Cloud System Metrics 14 - TROUBLESHOOTING DEPLOYMENT, CAPACITY, AUTOMATION, AND ORCHESTRATION ISSUES Troubleshoot Deployment Issues Troubleshoot Capacity Issues Troubleshoot Automation and Orchestration Issues 15 - TROUBLESHOOTING CONNECTIVITY ISSUES Identify Connectivity Issues Troubleshoot Connectivity Issues 16 - TROUBLESHOOTING SECURITY ISSUES Troubleshoot Identity and Access Issues Troubleshoot Attacks Troubleshoot Other Security Issues Additional course details: Nexus Humans CompTIA Cloud Plus Certification (Exam CV0-003) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the CompTIA Cloud Plus Certification (Exam CV0-003) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Microsoft Excel Macros & VBA - Online classroom
By Microsoft Office Training
Course Objectives At the end of this course you will be able to: Record and edit a Macro Assign macros to keyboard shortcuts, Quick Access Toolbar, Buttons and Shape objects. Use the Visual Basic Editor; change the properties of an object; add a module to a project; write the code for a procedure and then run it; and use the Object Browser to search procedures Manipulate data by declaring variables of different data types; combine data by using expressions; use functions to accept input and display output; and declare variables and procedures with the appropriate scope Use decision structures to create procedures that make decisions; and use loop structures to perform repetitive tasks Create an error handling routine in case things go wrong with VBA code ' 1 year email support service Take a closer look at the consistent excellent feedback from our growing corporate clients visiting our site ms-officetraining co uk Customer Feedback Best Training Ever! Just finished a bespoke 1-1 training course in Excel Advanced, Macros & VBA. Pedro is an excellent trainer, imparting his skills and knowledge in the best way - appropriately to audience skills, knowledge and ability. Pedro is always approachable, encouraging and supportive, giving delegates the optimum learning environment. I would not hesitate to recommend Pedro as a trainer, whatever your level of ability. Amanda Morris - Treasury & Systems Accountant at Reall - Real Equity for All The trainer was very knowledgeable, kept everyone involved and was enthusiastic. A great experience.. Simon Harper - Lloyd's of London My learning experience was awesome. Perdinand Reagan - Subsea7 Very nice and relaxed approach to teaching. Was definitely a good learning experience. Jerome Pupe - S5 Agency World The Trainer – Very positive + patient + helpful + thorough Agnes Souza - Direct Wines ' With more than 20 years experience, we deliver courses on all levels of the Desktop version of Microsoft Office and Office 365; ranging from Beginner, Intermediate, Advanced to the VBA level. Our trainers are Microsoft certified professionals with a proven track record with several years experience in delivering classroom, one to one, tailored and bespoke courses. Tailored In Company training: You can choose to run the course exactly as they are outlined by us or we can customise it so that it meets your specific needs. A tailored or bespoke course will follow the standard outline but may be adapted to your specific organisational needs. Introduction to Macros and VBA Introducing Visual Basic for Applications Recording a Macro Naming conventions for Macro Procedures Running a Macro Absolute or Relative Cell Referencing Saving and Opening Files with Macros Making macros always available Adding Macros to Keyboard Shortcuts, Quick Access Toolbar, Buttons and Shapes Editing a Macro in the Visual Basic Editor Understanding the Development Environment Customising the Editor Tips for General Typing in VBA Using Visual Basic Help Working with Procedures Program Design Understanding Modules Naming Rules Creating a Module Understanding Procedures Programming Macro Concepts Creating a Subroutine Creating a Function Understanding Arguments Exiting Procedures Calling Procedures Objects, Properties, Methods and Events Understanding Objects Properties, Methods, and Events Navigating the Object Hierarchy Understanding Collections Accessing a Member of a Collection Understanding Hierarchy Using the Object Browser Using the With Statement Working with Properties Working with Methods Creating an Event Procedure Reserved Macro Names Using Expressions, Variables and Intrinsic Functions Understanding Expressions and Statements Declaring Variables Understanding Data Types Determining the Value of Variables Working with Variable Scope Using Built-in VBA Functions Understanding Constants Using Message Boxes Controlling the Answer to a Message Box Using Input Boxes Declaring and Using Object Variables Controlling Program Execution Understanding Control-of-Flow Structures Using the If...End If Decision Structures Nested If Statements Using the Select Case ... End Select Structure Using the Do ... Loop Structure Using the For ... Next Structure Using the For Each ... Next Structure Guidelines for Use of Control-of-Flow Structures Debugging and Handling Errors Understanding Errors Using Debugging Tools Setting Breakpoints and Using Break Mode Stepping Through Code Trapping Errors with the On Error Statement Understanding the Err Object Working with Inline Error Handling Writing an Error-Handling Routine Working with Forms and Controls Understanding UserForms Creating a Form Displaying and Removing a Form Aligning and Sizing Controls Using the Toolbox Working with a Form's Properties, Methods, and Events Working with Form and Control Properties, Methods and Event Setting the Tab Order Populating a Control Who is this course for? Who is this course for? This course is designed to give proficiency in the Visual Basic Editor (VBE), predominantly making use of Excel objects, understanding Object's Properties, Events and Methods, basic VBA Object oriented programming, event handling, control structures, and debugging tools. Requirements Requirements Preferably, delegates should have attended the Excel Advanced course. Career path Career path Excel know-how can instantly increase your job prospects as well as your salary. 80 percent of job openings require spreadsheet and word-processing software skills Certificates Certificates Certificate of completion Digital certificate - Included

DP-080T00 Querying Data with Microsoft Transact-SQL
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for This course can be valuable for anyone who needs to write basic SQL or Transact-SQL queries. This includes anyone working with data as a data analyst, a data engineer, a data scientist, a database administrator or a database developer. It can also be useful for others peripherally involved with data, or wanting to learn more about working with data such as solution architects, students and technology managers. This course will teach the basics of Microsoft's dialect of the standard SQL language: Transact-SQL. Topics include both querying and modifying data in relational databases that are hosted in Microsoft SQL Server-based database systems, including: Microsoft SQL Server, Azure SQL Database and, Azure Synapse Analytics. 1 - Introduction to Transact-SQL Work with schemas Explore the structure of SQL statements Examine the SELECT statement Work with data types Handle NULLs 2 - Sort and filter results in T-SQL Sort your results Limit the sorted results Page results Remove duplicates Filter data with predicates 3 - Combine multiple tables with JOINs in T-SQL Understand joins concepts and syntax Use inner joins Use outer joins Use cross joins Use self joins 4 - Write Subqueries in T-SQL Understand subqueries Use scalar or multi-valued subqueries Use self-contained or correlated subqueries 5 - Use built-in functions and GROUP BY in Transact-SQL Categorize built-in functions Use scalar functions Use ranking and rowset functions Use aggregate functions Summarize data with GROUP BY Filter groups with HAVING 6 - Modify data with T-SQL Insert data Generate automatic values Update data Delete data Merge data based on multiple tables Additional course details: Nexus Humans DP-080T00 Querying Data with Microsoft Transact-SQL training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the DP-080T00 Querying Data with Microsoft Transact-SQL course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Face to Face Course via Zoom - Productive Conversations in Challenging Situations
By The Development People
We are delighted to share that we are now running our GP Admin Development Programmes Live Online! If your team have had enough of pre-recorded courses then this is perfect! We are delivering the content online - Live! Teams can get involved, interact with each other, and have great discussions. We deliver a suite of programmes to support their development pathway of GP admin staff. Just £79+vat pp for a half day workshop with resources. The second in the series is: Productive Conversations in Challenging Situations This workshop will provide an opportunity to understand why patients are experiencing conflict within themselves, what the impact is on their behaviour and how we can effectively work with them to find a positive solution. We add value by discussing the importance of the role your team play and how they can manage their own conflict when dealing with challenging situations. This workshop is based on the Chimp Paradox theory (by Professor Stephen Peters). We use the analogy of Chimp to make it memorable and fun to learn about! It's suitable for all staff (new and more experienced). We also encourage the line manager to participate so that they can follow up on the content using our manager support pack - enabling staff to sustain and embed the learning. The programme will cover the following: Understanding and defining conflict Why conflict happens Identifying & recognising different conflict types How to have more productive conversations Tools to help respond effectively and have problem solving conversations Keeping yourself 'safe', avoiding triggers and escalation Review, Reflect, Reset We will be running multiple dates so that you can enrol small groups of staff any one time, leaving you enough people to man the helm!If you have any questions then please do get in touch,lucy@thedevelopmentpeople.co.uk

Sustainability Summit for SMEs: Thriving Businesses and Strong Supply Chains!
By SustainabilitySupportServiceforBusinessTraining
Join us at our Sustainability Summit for SMEs to learn how to build thriving businesses and resilient supply chains in a fun and interactive Refund Policy Contact the organiser to request a refund.Eventbrite's fee is nonrefundable. About this event Event lasts 5 hours 30 minutes Sustainability Summit for SMEs: Thriving Businesses and Strong Supply Chains! Welcome to the Sustainability Summit 2024, a 1-day online event focused on sustainability for founders and senior decision makers in small and medium enterprises (SMEs), including those in the supply chains of larger organisations! In today’s dynamic business landscape, sustainability isn't just a buzzword; it's a necessity. Small and medium size enterprises must go beyond policy statements and adopt cohesive, actionable strategies to thrive. WHEN Date: Tuesday, 22 October 2024 Time: 10:00 AM – 3:15 PM (BST) Where: online (virtual event) This online Sustainability Summit will cover essential topics such as: Marketing, HR (skills and talent development), Low-carbon digital assets, Procurement, Finance and ESG. It will feature Guest Speakers, dynamic panel discussions and real-world case studies. Designed with small and medium enterprises at the centre, this learning event promises to be inspiring and thought provoking. Speakers will provide practical, actionable insights for immediate implementation as well as share effective ways to enable you to be more adaptable in the medium to long-term. Book now to participate from the comfort of your workplace [or your home office]. Our lineup of speakers include: Prof. Dave Spicer, Director of Business & Community Engagement, Univ. of Bradford Richard Clarke, Founder and Managing Director of Highland Carbon Tracy Cartwright, SHEQ Consultant and Director of Applaud Business Consultancy Antony Gutsa, Founder & CEO of Ecoswap and Banking Professional Giles Metcalfe, Ethical Marketer at Giles Metcalfe Digital Carolyn McGarry Williams, Co-Founder of 4 My Card and Director of Marketing Trevor Gibbs, Web Accessibility Specialist Amelia Banful, Head of Business Strategy, Enviro Electronics Dr Veronica Broomes, Founder of Sustainability Support Service & Sustainability Expert David Conner, Founder at 2030hub & Global Goals Week Organiser BENEFITS: reasons why you should attend Expert Insights: Hear from Guest Speakers and Panellists about the latest trends in sustainability and forthcoming changes in policies and legislation. Real-world case studies: Discover success stories from other SMEs that integrated multiple facets of sustainability for business benefits. Innovative Strategies: Learn actionable approaches to embed sustainability in your business and how to showcase this to win new business and talent for the future. Future-proof your business: Get inspired by new processes and up-skilling opportunities. Equip yourself with the knowledge to adapt and thrive. Networking: Connect with attendees during an interactive and fun 'lunchtime' session. PRICE: from £97.00 PLUS BONUSES: YOUR SWAG BAG GIFTS: *Personalised digital business card: discounted price for 1 year subscription for attendees. [Usual price: £65 or US$70] *Eco-friendly gift card: 10% OFF *Sustainability Calendar 2025: 40% OFF for attendees [You save £27 or US$29] DONATION TO CHARITY Our commitment to People, Planet and Communities (business, geographic, places) is ongoing. For this 2024 Sustainability Summit [online], we will donate 1% of ticket price (ex. VAT) to The Rotary Foundation, our global charity of choice. WHO SHOULD ATTEND This Sustainability Summit is ideal for: • Business Founders and Senior Leaders: Gain strategic insights and learn practical actions to embed sustainability in your organisation’s DNA. • SMEs in Supply Chains: Understand how to meet the sustainability expectations of larger organisations and enhance your competitiveness. • Procurement and HR Professionals: Update your knowledge and gain useful insights about varied road maps to evidence sustainability -multiple pillars: planet, people for high social impact, ESG. Don’t miss this chance to learn more about how your business can be at the forefront and boost competitiveness with embedding sustainability for environmental, social and economic benefits. BOOK YOUR PLACE NOW https://www.eventbrite.co.uk/e/sustainability-summit-for-smes-thriving-businesses-and-strong-supply-chains-tickets-993387768557 DON'T MISS OUT Don't miss this opportunity to learn in a dynamic virtual meeting, network with business leaders and founders in a professional environment and gain the knowledge you need to take your business to the next level with capable and resilient supply chains! #sustainabilitysummit, #onlinesustainabilityevent, #sustainabilitytraining, #CSR, #sustainabilityforSMEs, #businesssustainability #summit, #greenbusiness, #online, #supplychains, #planet #forpurpose #betterbusiness, #netzero, #conference

55348 Administering Microsoft Endpoint Configuration Manager
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is for experienced information technology (IT) professionals, typically described as Enterprise Desktop Administrators (EDAs). These EDAs deploy, manage, and maintain PCs, devices, and applications across medium, large, and enterprise organizations. A significant portion of this audience uses, or intends to use, the latest release of Configuration Manager to manage and deploy PCs, devices, and applications. Overview Describe the features Configuration Manager and Intune include, and explain how you can use these features to manage PCs and mobile devices in an enterprise environment. Analyze data by using queries and reports. Prepare a management infrastructure, including configuring boundaries, boundary groups, and resource discovery, and integrating mobile-device management with Intune. Deploy and manage the Configuration Manager client. Configure, manage, and monitor hardware and software inventory, and use Asset Intelligence and software metering. Identify and configure the most appropriate method to distribute and manage content used for deployments. Distribute, deploy, and monitor applications for managed users and systems. Maintain software updates for PCs that Configuration Manager manages. Implement Endpoint Protection for managed PCs. Configure an operating-system deployment strategy by using Configuration Manager. Manage and maintain a Configuration Manager site. This five-day course describes how to use Configuration Manager and its associated site systems to efficiently manage network resources. In this five-day course, you will learn day-to-day management tasks, including how to manage applications, client health, hardware and software inventory, operating system deployment, and software updates by using Configuration Manager. You also will learn how to optimize Endpoint Protection, manage compliance, and create management queries and reports. Although this course and the associated labs are written for Microsoft Endpoint Configuration Manager and Windows 11, the skills taught will also be backwards compatible with previous editions of System Center Configuration Manager and Windows 10. Prerequisites Networking fundamentals, including common networking protocols, topologies, hardware, media, routing, switching, and addressing. Active Directory Domain Services (AD DS) principles and fundamentals of AD DS management. Installation, configuration, and troubleshooting for Windows-based personal computers. Basic concepts of public key infrastructure (PKI) security. Basic understanding of scripting and Windows PowerShell syntax. Basic understanding of Windows Server roles and services. Basic understanding of the configuration options for iOS and Android Mobile device platforms. 1 - Managing computers and mobile devices in the enterprise Overview of systems management by using enterprise management solutions Overview of the Configuration Manager architecture Overview of the Configuration Manager administrative tools Tools for monitoring and troubleshooting a Configuration Manager site 2 - Analyzing data using queries, reports, and CMPivot Introduction to queries Configuring SQL Server Reporting Services Analyzing the real-time state of a device by using CMPivot 3 - Preparing the Configuration Manager management infrastructure Configuring site boundaries and boundary groups Configuring resource discovery Organizing resources using device and user collections 4 - Deploying and managing the Configuration Manager client Overview of the Configuration Manager client Deploying the Configuration Manager client Configuring and monitoring client status Managing client settings and performing management operations 5 - Managing inventory for PCs and applications Overview of inventory collection Configuring hardware and software inventory Managing inventory collection Configuring software metering Configuring and managing Asset Intelligence 6 - Distributing and managing content used for deployments Preparing the infrastructure for content management Distributing and managing content on distribution points 7 - Deploying and managing applications Overview of application management Creating applications Deploying applications Managing applications Deploying and managing Windows apps 8 - Maintaining software updates for managed PCs The software updates process Preparing a Configuration Manager site for software updates Managing software updates Configuring automatic deployment rules Monitoring and troubleshooting software updates Enabling third-party updates 9 - Implementing Defender Protection for managed PCs Overview of Endpoint Protection in Configuration Manager Configuring, deploying, and monitoring Endpoint Protection policies Configuring and deploying advanced threat policies 10 - Managing compliance and secure data access Overview of Compliance Settings Configuring compliance settings Viewing compliance results Managing resource and data access 11 - Managing operating system deployment An overview of operating system deployment Preparing a site for operating system deployment Deploying an operating system Managing Windows as a service 12 - Managing and maintaining a Configuration Manager site Configuring role-based administration Configuring Remote Tools Overview of Configuration Manager site maintenance and Management Insights Backing up and recovering a Configuration Manager site Updating the Configuration Manager infrastructure 13 - What?s new in Microsoft Endpoint Configuration Manager Whats new in Microsoft Endpoint Manager covering each semi annual release Additional course details: Nexus Humans 55348: Administering Microsoft Endpoint Configuration Manager training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the 55348: Administering Microsoft Endpoint Configuration Manager course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Face to Face Course via Zoom - Positive & Proactive Communication for Effective Call Handling
By The Development People
We are delighted to share that we are now running our GP Admin Development Programmes Live Online! If your team have had enough of pre-recorded courses then this is perfect! We are delivering the content online - Live! Teams can get involved, interact with each other, and have great discussions. We deliver a suite of programmes to support the development pathway of GP admin staff. Just £79+vat pp for a half day workshop with resources. The first in the series is: Positive & Proactive Communication for Effective Call Handling This workshop will provide an opportunity to look at how we positively communicate with others - taking into account patients expectations, stereotypes, our role, and how to have the best interactions! We add value by discussing the importance of their roles, exploring how change impacts us and patients, and how we can choose to respond. We couple this with a deeper exploration of communication techniques that leads to a greater understanding of how we can communicate using positive intention & language. It's suitable for all staff (new and more experienced). We also encourage the line manager to participate so that they can follow up on the content using our manager support pack - enabling staff to sustain and embed the learning. The programme will cover the following: The Heart Of The Surgery Changes & Choices Patient Experience Effective Communication Managing Other’s Emotions & Challenging Patients Importance of Signposting Keeping Motivated Creating New Habits We will be running multiple dates so that you can enrol small groups of staff any one time, leaving you enough people to man the helm!If you have any questions then please do get in touch,lucy@thedevelopmentpeople.co.uk