- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
3448 Design courses delivered Live Online
Microsoft Access for Office 365: Part 1
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for This course is designed for students looking to establish a foundational understanding of Access, including the skills necessary to create a new database, construct data tables, design forms and reports, and create queries. Overview In this course, you will create and manage an Access database. You will: Navigate within the Access application environment, create a simple database, and customize Access configuration options. Organize and manage data stored within Access tables. Use queries to join, sort, and filter data from different tables. Use forms to make it easier to view, access, and input data. Create and format custom reports. Data is everywhere. Most job roles today involve some form of data management. Virtually everyone is affected in some way by the need to manage data. A relational database application such as Microsoft© Access© can help you and your organization with this task. This course is the first part of a three-course series that covers the skills needed to perform database design and development in Access. Microsoft© Access© for Office 365?: Part 1 (this course): Focuses on the design and construction of an Access database?viewing, navigating, searching, and entering data in a database, as well as basic relational database design and creating simple tables, queries, forms, and reports. Microsoft© Access© for Office 365?: Part 2 : Focuses on optimization of an Access database, including optimizing performance and normalizing data, data validation, usability, and advanced queries, forms, and reports. Microsoft© Access© for Office 365?: Part 3 : Focuses on managing the database and supporting complex database designs, including import and export of data, using action queries to manage data, creating complex forms and reports, macros and VBA, and tools and strategies to manage, distribute, and secure a database. This course may be a useful component in your preparation for the Microsoft Access Expert (Microsoft 365 Apps and Office 2019): Exam MO-500 certification exam. Lesson 1: Working with an Access Database Topic A: Launch Access and Open a Database Topic B: Use Tables to Store Data Topic C: Use Queries to Combine, Find, Filter, and Sort Data Topic D: Use Forms to View, Add, and Update Data Topic E: Use Reports to Present Data Topic F: Get Help and Configure Options in Access Lesson 2: Creating Tables Topic A: Plan an Access Database Topic B: Start a New Access Database Topic C: Create a New Table Topic D: Establish Table Relationships Lesson 3: Creating Queries Topic A: Create Basic Queries Topic B: Add Calculated Columns in a Query Topic C: Sort and Filter Data in a Query Lesson 4: Creating Forms Topic A: Start a New Form Topic B: Enhance a Form Lesson 5: Creating Reports Topic A: Start a New Report Topic B: Enhance Report Layout Additional course details: Nexus Humans Microsoft Access for Office 365: Part 1 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Microsoft Access for Office 365: Part 1 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Networking in Google Cloud
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for This class is intended for network engineers and network admins that are either using Google Cloud Platform or are planning to do so. The class is also for individuals that want to be exposed to software-defined networking solutions in the cloud. Overview Configure Google VPC networks, subnets, and routers Control administrative access to VPC objects Control network access to endpoints in VPCsInterconnect networks among GCP projects Interconnect networks among GCP VPC networks and on-premises or other-cloud networks Choose among GCP load balancer and proxy options and configure them Use Cloud CDN to reduce latency and save money Optimize network spend using Network TiersConfigure Cloud NAT or Private Google Access to provide instances without public IP addresses access to other services Deploy networks declaratively using Cloud Deployment Manager or Terraform Design networks to meet common customer requirements Configure monitoring and logging to troubleshoot networks problems Learn about the broad variety of networking options on Google Cloud. This course uses lectures, demos, and hands-on labs to help you explore and deploy Google Cloud networking technologies, including Virtual Private Cloud (VPC) networks, subnets, and firewalls; interconnection among networks; load balancing; Cloud DNS; Cloud CDN; and Cloud NAT. You'll also learn about common network design patterns and automated deployment using Cloud Deployment Manager or Terraform. Google Cloud VPC Networking Fundamentals Recall that networks belong to projects. Explain the differences among default, auto, and custom networks. Create networks and subnets. Explain how IPv4 addresses are assigned to Compute Engine instances. Publish domain names using Google Cloud DNS. Create Compute Engine instances with IP aliases. Create Compute Engine instances with multiple virtual network. Controlling Access to VPC Networks Outline how IAM policies affect VPC networks. Control access to network resources using service accounts. Control access to Compute Engine instances with tag-based firewall rules. Sharing Networks across Projects Outline the overall workflow for configuring Shared VPC. Differentiate between the IAM roles that allow network resources to be managed. Configure peering between unrelated VPC Networks. Recall when to use Shared VPC and when to use VPC Network Peering. Load Balancing Recall the various load balancing services. Configure Layer 7 HTTP(S) load balancing. Whitelist and blacklist IP traffic with Cloud Armor. Cache content with Cloud CDN. Explain Layer 4 TCP or SSL proxy load balancing. Explain regional network load balancing. Configure internal load balancing. Recall the choices for enabling IPv6 Internet connectivity for Google Cloud load balancers. Determine which Google Cloud load balancer to use when. Hybrid Connectivity Recall the Google Cloud interconnect and peering services available to connect your infrastructure to Google Cloud. Explain Dedicated Interconnect and Partner Interconnect. Describe the workflow for configuring a Dedicated Interconnect. Build a connection over a VPN with Cloud Router. Determine which Google Cloud interconnect service to use when. Explain Direct Peering and Partner Peering. Determine which Google Cloud peering service to use when. Networking Pricing and Billing Recognize how networking features are charged for. Use Network Service Tiers to optimize spend. Determine which Network Service Tier to use when. Recall that labels can be used to understand networking spend. Network Design and Deployment Explain common network design patterns. Configure Private Google Access to allow access to certain Google Cloud services from VM instances with only internal IP addresses. Configure Cloud NAT to provide your instances without public IP addresses access to the internet. Automate the deployment of networks using Deployment Manager or Terraform. Launch networking solutions using Cloud Marketplace. Network Monitoring and Troubleshooting Configure uptime checks, alerting policies and charts for your network services. Use VPC Flow Logs to log and analyze network traffic behavior.

Tableau Desktop - Part 2
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for This course is designed for professionals in a variety of job roles who are currently using Tableau to perform numerical or general data analysis, visualization, and reporting. They need to provide data visualizations from multiple data sources, or combine data to show comparisons, manipulate data through calculations, create interactive visualizations, or create visualizations that showcase insights from statistical analysis. This course is also designed for students who plan to obtain Tableau Desktop Certified Associate certification, which requires candidates to pass the Tableau Desktop Certified Associate exam. Overview Blend data multiple sources. Join data. Access data in PDFs. Refine visualizations with sets and parameters. Analyze data with calculations. Visualize data with advanced calculations. Perform statistical analysis and forecasting. Create geographic visualizations. Get answers with Ask and Explain The advent of cloud computing and storage has ushered in the era of "big data." With the abundance of computational power and storage, organizations and employees with many different roles and responsibilities can benefit from analyzing data to find timely insights and gain competitive advantage. Data-backed visualizations allow anyone to explore, analyze, and report insights and trends from data. Tableau© software is designed for this purpose. Tableau was built to connect to a wide range of data sources and allows users to quickly create visualizations of connected data to gain insights, show trends, and create reports. Beyond the fundamental capabilities of creating data driven visualizations, Tableau allows users to manipulate data with calculations to show insights, make visualizations interactive, and perform statistical analysis. This gives users the ability to create and share data driven insights with peers, executives, and clients. Prerequisites Tableau Desktop: Part 1 Lesson 1: Blending Data from Multiple Sources Topic A: Blend Data Topic B: Refine Blends to Visualize Key Information Lesson 2: Joining Data Topic A: Create Joins Topic B: Troubleshoot Joins Topic C: Merge Data with Unions Lesson 3: Accessing Data in PDFs Topic A: Connect to PDFs Topic B: Clean Up and Organize PDF Data Lesson 4: Refining Visualizations with Sets and Parameters Topic A: Create Sets Topic B: Analyze Data with Sets Topic C: Apply Parameters to Refine Visualizations Topic D: Create Advanced Visualizations Lesson 5: Analyzing Data with Calculations Topic A: Create Calculated Fields to Analyze Data Topic B: Manipulate Data with Functions Topic C: Analyze Data with Table Calculations Lesson 6: Visualizing Data with Advanced Calculations Topic A: Create Groups and Bins with Calculations Topic B: Analyze Data with LOD Expressions Lesson 7: Performing Statistical Analysis and Forecasting Topic A: Perform Statistical Analysis Topic B: Forecast Data Trends Lesson 8: Creating Geographic Visualizations Topic A: Create Maps Topic B: Customize Mapped Data Lesson 9: Getting Answers with Ask and Explain Topic A: Ask Data Topic B: Explain Data Additional course details: Nexus Humans Tableau Desktop - Part 2 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Tableau Desktop - Part 2 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Certified Information Privacy Technologist (CIPT)
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Data Protection Officers IT Managers and Administrators Records Managers System Developers IT Security specialist Anyone who builds and develops IT systems Overview Critical data protection concepts and practices that impact IT Consumer data protection expectations and responsibility How to bake privacy into early stages of IT products and services for cost control, accuracy and speed-to-market How to establish data protection practices for data collection and transfer How to preempt data protection issues in the Internet of Things How to factor data protection into data classification and emerging tech such as cloud computing, facial recognition and surveillance How to communicate data protection issues with partners such as management, development, marketing and legal The Principles of Privacy in Technology training is the how to course on privacy and data protection practices in the development, engineering, deployment and auditing of IT products and services. Those taking the course will develop an understanding of privacy-related issues and practices in the context of the design and implementation of information and communication technologies and systems. The training is based on the body of knowledge for the IAPP?s ANSI accredited Certified Information Privacy Technologist (CIPT) certification program. Fundamentals of information privacy Reviewing the modern history of privacy Foundational privacy concepts Data protection roles and fair information practices Exploring the impacts of privacy and data protection regulations on information management Privacy in the IT environment Compliance requirements IT risks Stakeholder privacy expectations Differentiating between privacy and security Core privacy concepts Foundational elements for embedding privacy in IT Common privacy principles Data protection by design and default Privacy considerations in the information life cycle Privacy considerations throughout the stages of the information life cycle Privacy in systems and applications Examining the risks inherent in the IT environment and options for addressing them Identity and access management Credit card information and processing Remote access BYOD and telecommuting Data encryption Additional privacy-enhancing technologies in the enterprise environment Privacy techniques Strengths and weaknesses of authentication techniques Using identifiers Privacy by design Online privacy issues Unique challenges that come from online privacy issues Laws and regulations Online threats Social media E-commerce Tracking technologies Web security protocols Technologies with privacy considerations Privacy considerations associated with a variety of technologies Cloud computing Wireless IDs Location-based services ?Smart? technologies Video/data/audio surveillance Biometric recognition

PRINCE2 Agile Foundation: Virtual In-House Training
By IIL Europe Ltd
PRINCE2 Agile® Foundation: Virtual In-House Training PRINCE2 Agile® provides structure, governance, and control when working with agile concepts, methods, and techniques. It is a solution combining the flexibility and responsiveness of Agile with the clearly defined framework of PRINCE2. PRINCE2 Agile® framework covers a wide range of agile concepts, including SCRUM, Kanban, and Lean Startup. The PRINCE2 Agile® Foundation certificate is designed to help professionals deliver agile projects by tailoring PRINCE2® management controls with a broad toolset of agile delivery techniques and frameworks. PRINCE2 Agile® is an extension module tailored for forward-thinking organizations and individuals already benefiting from PRINCE2®. It provides further guidance on how to apply agile methods to the world's most recognized project management method. The purpose of the Practitioner qualification is to demonstrate that you can apply and tailor PRINCE2 Agile® in a scenario situation. What you will Learn Understand the key aspects of PRINCE2® Understand basic concepts behind common agile ways of working Demonstrate the purpose of combining PRINCE2® with agile Be able to fix and flex the aspects of a project in an agile context Apply the PRINCE2® principles and tailor the themes, processes, and management products to a project in an agile context Incorporate the areas that can support a PRINCE2 Agile® implementation To prepare Participants for the PRINCE2 Agile® Foundation exam Benefits Agile methods allow organizations to realize the benefits of products and potentially an earlier return on investment while products are being developed and improved. Improved communication through the use of common terminology across PRINCE2® and agile disciplines. Develop a clear definition of how agile can govern a project's delivery, while PRINCE2® governs projects as a whole. Seamless integration: PRINCE2 Agile® will complementPMBOK® GuideandAPM Body of Knowledge®just as PRINCE2® does currently. It will also be of interest for Program Managers with MSP® who need to understand how projects relate to the delivery mechanism. The most up-to-date and relevant view of Agile project management methodologies, PRINCE2 Agile® references the 'flow-based' working featured in Kanban in addition to other agile concepts not covered in other qualifications. Introduction - Getting Started Part 1 An overview of PRINCE2 Agile Overview Blending PRINCE2 and Agile What to fix and what to flex Part 2 Agile behaviors ad the PRINCE2 Principles Agile and the PRINCE2 Themes Part 3 Focus areas Agile and the PRINCE2 Processes Examination preparation Examination. Summary - What did we learn, and how can we implement this in our work environment?

Management of Risk (M_o_R) Practitioner: Virtual In-House Training
By IIL Europe Ltd
Management of Risk (M_o_R®) Practitioner: Virtual In-House Training The M_o_R® Practitioner course has been designed to provide learners with the opportunity to practice the practical application of the M_o_R method and covers the twelve M_o_R principles: Approach, Process and the basic techniques essential to managing risks using the M_o_R guidance. The purpose of the M_o_R Practitioner qualification is to confirm that the learner has achieved sufficient understanding of how to apply and tailor M_o_R in a scenario situation. What you will Learn At the end of the M_o_R Practitioner course, learners will gain competencies in: M_o_R framework (principles, approach based on risk documentation, process steps, and embedding and reviewing M_o_R principles Outline of M_o_R approach documents (including policy, process guide, and risk communications plan) Risk identification, assessment, and control Embedding and reviewing M_o_R M_o_R organizational perspectives (strategic, program, project, operational) Benefits The M_o_R Practitioner course offers a wide-ranging set of guidelines that will help in the management of risk in a project or program environment. It will help prepare learners for the M_o_R Practitioner Exam. They will feel more confident in approaching risk management after attending the course and will be aware of the use of different techniques that can assist in this task, including: Improved basis for effective strategy formation Reduced time spent fire-fighting and fewer unwelcome surprises Increased likelihood of successful change initiative outcomes Closer internal focus on doing the right things properly Increase in efficient use of resources waste and fraud Better management of contingency resources M_o_R roles and responsibilities M_o_R health check M_o_R maturity model Risk specialisms (including business continuity management) Introduction Introduction to the course What is a risk? What is risk management? Why is risk management so important? Basic risk definitions The development of knowledge about risk management Corporate governance and internal control Where and when should risk management be applied? M_o_R Principles The purpose of M_o_R principles Aligns with objectives Fits the context Engages stakeholders Provides clear guidance Informs decision-making Facilitates continual improvement Creates a supportive culture Achieves measurable value Risk management maturity models M_o_R Approach Relationship between the documents Risk management policy Risk management process guide Risk management strategy Risk register Issue register Risk response plan Risk improvement plan Risk communications plan M_o_R Process Common process barriers Identify - contexts Identify - the risks Assess - estimate Assess - evaluate Plan Implement Communication throughout the process M_o_R Perspectives Strategic perspective Programme perspective Project perspective Operational perspective Risk Specialisms Business continuity management Incident and crisis management Health and Safety management Financial risk management Environmental risk management Reputational risk management Contract risk management

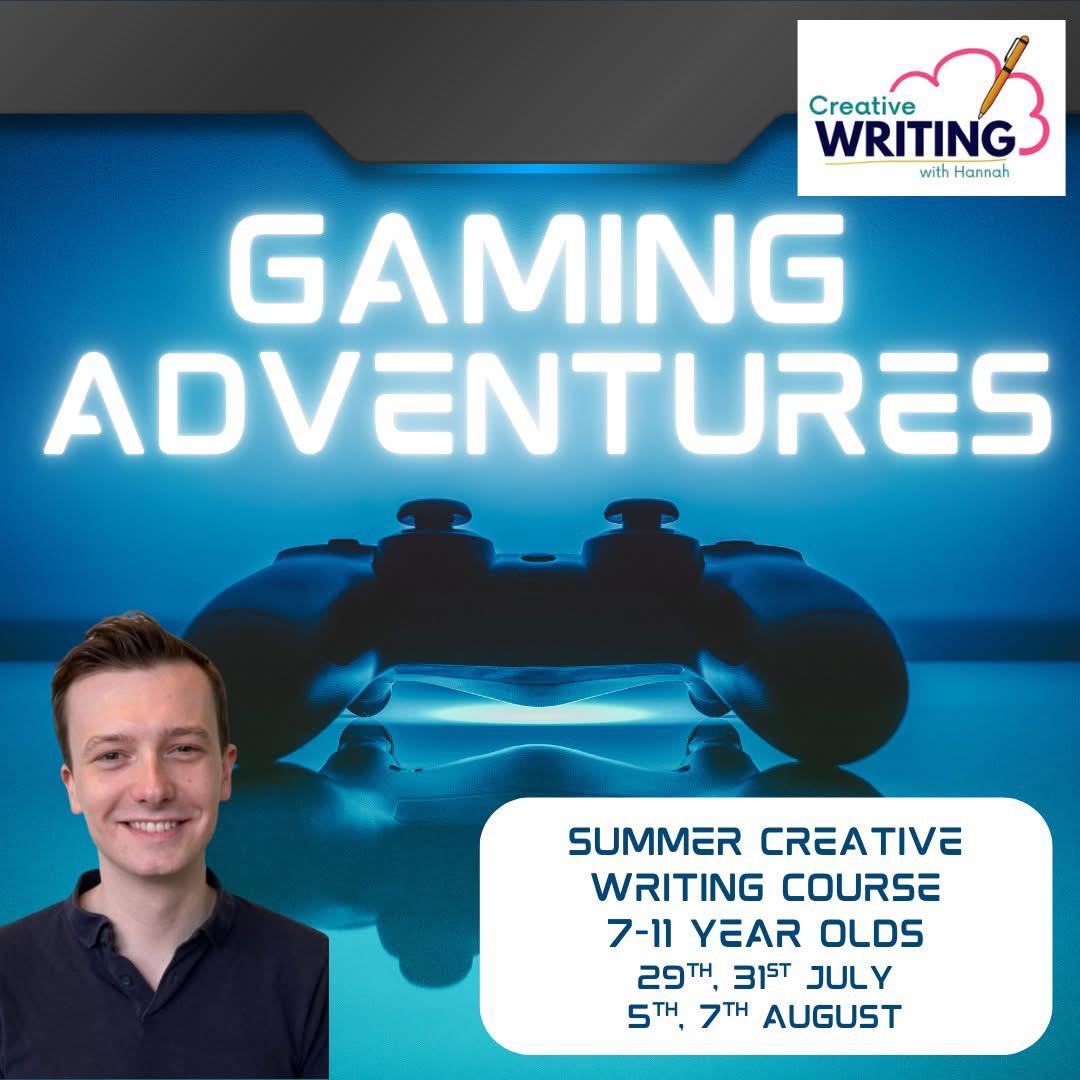
👾 Gaming Adventures (7-11 year olds)
By Creative Writing with Hannah
Calling all gamers! Is your favourite game Minecraft? Or do you have a different game in mind? Would your child enjoy writing game reviews or writing up their very own game design? Children will improve their English writing skills whilst engaging in their gaming interests. Teacher: William Please note: Lessons for this course will be on Tuesday 29th of July, Thursday 31st July, Tuesday 5th and Thursday 7th of August. Tuesdays and Thursdays at 10am UK/1pm UAE/5pm HK. If you cannot attend a lesson for any reason, Lauren will record it and send you a link to watch the sessions.
Petroleum Geology for Non-Geologists
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course To the non-geologist, working with Petroleum Geologists can be confusing. Petroleum geology has specific terminology and many concepts and data sources unfamiliar to the uninitiated. This course has been designed to introduce these terms and provide an insight into how oil and gas are formed, how they are found and how they are extracted. Using a holistic combination of lectures, experiments, case study and practical exercises, the course involves an introduction to fundamental geological concepts, to exploration techniques, prospecting, drilling, well logs and recovery methods. The course will also demystify the terminology surrounding petroleum geology, demonstrate the use of geological information to show the value and weakness of different datasets, and lead to better communication and decision-making between the geologists and non-geologists. It will feature world-class virtual reality field trips that incorporate activities and features unavailable in the physical field, and provide for a more integrated and flexible learning resource (also see the trainer's article on page 4 which was first published in GEO ExPro Magazine, the upstream oil and gas industry's favourite magazine). Course Highlights: Course facilitator has delivered petroleum geology training to many companies over the years Facilitator is also a professionally trained teacher and former university lecturer who is experienced in communicating with people at all levels of technical knowledge Practical exercises, experiments, examination of real rocks, a virtual reality field trip and case study are used to clarify and reinforce important concepts Training Objectives By attending this training, you will be able to acquire the following: Understand the geological methods and principles used in hydrocarbon exploration, development and production. Understand the key elements of a petroleum system, from hydrocarbon source to reservoir and seal Appreciate basin analysis, regional geology and play based exploration techniques Be aware of the different sorts of hydrocarbon trap from structural to stratigraphic Understand the technical terminology, tools and methods used in exploration geology Learn about unconventional Understand and evaluate the sources and reliability of various types of geological information Understand acquisition, processing and interpretation of seismic data Learn the technical processes and terminology involved in exploration Understand how a prospect is defined and risked Understand how seismic, existing well information and outcrop geology can be used for exploration Gain an understanding of the methods used for petroleum geology to allow a discovery to be appraised and then developed Target Audience The course is suitable to all personnel, but those that benefit most include: This course will benefit Petroleum Engineers (reservoir, drilling, production) who work with geological data, Geophysicists with little or no geological background, Project managers whose teams include petroleum geologists, Finance, Procurement, Marketing and Communications staff, and government Data Managers who handle petroleum geological data and need to understand the sources of different types of data. Trainer Your expert course leader is the Geosciences Technical Director for PetroEdge. She was previously, the manager of Robertson Petroleum Training Centre and a Senior Project Scientist at Robertson CGG. She has over 20 years of experience in teaching geology and leading field trips. Prior to her 8 years at Robertson, she was in academia as a lecturer for 6 years and a Research Fellow for 3 years. She has conducted fieldwork and led field trips in the US and many areas in the UK. In addition, she has led university regional geology day schools and has comprehensive experience in course and study programme writing. She has extensive experience in delivering courses and in Clastic and Carbonate Reservoir Geology, Deepwater Turbidites, Sandstone Reservoirs, Wireline Log Interpretation, Integrated Sequence Stratigraphy, Basin Analysis and Exploration & Appraisal workshops globally. In delivering the Exploration Team Management Workshop, she has project managed and taught key principles and modules on project planning, data collection/collation, geophysical assessment, stratigraphy and facies mapping, source rock facies and hydrocarbon generation, play fairway mapping, risking and prospect evaluation. Her knowledge and enthusiasm for instructing is reflected in consistently being rated as excellent by trainees, and clients specifically requesting her participation in courses. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

Neglect: Recognising and Responding to the Impact on Children
By Brightcore Consultancy
Join us for an insightful masterclass that delves into the profound effects of neglect on a child's life. This session is meticulously designed for professionals working closely with children in various educational settings, providing essential knowledge and practical tools to identify, manage, and seek support for neglected children.

Securing Cisco Networks with Open Source Snort (SSFSNORT) v2.1
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The primary audience for this course is as follows: Security administrators Security consultants Network administrators System engineers Technical support personnel Channel partners and resellers Overview Upon completing this course, the learner will be able to meet these overall objectives: Define the use and placement IDS/IPS components. Identify Snort features and requirements. Compile and install Snort. Define and use different modes of Snort. Install and utilize Snort supporting software. Securing Cisco Networks with Open Source Snort (SSFSNORT) v3.0 is a 4-day course that shows you how to deploy Snort© in small to enterprise-scale implementations. You will learn how to install, configure, and operate Snort in Intrusion Detection System (IDS) and Intrusion Prevention System (IPS) modes. You?ll practice installing and configuring Snort, utilize additional software tools and define rules to configure and improve the Snort environment, and more. The course qualifies for 32 Cisco Continuing Education credits (CE) towards recertification.This course will help you:Learning how to implement Snort, an open-source, rule-based, intrusion detection and prevention system. Gain leading-edge skills for high-demand responsibilities focused on security. Module 1: Detecting Intrusions with Snort 3.0 History of Snort IDS IPS IDS vs. IPS Examining Attack Vectors Application vs. Service Recognition Module 2: Sniffing the Network Protocol Analyzers Configuring Global Preferences Capture and Display Filters Capturing Packets Decrypting Secure Sockets Layer (SSL) Encrypted Packets Module 3: Architecting Nextgen Detection Snort 3.0 Design Modular Design Support Plug Holes with Plugins Process Packets Detect Interesting Traffic with Rules Output Data Module 4: Choosing a Snort Platform Provisioning and Placing Snort Installing Snort on Linux Module 5: Operating Snort 3.0 Start Snort Monitor the System for Intrusion Attempts Define Traffic to Monitor Log Intrusion Attempts Actions to Take When Snort Detects an Intrusion Attempt License Snort and Subscriptions Module 6: Examining Snort 3.0 Configuration Introducing Key Features Configure Sensors Lua Configuration Wizard Module 7: Managing Snort Pulled Pork Barnyard2 Elasticsearch, Logstash, and Kibana (ELK) Module 8: Analyzing Rule Syntax and Usage Anatomy of Snort Rules Understand Rule Headers Apply Rule Options Shared Object Rules Optimize Rules Analyze Statistics Module 9: Use Distributed Snort 3.0 Design a Distributed Snort System Sensor Placement Sensor Hardware Requirements Necessary Software Snort Configuration Monitor with Snort Module 10: Examining Lua Introduction to Lua Get Started with Lua
