- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Network fundamentals training course description An intensive hands on IP foundation leading to LINX Accredited Internet Technician stage 1. The course focuses on all parts of TCP/IP including layers 4 to 7 on end stations as well as layer 3 on routers. The TCP/IP protocols are also studied to enable delegates to be able to troubleshoot TCP/IP using Wireshark. Hands on sessions are used to reinforce the theory rather than teach specific manufacturer equipment. A multiple choice exam, leading to the LAIT I certification, is available after the course. The exam consists of 40 questions and lasts 1.5 hours. What will you learn Use ping, traceroute and other tools to diagnose faults on a network. Configure IP on PCs and routers. Plan IP addresses and subnets. Analyse IP and TCP packets using an analyser. Troubleshoot TCP/IP. Network fundamentals training course details Who will benefit: Network engineers. Prerequisites: None Duration 5 days Network fundamentals training course contents What is TCP/IP? TCP and IP are protocols, 7 layer model, network layers, hardware/software layers, internetworking, protocols, What is IP? What is TCP? The internet, The IAB, RFCs. Ping and Wireshark Host configuration, IP addresses, subnet masks, default gateways, ping. Hands on Base configuration. Testing with ping. Analysing packets with Wireshark. Switches and Wireshark Switches versus hubs, layer 2 forwarding table, flooding, broadcasts. Hands on Building a switched based network. Configuring network devices Configuration options, console port, putty, telnet. Hands on Configuring switches, telnet. IP IP packet format, protocol field, TTL, DiffServ, fragments, ICMP. Hands on IP packet analysis. IP addressing 32 bits, dotted decimal, rules, networks, role of subnet masks, simple subnetting, prefix notation. Broadcasts, special use addresses. Hands on Planning and implementing addressing. IP and the lower layers ARP, media not supporting ARP. Hands on ARP. Routing What are routers? What routers do, default gateways, routing and addressing, routing tables, ways to update routing tables. Hands on Building a routed network, traceroute. Routing protocols IGPs and EGPs, RIP, RIPv2, Why not to use RIP, OSPF, OSPF metrics, convergence, distance vector protocols, link state protocols. Hands on OSPF, analysing routing tables, loopbacks. Network simulators Network simulators, EVE-NG, GNS3, CML. Hands on Using EVE-NG. Subnetting Subnetting to the bit level, ranges, how prefixes are used. Hands on Subnetting. VLANS and IP addressing What are VLANs, tagging, 802.1Q, Inter VLAN routing. Hands on Inter VLAN routing. TCP and UDP Layer 4, port numbers, client ports, broadcasts multicasts and layer 4, UDP header, TCP header, connections, ACK, sliding windows, options, connection states. Sockets. Hands on Analysing TCP packets. IPv4 address configuration Private addresses, NAT, NAPT, dynamic addressing, DHCP, link local addresses. Hands on DHCP, NAT. IPv6 What is IPv6, 128 bit addresses, address formats, IPv6 address allocation, header format, migration, dual stack, tunnelling, NAT64, DNS64. Hands on IPv6 setup troubleshooting. IPv6 address configuration Static addressing, EUI-64 addresses, IPv6 address order, SLAAC, DHCPv6. Hands on SLAAC. Applications Clients, servers, HTTP, Email, resource sharing, VoIP, video, terminal emulation, remote desktop. Network management and SNMP. Hands on Servers, TFTP, VoIP packet analysis. DNS Names and addresses, hosts file, how DNS works. FQDNs, DNS client configuration. Hands on Troubleshooting DNS. Security Firewalls, firewall architectures, DMZ, how firewalls work, proxy servers, filtering, ACLs, IDS, VPNs, authentication, encryption, tunnels, secure protocols. Hands on Firewalls, SSH Troubleshooting Methods, tools. Using the 7 layer model. Troubleshooting toolkits. Hands on Fixing the network.

LINX 1 training course description An intensive hands on IP foundation leading to LINX Accredited Internet Technician stage 1. The course focuses on all parts of TCP/IP including layers 4 to 7 on end stations as well as layer 3 on routers. The TCP/IP protocols are also studied to enable delegates to be able to troubleshoot TCP/IP using Wireshark. Hands on sessions are used to reinforce the theory rather than teach specific manufacturer equipment. A multiple choice exam, leading to the LAIT I certification, is available after the course. The exam consists of 40 questions and lasts 1.5 hours. What will you learn Use ping, traceroute and other tools to diagnose faults on a network. Configure IP on PCs and routers. Plan IP addresses and subnets. Analyse IP and TCP packets using an analyser. Troubleshoot TCP/IP. LINX 1 training course details Who will benefit: Network engineers. Prerequisites: None. Duration 5 days LINX 1 training course contents What is TCP/IP? TCP and IP are protocols, 7 layer model, network layers, hardware/software layers, internetworking, protocols, What is IP? What is TCP? The internet, The IAB, RFCs. Ping and Wireshark Host configuration, IP addresses, subnet masks, default gateways, ping. Hands on Base configuration. Testing with ping. Analysing packets with Wireshark. Switches and Wireshark Switches versus hubs, layer 2 forwarding table, flooding, broadcasts. Hands on Building a switched based network. Configuring network devices Configuration options, console port, putty, telnet. Hands on Configuring switches, telnet. IP IP packet format, protocol field, TTL, DiffServ, fragments, ICMP. Hands on IP packet analysis. IP addressing 32 bits, dotted decimal, rules, networks, role of subnet masks, simple subnetting, prefix notation. Broadcasts, special use addresses. Hands on Planning and implementing addressing. IP and the lower layers ARP, media not supporting ARP. Hands on ARP. Routing What are routers? What routers do, default gateways, routing and addressing, routing tables, ways to update routing tables. Hands on Building a routed network, traceroute. Routing protocols IGPs and EGPs, RIP, RIPv2, Why not to use RIP, OSPF, OSPF metrics, convergence, distance vector protocols, link state protocols. Hands on OSPF, analysing routing tables, loopbacks. Network simulators Network simulators, EVE-NG, GNS3, CML. Hands on Using EVE-NG. Subnetting Subnetting to the bit level, ranges, how prefixes are used. Hands on Subnetting. VLANS and IP addressing What are VLANs, tagging, 802.1Q, Inter VLAN routing. Hands on Inter VLAN routing. TCP and UDP Layer 4, port numbers, client ports, broadcasts multicasts and layer 4, UDP header, TCP header, connections, ACK, sliding windows, options, connection states. Sockets. Hands on Analysing TCP packets. IPv4 address configuration Private addresses, NAT, NAPT, dynamic addressing, DHCP, link local addresses. Hands on DHCP, NAT. IPv6 What is IPv6, 128 bit addresses, address formats, IPv6 address allocation, header format, migration, dual stack, tunnelling, NAT64, DNS64. Hands on IPv6 setup troubleshooting. IPv6 address configuration Static addressing, EUI-64 addresses, IPv6 address order, SLAAC, DHCPv6. Hands on SLAAC. Applications Clients, servers, HTTP, Email, resource sharing, VoIP, video, terminal emulation, remote desktop. Network management and SNMP. Hands on Servers, TFTP, VoIP packet analysis. DNS Names and addresses, hosts file, how DNS works. FQDNs, DNS client configuration. Hands on Troubleshooting DNS. Security Firewalls, firewall architectures, DMZ, how firewalls work, proxy servers, filtering, ACLs, IDS, VPNs, authentication, encryption, tunnels, secure protocols. Hands on Firewalls, SSH Troubleshooting Methods, tools. Using the 7 layer model. Troubleshooting toolkits. Hands on Fixing the network.

TCP/IP training course description An intensive hands on IP foundation leading to LINX Accredited Internet Technician stage 1. The course focuses on all parts of TCP/IP including layers 4 to 7 on end stations as well as layer 3 on routers. The TCP/IP protocols are also studied to enable delegates to be able to troubleshoot TCP/IP using Wireshark. Hands on sessions are used to reinforce the theory rather than teach specific manufacturer equipment. A multiple choice exam, leading to the LAIT I certification, is available after the course. The exam consists of 40 questions and lasts 1.5 hours. What will you learn Use ping, traceroute and other tools to diagnose faults on a network. Configure IP on PCs and routers. Plan IP addresses and subnets. Analyse IP and TCP packets using an analyser. Troubleshoot TCP/IP. TCP/IP training course details Who will benefit: Network engineers. Prerequisites: None Duration 5 days TCP/IP training course contents What is TCP/IP? TCP and IP are protocols, 7 layer model, network layers, hardware/software layers, internetworking, protocols, What is IP? What is TCP? The internet, The IAB, RFCs. Ping and Wireshark Host configuration, IP addresses, subnet masks, default gateways, ping. Hands on Base configuration. Testing with ping. Analysing packets with Wireshark. Switches and Wireshark Switches versus hubs, layer 2 forwarding table, flooding, broadcasts. Hands on Building a switched based network. Configuring network devices Configuration options, console port, putty, telnet. Hands on Configuring switches, telnet. IP IP packet format, protocol field, TTL, DiffServ, fragments, ICMP. Hands on IP packet analysis. IP addressing 32 bits, dotted decimal, rules, networks, role of subnet masks, simple subnetting, prefix notation. Broadcasts, special use addresses. Hands on Planning and implementing addressing. IP and the lower layers ARP, media not supporting ARP. Hands on ARP. Routing What are routers? What routers do, default gateways, routing and addressing, routing tables, ways to update routing tables. Hands on Building a routed network, traceroute. Routing protocols IGPs and EGPs, RIP, RIPv2, Why not to use RIP, OSPF, OSPF metrics, convergence, distance vector protocols, link state protocols. Hands on OSPF, analysing routing tables, loopbacks. Network simulators Network simulators, EVE-NG, GNS3, CML. Hands on Using EVE-NG. Subnetting Subnetting to the bit level, ranges, how prefixes are used. Hands on Subnetting. VLANS and IP addressing What are VLANs, tagging, 802.1Q, Inter VLAN routing. Hands on Inter VLAN routing. TCP and UDP Layer 4, port numbers, client ports, broadcasts multicasts and layer 4, UDP header, TCP header, connections, ACK, sliding windows, options, connection states. Sockets. Hands on Analysing TCP packets. IPv4 address configuration Private addresses, NAT, NAPT, dynamic addressing, DHCP, link local addresses. Hands on DHCP, NAT. IPv6 What is IPv6, 128 bit addresses, address formats, IPv6 address allocation, header format, migration, dual stack, tunnelling, NAT64, DNS64. Hands on IPv6 setup troubleshooting. IPv6 address configuration Static addressing, EUI-64 addresses, IPv6 address order, SLAAC, DHCPv6. Hands on SLAAC. Applications Clients, servers, HTTP, Email, resource sharing, VoIP, video, terminal emulation, remote desktop. Network management and SNMP. Hands on Servers, TFTP, VoIP packet analysis. DNS Names and addresses, hosts file, how DNS works. FQDNs, DNS client configuration. Hands on Troubleshooting DNS. Security Firewalls, firewall architectures, DMZ, how firewalls work, proxy servers, filtering, ACLs, IDS, VPNs, authentication, encryption, tunnels, secure protocols. Hands on Firewalls, SSH Troubleshooting Methods, tools. Using the 7 layer model. Troubleshooting toolkits. Hands on Fixing the network.

The Youth Worker Training Course aims to provide great insight into the skills and knowledge related to working in this area of work and applying these principles to the working world as a Youth Worker. You will learn all the necessary skills and techniques to deal with situations affecting this age group and to promote their learning. You will have the chance to develop positive working relationships with young people and see the outcomes from your efforts first hand. This youth work training course will discuss the key skills and knowledge related to children and young people, their families, your role as a youth worker, and more. Why Choose this Course? Earn a digital Certificate upon successful completion. Accessible, informative modules taught by expert instructors Study in your own time, at your own pace, through your computer tablet or mobile device Benefit from instant feedback through mock exams and multiple-choice assessments Get 24/7 help or advice from our email and live chat teams Full Tutor Support on Weekdays Course Design The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. Learn the skills you need for youth work qualification. You are taught through a combination of: Video lessons Online study supplies Mock tests Multiple-choice evaluation Certification Upon successful completion of the Animal Care course, you will be able to obtain your course completion e-certificate. A Print copy by post is also available at an additional cost of £9.99, and PDF Certificate at £4.99. The certificate in animal care will open up many career opportunities for you. What are you waiting for? Enrol today!

Free Work Life Discovery Coaching Workshop
By Women to Work
A practical and inspiring women’s development coaching workshop giving you time to reflect and focus on yourself and what’s important to you.

Introduction to Carbon Capture and Storage (CCS) for Non-Technical Professionals
By EnergyEdge - Training for a Sustainable Energy Future
About this training Carbon Capture and Storage (CCS) is an upcoming new technology that has a vital place within global efforts to decarbonise. It has a unique set of challenges, opportunities and risks to be understood and accommodated within appropriate legal, regulatory, and social and public license frameworks. The course has a strong international and global south emphasis with case studies on CCS projects and will touch on the role of CCS in developing country energy transition. The course satisfies a part of the market that is not currently catered for - the wider science, risks, financing, regulation, planning and social license aspects of CCS. These are issues that are as important as the technical issues in the sense that any of them can be a show-stopper for CCS. Training Objectives Upon completion of this course, participants will be able to: Place CCS within the context of the global geological carbon cycle and the contribution to could make to carbon abatement Explore the basic engineering and other challenges and solutions of CO2 transport and capture Recognize the geological challenges and solutions of CO2 storage Learn the methods of geological and environmental monitoring of CCS sites and why monitoring is important Understand the policy and finance challenges and solutions of CCS projects Know the importance of social license to operate and how to gain a social license to operate Target Audience This course will cater for in-company legal specialists, finance, project managers, marketing and communications specialists; as well as geologists, planners and environmental scientists in regulatory or government roles in regions considering the development of CCS. The course will provide up to date and relevant information to help in understanding opportunities and in managing risk. Geoscientists Government energy regulators and policy makers Financiers and investors Government natural resource and planning department Environmental scientists Finance professionals Marketing and communication professionals Legal specialists Project managers Course Level Basic or Foundation Trainer Your expert course leader is one of the most influential figures in British geoscience. He has 25 years' experience in geological, energy, and palaeontological science and research, including 8 years national level science leadership as the UK's chief geologist (Executive Chief Scientist and Director of Science and Technology of the British Geological Survey). He has been providing geoscience advice to Government for almost 15 years and has an excellent overview of Government policy, industrial activity and funding landscape in applied and energy geoscience, including CCUS and shale gas. He is a well-known communicator of science and has published three single-author popular science books (one award-winning), including the best introductory book on CCS 'Returning Carbon to Nature' Elsevier 2013. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

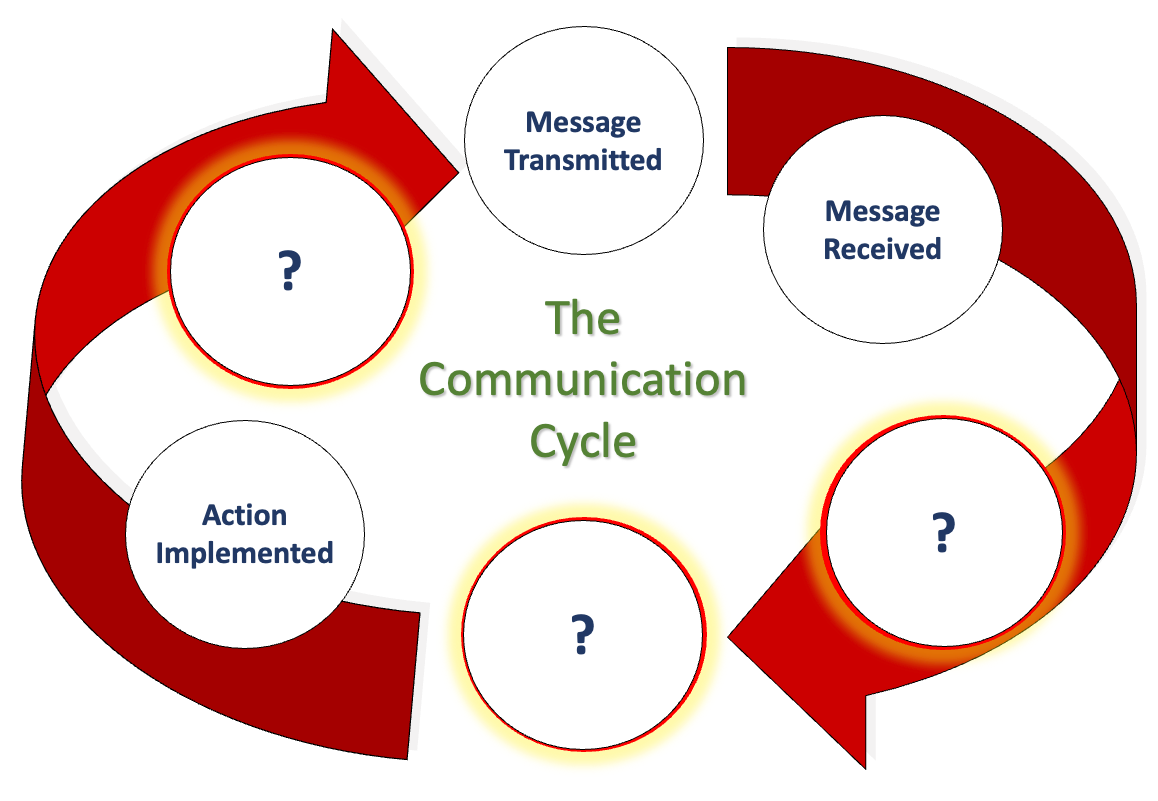
We communicate daily in many ways, including email, phone, text, Zoom, Teams, Google Meets, Slack, and even that old-fashioned thing, what was it now... oh yes, talking face-to-face. But, when we look at communication closely and really drill down into what we are doing in conjunction with how our brain works (neuroscience), how internal, organisational, and social politics control what we believe we can say, how hierarchical positioning impacts our honesty and how the lack of psychological safety means we say what we know others want to hear rather than what they need to hear…. It is oh so complicated! This workshop not only explores the concept of excellent communication, but we also want to hear what you believe it is too. We also delve into how organisational culture influences our perception of speaking up. Factors that hinder open and honest communication, and we work collaboratively towards removing these barriers to achieve a communication style that fosters trust and transparency, creating psychological safety. This workshop is particularly relevant to our Emotional Intelligence workshop (EI and Me). We firmly believe that developing emotional intelligence is the key to unlocking Clean Communication, a skill that is crucial for all of us, regardless of our roles and responsibilities, so that we thrive in our professional environment. If you want to see if we are correct, why not have us facilitate a workshop for you and see what you get by the end of it? LENGTH - Normally, one day. But please contact us to discuss your specific needs, or we can offer advice. NEXT WORKSHOP START - Please ask for more information as we deliver bespoke closed events for your people at your location or a mutually suitable location. WORKSHOP DELIVERY - The best environment for this workshop is face-to-face, but we can facilitate this workshop online. Suitability - Who should attend? Who Should Attend and Why? Who? - Perhaps think of this another way… who shouldn’t attend to ensure we can attain Clean Communication? There’s your answer. Why? - Every person needs to understand what we are saying above about how we get trapped in this organisational formatting which changes how we communicate and how it prevents us from communicating cleanly. EVERY organisation has this, despite what our values profess. And 'Values', that’s a whole other story. Workshop Content Using the 'Moccasin Approach'® to clean our personal and organisational communication LaPD’s Communication Cycle and what we must consider. (Can you work out what the ? represent above? Accountability and Responsibility raises its head in Communication. It has to. Bias, unconscious bias and its impacts on our communication. The conundrum of communicating with others and their styles (The TRAP). How would my perfect Manager/Leader communicate with me? Nonverbal communication (body language), rapport, Clean Communication. Negative communication can go viral (Self-Fulfilling Prophecy). Reflections, findings and goals (individual and team). Meeting our workshop objectives by listing five areas for development. Workshop delivery and venue This workshop is usually one day in duration, and it focuses solely on how we communicate with each other. It can also be a two-day event incorporating aspects of Emotional Intelligence (EI) with group, and individual activities to allow discussions about the various communication we need in your organisation. When you consider the content we deliver, we are sure you will understand why we always prefer to deliver our workshops, courses and programmes face-to-face. Face-to-face workshops and courses can be held at a location of your choice or, if you wish, a central UK location, such as the Macdonald Burlington Hotel in Birmingham, located directly across from the Birmingham New Street train station. We can deliver our workshops, courses and programmes online, although this will mean splitting elements into manageable learning events to suit the online environment.
Dive into the crucial world of 'Manual Handling Training' and equip yourself with skills pivotal for every workplace. This course serves as a lighthouse, guiding you through the often-misunderstood maze of work-related accidents caused by incorrect manual handling. By shedding light on risk identification, the course paves the way for robust risk assessments, ultimately culminating in effective control measures. With a special focus on safe lifting techniques, we ensure that you walk away with the confidence to navigate the demands of any workplace environment safely and efficiently. Learning Outcomes Understand the intricate link between manual handling and work-related accidents. Develop proficiency in pinpointing manual handling risks prevalent in varied settings. Master the art of conducting comprehensive manual handling risk assessments. Implement strategies to control and diminish the risks associated with manual handling. Imbibe best practices and techniques for safe lifting, ensuring workplace safety. Why choose this Manual Handling Training? Unlimited access to the course for a lifetime. Opportunity to earn a certificate accredited by the CPD Quality Standards after completing this course. Structured lesson planning in line with industry standards. Immerse yourself in innovative and captivating course materials and activities. Assessments are designed to evaluate advanced cognitive abilities and skill proficiency. Flexibility to complete the Manual Handling Training Course at your own pace, on your own schedule. Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience. Who is this Manual Handling Training for? Individuals involved in occupations with regular manual handling tasks. Health and safety officers aiming to upgrade their skillset. Managers overseeing teams in physically demanding roles. Warehouse and logistics personnel. Students contemplating careers in sectors where manual handling is paramount. Career path Health and Safety Officer: £25,000 - £40,000 Warehouse Manager: £24,000 - £35,000 Logistics Coordinator: £20,000 - £32,000 Construction Site Supervisor: £30,000 - £50,000 Facility Maintenance Manager: £28,000 - £45,000 Production Line Supervisor: £22,000 - £38,000 Prerequisites This Manual Handling Training does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Manual Handling Training was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Certification After studying the course materials, there will be a written assignment test which you can take at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £4.99 Original Hard Copy certificates need to be ordered at an additional cost of £8. Course Curriculum Manual Handling Training Module 01: Manual Handling and Work-related Accidents 00:30:00 Module 02: Identifying the Manual Handling Risks 00:30:00 Module 03: Manual Handling Risk Assessments 00:30:00 Module 04: How to Prepare a Manual Handling Operation 00:30:00 Module 05: Manual Handling Techniques 00:21:00


