- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
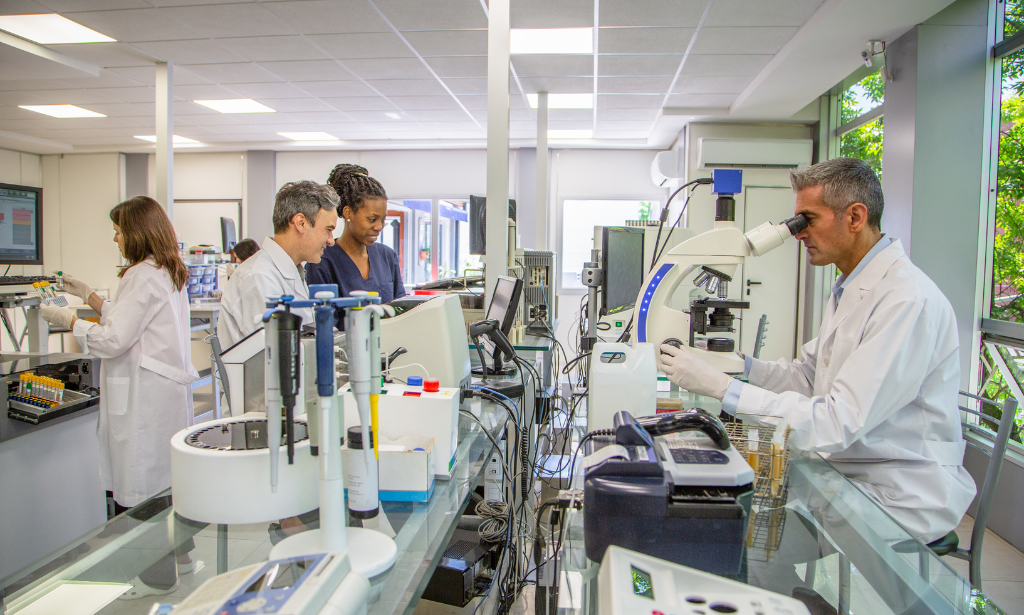
Enhance your career in healthcare with the Laboratory Expert Diploma. This comprehensive online course covers essential topics for aspiring Lab Technicians, including laboratory services, equipment operation, and safety protocols. Gain practical skills and earn a CPD certificate upon completion.
Bloodborne Pathogens
By Course Cloud
Step into the world of bloodborne pathogens: a complete journey, covering everything with our dynamic online course.
Learn how to establish and enforce security policies and procedures in the workplace with the Security Officer Training Course. This security risk management program is ideal for beginners who are new to this field. You will get a complete overview of the role and responsibilities of a security officer, and on completion, will be equipped with the skills and knowledge to kick-start your career. Throughout this security management course, you will explore the basic principles of security and the fundamental principles of security governance. You will also develop your understanding of the different types of crimes, prevention strategies and organisation security models. Learning Outcomes of The Security Officer Training Course: Understand the basics of security management, planning and implementing Explore the fundamental principles of security governance and the accountability framework Expand your knowledge of the different types of crimes and crime prevention tactics Familiarise with the role and responsibilities of a security office Learn about the different types of organisational security models Get a detailed overview of security risk management and how to conduct a risk assessment Understand how to effectively manage and report cases of domestic and sexual violence in the workplace Explore prevention strategies for domestic and violent abuse Why choose this course Earn an e-certificate upon successful completion. Accessible, informative modules taught by expert instructors Study in your own time, at your own pace, through your computer tablet or mobile device Benefit from instant feedback through mock exams and multiple-choice assessments Get 24/7 help or advice from our email and live chat teams Full Tutor Support on Weekdays Course Design The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of Video lessons Online study materials Mock exams Multiple-choice assessment Certification After the successful completion of the final assessment, you will receive a CPD-accredited certificate of achievement. The PDF certificate is for £9.99, and it will be sent to you immediately after through e-mail. You can get the hard copy for £15.99, which will reach your doorsteps by post.

Leadership Management & Team Leader - Level 7 Advanced Diploma
4.7(47)By Academy for Health and Fitness
24 Hours Left! Don't Let the Winter Deals Slip Away - Enrol Now! Strong leaders are the foundation of any successful business. A Leader can make or break a team, so enhancing or solidifying your leadership skills is crucial to being the best leader you can be. Around 49% of all employees in the UK at some point quit their jobs because of their lack of Leadership and management. With step-by-step instructions from our Leadership & Management Level 7 Advance Diploma, you will avoid all the mistakes that most managers/ leaders make and become an ideal leader who inspires, motivates & achieves goals by properly managing employees. This Advanced Diploma in Leadership & Management at QLS Level 7 course is endorsed by The Quality Licence Scheme & Accredited by CPD (with 250 CPD points) to make your skill development & career progression more accessible than ever! The Leadership & Management Level 7 Advanced Diploma Offers the Following Courses with Free Certificate: Course 01: Strategic Business Management Course 02: Financial Management Course 03: Diploma in Performance Analysis Course 04: Unconscious Bias Training Course 05: Decision-Making in High-Stress Situations In this Leadership Management & Team Leader Level 7 Advanced Diploma Training Programme, you learn about different Leadership Management styles & which one will suit you best. You find out how to create a high-performance team that can always get things done, along with detailed lessons on managing office politics, negotiating, communicating, succession planning & much more. Learning Outcomes of This Leadership Management & Team Leader Level 7 Advanced Diploma Course: The learning objectives for this Leadership Management & Team Leader Level 7 Advanced Diploma Training course are broken down in detail below. After finishing the course, you will: Understand the fundamental concepts and significance of leadership management. Explore key leadership theories and their applicability in organizational settings. Enhance leadership performance through evaluation and actionable strategies. Build, nurture, and sustain high-performing team dynamics. Master strategies to motivate employees and boost morale. Develop organizational skills crucial for effective leadership management. Learn to identify, acquire, and integrate top talent effectively. Design and implement strategic succession planning initiatives. Optimize business processes for efficiency and productivity. Enhance communication skills tailored for leadership roles. Acquire effective negotiation techniques for leadership scenarios. Utilize Microsoft Office tools for effective leadership management tasks. Optimize time management for leadership effectiveness and efficiency. Navigate office politics while maintaining professional integrity and much more Why Prefer Our Leadership Management & Team Leader Level 7 Advanced Diploma Course? Level 7 Quality Licence Scheme Endorsed 30 DAYS UNCONDITIONAL MONEY BACK GUARANTEE CPD Certified Course Free e-Certificates and Student ID Card Innovative and engaging content Free Assessments 24/7 Exper Tutor Support Student Testimonials - What Our Students Say! ''An excellent and insightful course on Leadership and Management. The course is well-structured and engaging. Two thumbs up :)'' Reviewed by LOUIS BOBB ''Lots of good in-depth knowledge, easily accessible, well structured and clearly set out. A joy to work with.'' Reviewed by Kevin Reid ''Great contents. I will highly recommend it.'' Reviewed by Stephen Oparah So enrol now in this Leadership Management & Team Leader course today to Advance your career! Leadership Management & Team Leader Level 7 Advanced Diploma Course Curriculum of Leadership Management & Team Leader Level 7 Advanced Diploma Leadership Management Module 01: Introduction to Leadership Management Leadership Management Module 02: Leadership Management Theories Leadership Management Module 03: Improving Leadership Performance Leadership Management Module 04: High-Performance Teams Leadership Management Module 05: Motivating Employees Leadership Management Module 06: Organisational Skills Leadership Management Module 07: Talent Acquisation Leadership Management Module 08: Succession Planning Leadership Management Module 09: Business Process Optimisation Leadership Management Module 10: Communication Skills Leadership Management Module 11: Negotiation Techniques Leadership Management Module 12: Managing Meetings and Giving Feedback Leadership Management Module 13: Managing Change Leadership Management Module 14: Time Management Leadership Management Module 15: Dealing with Stress Situations Leadership Management Module 16: Emotional Intelligence Leadership Management Module 17: Managing Conflict Leadership Management Module 18: Dealing with Office Politics Leadership Management Module 19: Risk Assessment Leadership Management Module 20: Corporate Responsibility and Ethics Leadership Management Module 21: Microsoft Word, Excel, PowerPoint CPD 320 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Leadership Management & Team Leader Level 7 Advanced Diploma For leaders and high potential managers to upgrade their capacity to deal with competence and lead for individual and organisational achievement. Entrepreneurs. Business owners. Anyone who wants to be a great leader. Requirements Our Leadership Management & Team Leader Level 7 Advanced Diploma course is open to all. Career path Our Leadership Management & Team Leader Level 7 Advanced Diploma course will open the door to opportunities. General Manager Director Human Resources Managers Operation Manager Supervisor Administrative Services Manager

STARS - Scottish Training for Alcohol Retailers and Servers Course
5.0(43)By Knight Training (UK) Ltd
The Scottish Training for Alcohol Retailers and Servers Course (STARS) course meets the requirements of The Licensing (Scotland) Regulations 2007, which states that every person who is involved in the making of alcohol sales must receive ‘relevant training. Come to Knight Training to receive your STARS course today! Call us now on 01524 388279!

The foods we digest every day contain microbiological hazards and bacteria that involve allergic, physical, and chemical risks. This course will educate you regarding all essentials and bring you an opportunity to learn how to stay safe. Start learning Food Safety Course: Microbes, Allergen Control & Cleaning that will give you enough knowledge and skills to build your dream career. About this course This Food Safety Course: Microbes, Allergen Control & Cleaning helps to grow your skills faster through the power of relevant content and world-class tutors. In this industry-leading bite-sized course, you will learn up-to-date knowledge in the relevant field within a few hours and get certified immediately. The modules of this course are very easy to understand and all of the topics are split into different sections. You will easily grasp and use the knowledge gained from this course in your career and go one step ahead of your competitors. The course is designed to improve your employability and provide you with the tools you need to succeed. Enrol today and start learning your essential skills. Why choose this course Earn a digital Certificate upon successful completion. Accessible, informative modules taught by expert instructors Study in your own time, at your own pace, through your computer tablet or mobile device Get 24/7 help or advice from our email and live chat teams Get full tutor support on weekdays (Monday to Friday) Course Design The Food Safety Course: Microbes, Allergen Control & Cleaning is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of Video lessons Online study materials Who Is This Course For:â This Food Safety Course: Microbes, Allergen Control & Cleaning is ideal for those who want to be skilled in this field or who wish to learn a new skill to build their dream career. If you want to gain extensive knowledge, potential experience, and be an expert in the related field then this is a great course for you to grow your career. Requirements This course is for anyone who would like to learn Food Safety Course: Microbes, Allergen Control & Cleaning related skills to aid his/her career path. No formal entry prerequisites are required Certification Upon successful completion of the course, you will be able to obtain your course completion e-certificate free of cost. Print copy by post is also available at an additional cost of £9.99 and PDF Certificate at £4.99. Course Content Module 1: Microbiological Hazards and Bacteria Module 2: Allergic, Physical and Chemical Risks Module 3: Food Poisoning and Preventive Measures Module 4: Safe Cleaning Course Content Food Safety: Food Poisoning. Control Measures and Cleaning Module 1: Microbiological Hazards and Bacteria 00:20:00 Module 2: Allergic, Physical and Chemical Risks 00:18:00 Module 3: Food Poisoning and Preventive Measures 00:18:00 Module 4: Safe Cleaning 00:18:00 Frequently Asked Questions Are there any prerequisites for taking the course? There are no specific prerequisites for this course, nor are there any formal entry requirements. All you need is an internet connection, a good understanding of English and a passion for learning for this course. Can I access the course at any time, or is there a set schedule? You have the flexibility to access the course at any time that suits your schedule. Our courses are self-paced, allowing you to study at your own pace and convenience. How long will I have access to the course? For this course, you will have access to the course materials for 1 year only. This means you can review the content as often as you like within the year, even after you've completed the course. However, if you buy Lifetime Access for the course, you will be able to access the course for a lifetime. Is there a certificate of completion provided after completing the course? Yes, upon successfully completing the course, you will receive a certificate of completion. This certificate can be a valuable addition to your professional portfolio and can be shared on your various social networks. Can I switch courses or get a refund if I'm not satisfied with the course? We want you to have a positive learning experience. If you're not satisfied with the course, you can request a course transfer or refund within 14 days of the initial purchase. How do I track my progress in the course? Our platform provides tracking tools and progress indicators for each course. You can monitor your progress, completed lessons, and assessments through your learner dashboard for the course. What if I have technical issues or difficulties with the course? If you encounter technical issues or content-related difficulties with the course, our support team is available to assist you. You can reach out to them for prompt resolution.

Online Fire Safety Course
By NextGen Learning
Online Fire Safety Course Course Overview This Online Fire Safety Course provides comprehensive knowledge essential for understanding fire hazards, prevention, and emergency response. Designed to equip learners with the skills to identify fire risks and implement effective safety measures, the course covers current UK fire safety legislation, prevention strategies, and evacuation procedures. Learners will gain confidence in recognising potential fire dangers and understanding their responsibilities to maintain a safe environment. Suitable for individuals across various sectors, the course ensures participants can contribute effectively to fire safety awareness and compliance within their workplace or community. Upon completion, learners will be well-prepared to support fire safety initiatives and promote safer environments. Course Description This course delves into the fundamental aspects of fire safety, starting with an introduction to fire risks and causes. It explores key UK fire safety laws and regulations, ensuring learners understand legal responsibilities. The course covers preventive measures, including fire detection systems and risk assessments, and provides detailed guidance on emergency evacuation procedures. Throughout the course, learners will develop critical skills to assess hazards, plan safety measures, and respond appropriately during fire incidents. The structured content is delivered through clear explanations and informative materials, enabling learners to apply knowledge confidently within their roles. This course is ideal for those wishing to expand their understanding of fire safety principles and regulatory compliance in a professional context. Online Fire Safety Course Curriculum Module 01: Introduction to Fire Safety Module 02: Fire Safety Legislation Module 03: Measures of Fire Safety Module 04: Fire Emergency Evacuation Procedures (See full curriculum) Who Is This Course For? Individuals seeking to enhance their knowledge of fire safety principles. Professionals aiming to develop their competence in workplace safety compliance. Beginners with an interest in fire prevention and emergency planning. Managers responsible for health and safety within their organisation. Career Path Fire Safety Officer Health and Safety Coordinator Facilities Manager Compliance Advisor Emergency Planning Officer

Fire Warden (Marshal) Training
By NextGen Learning
Fire Warden (Marshal) Training Course Overview The Fire Warden (Marshal) Training course equips individuals with the essential skills and knowledge to manage fire safety in the workplace. It covers a comprehensive range of topics, from understanding fire safety basics to mastering evacuation procedures and regulations. Learners will gain the confidence to take on the role of a Fire Warden, ensuring they are prepared to implement preventive measures and respond effectively in the event of a fire emergency. By the end of the course, learners will have a solid understanding of fire safety protocols and be able to act decisively to safeguard people and property. Course Description This course offers in-depth coverage of fire safety, with a focus on the responsibilities and duties of a Fire Warden. Participants will explore key areas such as fire prevention, emergency response, and effective evacuation strategies. The curriculum also includes important legal regulations and risk assessment procedures, equipping learners with the tools to ensure compliance and enhance safety within their organisation. The course is designed to provide both theoretical knowledge and an understanding of best practices in fire safety, ensuring that learners are well-prepared to fulfil the role of a Fire Warden with confidence. Fire Warden (Marshal) Training Curriculum Module 01: Basics of Fire Safety Module 02: Introduction to Fire Warden Module 03: Preventive Duties Module 04: Emergency Duties and Qualities Module 05: Fire Safety Measures Module 06: Evacuation Strategies Module 07: Regulations and Risk Assessment (See full curriculum) Who is this course for? Individuals seeking to improve fire safety knowledge. Professionals aiming to enhance workplace safety. Beginners with an interest in fire safety management. Organisations needing to train staff on fire warden duties. Career Path Fire Warden Health and Safety Officer Emergency Response Coordinator Workplace Safety Advisor Fire Safety Consultant

Brain Injury Rehabilitation
By NextGen Learning
Brain Injury Rehabilitation Course Overview This "Brain Injury Rehabilitation" course provides an in-depth exploration of the human brain, its functions, and the impact of brain injuries. It covers a broad range of topics, including concussion, acquired brain injuries, and injuries resulting from sports. Learners will gain a comprehensive understanding of brain injury prevention, recovery, and rehabilitation processes. Designed to equip individuals with valuable knowledge, this course is essential for anyone aiming to understand brain health, and it provides key insights into how to support individuals recovering from brain injuries. Upon completion, learners will be well-equipped to engage in roles where brain injury management and rehabilitation are crucial. Course Description The course delves into various types of brain injuries, including concussions, acquired brain injuries, and sports-related brain trauma. It provides a detailed understanding of the human brain, the causes and effects of different brain injuries, and key rehabilitation strategies. Throughout the course, learners will explore prevention techniques and rehabilitation approaches, gaining essential skills to support brain injury recovery. The learning experience is designed to be informative and insightful, ensuring that participants can apply their knowledge to improve patient care and rehabilitation outcomes in clinical or supportive environments. By the end of the course, learners will be equipped with a robust understanding of brain injury rehabilitation and how to effectively contribute to the recovery process. Brain Injury Rehabilitation Curriculum Module 01: Understanding Human Brain and Related Injuries Module 02: Overview of Brain Concussion Module 03: All About Acquired Brain Injury Module 04: Brain Injuries Due to Sports Module 05: Prevention of Injury Module 06: Recovery and Rehabilitation (See full curriculum) Who is this course for? Individuals seeking to understand brain health and rehabilitation Professionals aiming to specialise in brain injury recovery Beginners with an interest in neuroscience or healthcare Healthcare workers wishing to enhance their knowledge in rehabilitation Career Path Rehabilitation Specialist Brain Injury Support Worker Sports Medicine Professional Neurological Rehabilitation Therapist Healthcare Practitioner specialising in Brain Injury Recovery

Spill Management Training
By NextGen Learning
Spill Management Training Course Overview This Spill Management Training course provides a comprehensive understanding of how to effectively manage and respond to spill incidents in various settings. Covering a range of topics, from hazardous substances and pollution response planning to spill clean-up and prevention, the course prepares learners to handle spill incidents with confidence. Through clear guidelines and site-specific solutions, the course ensures that learners are equipped to minimise environmental impact, reduce risks, and comply with relevant regulations. Learners will gain valuable skills in spill management, safety practices, and regulatory compliance, ensuring a safer work environment. Course Description The Spill Management Training course delves deeper into key areas essential for spill management, including hazardous substances identification, response strategies, and effective clean-up methods. Learners will explore pollution incident response planning, spill management techniques for different environments, and site-specific pollution control options. Each module is designed to offer valuable insights into best practices for spill prevention and control, while encouraging a culture of responsibility and environmental awareness. By the end of the course, learners will have the skills to manage spills efficiently, ensuring safety and compliance within their workplace. Spill Management Training Curriculum Module 01: Introduction to Spill Management Module 02: Hazardous Substances Module 03: Pollution Incident Response Planning Module 04: Managing a Spill Module 05: Spill Clean-Up Guideline Module 06: Spills on a Road or Highway Module 07: Diesel Spillages: An Overview Module 08: Site-Specific Pollution Control Options Module 09: Spill Prevention & Control Checklist Module 10: Ways to Encourage Best Practice (See full curriculum) Who is this course for? Individuals seeking to enhance their environmental safety skills. Professionals aiming to specialise in spill management or environmental protection. Beginners with an interest in pollution control and safety procedures. Organisations requiring staff training in spill management and compliance. Career Path Environmental Health and Safety Officer Spill Response Coordinator Environmental Consultant Pollution Control Specialist Health and Safety Manager
