- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
34842 Courses delivered Online
Systems Engineering Advanced Diploma with Project management & Scrum Master - 8 Courses Bundle
By NextGen Learning
Are you ready to embark on an enlightening journey of wisdom with the Systems Engineering bundle, and pave your way to an enriched personal and professional future? If so, then Step into a world of knowledge with our course bundle - Systems Engineering Advanced Diploma with Project management & Scrum Master. Delve into eight immersive CPD Accredited courses, each a standalone course: Course 01: Project Management Course 02: Project Planning for Everyone Course 03: Scrum Master Training Course Course 04: Strategic Management Course 05: Project Management: How to Build a Project Charter Course 06: RCA: Root Cause Analysis Course 07: Cost Control & Project Scheduling Course 08: Process Improvement: How to Reduce Waste Traverse the vast landscapes of theory, unlocking new dimensions of understanding at every turn. Let the Systems Engineering Advanced Diploma with Project management & Scrum Master bundle illuminate your path to wisdom. The Systems Engineering Advanced Diploma with Project management & Scrum Master bundle offers a comprehensive exploration into a rich tapestry of vast knowledge across eight carefully curated courses. The journey is designed to enhance your understanding and critical thinking skills. Each course within the bundle provides a deep-dive into complex theories, principles, and frameworks, allowing you to delve into the nuances of the subject matter at your own pace. In the framework of the Systems Engineering Advanced Diploma with Project management & Scrum Master package, you are bestowed with complimentary PDF certificates for all the courses included in this bundle, all without any additional charge. Adorn yourself with the Systems Engineering bundle, empowering you to traverse your career trajectory or personal growth journey with self-assurance. Register today and ignite the spark of your professional advancement! So, don't wait further and join the Systems Engineering Advanced Diploma with Project management & Scrum Master community today and let your voyage of discovery begin! Learning Outcomes: Attain a holistic understanding in the designated areas of study with the Systems Engineering bundle. Establish robust bases across each course nestled within the Systems Engineering bundle. Decipher intricate concepts through the articulate content of the Systems Engineering bundle. Amplify your prowess in interpreting, scrutinising, and implementing theories. Procure the capacity to engage with the course material on an intellectual and profound level. Become proficient in the art of problem-solving across various disciplines. Stepping into the Systems Engineering bundle is akin to entering a world overflowing with deep theoretical wisdom. Each course within this distinctive bundle is an individual journey, meticulously crafted to untangle the complex web of theories, principles, and frameworks. Learners are inspired to explore, question, and absorb, thus enhancing their understanding and honing their critical thinking skills. Each course invites a personal and profoundly enlightening interaction with knowledge. The Systems Engineering bundle shines in its capacity to cater to a wide range of learning needs and lifestyles. It gives learners the freedom to learn at their own pace, forging a unique path of discovery. More than just an educational journey, the Systems Engineering bundle fosters personal growth, enabling learners to skillfully navigate the complexities of the world. The Systems Engineering bundle also illuminates the route to a rewarding career. The theoretical insight acquired through this bundle forms a strong foundation for various career opportunities, from academia and research to consultancy and programme management. The profound understanding fostered by the Systems Engineering bundle allows learners to make meaningful contributions to their chosen fields. Embark on the Systems Engineering journey and let knowledge guide you towards a brighter future. CPD 80 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Individuals keen on deepening their firm understanding in the respective fields. Students pursuing higher education looking for comprehensive theory modules. Professionals seeking to refresh or enhance their knowledge. Anyone with a thirst for knowledge and a passion for continuous learning. Career path Armed with the Systems Engineering bundle, your professional journey can reach new heights. The comprehensive theoretical knowledge from this bundle can unlock diverse career opportunities across several fields. Whether it's academic research, consultancy, or programme management, the Systems Engineering bundle lays a solid groundwork. Certificates CPD Certificate Of Completion Digital certificate - Included 8 Digital Certificates Are Included With This Bundle CPD Quality Standard Hardcopy Certificate (FREE UK Delivery) Hard copy certificate - £9.99 Hard copy Transcript - £9.99

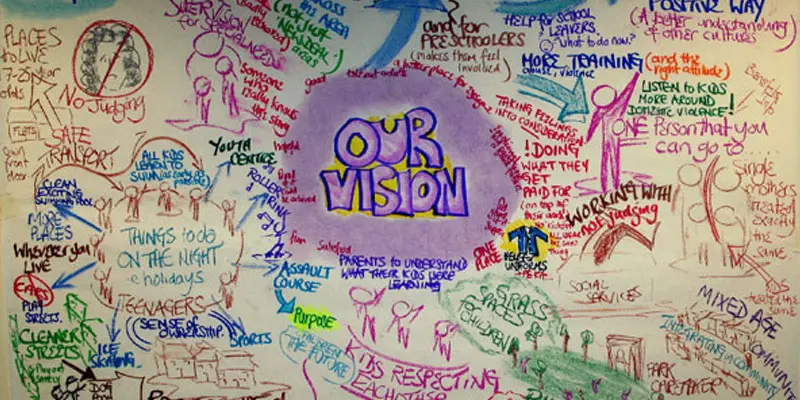
PARENT SOLUTIONS CIRCLE
By Inclusive Solutions
In this course we explore how we have attempted to build inclusive circles of support around individuals and contrast this with a radical approach to problem solving with parents – the Parent Solutions Circle. Parent Solutions is a brand new approach to problem solving with parents based on our live group work in schools. A focus on challenging behaviour brings interest, energy and commitment. Course Category Inclusion Peer Support Parents and Carers Behaviour and relationships Description In this course we explore how we have attempted to build inclusive circles of support around individuals and contrast this with a radical approach to problem solving with parents – the Parent Solutions Circle Parent Solutions is a brand new approach to problem solving with parents based on our live group work in schools. A focus on challenging behaviour brings interest, energy and commitment. Essentially the approach involves gathering a group of parents and carers together who recognise how challenging their own children are and would like some help to figure out how to be with them or how to manage an aspect of their behaviour. The process is facilitated but majors on the parents offering each other their wisdom and ideas. The directness that only peers can provide to each other makes the work both powerful and effective. Mobilising the wisdom and experiences of parents in a safe way is a delicate art. In this training we will explore how this can best be done. Parents who have been on all the courses and had all the professional advice in world love this way of working because they get to offer each other their experience, ideas and wisdom. The approach is capacity focused, person centred approach to working with parents rather than the dominant deficit oriented and ‘medical model’ of viewing and planning for parents. We work with rather than do things to a group of parents. This training can be modelled with a group of parents or can be demonstrated with a group of professionals. We prefer mixed groups. Learning Objectives For participants to learn how to set up a Parent Solutions Circle For participants to understand the underlying rationale and ethos of this way of working To learn the facilitation process and stages of the Circle process Who Is It For? Anyone interested in working with parents and carers in a way that builds and makes use of their capacities rather than focus on their challenges and difficulties. School leaders and managers Social Care teams Community organisers Psychologists Course Content True parent empowerment Facilitating groups Problem solving process Handling group communication Allowing direct feedback and challenge between participants in a safe way Building relationships Creating natural circles of support that can provide peer support and mutual problem solving If you liked this course you may well like: Creating Community Circles
CPD Accredited, Interactive Short Course 2 or 3.5 hour hr sessions What are the autistic spectrum disorder, autism and asperger's syndrome? How can you best understand, and thus help, those affected? Course Contents of the shorter course: What is ASD Autism and Asperger's Syndrome Understanding those on the Spectrum How to approach and help those on the Autistic Spectrum Great for teachers and TAs in schools, and for those working in care with older people with ASD Benefits of this Short Course: About 1% of the population is thought to be on the Autistic Spectrum That is several children per nursery and primary school and a significant amount of young people in secondary schools Many with Asperger's Syndrome will also go to university The way they experience the world is very different to 'neuro-typical' people Understanding their condition helps to support them and give them the best chance
Football Agent Training - Job Ready Program + Career Support & Money Back Guarantee
4.5(3)By Studyhub UK
The average salary for a football agent in the UK is •40,510 per year. However, top agents can earn significantly more. For example, the highest-paid football agent in the world, Mino Raiola, earned an estimated $85 million in 2021. Football agents represent professional footballers in negotiations with clubs and sponsors. They work with players to develop their careers and ensure they get the best possible deals. If you are interested in a career in football, then our Football Agent Training program can help you get started. Our program provides you with the skills and knowledge you need to be successful in this competitive industry. We also offer a variety of career development services, including: One-on-one counselling with industry professionals CV and cover letter writing assistance Job search assistance We are committed to helping you succeed in your career as a football agent. Our program provides you with the tools and resources you need to achieve your goals. So what are you waiting for? Enrol in the Football Agent Training today! Our mission is simple: to be your trusted partner and assist you every step of the way until you land the job of your dreams. Why Choose Us Here's what makes our Football Agent Training Program stand out from the crowd: Personalised Job Search Assistance: We're in this together! Our dedicated team will work tirelessly to support your entire job searching process. From crafting a standout resume to submitting it to top companies, we'll ensure you have a compelling application that gets noticed. Expertly Crafted CV: Your resume is your ticket to the interview room. Our professional resume writers will create a customised CV highlighting your unique skills and experiences. This will maximise your chances of standing out among the competition. Strategic Placement: We understand the power of casting a wide net. We'll strategically submit your CV to various platforms and networks, expanding your reach and connecting you with valuable opportunities that align with your career goals. One-On-One Consultation Sessions with Industry Experts: Gain invaluable insights and guidance from seasoned Football Agents who have thrived in the field. Our consultation sessions provide you with insider tips, tricks, and advice, empowering you to navigate the industry with confidence and expertise. Comprehensive Skill Development: Our program is designed to equip you with the most sought-after skills in the Football Agent sector. From mastering cutting-edge tools to honing your skills, we'll ensure you have the knowledge and expertise to excel in any football-driven environment. Ongoing Support: We understand that the journey to landing your dream job doesn't end with placement. That's why our commitment to your success extends well beyond your initial training. Our support team will be available to answer your questions, provide guidance, and assist you as you progress in your career. Here are the 6 courses we will provide once you enrol in the program: Course 01: Football/ Sport Agent Course 02: Sports Therapy Course 03: Sports Injuries Course 04: Sports Nutrition Course 05: Football Coach Online Course Course 06: Sports Psychology These courses will help you to develop your knowledge and skills to become a successful Football Agent. The Program is completed in 5 easy steps: Step 1 - Enrol in the program and start learning from the courses we provide After you enrol in this Football Agent Training Program, you will get lifetime access to 6 premium courses related to Football. These courses will teach you the knowledge and skills required to become a successful Football Agent. Our customer service team will help you and keep in contact with you every step of the way. Step 2 - Complete your courses and get certifications After learning from the courses, you must obtain certificates for each course. There will be exams for every course, and you have to pass them to get your certificate. To pass successfully, you must get 90% marks for the first course and 80% for the rest relevant courses. Once you pass the exams, you will receive hardcopy certificates. These certificates will prove that you're an expert in the subject. Step 3 - Get a consultation session from a professional Football Agent Take your Football Agent skills to new heights with a one-on-one consultation session led by a seasoned professional. Gain invaluable insights, expert tips, and tailored advice that will propel your career forward. Step 4 - Complete the CV and attend the interview Once you've successfully obtained the certifications, our team of professionals will build you a compelling CV and LinkedIn profile. With these powerful tools in hand, you'll be fully prepared to tackle job interviews confidently. Kickstart your Football Agent career with a starting salary ranging from •30,000 to •50,000 annually. Step into the Football Agent industry with the assurance of a promising future. Step 5 - We will not leave you until you get a job Our commitment to your success goes above and beyond. We won't stop until you land that dream job. With personalised support, expert guidance, and unwavering dedication, we'll be by your side until you secure the perfect opportunity. Your job search becomes our mission, ensuring you have the best chance at a successful career as a Football Agent. Don't let your dream career as a Football Agent remain out of reach. You just have to learn and gain knowledge and skills. Finding a job is our task! We will remove most of your worries and help you focus on only developing your skills. So join our Football Agent Training Program today, and let us be your trusted partner on your journey to success. CPD 100 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This Football Agent Training program is ideal for: Aspiring football agents eager to enter the dynamic world of sports management. Football enthusiasts seeking personalised guidance and mentorship to kick-start their careers. Individuals passionate about building connections and forging relationships within the football industry. Professionals looking to transition into a rewarding role as a football agent and in need of comprehensive training and support. Requirements No experience required. Just enrol & start learning. Career path Football Agent Training offers a clear trajectory in the UK's football industry. With our one-on-one mentoring, CV building, and job opportunity support, you'll develop the skills and connections to become a successful football agent. Secure a role with clubs, agencies, or start your own agency, negotiating contracts, scouting talent, and shaping the careers of top football stars. Certificates CPD Accredited e-Certificate Digital certificate - Included CPD Accredited Framed (Hardcopy) Certificate Hard copy certificate - Included Enrolment Letter Digital certificate - Included Student ID Card Digital certificate - Included

FSSC 22000 v6 Lead Auditor (CQI and IRCA Certified)
By QUALITY ACADEMY
Become an FSSC 22000 v6 Lead Auditor with our CQI and IRCA certified course. Gain the skills to lead food safety management audits and elevate your career. Enroll today!

WORKING WITH PARENTS AND CARERS
By Inclusive Solutions
In this practical and engaging workshop there is input on building an effective team around a child, problem solving as a team, improving communication and handling conflict. Communication with parents, problem solving and collaborating is explored. Empathy with parents who are ‘labelled’ is encouraged. Course Category Parents and Carers Description In this practical and engaging workshop there is input on building an effective team around a child, problem solving as a team, improving communication and handling conflict. Communication with parents, problem solving and collaborating is explored. Empathy with parents who are ‘labelled’ is encouraged. A key aspect of this day is ‘reframing’ how we think about the most difficult, hard to work with parents who attract many labels. Participants soon discover that they are more similar than they realise to those labelled ‘others’. The day gives those present opportunities to reflect on their attitudes and practice in relation to parents who are different. Practical ideas for joint problem solving and active engagement are fully explored. Testimonials “Made me more aware of how to approach parents and carers” “It (the conference) couldn’t have been improved. All the speakers were good” “I’ll have a more positive approach to welcoming people” “It will encourage us as practitioners to listen and think a little more. Learning Objectives Increased confidence in working with parents Access to a wider range of practical and thoughtful strategies when collaborating with parents and carers Deeper understanding of core values surrounding inclusion of disabled children in collaboration with parents and carers Opportunity to reflect on professional attitudes and behaviour towards parents with a focus on labelling and stigmatisation New skills and processes to make joint work successful Who Is It For ? Early Years and School based Practitioners Children Centre Staff Heads and Deputies SENCOs Advanced Skills Teachers Primary and secondary teachers Local Authority Support Services Social Workers Health Workers Course Content The course answers the questions: Why is this parent impossible to work with? Where do I begin to communicate with some parents? How can I collaborate with parents and carers to include high profile children or young people? Best delivered over the course of a full day we will cover: The importance of WELCOME Labelling and reframing: Setting the tone: Reframing language to describe parents Providing parents with insights about children’s behaviour using stories Circle of Courage as applied to parents Circles of Support The Intentional Building of Relationships Not doing it alone – The Importance of Teams in developing inclusive practice Problem solving: Circles of Adults/Solution Circles Community Guides If you liked this you may like: COMMUNITY CIRCLES
Primary Teaching, Educational Psychology and Teacher's Lesson Planning
By Imperial Academy
Level 3, 4 & 5 QLS Endorsed Diploma | QLS Hard Copy Certificate Included | Plus 10 CPD Courses | Lifetime Access

Social Worker Training Diploma Online
By Lead Academy
This course will equip you with the skills to work with every group of people ranging from children, adolescents, adults and people with disabilities. You will also learn how to drive a successful management system within a care home as well as how to develop community care in social services. This Course At A Glance Accredited by CPD UK Endorsed by Quality Licence Scheme Know what sports first aid is and why it is vital Understand the role of the sports coach or the first responder to injuries Identify the best practices for injury and illness prevention Discover the most common injuries in terms of sports casualties Learn about some serious injuries and how to treat and prevent them Learn about the injuries that can occur during outdoor activities Know how to administer first aid and lead rescue operations in case of water sports Learn how to perform CPR and how to use AED Learn how to report injuries, including how to comfort and reassure the injured person Know how to evaluate an injury and check for pre-existing health issues Learn how to manage and prevent an injury Social Worker Training Diploma Overview In order to keep current in the field of social work, you must use the most recent research, grasp the new rules and regulations, retain your licence or professional credential, and obtain extra training to address the demands of an ageing population that requires constant social care assistance. This Social Worker Training Diploma Online will provide you with the necessary skills and experience required for the job. It is excellent for both beginners and those who are presently employed as a health and social care workers or social and community workers. This comprehensive Social Worker Training Diploma Online provides valuable insight into the UK's healthcare system, including the codes of conduct and regulations that must be maintained. You will also gain knowledge about the principles, theories and practice models of social work. This course highlights how equality and diversity can be maintained in health and social care including the key aspects of achieving underpinning quality health and social care work in the UK. Finally, you will learn how to design an effective care plan and implement it within a social care environment. Upon successful completion of this Social Worker Training Diploma Online, you will be able to make a difference by aiding and assisting society's most vulnerable people. Who should take this course? This Social Worker Training Diploma Online is suitable for: Nurse Doctors Social care workers Aspiring Social Care worker Students in the Public Health Care field Whether you are self-taught and you want to fill in the gaps for better efficiency and productivity, this course will set you up with a solid foundation to become a confident health and social care worker or social and community worker and develop more advanced skills. This training is not, however, confined to a single profession or industry. It may also be valuable to a broader audience of people who want to learn more about the basics of social care. Entry Requirements There are no academic entry requirements for this Social Worker Training Diploma Online, and it is open to students of all academic backgrounds. However, you are required to have a laptop/desktop/tablet or smartphone and a good internet connection. Assessment Method This Social Worker Training Diploma Online assesses learners through multiple-choice questions (MCQs). Upon successful completion of the modules, learners must answer MCQs to complete the assessment procedure. Through the MCQs, it is measured how much a learner could grasp from each section. In the assessment pass mark is 60%. Course Curriculum Module 1: What Is Social Work And Community Care What Is Social Work And Community Care Module 2: Principles Of Social Work Principles Of Social Work Module 3: Theories And Practice Models Of Social Work Theories And Practice Models Of Social Work Module 4: Collaboration in social work Collaboration in social work Module 5: Relationship-based practice Relationship-based practice Module 6: About Health and Social Care About Health and Social Care Module 7: Overview of the UK HealthCare System Overview of the UK HealthCare System Module 8: Principles of Health and Social Care Principles of Health and Social Care Module 9: Codes of Conduct & Legislations in Health & Social Care in the UK Codes of Conduct & Legislations in Health & Social Care in the UK Module 10: Equality and Diversity in Health and Social Care Equality and Diversity in Health and Social Care Module 11: Management in Care Homes Management in Care Homes Module 12: Key Aspects Underpinning Quality Health & Social Care Work in the UK Key Aspects Underpinning Quality Health & Social Care Work in the UK Module 13: Social work with children and adolescent Social work with children and adolescent Module 14: Adult Social Care Adult Social Care Module 15: Social Work With People With Disabilities Social Work With People With Disabilities Module 16: Interviewing and Counselling Interviewing and Counselling Module 17: The Development of Community Care in the Social Services The Development of Community Care in the Social Services Module 18: Social Work & Community Care Management Social Work & Community Care Management Module 19: Assessment in Community Care Assessment in Community Care Module 20: Care Planning & Implementation Care Planning & Implementation Conclusion Conclusion Assessment Assessment - Social Worker Training Diploma Online Recognised Accreditation CPD Certification Service This course is accredited by continuing professional development (CPD). CPD UK is globally recognised by employers, professional organisations, and academic institutions, thus a certificate from CPD Certification Service creates value towards your professional goal and achievement. CPD certificates are accepted by thousands of professional bodies and government regulators here in the UK and around the world. Many organisations look for employees with CPD requirements, which means, that by doing this course, you would be a potential candidate in your respective field. Quality Licence Scheme Endorsed The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. It will give you a competitive advantage in your career, making you stand out from all other applicants and employees. Certificate of Achievement Endorsed Certificate from Quality Licence Scheme After successfully passing the MCQ exam you will be eligible to order the Endorsed Certificate by Quality Licence Scheme. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. It will give you a competitive advantage in your career, making you stand out from all other applicants and employees. There is a Quality Licence Scheme endorsement fee to obtain an endorsed certificate which is £65. Certificate of Achievement from Lead Academy After successfully passing the MCQ exam you will be eligible to order your certificate of achievement as proof of your new skill. The certificate of achievement is an official credential that confirms that you successfully finished a course with Lead Academy. Certificate can be obtained in PDF version at a cost of £12, and there is an additional fee to obtain a printed copy certificate which is £35. FAQs Is CPD a recognised qualification in the UK? CPD is globally recognised by employers, professional organisations and academic intuitions, thus a certificate from CPD Certification Service creates value towards your professional goal and achievement. CPD-certified certificates are accepted by thousands of professional bodies and government regulators here in the UK and around the world. Are QLS courses recognised? Although QLS courses are not subject to Ofqual regulation, they must adhere to an extremely high level that is set and regulated independently across the globe. A course that has been approved by the Quality Licence Scheme simply indicates that it has been examined and evaluated in terms of quality and fulfils the predetermined quality standards. When will I receive my certificate? For CPD accredited PDF certificate it will take 24 hours, however for the hardcopy CPD certificate takes 5-7 business days and for the Quality License Scheme certificate it will take 7-9 business days. Can I pay by invoice? Yes, you can pay via Invoice or Purchase Order, please contact us at info@lead-academy.org for invoice payment. Can I pay via instalment? Yes, you can pay via instalments at checkout. How to take online classes from home? Our platform provides easy and comfortable access for all learners; all you need is a stable internet connection and a device such as a laptop, desktop PC, tablet, or mobile phone. The learning site is accessible 24/7, allowing you to take the course at your own pace while relaxing in the privacy of your home or workplace. Does age matter in online learning? No, there is no age limit for online learning. Online learning is accessible to people of all ages and requires no age-specific criteria to pursue a course of interest. As opposed to degrees pursued at university, online courses are designed to break the barriers of age limitation that aim to limit the learner's ability to learn new things, diversify their skills, and expand their horizons. When I will get the login details for my course? After successfully purchasing the course, you will receive an email within 24 hours with the login details of your course. Kindly check your inbox, junk or spam folder, or you can contact our client success team via info@lead-academy.org

Professional Chef Training, Cooking, Kitchen & Restaurant Management with 20 Bonus Recipes
4.5(3)By Studyhub UK
This comprehensive course is designed to transform individuals into skilled chefs, equipping them not only with culinary expertise but also management proficiency in the kitchen and restaurant settings. Covering a wide range of topics from fundamental cooking skills and recipe creation to kitchen management, food business basics, and restaurant management, participants will gain a holistic understanding of the culinary world. The course also includes a bonus of 20 diverse recipes to enhance practical cooking skills. Learning Outcomes: Master essential cooking and food preparation skills. Develop a deep understanding of kitchen equipment and tools. Learn about different cooking styles and cuisines. Understand the qualities and traits of successful chefs. Gain proficiency in outdoor cooking, baking, and vegetarian cooking. Acquire knowledge in managing restaurant operations effectively. Learn marketing strategies and quality control in the food business. Enhance culinary creativity through a variety of recipes. Why buy this Professional Chef Training, Cooking, Kitchen & Restaurant Management with 20 Bonus Recipes? Unlimited access to the course for forever Digital Certificate, Transcript, student ID all included in the price Absolutely no hidden fees Directly receive CPD accredited qualifications after course completion Receive one to one assistance on every weekday from professionals Immediately receive the PDF certificate after passing Receive the original copies of your certificate and transcript on the next working day Easily learn the skills and knowledge from the comfort of your home Certification After studying the course materials of the Professional Chef Training, Cooking, Kitchen & Restaurant Management with 20 Bonus Recipes you will be able to take the MCQ test that will assess your knowledge. After successfully passing the test you will be able to claim the pdf certificate for £5.99. Original Hard Copy certificates need to be ordered at an additional cost of £9.60. Who is this course for? This Professional Chef Training, Cooking, Kitchen & Restaurant Management with 20 Bonus Recipes course is ideal for Aspiring chefs looking to establish a strong culinary foundation. Individuals interested in pursuing a career in restaurant management. Cooks and food enthusiasts aiming to refine their skills. Culinary professionals seeking to expand their expertise. Prerequisites This Professional Chef Training, Cooking, Kitchen & Restaurant Management with 20 Bonus Recipes was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Career path Line Cook - Average Salary: £18,000 - £24,000 per year. Sous Chef - Average Salary: £25,000 - £35,000 per year. Head Chef - Average Salary: £30,000 - £45,000 per year. Executive Chef - Average Salary: £40,000 - £60,000 per year. Restaurant Manager - Average Salary: £25,000 - £40,000 per year. Course Curriculum Becoming a Chef Can TV Chefs Teach You To Cook? 00:30:00 Improving Cooking And Food Preparation Skills 00:15:00 Catering To Unique Tastes 00:30:00 Qualities Of A Successful Chef 00:30:00 Achieve Perfection As A Saucier 00:30:00 Becoming The Perfect Chef 01:00:00 Equipment For Perfect Chefs 00:30:00 How To Become The Perfect Chef: Attending School 00:30:00 The Keys To Getting and Using Feedback 00:30:00 What Can You Do With A Culinary Degree 01:00:00 Knife Skills For The Perfect Chef 00:30:00 Making Meals Easy to Eat Healthy 00:30:00 Plating for the At Home Chef 00:30:00 Perfect Chefs Choose A Speciality 00:30:00 Finding Local Cooking Classes 00:30:00 How Can You Become a Professional Chef 00:30:00 The Physical Qualities of the Perfect Chef 00:15:00 The Importance of Testing Recipes 00:15:00 The Chefs Important Baking Tools 01:00:00 The Learning Curve To Becoming The Perfect Chef 00:15:00 The Job of a Professional Chef 00:30:00 The Mix of Sweet, Spicy and Savory 00:30:00 The Perfect At Home Chef 00:30:00 The Perfect Chef Opens A Restaurant 00:15:00 The Physical Demand of Being a Chef 00:15:00 Kitchen Management Buying Kitchen Equipment: Tips And Tricks To Save Money 01:00:00 The Well Equipped Kitchen 00:15:00 Take Inventory 01:00:00 Be Wary Of The Latest Trends 01:00:00 Inexpensive Vs. Cheap 00:15:00 Needing Vs. Wanting 01:00:00 Comparison Shopping 01:00:00 How To Find The Best Deals 01:00:00 Secrets Of Outdoor Cooking Recipes 01:00:00 Once A Month Cooking Recipes 00:15:00 Mother's Day Cooking Made Easy 01:00:00 Mardi Gras Cooking Cajun Style 00:30:00 Learn To Cook Italian Food On Vacation 01:00:00 Cooking With A Dutch Oven 01:00:00 Recipes Of Italian Vegetarian Cooking 01:00:00 Home Cooking Network: An Array Of Recipes 00:30:00 America's Home Cooking: The Television Program 01:00:00 A Wonderful Experience With Outdoor Cooking Burners 00:30:00 Cooking For Sunday Dinner 01:00:00 Healthy Cooking Oils 01:00:00 Cooking Cajun Food 01:00:00 Paula's Home Cooking Recipes 00:30:00 The Importance Of Eating A Healthful Vegetarian Diet 01:00:00 Italian Food On A Date 00:30:00 The History Of Pasta In Italian Food 01:00:00 Review Of Different Vegetarian Cooking Shows 00:30:00 Italian Cooking Brochutto 01:00:00 Cooking Christmas Cookies 01:00:00 Back To Beginning For President's Day Cooking 00:30:00 Microwave Bacon Cooking Equipment 00:30:00 Cheap Italian Food In Milan 01:00:00 Chinese Cooking Wok 01:00:00 7 Useful Cooking Tips And Hints 01:00:00 Down Home Cooking 00:30:00 Italian Cooking School 00:30:00 Cooking Games 00:30:00 Italian Cooking Recipes 00:30:00 French Cooking Holidays 00:30:00 Managing Restaurant Food Business Basics 01:00:00 Put Together Your Business Concept 00:30:00 Identify your Target Market 00:30:00 Identify Your Competition 00:30:00 Write A Mission Statement 00:30:00 Downline Basics 00:30:00 Equipment And Supplies 00:30:00 Marketing And Quality Control 00:30:00 Wrapping Up 00:15:00 Recipes Recipe - I 01:00:00 Recipe - II 01:00:00 Recipe - III 01:00:00 Recipe - IV 01:00:00 Recipe - V 01:00:00 Recipe - VI 00:10:00 Recipe - VII 00:10:00 Recipe - VIII 00:12:00 Recipe - IX 00:10:00 Recipe - X 00:15:00 Recipe - XI 00:30:00 Recipe - XII 00:30:00 Recipe - XIII 00:15:00 Recipe - XIV 00:30:00 Recipe - XV 00:30:00 Recipe - XVI 00:10:00 Recipe -XVII 00:15:00 Recipe -XVIII 00:15:00 Recipe -XIX 00:13:00 Recipe -XX 00:10:00 Recommended Reading Recommended Reading: Professional Cooking, Kitchen and Restaurant Management 00:00:00 Mock Exam Mock Exam- Professional Cooking, Kitchen and Restaurant Management 00:20:00 Final Exam Final Exam- Professional Cooking, Kitchen and Restaurant Management 00:20:00

Supervisor Training Level 3 & 4
By Imperial Academy
Level 4 QLS Endorsed Course | Endorsed Certificate Included | Plus 5 Career Guided Courses | CPD Accredited
