- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Animal Care Course
By The Teachers Training
Animal Care Course is yet another 'Teacher's Choice' course from Teachers Training for a complete understanding of the fundamental topics. You are also entitled to exclusive tutor support and a professional CPD-accredited certificate in addition to the special discounted price for a limited time. Just like all our courses, this Animal Care Course and its curriculum have also been designed by expert teachers so that teachers of tomorrow can learn from the best and equip themselves with all the necessary skills. Consisting of several modules, the course teaches you everything you need to succeed in this profession. The course can be studied part-time. You can become accredited within 05 Hours studying at your own pace. Your qualification will be recognised and can be checked for validity on our dedicated website. Why Choose Teachers Training Some of our website features are: This is a dedicated website for teaching 24/7 tutor support Interactive Content Affordable price Courses accredited by the UK's top awarding bodies 100% online Flexible deadline Entry Requirements No formal entry requirements. You need to have: Passion for learning A good understanding of the English language Be motivated and hard-working Over the age of 16. Certification CPD Certification from The Teachers Training Successfully completing the MCQ exam of this course qualifies you for a CPD-accredited certificate from The Teachers Training. You will be eligible for both PDF copy and hard copy of the certificate to showcase your achievement however you wish. You can get your digital certificate (PDF) for £4.99 only Hard copy certificates are also available, and you can get one for only £10.99 You can get both PDF and Hard copy certificates for just £12.99! The certificate will add significant weight to your CV and will give you a competitive advantage when applying for jobs. Module 01: Introduction to the Care and Animal Welfare of All Species Introduction to Care and Welfare of All Animal Species 00:29:00 Module 02: Basic Animal Health Basic Animal Health 00:25:00 Module 03: Hygiene Hygiene 00:26:00 Module 04: First Aid for Animals First Aid for Animals 00:26:00 Module 05: Nutrition Nutrition 00:23:00 Module 06: Getting to Know the Dogs & Puppies Getting to Know the Dogs _ Puppies 00:24:00 Module 07: Getting to Know the Kittens and Cats Getting to Know the Kittens and Cats 00:31:00 Module 08: Learning about Horses Learning about Horses 00:25:00 Module 09: Learning about Birds Learning about Birds 00:23:00 Module 10: Specific Information on Rabbits & Guinea-Pigs Specific Information on Rabbits _ Guinea-Pigs 00:19:00 Module 11: Specific Information on Ornamental Fish Specific Information on Ornamental Fish 00:29:00

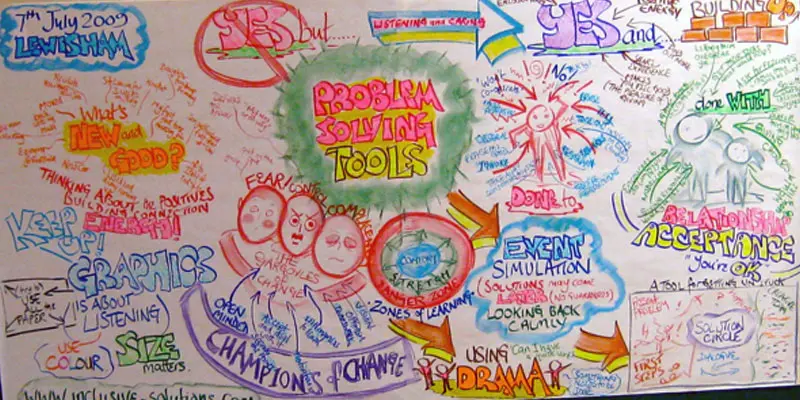
PROBLEM SOLVING TOOLS AND TECHNIQUES
By Inclusive Solutions
In this practical workshop session we will explore ways of problem solving around complex situations. The session will be practical and will aim to allow the sharing of experiences and good practice as well promoting innovative approaches to problem solving around systemic, organisational as well as individual inclusion issues. Course Category Behaviour and Relationships Visioning and Problem Solving Description ‘The question is not should they be here anymore. Now it’s how can we figure out how best to include them?’ In this practical workshop session we will explore ways of problem solving around complex situations. The session will be practical and will aim to allow the sharing of experiences and good practice as well promoting innovative approaches to problem solving around systemic, organisational as well as individual inclusion issues. Behaviour problems, relationship challenges and personnel dilemmas can all be worked on with these team oriented problem solving processes. We will introduce participants to a range of powerful effective approaches for them to choose from back in their own workplaces. Testimonials A great day – going away buzzing with ideas Excellent! Inspirational! Informative! Learning Objectives Increased confidence regarding problem solving around inclusion in mainstream settings Access to a wider range of practical strategies and techniques to impact on communication, realtionship, learning and behaviour issues Learn new problem solving processes Who Is It For ? Early Years and School based Practitioners Heads and Deputies Guidance staff Learning Support teams SENCOs Primary and secondary teachers Parents Local Authority Support Services Community workers and carers Course Content The course answers the questions : How can we work out how to include this child best? Is there a more structured way to run this meeting? Can we explore the emotional impact the person is having on us and still agree strategies? How can I get unstuck from this problem? The day will cover: Solution Circles Solution Focused approaches Synectics – using analogies and out of the box creativity Circles of Adults Using Imagination to solve problems If you liked this course you may well like: CIRCLES OF ADULTS
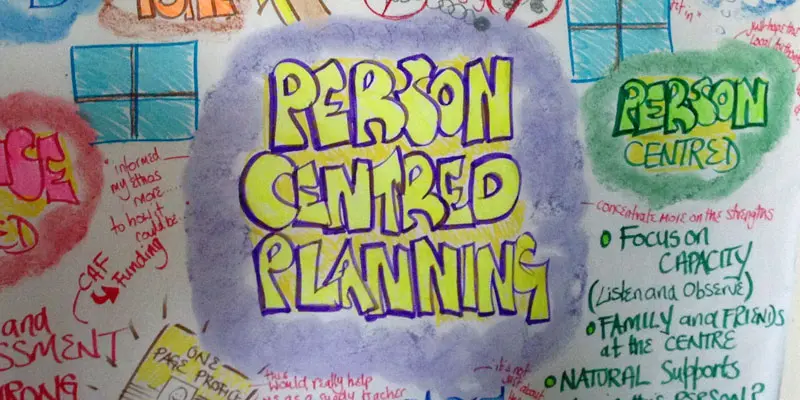
PERSON CENTRED REVIEWS
By Inclusive Solutions
Learn how to carry out a Person Centred Review based on the values of person centred thinking. Course Category Person Centred Planning Inclusion Strategic Work Visioning and Problem Solving Description Person centred planning is a way of expressing a set of inclusive values through a unique range of tools and techniques. The most commonly used person centred tool is a Person Centred Review – and it shows these values in action. All person centred planning tools and processes are driven by a commitment to achieve inclusive outcomes for the person whose plan it is, and the young people involved are always present throughout their planning session. The focus of all person centred approaches is the whole person irrespective of the label they carry. Two people, a process facilitator and a graphic facilitator, typically facilitate plans. The role of the support service staff in this work is as a facilitator not as an expert participant, problem solver, assessor or provider of consultation. Person Centred Reviews like MAPS and PATH are especially effective tools in planning transitions and annual review processes for young people with additional support needs and for through-care planning for young people who are looked after or accommodated. Over time person centred working will reveal areas of unmet need in current provision and thereby inform the ongoing strategic planning within any particular region. Testimonials Be the first…. Learning Objectives To Explore the values underpinning person centred working To show how person centred planning with Person Centred Reviews naturally captures young people’s strengths and capacities A demonstration of how person centred reviews encourage meaningful consultation and participation with young people (particularly for those who cannot make their views known in typical ways To show how Person Centred Planning leads to the building of stronger parent/school partnerships To indicate how person centred planning can promote multi-agency teamwork and shared responsibilities To increase understanding the how of process and graphic facilitation in person centred work. Who Is It For ? Teachers and School Staff Education Services Social Care Staff Health Professionals Transition Coordinators Family Support Workers Link Workers Course Content An introduction to the person centred planning Person Centred Reviews – live demonstrations of process in action followed by real time coaching of facilitation skills. We would stress that this is an introductory day and that participants will be expected to make plans for their own follow up and further practice of the tools covered in the course of the day. If you liked this course you may well like: PERSON CENTRED PLANNING USING PATH AND MAPS
PUPIL PARTICIPATION: LISTENING TO THE POWERFUL VOICE OF YOUNG PEOPLE
By Inclusive Solutions
Local authorities are being encouraged to seek the views of young people in relation to the services they receive. Schools and the whole range of support services (e.g. behaviour support, youth offending teams, social services, CAMHS etc.) are being expected to routinely ask young people for their views. This goes beyond involving young people in plans that concern them e.g care plans, individual education plans, pastoral support plans etc. Online Course now available via Teachable Platform – Ask the Children Learn at your own pace… lots of text and video support Course Category Peer Support Description Local authorities are being encouraged to seek the views of young people in relation to the services they receive. Schools and the whole range of support services (e.g. behaviour support, youth offending teams, social services, CAMHS etc.) are being expected to routinely ask young people for their views. This goes beyond involving young people in plans that concern them e.g care plans, individual education plans, pastoral support plans etc. This training will focus on how young people can be effectively engaged in giving their views and will present a model for use in evaluating services to young people based on the concept of resilience. This model enables young people to be clear about what has helped and hindered them in being able to overcome difficulties. It also provides a framework for evaluating the extent to which services are reducing risk and increasing protective factors to enable young people to develop the resilience. Testimonials ‘Yet again inspiring and opening more doors than I can go through’? ‘This opened a lot of avenues for thought and reflection. It will help me to help colleagues to see where they can improve practice to create a more inclusive environment within the whole school.’ ‘Some great ideas and restored my self belief! Fantastic’ Learning Objectives Strategies for engaging young people Knowledge and Understanding of resilience In relation to system and environmental factors Strategies for reducing risk and increasing protective factors In relation to Individual young people and services Evaluation framework for services to young people Who Is It For ? Youth offending teams Social services CAMHS Primary and secondary teachers Heads and Deputies SENCOs Learning Support and Guidance staff Advanced Skills Teachers Parents Local Authority Support Services Community Development workers Early Years and School based Practitioners Social work staff Health Services Course Content The course answers the questions : How can we truly involve pupils? Practically how do we go about listening to pupils views? What if we do not like what they tell us? How can we involve our most disaffected young people? Key themes Tools for engaging young people and gaining their views The concept of resilience System and environmental risk and protective factors that impact on young people’s resilience Reducing risk and Increasing protective factors Resilience planning for Individuals and services Evaluating services to young people If you liked this course you may well like: CIRCLES OF FRIENDS

PL-100T00 Microsoft Power Platform App Maker
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The App Maker builds solutions to simplify, automate, and transform tasks and processes for themselves and their team where they have deep expertise in the solution business domain. They have basic data modeling, user experience design, requirements analysis, and process analysis skills. The App Maker creates and enforces business processes, structures digital collection of information, improves efficiency of repeatable tasks, and automates business processes. The App Maker uses the Maker tools of Power Platform to solve business problems. They may use advanced features of Microsoft apps and third-party productivity tools. The App Maker is aware of the capabilities and limitations of available tools and understands how to apply them. The App Maker is self-directed, and solution focused. They may not have formal IT training but are comfortable using technology to solve business problems with a personal growth mindset. They understand the operational need and have a vision of the desired outcome. They approach problems with phased and iterative strategies. This course will teach you how to build apps with low-code techniques to simplify, automate, and transform business tasks and processes using Microsoft Power Platform. This course contains a 1-day Applied Workshop. This workshop will allow you to practice your App Maker skills by creating an end-to-end solution to solve a problem for a fictitious company. The solution will include a Microsoft Dataverse database, Power Apps canvas app, and Power Automate flows. 1 - Get started with Microsoft Power Platform for app makers Identify components Create apps Get started with Microsoft Dataverse Work with Copilot in Microsoft Power Platform 2 - Create tables in Dataverse Table characteristics Table relationships Dataverse logic and security Dataverse auditing Dual-write vs. virtual tables 3 - Create and manage columns within a table in Dataverse Define columns in Microsoft Dataverse Column types in Microsoft Dataverse Add a column to a table Primary name column Restrictions that apply to columns in a table Create an auto numbering column Create an alternate key 4 - Load/export data and create data views in Dataverse View data in a table Create or edit views of data in a table Dataverse data import options Load data into a table Dataverse data export options Export Add, update, or delete data in a table by using Excel Import data using Power Query 5 - Export data from Dataverse and use Microsoft Excel to edit records Export data to Excel Edit and update data in Excel 6 - Get started with Microsoft Dataverse for Teams Dataverse for Teams vs Dataverse Provision your first Dataverse environment Create your first table to store data 7 - Build your first app with Power Apps and Dataverse for Teams Create your first app with the hero template Customize your app with Power Apps Studio Publish your app Install template apps 8 - Build your first workflow with Power Automate and Dataverse for Teams Types of workflows that Power Automate can build in Dataverse Schedule a flow 9 - Create reports with Power BI and Dataverse for Teams Connect to and transform Dataverse for Teams data from Power BI Create a Power BI report Publish the report Share the data 10 - Get started building with Power BI Use Power BI Building blocks of Power BI Tour and use the Power BI service 11 - Explore what Power BI can do for you What can I do with the Power BI service as a consumer? View content in the Power BI service Collaborate and share in Power BI Find and view dashboards and reports 12 - Create and manage workspaces in Power BI Distribute a report or dashboard Monitor usage and performance Recommend a development life cycle strategy Troubleshoot data by viewing its lineage Configure data protection 13 - Manage semantic models in Power BI Use a Power BI gateway to connect to on-premises data sources Configure a semantic model scheduled refresh Configure incremental refresh settings Manage and promote semantic models Troubleshoot service connectivity Boost performance with query caching (Premium) 14 - Create dashboards in Power BI Configure data alerts Explore data by asking questions Review Quick insights Add a dashboard theme Pin a live report page to a dashboard Configure a real-time dashboard Set mobile view 15 - Implement row-level security Configure row-level security with the static method Configure row-level security with the dynamic method 16 - Create dashboards in Power BI Configure data alerts Explore data by asking questions Review Quick insights Add a dashboard theme Pin a live report page to a dashboard Configure a real-time dashboard Set mobile view 17 - Secure, publish, and share data in Power BI Share and use reports in Power BI Row-level security Publish a report to a Power BI workspace Share reports and user experience Protect data in Power BI Data refresh and alerts 18 - Embed Power BI content Embed Power BI reports Embed other Power BI content types Optimize the embedding experience 19 - How to build your first model-driven app with Dataverse Model-driven apps, powered by Microsoft Dataverse Explore sample apps 20 - Get started with model-driven apps in Power Apps Introducing model-driven apps Components of model-driven apps Design model-driven apps Incorporate business process flows 21 - Configure forms, charts, and dashboards in model-driven apps Forms overview Form elements Configure multiple forms Use specialized form components Configure views overview Configure grids Create and edit views Configure charts overview Dashboards overview Use interactive streams and tiles 22 - Manage Dynamics 365 model-driven app settings and security Configure role-based security Manage teams and business units Explore settings and customizations 23 - Use specialized components in a model-driven form Create business process flows Embed a canvas app in a model-driven form Add a timeline in a model-driven form Create a report in a model-driven form 24 - Get started with Power Apps canvas apps Start Power Apps Power Apps data sources Use Power Apps with Power Automate and Power BI Designing a Power Apps app 25 - Customize a canvas app in Power Apps Improve your app by making basic customizations Explore controls and screens in canvas apps 26 - How to build the User Interface in a canvas app in Power Apps Use themes to quickly change the appearance of your app Brand a control Icons Images Personalization Build for phones or tablets 27 - Navigation in a canvas app in Power Apps Understanding navigation The Navigate and Back functions More ways to use the Navigate function 28 - Manage apps in Power Apps Power Apps review 29 - Build a mobile-optimized app from Power Apps Learn about mobile-optimized apps Identify components to make a canvas app mobile-optimized Create a mobile-optimized app that uses responsive designs Identify performance considerations for a mobile-optimized canvas app 30 - Use and understand Controls in a canvas app in Power Apps Core properties of controls Entering and displaying data with text controls Additional controls for enhancing your app's usability Media Modern controls Work with component libraries 31 - Create formulas to change properties in a Power Apps canvas app Formulas overview Use a formula to modify the format of controls Use formulas to perform calculations Use a control to modify the property of other controls Conditional formatting Functions for validating data 32 - Use imperative development techniques for canvas apps in Power Apps Imperative versus declarative development The three types of variables in Power Apps Global variables Contextual variables Collections Additional variable concepts 33 - Manage apps in Power Apps Power Apps review 34 - Create formulas to change properties in a Power Apps canvas app Formulas overview Use a formula to modify the format of controls Use formulas to perform calculations Use a control to modify the property of other controls Conditional formatting Functions for validating data 35 - Create formulas to change behaviors in a Power Apps canvas app Formulas and functionality Understanding true and false Understanding control behaviors and actions Performing multiple actions in a formula Control the display mode through a formula Use controls and functions to create a dynamic formula 36 - Author a basic formula that uses tables and records in a Power Apps canvas app Records and tables Using the Table function Store a table Filter your table Use the lookup function to return a record Additional table functions 37 - Build a canvas app for a real estate solution with Copilot in Power Apps 38 - Get started with Power Automate Introducing Power Automate Create your first flow Troubleshoot flows 39 - Build approval flows with Power Automate Provide solutions to real-world scenarios. 40 - Build flows to manage user information 41 - Power Automate's deep integration across multiple data sources 42 - Use the Admin center to manage environments and data policies in Power Automate Administer flows Export and import flows Learn how to distribute button flows 43 - Use AI Builder in Power Automate AI Builder in Power Automate saves time Advanced usage of AI Builder in Power Automate 44 - Optimize your business process with process advisor Get familiar with process advisor Create your first recording Edit recordings and group actions Analyze recordings and interpret results Automation recommendations 45 - Optimize your business process with process advisor Get familiar with process advisor Create your first recording Edit recordings and group actions Analyze recordings and interpret results Automation recommendations 46 - Build flows for a real estate solution using Copilot in Power Automate When to use Copilot in Power Automate 47 - Use Dataverse triggers and actions in Power Automate Dataverse triggers Query data Create, update, delete, and relate actions 48 - Create tables in Dataverse Table characteristics Table relationships Dataverse logic and security Dataverse auditing Dual-write vs. virtual tables 49 - Create and manage columns within a table in Dataverse Define columns in Microsoft Dataverse Column types in Microsoft Dataverse Add a column to a table Primary name column Restrictions that apply to columns in a table Create an auto numbering column Create an alternate key 50 - Get started with Power Apps canvas apps Start Power Apps Power Apps data sources Use Power Apps with Power Automate and Power BI Designing a Power Apps app 51 - How to build the User Interface in a canvas app in Power Apps Use themes to quickly change the appearance of your app Brand a control Icons Images Personalization Build for phones or tablets 52 - Get started with Power Automate Introducing Power Automate Create your first flow Troubleshoot flows 53 - Challenge Project - Build a booking requests app with Power Apps and Power Automate Prepare

PMI-PBA Exam Prep: In-House Training
By IIL Europe Ltd
PMI-PBA® Exam Prep: In-House Training The course provides targeted exam preparation support for PMI®'s Professional in Business Analysis exam candidates, including a content review of The PMI Guide to Business Analysis, a review of the PMI-PBA® reference books, and an exam preparation tutorial. You will be given a Study Guide that you can re-use to assess your knowledge gaps as part of your Personal Action Plan. Your score on this for each Knowledge Area can be compared to your results on the quiz at the end of each course module to guide your study efforts. What you will Learn Upon completion, participants will be able to: Demonstrate familiarity with the structure, content and framework of The PMI Guide to Business Analysis Explain the six Knowledge Areas of The PMI Guide to Business Analysis, as well as, their inter-relationships with each other and the six Process Groups Differentiate among the five business analysis domains in the project life cycle Create a personal action plan to study and prepare for the PMI-PBA® Exam Getting Started PMI-PBA Examination Certification Process The Credential Examination Foundation Concepts for PMI-PBA® Prep Business analysis terminology and definitions Business analysis project, program, and portfolio management Product and project life cycles Skills and qualities of a business analyst Introduction to Business Analysis in Projects Business analysis overview How organizations implement business analysis Business analyst and project manager relationships Requirements definitions and types Practice quiz On-Demand Segment A: Define the Business Problem (Pre-work for Needs Assessment) Needs Assessment Review Needs Assessment knowledge area Identify problem or opportunity Assess current and future state Determine options and provide recommendations Facilitate product roadmap development Assemble business case Practice quiz Stakeholder Engagement Review Stakeholder Engagement knowledge area Identify Stakeholders and conduct analysis Determine Stakeholder engagement and communication approach Conduct business analysis planning Practice quiz On-Demand Segment B: The Elicitation Plan (Pre-work for Elicitation) Elicitation Review Elicitation knowledge area Determine Elicitation approach Preparing for Elicitation Conducting Elicitation Confirming Elicitation results Practice quiz On-Demand Segment C: Overview of Requirements Analysis (Pre-work for Analysis) Analysis Review Analysis knowledge area Determine Analysis approach Create and analyze models Define requirements and acceptance criteria Verify, validate, and prioritize requirements Identify and analyze product risks Assess product design options Practice quiz Traceability and Monitoring Review Traceability and Monitoring knowledge area Determine Traceability and Monitoring approach Establish relationships and dependencies Select and approve requirements Make changes to requirements and other product information Practice quiz Solution Evaluation Review Solution Evaluation knowledge area Evaluate solution performance Determine solution evaluation approach Evaluate acceptance results and address defects Obtain solution acceptance for release Practice quiz Exam Application and Preparation Process Applying for the Exam Studying for the Exam Sitting for the Exam Reviewing your Knowledge Gap Practice Exam Study Guide - a reliable learning aid Summary and Next Steps Crystallizing the Business Analysis Domains Developing a Personal Action Plan for Exam Study

SC-200T00 Microsoft Security Operations Analyst
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The Microsoft Security Operations Analyst collaborates with organizational stakeholders to secure information technology systems for the organization. Their goal is to reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders. Responsibilities include threat management, monitoring, and response by using a variety of security solutions across their environment. The role primarily investigates, responds to, and hunts for threats using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security products. Since the Security Operations Analyst consumes the operational output of these tools, they are also a critical stakeholder in the configuration and deployment of these technologies. Learn how to investigate, respond to, and hunt for threats using Microsoft Sentinel, Microsoft Defender for Cloud, and Microsoft 365 Defender. In this course you will learn how to mitigate cyberthreats using these technologies. Specifically, you will configure and use Microsoft Sentinel as well as utilize Kusto Query Language (KQL) to perform detection, analysis, and reporting. The course was designed for people who work in a Security Operations job role and helps learners prepare for the exam SC-200: Microsoft Security Operations Analyst. Prerequisites Basic understanding of Microsoft 365 Fundamental understanding of Microsoft security, compliance, and identity products Intermediate understanding of Windows 10 Familiarity with Azure services, specifically Azure SQL Database and Azure Storage Familiarity with Azure virtual machines and virtual networking Basic understanding of scripting concepts. 1 - Introduction to Microsoft 365 threat protection Explore Extended Detection & Response (XDR) response use cases Understand Microsoft Defender XDR in a Security Operations Center (SOC) Explore Microsoft Security Graph Investigate security incidents in Microsoft Defender XDR 2 - Mitigate incidents using Microsoft 365 Defender Use the Microsoft Defender portal Manage incidents Investigate incidents Manage and investigate alerts Manage automated investigations Use the action center Explore advanced hunting Investigate Microsoft Entra sign-in logs Understand Microsoft Secure Score Analyze threat analytics Analyze reports Configure the Microsoft Defender portal 3 - Protect your identities with Microsoft Entra ID Protection Microsoft Entra ID Protection overview Detect risks with Microsoft Entra ID Protection policies Investigate and remediate risks detected by Microsoft Entra ID Protection 4 - Remediate risks with Microsoft Defender for Office 365 Automate, investigate, and remediate Configure, protect, and detect Simulate attacks 5 - Safeguard your environment with Microsoft Defender for Identity Configure Microsoft Defender for Identity sensors Review compromised accounts or data Integrate with other Microsoft tools 6 - Secure your cloud apps and services with Microsoft Defender for Cloud Apps Understand the Defender for Cloud Apps Framework Explore your cloud apps with Cloud Discovery Protect your data and apps with Conditional Access App Control Walk through discovery and access control with Microsoft Defender for Cloud Apps Classify and protect sensitive information Detect Threats 7 - Respond to data loss prevention alerts using Microsoft 365 Describe data loss prevention alerts Investigate data loss prevention alerts in Microsoft Purview Investigate data loss prevention alerts in Microsoft Defender for Cloud Apps 8 - Manage insider risk in Microsoft Purview Insider risk management overview Create and manage insider risk policies Investigate insider risk alerts Take action on insider risk alerts through cases Manage insider risk management forensic evidence Create insider risk management notice templates 9 - Investigate threats by using audit features in Microsoft Defender XDR and Microsoft Purview Standard Explore Microsoft Purview Audit solutions Implement Microsoft Purview Audit (Standard) Start recording activity in the Unified Audit Log Search the Unified Audit Log (UAL) Export, configure, and view audit log records Use audit log searching to investigate common support issues 10 - Investigate threats using audit in Microsoft Defender XDR and Microsoft Purview (Premium) Explore Microsoft Purview Audit (Premium) Implement Microsoft Purview Audit (Premium) Manage audit log retention policies Investigate compromised email accounts using Purview Audit (Premium) 11 - Investigate threats with Content search in Microsoft Purview Explore Microsoft Purview eDiscovery solutions Create a content search View the search results and statistics Export the search results and search report Configure search permissions filtering Search for and delete email messages 12 - Protect against threats with Microsoft Defender for Endpoint Practice security administration Hunt threats within your network 13 - Deploy the Microsoft Defender for Endpoint environment Create your environment Understand operating systems compatibility and features Onboard devices Manage access Create and manage roles for role-based access control Configure device groups Configure environment advanced features 14 - Implement Windows security enhancements with Microsoft Defender for Endpoint Understand attack surface reduction Enable attack surface reduction rules 15 - Perform device investigations in Microsoft Defender for Endpoint Use the device inventory list Investigate the device Use behavioral blocking Detect devices with device discovery 16 - Perform actions on a device using Microsoft Defender for Endpoint Explain device actions Run Microsoft Defender antivirus scan on devices Collect investigation package from devices Initiate live response session 17 - Perform evidence and entities investigations using Microsoft Defender for Endpoint Investigate a file Investigate a user account Investigate an IP address Investigate a domain 18 - Configure and manage automation using Microsoft Defender for Endpoint Configure advanced features Manage automation upload and folder settings Configure automated investigation and remediation capabilities Block at risk devices 19 - Configure for alerts and detections in Microsoft Defender for Endpoint Configure advanced features Configure alert notifications Manage alert suppression Manage indicators 20 - Utilize Vulnerability Management in Microsoft Defender for Endpoint Understand vulnerability management Explore vulnerabilities on your devices Manage remediation 21 - Plan for cloud workload protections using Microsoft Defender for Cloud Explain Microsoft Defender for Cloud Describe Microsoft Defender for Cloud workload protections Enable Microsoft Defender for Cloud 22 - Connect Azure assets to Microsoft Defender for Cloud Explore and manage your resources with asset inventory Configure auto provisioning Manual log analytics agent provisioning 23 - Connect non-Azure resources to Microsoft Defender for Cloud Protect non-Azure resources Connect non-Azure machines Connect your AWS accounts Connect your GCP accounts 24 - Manage your cloud security posture management? Explore Secure Score Explore Recommendations Measure and enforce regulatory compliance Understand Workbooks 25 - Explain cloud workload protections in Microsoft Defender for Cloud Understand Microsoft Defender for servers Understand Microsoft Defender for App Service Understand Microsoft Defender for Storage Understand Microsoft Defender for SQL Understand Microsoft Defender for open-source databases Understand Microsoft Defender for Key Vault Understand Microsoft Defender for Resource Manager Understand Microsoft Defender for DNS Understand Microsoft Defender for Containers Understand Microsoft Defender additional protections 26 - Remediate security alerts using Microsoft Defender for Cloud Understand security alerts Remediate alerts and automate responses Suppress alerts from Defender for Cloud Generate threat intelligence reports Respond to alerts from Azure resources 27 - Construct KQL statements for Microsoft Sentinel Understand the Kusto Query Language statement structure Use the search operator Use the where operator Use the let statement Use the extend operator Use the order by operator Use the project operators 28 - Analyze query results using KQL Use the summarize operator Use the summarize operator to filter results Use the summarize operator to prepare data Use the render operator to create visualizations 29 - Build multi-table statements using KQL Use the union operator Use the join operator 30 - Work with data in Microsoft Sentinel using Kusto Query Language Extract data from unstructured string fields Extract data from structured string data Integrate external data Create parsers with functions 31 - Introduction to Microsoft Sentinel What is Microsoft Sentinel? How Microsoft Sentinel works When to use Microsoft Sentinel 32 - Create and manage Microsoft Sentinel workspaces Plan for the Microsoft Sentinel workspace Create a Microsoft Sentinel workspace Manage workspaces across tenants using Azure Lighthouse Understand Microsoft Sentinel permissions and roles Manage Microsoft Sentinel settings Configure logs 33 - Query logs in Microsoft Sentinel Query logs in the logs page Understand Microsoft Sentinel tables Understand common tables Understand Microsoft Defender XDR tables 34 - Use watchlists in Microsoft Sentinel Plan for watchlists Create a watchlist Manage watchlists 35 - Utilize threat intelligence in Microsoft Sentinel Define threat intelligence Manage your threat indicators View your threat indicators with KQL 36 - Connect data to Microsoft Sentinel using data connectors Ingest log data with data connectors Understand data connector providers View connected hosts 37 - Connect Microsoft services to Microsoft Sentinel Plan for Microsoft services connectors Connect the Microsoft Office 365 connector Connect the Microsoft Entra connector Connect the Microsoft Entra ID Protection connector Connect the Azure Activity connector 38 - Connect Microsoft Defender XDR to Microsoft Sentinel Plan for Microsoft Defender XDR connectors Connect the Microsoft Defender XDR connector Connect Microsoft Defender for Cloud connector Connect Microsoft Defender for IoT Connect Microsoft Defender legacy connectors 39 - Connect Windows hosts to Microsoft Sentinel Plan for Windows hosts security events connector Connect using the Windows Security Events via AMA Connector Connect using the Security Events via Legacy Agent Connector Collect Sysmon event logs 40 - Connect Common Event Format logs to Microsoft Sentinel Plan for Common Event Format connector Connect your external solution using the Common Event Format connector 41 - Connect syslog data sources to Microsoft Sentinel Plan for syslog data collection Collect data from Linux-based sources using syslog Configure the Data Collection Rule for Syslog Data Sources Parse syslog data with KQL 42 - Connect threat indicators to Microsoft Sentinel Plan for threat intelligence connectors Connect the threat intelligence TAXII connector Connect the threat intelligence platforms connector View your threat indicators with KQL 43 - Threat detection with Microsoft Sentinel analytics What is Microsoft Sentinel Analytics? Types of analytics rules Create an analytics rule from templates Create an analytics rule from wizard Manage analytics rules 44 - Automation in Microsoft Sentinel Understand automation options Create automation rules 45 - Threat response with Microsoft Sentinel playbooks What are Microsoft Sentinel playbooks? Trigger a playbook in real-time Run playbooks on demand 46 - Security incident management in Microsoft Sentinel Understand incidents Incident evidence and entities Incident management 47 - Identify threats with Behavioral Analytics Understand behavioral analytics Explore entities Display entity behavior information Use Anomaly detection analytical rule templates 48 - Data normalization in Microsoft Sentinel Understand data normalization Use ASIM Parsers Understand parameterized KQL functions Create an ASIM Parser Configure Azure Monitor Data Collection Rules 49 - Query, visualize, and monitor data in Microsoft Sentinel Monitor and visualize data Query data using Kusto Query Language Use default Microsoft Sentinel Workbooks Create a new Microsoft Sentinel Workbook 50 - Manage content in Microsoft Sentinel Use solutions from the content hub Use repositories for deployment 51 - Explain threat hunting concepts in Microsoft Sentinel Understand cybersecurity threat hunts Develop a hypothesis Explore MITRE ATT&CK 52 - Threat hunting with Microsoft Sentinel Explore creation and management of threat-hunting queries Save key findings with bookmarks Observe threats over time with livestream 53 - Use Search jobs in Microsoft Sentinel Hunt with a Search Job Restore historical data 54 - Hunt for threats using notebooks in Microsoft Sentinel Access Azure Sentinel data with external tools Hunt with notebooks Create a notebook Explore notebook code

Professional Certificate Course in Managing the E-Enterprise in London 2024
4.9(261)By Metropolitan School of Business & Management UK
The aim of this course is to provide a comprehensive understanding of e-commerce and its organizational structure. By the end of this course, students will be able to compare conventional design and e-organization, understand the concept and dynamics of e-retailing, and apply the concept of e-services. After the successful completion of the course, you will be able to learn about the following, Compare Conventional Design and E-Organization Understand E-commerce Enterprise's Organizational Structure Understand the concept and dynamics of E-Retailing Understand and utilize a Conversion Funnel Understand and apply the concept of E-services. The aim of this course is to provide learners with a comprehensive understanding of the key concepts, principles, and dynamics of e-commerce enterprise, and the impact of technology on organizational structure, design, and operations. The course will explore the differences between conventional design and e-organization, with a focus on e-retailing, conversion funnel, and e-services. By the end of the course, learners will have developed the knowledge and skills required to evaluate, analyze, and implement effective e-commerce strategies to drive organizational growth and success. The aim of this course is to provide a comprehensive understanding of e-commerce and its organizational structure. By the end of this course, students will be able to compare conventional design and e-organization, understand the concept and dynamics of e-retailing, and apply the concept of e-services. They will also be able to utilize a conversion funnel to analyze customer behavior and optimize the e-commerce experience. This course aims to equip students with the skills and knowledge necessary to succeed in the ever-evolving e-commerce industry. VIDEO - Course Structure and Assessment Guidelines Watch this video to gain further insight. Navigating the MSBM Study Portal Watch this video to gain further insight. Interacting with Lectures/Learning Components Watch this video to gain further insight. Managing the E-Enterprise Self-paced pre-recorded learning content on this topic. Managing the E-Enterprise Put your knowledge to the test with this quiz. Read each question carefully and choose the response that you feel is correct. All MSBM courses are accredited by the relevant partners and awarding bodies. Please refer to MSBM accreditation in about us for more details. There are no strict entry requirements for this course. Work experience will be added advantage to understanding the content of the course.The certificate is designed to enhance the learner's knowledge in the field. This certificate is for everyone eager to know more and get updated on current ideas in their respective field. We recommend this certificate for the following audience. E-commerce Manager Chief Digital Officer Digital Marketing Manager Online Business Manager Web Analytics Manager Social Media Manager Customer Relationship Manager Average Completion Time 2 Weeks Accreditation 3 CPD Hours Level Advanced Start Time Anytime 100% Online Study online with ease. Unlimited Access 24/7 unlimited access with pre-recorded lectures. Low Fees Our fees are low and easy to pay online.

Certified Information Security Manager (CISM)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for The intended audience for this course is information security and IT professionals, such as network administrators and engineers, IT managers, and IT auditors, and other individuals who want to learn more about information security, who are interested in learning in-depth information about information security management, who are looking for career advancement in IT security, or who are interested in earning the CISM certification. Overview Establish and maintain a framework to provide assurance that information security strategies are aligned with business objectives and consistent with applicable laws and regulations. Identify and manage information security risks to achieve business objectives. Create a program to implement the information security strategy. Implement an information security program. Oversee and direct information security activities to execute the information security program. Plan, develop, and manage capabilities to detect, respond to, and recover from information security incidents. In this course, students will establish processes to ensure that information security measures align with established business needs. Prerequisites Information security governance Information risk management Information security program development Information security program management Incident management and response 1 - Information Security Governance Develop an Information Security Strategy Align Information Security Strategy with Corporate Governance Identify Legal and Regulatory Requirements Justify Investment in Information Security Identify Drivers Affecting the Organization Obtain Senior Management Commitment to Information Security Define Roles and Responsibilities for Information Security Establish Reporting and Communication Channels 2 - Information Risk Management Implement an Information Risk Assessment Process Determine Information Asset Classification and Ownership Conduct Ongoing Threat and Vulnerability Evaluations Conduct Periodic BIAs Identify and Evaluate Risk Mitigation Strategies Integrate Risk Management into Business Life Cycle Processes Report Changes in Information Risk 3 - Information Security Program Development Develop Plans to Implement an Information Security Strategy Security Technologies and Controls Specify Information Security Program Activities Coordinate Information Security Programs with Business Assurance Functions Identify Resources Needed for Information Security Program Implementation Develop Information Security Architectures Develop Information Security Policies Develop Information Security Awareness, Training, and Education Programs Develop Supporting Documentation for Information Security Policies 4 - Information Security Program Implementation Integrate Information Security Requirements into Organizational Processes Integrate Information Security Controls into Contracts Create Information Security Program Evaluation Metrics 5 - Information Security Program Management Manage Information Security Program Resources Enforce Policy and Standards Compliance Enforce Contractual Information Security Controls Enforce Information Security During Systems Development Maintain Information Security Within an Organization Provide Information Security Advice and Guidance Provide Information Security Awareness and Training Analyze the Effectiveness of Information Security Controls Resolve Noncompliance Issues 6 - Incident Management and Response Develop an Information Security Incident Response Plan Establish an Escalation Process Develop a Communication Process Integrate an IRP Develop IRTs Test an IRP Manage Responses to Information Security Incidents Perform an Information Security Incident Investigation Conduct Post-Incident Reviews

Special Executive Master's Programme in Strategic Business Management
4.9(261)By Metropolitan School of Business & Management UK
Special Executive Masters Programme (S.E.M.P) This programme is geared at enhancing professionals' careers. The SEMP is an encapsulated Senior Management Programmes are short certificate modules designed for anyone who would benefit from more in-depth business knowledge delivered in a short and intensive programme What makes us different? We are a world class business school located in the heart of London, Dubai, Islamabad and Lagos. We are one of the fastest growing British business schools with a stylish blended learning model that is both online and on campus. Learn more about the programme Special Executive Master's Programme in Strategic Business Management Course Overview The MSBM Special Executive Masters Programmes (SEMP) allows you to update your skills, develop new skills, and explore and develop interests in a wide range of topics. These courses can be taken as personal or professional development and may enhance your employability. Gaining deep insight into successful business strategies is a must for business professionals and managers alike. That’s because no matter where you are in your career, it’s critical to understand the market your business is in and the effect your leadership and decision making can have on your company’s success. How else can you maintain your company’s value proposition, increase market share, and remain competitive? Strategic management is important because it helps in setting detailed goals, analyzing all our internal and external resources, analyzing our external environment, as well as stakeholder views. Good corporate governance needs an efficient strategic management process. Course Details Mode of Study Using Web-based technology, this program provides self-paced, individualized instruction that can be taken anywhere and anytime an individual has access to a computer and the Internet. This Programme is suitable for successful professionals or specialists in the private, public, or voluntary sectors who have new management responsibilities and need to quickly expand their management knowledge. This Programme serves as a refresher course for those who have had their Masters a long time ago and need quick reminders and professional/ academic updates while it serves as a primer for those very experienced Professionals who never made time out for their masters yet they require the academic and practical relevance of this master’s experience. It is a short executive training that runs online for 3 months. Candidates will run 2 months of active lectures and series of assignments and 1 month for their dissertation. Upon successful completion of the Programme, candidates will be awarded a Continuing Professional Development (CPD) certificate in the specific Programme they have completed. What is a CPD Course? Continuing Professional Development (CPD) is the means by which professionals maintain and enhance their knowledge and skills. The world is constantly moving at a very fast pace so undertaking CPD is essential to support a professional in his/her current role as well as helping them with career progression. CPD is all about upgrading knowledge, skills, and capabilities to remain effective and compliant. A CPD course is an investment that you make in yourself. It’s a way of planning your development that links learning directly to practice. CPD can help you keep your skills and knowledge up to date and prepare you for greater responsibilities. It can boost your confidence, strengthen your professional credibility, and help you become more creative in tackling new challenges. Is the SEMP Strategic Business Management Programme right for me? In this online course, you will: Gain new perspectives for building market resilience and dominance for your organization. Understand the difference between corporate and business strategy and what it takes for a corporate headquarters to add value and increase business unit success. Study best practices in key areas of corporate strategy, including diversification, mergers and acquisitions, strategic alliances, corporate governance, and strategic leadership. Why SEMP Strategic Business Management? Strategic management is important because it helps in setting detailed goals, analyzing all internal and external resources, analyzing the external environment, as well as stakeholders’ views. Good corporate governance needs an efficient strategic management process. Who should enroll in this online Certificate Program? This non-credit-bearing course benefits professionals at all levels who want to contribute to their organization’s performance. It is ideal for directors and company executives who determine strategic directions to position their organizations well so as to lead within their different industries. The SEMP Strategic Business Management Certificate program is open to anyone interested in gaining and improving their organizational management skills. Modules What is Strategy?· Understanding Strategic Management· Understanding the Competitive Environment· Analyzing the Competitive Environment· Stakeholder Analysis, Organisational Purpose, and Organizational Vision· Understanding Core Competence· Competitive Advantages· Competitive Strategy· Strategic Choice · Strategy Formulation· Strategy Implementation· Business Ethics and Social Responsibility Accreditation The content of this course has been independently certified as conforming to universally accepted Continuous Professional Development (CPD) guidelines. Entry Requirements There are no strict entry requirements for this course. Work experience will be added advantage to understanding the content of the course. Workshops This is a self-study programme with unlimited tutor support. You will never be more than a message or phone call away from our tutors. Visa Requirements There are no Visa requirements for this course as it's an Online Course.
