- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
RACISM – ACKNOWLEDGING AND UNDERSTANDING
By Inclusive Solutions
In this course we deepen participants understanding of systemic racism and the spectrum of privilege. It challenges the participants to examine their behaviours and take close looks at some of the views they have held since a very young age, e.g. this area is a “bad” area, because it has a high proportion of black/brown people living in it, or that young black men in tracksuits are “thugs”. We think about where these messages come from and how people are indoctrinated by the media. Course Category Inclusion Team Building Leadership Emotional needs Description In this course we deepen participants understanding of systemic racism and the spectrum of privilege. It challenges the participants to examine their behaviours and take close looks at some of the views they have held since a very young age, e.g. this area is a “bad” area, because it has a high proportion of black/brown people living in it, or that young black men in tracksuits are “thugs”. We think about where these messages come from and how people are indoctrinated by the media. We explore the reasons why white people are so defensive when it comes to talking about race. We discuss having racial biases and the implications of them, such as unconsciously insulting people around us in the workplace. When we become aware of how our behaviours can affect people, we then look for solutions. The course is designed for groups of professionals to come together as a team to try and take responsibility for the racism that goes on in their workplace – empowering the leadership to have difficult conversations with team members and create a paradigm shift across the entire organisation. Please come with an open mind, and you might be surprised at what you find out. We are striving for a world where racism is an open conversation and not a topic that we shy away from. Testimonials “That was a really insightful session and thought provoking. I would love to attend more sessions on racism. Thank you for the engaging questions and delivery” “Lots of things to reflect on!” Learning Objectives Participants will: Confront their own racism and unconscious biases Become aware of the ways they treat people differently based on race Think about practical changes they can make in their workplaces Who Is It For? Leadership teams seeking guidance and reflection Educators who want to get it right People who have had not had much contact with people outside their own race People who believe they are “not racist” Course Content Background – brief history of systemic racism Racism as a binary – the problem with thinking only “bad” people can be racist Trust – how do we feel around people we don’t trust? Difference – how do we act when we feel different? What do Good Manners look like around people of different cultures? What does Good Allyship look like in the workplace? Why don’t we talk about race? What does your race mean to you? Examining our privilege – activity Interracial friendship video Visioning – what does the ideal workplace look like? Setting Actions – what achievable actions can we set to bring us closer to our dream future?

Boost your team's performance through better communication!
By Culture Fit Consulting Ltd
This interactive 3-hour webinar is designed for teams who want to understand one another’s behavioural style and improve how the team interacts. Using the DISC framework, we'll uncover how people think, behave, and work differently. Participants will understand their own behavioural style and its impact on others. We'll explore how different styles prefer to communicate and collaborate, and how to adapt our messages to team members with diverse working styles and communication preferences.
In this competitive job market, you need to have some specific skills and knowledge to start your career and establish your position. This Entrepreneurs Business Planning course will help you understand the current demands, trends and skills in the sector. The course will provide you with the essential skills you need to boost your career growth in no time. The Entrepreneurs Business Planning course will give you clear insight and understanding about your roles and responsibilities, job perspective and future opportunities in this field. You will be familiarised with various actionable techniques, career mindset, regulations and how to work efficiently. This course is designed to provide an introduction to Entrepreneurs Business Planning and offers an excellent way to gain the vital skills and confidence to work toward a successful career. It also provides access to proven educational knowledge about the subject and will support those wanting to attain personal goals in this area. Learning Objectives Learn the fundamental skills you require to be an expert Explore different techniques used by professionals Find out the relevant job skills & knowledge to excel in this profession Get a clear understanding of the job market and current demand Update your skills and fill any knowledge gap to compete in the relevant industry CPD accreditation for proof of acquired skills and knowledge Who is this Course for? Whether you are a beginner or an existing practitioner, our CPD accredited Entrepreneurs Business Planning course is perfect for you to gain extensive knowledge about different aspects of the relevant industry to hone your skill further. It is also great for working professionals who have acquired practical experience but require theoretical knowledge with a credential to support their skill, as we offer CPD accredited certification to boost up your resume and promotion prospects. Entry Requirement Anyone interested in learning more about this subject should take this Entrepreneurs Business Planning course. This course will help you grasp the basic concepts as well as develop a thorough understanding of the subject. The course is open to students from any academic background, as there is no prerequisites to enrol on this course. The course materials are accessible from an internet enabled device at anytime of the day. CPD Certificate from Course Gate At the successful completion of the course, you can obtain your CPD certificate from us. You can order the PDF certificate for £4.99 and the hard copy for £9.99. Also, you can order both PDF and hardcopy certificates for £12.99. Career path The Entrepreneurs Business Planning will help you to enhance your knowledge and skill in this sector. After accomplishing this course, you will enrich and improve yourself and brighten up your career in the relevant job market. Course Curriculum Introduction to Business Plan for Entrepreneurs Business Plan for Entrepreneurs Achieve Your Short & Long Term Goals preview 00:04:00 Module 01: Things to Consider Before Starting a Business Plan Things to Consider Before Starting a Business Plan 00:04:00 Lesson 01 Identify Your Skills 00:04:00 Lesson 02 Audit the Market Demand of Your Idem 00:04:00 Lesson 03 Check for Availability of Resources 00:04:00 Lesson 04 Work on a Financial Plan 00:03:00 Lesson 05 Be Ready to Face Failure 00:03:00 Module 02: The Elements of a Business Plan The Elements of a Business Plan 00:03:00 Lesson 01 Mission Statement (Company Overview) 00:04:00 Lesson 02 Marketplace Opportunity 00:05:00 Lesson 03 Product/Service Information 00:04:00 Lesson 04 Sales/Market Plan 00:04:00 Lesson 05 Financials 00:04:00 Module 03: Who Are You Writing the Business Plan For Who Are You Writing the Business Plan For 00:04:00 Lesson 01 You Want to Start a Business 00:03:00 Lesson 02 You Own an Established Firm and are Seeking Help 00:04:00 Lesson 03 You Need to Determine Your Objectives 00:04:00 Lesson 04 You're Trying to Predict the Future 00:04:00 Lesson 05 You Want to Use it to Raise Money 00:03:00 Module 04: The Purpose of a Business Plan The Purpose of a Business Plan 00:03:00 Lesson 01 Provide a Road Map 00:04:00 Lesson 02 Understand What to Focus On 00:04:00 Lesson 03 Raise finance 00:04:00 Lesson 04 Manage your Business Effectively 00:04:00 Lesson 05 Enlightening Executive Talent 00:04:00 Module 05: How a Business Plan Can Help with Long Term Success How a Business Plan Can Help with Long Term Success 00:04:00 Lesson 01 A Business Plan Is Simply a Must-Have for Some Businesses 00:05:00 Lesson 02 A Business Plan Helps You Make Decisions 00:03:00 Lesson 03 A Business Plan Can Be a Reality Check 00:05:00 Lesson 04 A Business Plan Can Give You New Ideas 00:05:00 Lesson 05 A Business Plan Creates an Action Plan 00:03:00 Module 06: Reasons You Need a Business Plan Reasons You Need a Business Plan 00:04:00 Lesson 01 Gain a Deep Understanding of Your Market 00:03:00 Lesson 02 Hold Yourself Accountable 00:04:00 Lesson 03 Know Your Message 00:05:00 Lesson 04 Confirm the Math 00:06:00 Lesson 05 Iron Out Possible Kinks 00:04:00 Module 07: Conclusion Review 00:03:00 Certificate and Transcript Order Your Certificates or Transcripts 00:00:00

Managing tribes in Social Media Marketing
By Study Plex
Recognised Accreditation This course is accredited by continuing professional development (CPD). CPD UK is globally recognised by employers, professional organisations, and academic institutions, thus a certificate from CPD Certification Service creates value towards your professional goal and achievement. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. What is CPD? Employers, professional organisations, and academic institutions all recognise CPD, therefore a credential from CPD Certification Service adds value to your professional goals and achievements. Benefits of CPD Improve your employment prospects Boost your job satisfaction Promotes career advancement Enhances your CV Provides you with a competitive edge in the job market Demonstrate your dedication Showcases your professional capabilities What is IPHM? The IPHM is an Accreditation Board that provides Training Providers with international and global accreditation. The Practitioners of Holistic Medicine (IPHM) accreditation is a guarantee of quality and skill. Benefits of IPHM It will help you establish a positive reputation in your chosen field You can join a network and community of successful therapists that are dedicated to providing excellent care to their client You can flaunt this accreditation in your CV It is a worldwide recognised accreditation What is Quality Licence Scheme? This course is endorsed by the Quality Licence Scheme for its high-quality, non-regulated provision and training programmes. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. Benefits of Quality License Scheme Certificate is valuable Provides a competitive edge in your career It will make your CV stand out Course Curriculum How to create tribes on social media Understanding Community Management 1.1 00:03:00 Why Should We Build Our Own Community 1.2 00:07:00 Create online tribes How to Create your Great Strategy 2.1 00:10:00 Using social media to build your community.2.2 00:07:00 Best Practices for Community Building 2.3 00:07:00 Growing your tribes on social media Creating content keeps your tribes alive.3.1 00:10:00 How to increase active participation in your communities.3.2 00:07:00 How to find brand ambassadors and influencers.3.3 00:07:00 How to promote your community.3.4 00:08:00 Measuring their success and performance How to scale your community.4.1mov 00:08:00 How to measure the growth of your fans.4.2 00:07:00 Demonstrate your influence in communities as a leader.4.3 00:05:00 Tools for managing audiences and communities Very good use of tools for community management.5.1mov 00:04:00 Welcome to the world of marketing where short video is king Modern digital marketing strategies1.1 00:05:00 The role of short-form video in social media marketing1.2 00:08:00 Techniques to create strong short-form video1.3 00:08:00 Digging deeper TikTok1.4 00:08:00 Digging deeper Instagram Reels1.5 00:05:00 Effective marketing strategies for TikTok videos Top Strategies for Creating Effective TikToks2.1 00:08:00 Understanding the TikTok algorithm2.2 00:08:00 Using hashtags effectively2.3 00:08:00 Capitalizing on trends and challenges2.4 00:08:00 Leveraging influencers2.5 00:08:00 Creating ads2.6 00:07:00 Using other TikTok tools and techniques2.7 00:06:00 Effective marketing strategies for instagram reels Connections between Reels and TikTok strategies3.1 00:07:00 Understanding the unique selling points of Instagram Reels.3.2 00:07:00 Implementing your social strategy for TikTok and Reels3.3 00:03:00 Creating a social media roadmap Set your goals.1.1 00:05:00 Define Your Target Audience.1.2 00:05:00 Choosing the most successful social networks Invest in smart channels.2.1 00:05:00 The most successful social networks.2.2 00:05:00 Social Networks for Message and Chat.2.3 00:05:00 Very important niche social networks.2.4 00:05:00 Great social media posting models How we can create great messages.3.1 00:05:00 Manage by setting a great calendar.3.2 00:05:00 Managing ads on social media.3.3 00:05:00 Effective sustainable communication with customers Achieve success with the masses by Building communities.4.1 00:05:00 Importance of customer service in social media.4.2 00:05:00 How can we turn social media into sales? Strengthen sales by directly supporting.5.1 00:07:00 Developing business by partnering with Influencers.5.2 00:04:00 Measuring social media in the most efficient way Connecting social networks with goals.6.1 00:05:00 Constantly making the best improvements to social media More than being active.7.1 00:05:00 Bring Great Apps to Life 7.2 00:05:00 Good understanding of content Content means too much.1.1 00:03:00 Content is more than all blogs and articles 1.2 00:02:00 Content is more than a cost understanding 1.3 00:02:00 Understand content marketing Understand Content Marketing 2.1 00:04:00 Where did This Content Marketing Come From 2.2 00:07:00 What is the Main Purpose of Content Marketing 2.3 00:04:00 Advanced goals of content marketing 2.4 00:04:00 Details for successful content marketing How to grow the niche content audience 3.1 00:04:00 Understanding a Different Brand Perspective 3.2 00:04:00 Presenting content experiments 3.3 00:05:00 Actively understanding content 3.4 00:03:00 Developing a successful content marketing strategy Forget what you know 4.1 00:04:00 Choosing the right audience 4.2 00:04:00 Our competitive analysis priority 4.3 00:04:00 Understand Your Right to Win 4.4 00:03:00 How we can create and source effective content Creating content on the customer journey 5.1 00:05:00 Choosing content marketing formats and channels 5.2 00:04:00 Source from anywhere 5.3 00:04:00 Making content very effective 5.4 00:04:00 Grow content operations Choosing a content calendar 6.1 00:04:00 Understand Content Processes 6.2 00:04:00 Clarifying roles and responsibilities 6.3 00:05:00 Content operations that come to life 6.4 00:03:00 Create advanced intelligence for content Selecting content KPIs 7.1 00:05:00 Monitoring content KPI data 7.2 00:05:00 Optimizing content performance regularly 7.3 00:06:00 Using content technology by constantly renewing it Finding content technology 8.1 00:03:00 Considering advanced content technology 8.2 00:04:00 Developing strategy for content technology 8.3 00:03:00 Seize content marketing opportunities Scaling Content Marketing 9.1 00:03:00 Succeeding as a Small Business 9.2 00:03:00 Succeed as a Large or Corporate Business 9.3 00:03:00 Instagram Profile Setup and Orientation Tour the Instagram user Interface 1.1 00:06:00 Convert to an Instagram Professional Account 1.2 00:04:00 Optimizing your Professional Instagram Profile 1.3 00:04:00 Optimizing Uploads of Photos and Videos 1.4 00:05:00 Modify Instagram Settings 1.5 00:04:00 Using Instagram on a Computer 1.6 00:02:00 Get Started with Marketing on Instagram Explore Models of Business Success 2.1 00:05:00 Built-in Tools for Marketing 2.2 00:04:00 Interact with the Community to Build Trust 2.3 00:05:00 Develop a Marketing Strategy for Instagram Content Ideas and Strategies for Instagram 3.1 00:05:00 Create a Unique Style on Instagram 3.2 00:04:00 Research your Competition on Instagram 3.3 00:04:00 Utilize Hashtags With a Posting Schedule 3.4 00:05:00 Implement Your Instagram Marketing Campaign Marketing with Instagram Stories 4.1 00:04:00 Marketing with Instagram Reels 4.2 00:04:00 Marketing With IGTV 4.3 00:05:00 Marketing With Live Video on Instagram 4.4 00:05:00 Using Instagram Shopping Posts 4.5 00:04:00 Content Marketing with Instagram Guides 4.6 00:04:00 Leveraging Instagram Paid ads 4.7 00:05:00 Optimize Your Marketing Strategy on Instagram Review Instagram Insights to Optimize Marketing Strategy 5.1 00:05:00 Run Polls and ask Questions on Instagram 5.2 00:05:00 Saving Instagram Stories as Story Highlights 5.3 00:04:00 Embedding Instagram Photos into Websites 5.4 00:02:00 Useful Instagram Enhancement Platforms 5.5 00:05:00 Additional Resources 5.6 00:02:00 Live Video Styles Live Educational Videos 1.1 00:05:00 Live Interview Videos 1.2 00:04:00 Live Demo Videos 1.3 00:04:00 Live Video Tours 1.4 00:04:00 Creating Live Video Content When to Create Live Video 2.1 00:04:00 Different live video platforms 2.2 00:05:00 Preparing for Your Live Video 2.3 00:03:00 Introductions and Conclusions in Your Live Video 2.4 00:05:00 Creating Engagement During Live Videos 2.5 00:03:00 Promoting Your Live Video Building your Live Video Audience 3.1 00:05:00 Sharing Your Live Video 3.2 00:05:00 Repurposing your Live Video 3.3 00:04:00 Launching Live Video Tools for Live Video 4.1 00:04:00 Visuals for Live Video 4.2 00:04:00 Start Creating Live Videos 4.3 00:01:00 Story Basics How Stories Connect 1.1 00:06:00 Story Types to Grow 1.2 00:07:00 Good Story Qualities 1.3 00:07:00 Building a Story Finding Your Story 2.1 00:05:00 Your Audience 2.2 00:04:00 Call to Action 2.3 00:06:00 Telling a Story Story Structure 3.1 00:06:00 Grabbing Attention 3.2 00:05:00 Deep Engagement 3.3 00:08:00 Growing Community 3.4 00:04:00 Interactive Stories 3.5 00:05:00 More More Material 4.1 00:03:00 Interview 4.2 00:03:00 Core Values 4.3 00:03:00 Connect Before Convincing 4.4 00:03:00 Crowdfunding 4.5 00:03:00 How to Start Your Story 4.6 00:03:00 Tell Stories in Person 4.7 00:03:00 Obtain Your Certificate Order Your Certificate of Achievement 00:00:00 Get Your Insurance Now Get Your Insurance Now 00:00:00 Feedback Feedback 00:00:00

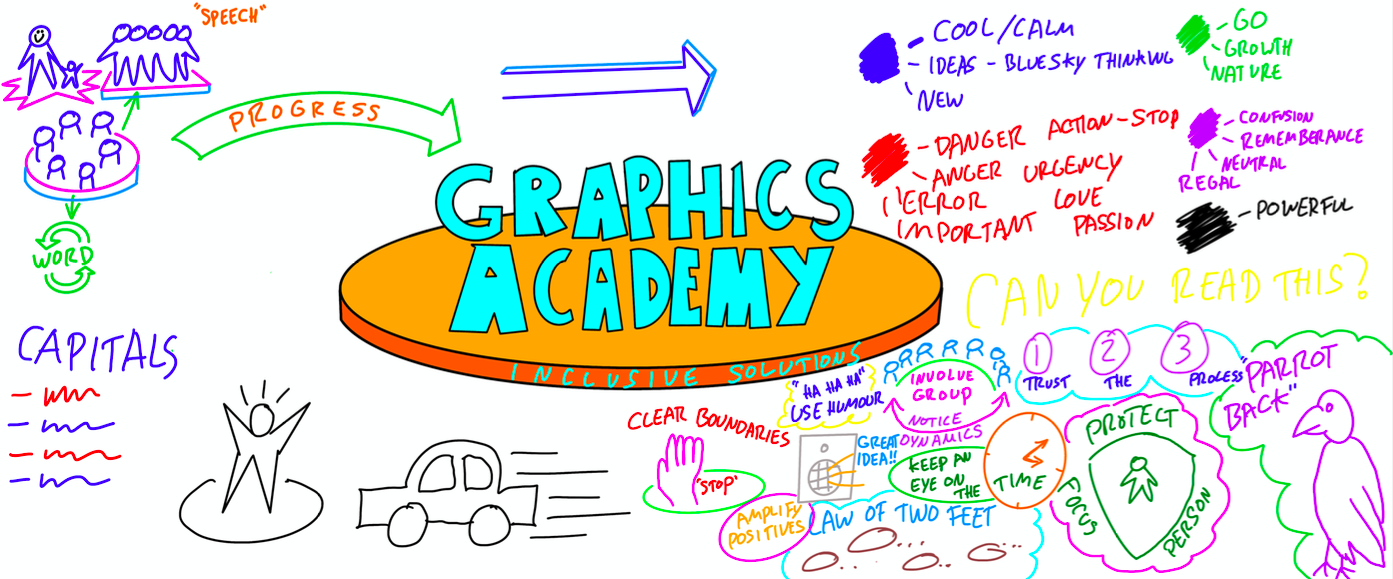
GRAPHIC FACILITATION – AN INTRODUCTION
By Inclusive Solutions
This day will introduce you to the basic techniques and skills involved in doing graphic facilitation. Learn how to use a BIG piece of paper and a handful of pens to create a memorable summary of your training day, team meeting or your work with young people and families. Learn how to harvest the essence of an event in a visual representation. This is a ‘hands on’ interactive day built around demonstrations of graphic facilitation, coaching and the chance to try things out. Ideal for teams who can then go on together to practice, practice, practice. Learning Objectives To introduce you to the basic skills of graphic facilitation – no previous experience is needed To develop your capacity to ‘listen under the words’ and draw out the deeper messages To help you suspend your self-doubt – “I can’t draw!” and rediscover your capacity to create an effective visual representation of a meeting/training day/conversation etc Course Content The day will introduce you to the fundamentals of graphic facilitation and will include the following topics: Pens, Pastels and Paper – what you will need to get started The basic ‘grammar’ of graphic facilitation; the essential shapes, using colour, images, lettering, words, creating connection How to listen for the essence of what is being said and translate this into visual language A chance to do it live – with coaching
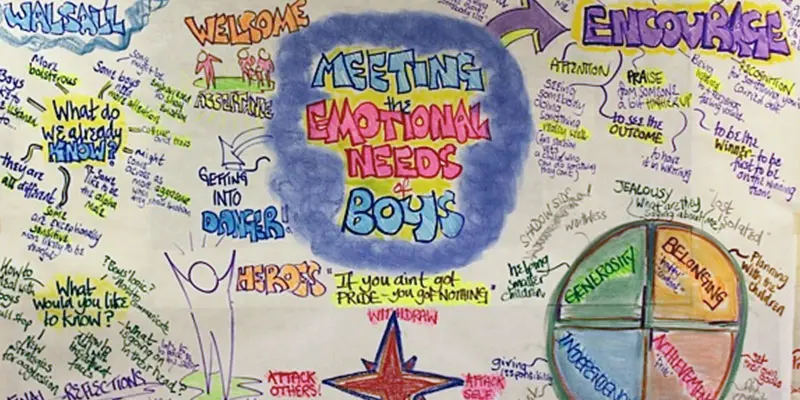
BOYS’ EMOTIONAL NEEDS
By Inclusive Solutions
This workshop gives an opportunity to focus on the emotional needs of boys and how to meet these. We lift the lid on an emerging urgent inclusion issue,namely meeting the emotional needs of boys. Everyone knows a boy. They may be pupil, son, brother, parent or partner. Boys when they become adults are over represented in the prison, and mental health system. Course Category Meeting emotional needs Description This workshop gives an opportunity to focus on the emotional needs of boys and how to meet these. We lift the lid on an emerging urgent inclusion issue,namely meeting the emotional needs of boys. Everyone knows a boy. They may be pupil, son, brother, parent or partner. Boys when they become adults are over represented in the prison, and mental health system. In one recent year 1300 young men committed suicide in the UK. In the UK the commonest cause of death among those aged 16-35 is suicide. Three men for every one woman kill themselves every year (Guardian, June 2006). 1 in 4 women experience domestic violence and 2 women a week are killed by a current or ex partner. Boys and men are a major concern. We need to find ways to allow them to unclench their hearts and learn to experience, process, communicate and manage their own emotional lives for their own and for the good of the wider community. Testimonials ‘Thanks for a super day, lots of good ideas for our citizens of the future. We need to offer them the best and what we would offer our own children’?? ‘Enjoyed the day very much. Brilliant ideas and lots of food for thought. Will use the solution circle. A great tool!’ ‘went well and the ethos/participation was commendably facilititated. well done’. ‘Wonderful day!’ ‘Still getting lots of positive messages this end.’ Learning Objectives Increased understanding of boys’ emotional needs Access to a wider range of practical strategies to impact on meeting emotional and behaviour problems Deeper understanding of core values surrounding inclusion of boys Opportunity to reflect on professional attitudes and behaviour towards boys and their emotional challenges New skills and processes to make boys’ inclusion and achievement more successful Who Is It For ? Early years and school based practitioners Key workers Teaching Assistants with support roles Heads and deputies SENCOs Advanced skills teachers Primary and secondary classroom teachers Parents Local authority support services Course Content The course explores the questions : Is there a problem with boys? What can we do to meet the emotional needs of boys? What helps? What should our priority be with boys? This workshop will explore: Cultural and historical expectations of boys in our society Shared experiences of teaching and parenting boys Circle of Courage as away of understanding emotional needs Fathers, mothers and sons Drinking and drugs: filling the emotional void Depression and suicide Anger and violence Solution Circle Problem Solving around boys needs What boys really need
BABY PROJECT – WORKING WITH BABIES TO INCREASE EMPATHY
By Inclusive Solutions
This radical way of building empathy is inspired by the work of the ‘Roots of Empathy’ organisation in Canada. Roots of Empathy (ROE) is dedicated to building caring and peaceful societies through the development of empathy in children. It is a parenting education programme for elementary school students (between the ages of 3 to 14 years) based on monthly visits to the classroom by a parent and infant from the school neighbourhood. Course Category Behaviour and Relationships Autism and Communication Meeting emotional needs Description This radical way of building empathy is inspired by the work of the ‘Roots of Empathy’ organisation in Canada. As Mary Gordon founder of this way of working describes: ‘By regular visits to the classroom of local mums and their children build an empathic relationship with the baby.MARY GORDON Roots of Empathy (ROE) is dedicated to building caring and peaceful societies through the development of empathy in children. It is a parenting education program for elementary school students (between the ages of 3 to 14 years) based on monthly visits to the classroom by a parent and infant from the school neighbourhood. We teach teachers and educators to help children to observe, over the school year, how their baby forms an attachment to his or her parent. Children are encouraged to record how the infants develop. The children learn to spot their babies cues and unique temperament, while celebrating developmental milestones. Children are prepared for responsible and responsive parenting as they increase their knowledge about human development, learning, and infant safety. The baby project program brings about the development of empathy and emotional literacy: As children learn to take the perspective of others they are less likely to hurt through bullying, exclusion, aggression, and violence. Children learn how to challenge cruelty and injustice in their own classroom. Messages of social inclusion and activities that are consensus-building contribute to a culture of caring that changes the tone of the classroom. Involving fathers and men provides rich models of male nurturance Testimonials ‘13% increase in empathy scores for our year 1s’ ‘Years 2s empathy had increased by 35%’ ‘Now that I am older I can be happy for other people’ (6 year old) ‘Everyone is special – thats the truth – but when I was small I thought its not fair when someone got a present and I didn’t’ (7 year old) Dramatic improvements in children taking responsibility for actions and being less defiant over the year of the project. Learning Objectives Understanding of method and approach to building empathy with babies Full understanding of background to this approach Practical advice received as to how to set up baby project in classrooms across school Who Is It For ? Teachers School leaders Project Coordinators Social Care Course Content We will provide theoretical and evidence back ground to impact of this work. We will describe existing UK school based work. We will inspire staff in attendance to want to actively engage in this work There may even be a baby to hold!!

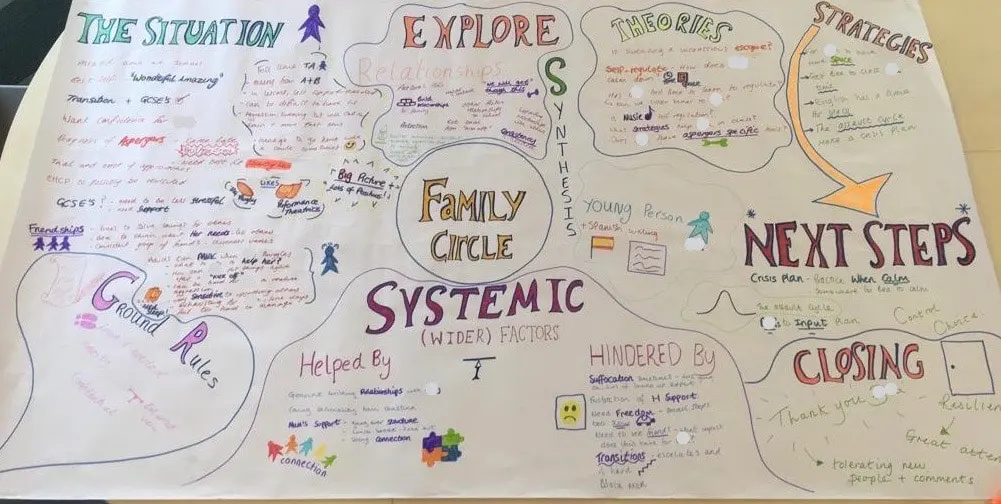
FAMILY CIRCLES
By Inclusive Solutions
Click to read more about this training, in which we demonstrate a live problem solving approach which is based on the active participation of family members. Course Category Inclusion Parents and Carers Behaviour and relationships Problem Solving Description In this training we demonstrate a live problem solving approach which is based on the active participation of family members. ‘Family Circles’ is an evolving new approach to problem solving with families and is based on our years of family work and the development and use of the Circle of Adults process. Inspired by our own Parent Solutions work and the Circle of Adults process as well as Family Group Conferencing and other Restorative Interventions we bring you Family Circles. Essentially the approach involves gathering a family together for a process that is facilitated but majors on the family members offering each other their wisdom and ideas. The approach is capacity focused, person centred approach to working with families rather than the dominant deficit oriented and ‘medical model’ of viewing and planning for or doing things to families. This training can be modelled with a group of professionals or better still with a family. In our work with families we develop the importance of naming stories or theories and seeking linkages and synthesis between what is found out and explored about the family situation and its history. We like participants to sit with the uncertainty, to reflect on the question ‘why’ but without judgement of each other. Deeper reflections may span a whole range of perspectives from ‘within person’ considerations, to situational or systemic possibilities. Health or emotional issues can be reflected on alongside organisational or transactional aspects of what is going on for the family. The better the shared understanding the better the strategy or actions which emerge from these meetings. Quality hypotheses with a close fit to reality lead to more effective implementation in the real world. We encourage ‘loose’ thinking, a search for connections, deeper listening, an ‘open mind’, speculation and exploration without moral judgements. From this stance self-reflection as well as reflection on the situation can produce remarkable insights. The quality of theories or new stories generated is directly influenced by family members’ experiences and the models of learning, behaviour and emotion, systems, educational development, change and so on that they have been exposed to. Learning Objectives To provide opportunities for: Shared problem solving in a safe exploratory climate in which the family will find its own solutions. Individuals to reflect on their own actions and strategies An exploration of whole-family processes and their impact Emotional support and shared understandings of issues at a child, parent, family, school and community level. Feed back to each other on issues, ideas and strategies that are agreed to be worth sharing with them. Who Is It For? Anyone interested in working with families in a way that builds and makes use of their capacities rather than focus on their challenges and difficulties. Social Care teams School staff Community organisers Educational Psychologists Course Content True family empowerment Deepening shared stories and understandings Facilitating groups Problem solving process Handling family group communication Allowing direct feedback and challenge between participants in a safe way Building relationships Process: Family members are welcomed: Introductions are carried out, ground rules and aims clarified whilst coffee is drunk. A recap from the last session is carried out: To follow up developments and reflections after the last meeting. One issue is selected for the main focus Issue presentation: The family member who raised the concern is asked questions to tell the ‘story’ of the issue or problem. Additional questions/information from the group about the problem are gathered: Ground rules may need to be observed carefully here. Individual participants need to be kept focused and prevented from leaping to premature conclusions or to making ‘helpful’ suggestions about strategy. Relationship aspects to the problem are explored. Metaphors and analogies are invited. How would a fly on the wall see your relationship? If you were alone together on a desert island, what would it be like? Impact of previous relationships/spillage from one relationship to another are explored. Eg what situation they are reminded of? For instance, does this situation remind you of any of those angry but helpless feelings you had with your other son when he was an adolescent? This provides opportunities to reflect on how emotions rub off on other people. The parent feels really frustrated, and on reflection we can see that so does the child System/Organisation factors (Family system/school and community systems and so on): What aspects help or hinder the problem? For instance, does the pastoral system of the local school provide space, or time and skilled personnel able to counsel this young person and work actively with their parents? Synthesis. At this stage the Graphic facilitator summarises what they have heard. They then go on to describe linkages and patterns in what they have heard. This can be very powerful. The person doing the graphic work has been able to listen throughout the presentation process and will have been struck by strong messages, emotions and images as they have arisen. The story and meaning of what is happening in the situation may become a little clearer at this point. Typical links may be ‘mirrored emotions’ strong themes such as loss and separation issues, or repeated processes such as actions triggering rejection. This step provides an excellent grounding for the next process of deepening understanding. What alternative strategies/interventions are open to be used? Brainstormed and recorded. ’Either/ors’ need to be avoided at this time also. This needs to be a shared session in which the family member who is presenting the concern contributes as much as anyone. Care is needed to ensure that this person is not overloaded with other people’s strategies. The final selection of strategy or strategies from the brainstormed list is the problem presenter’s choice. Strategies might include: a special time for the young person, a meeting with the child’s parents to explore how she is being managed at home and to share tactics, a home-school diary, counselling, or an agreed action plan that all are aware of, agreed sanctions and rewards and so forth. Strategies may productively involve processes of restitution and restoration, when ‘sorry’ is not enough. Making it right, rather than punishments or rewards, may then becomes the focus. First Steps. The problem presenter is finally asked to agree one or two first steps which they can carry out over the next 3-7 days. It can help to assign a ‘coach’ who will check in with them to ensure they have carried out the action they have named. This is a time to be very specific. Steps should be small and achievable. The person is just ‘making a start’. A phone call, or making an agreement with a key other person not present at the meeting would be ideal examples. Final reflections. Sometimes referred to as a ‘round of words’ help with closure for all involved. Reflections are on the process not the problem. In large families this is best done standing in a circle. In smaller groups all can remain sitting. Passing around a ‘listening stick’ or something similar such as a stone or light heighten the significance of the process ending and improve listening. Finally the problem presenter is handed the ‘Graphic’ this is their record of the meeting and can be rolled and presented ceremoniously by the facilitators for maximum effect! If you liked this course you may well like: Parent Solutions
React Bootcamp with .NET API (Router, Redux Toolkit, Hooks)
By Packt
This comprehensive course is designed to take you on a journey of mastering React, the popular JavaScript library for building dynamic user interfaces, and combining it with the power of .NET API for seamless back-end integration. This course will provide you with a solid foundation and hands-on experience in building full-stack applications.