- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
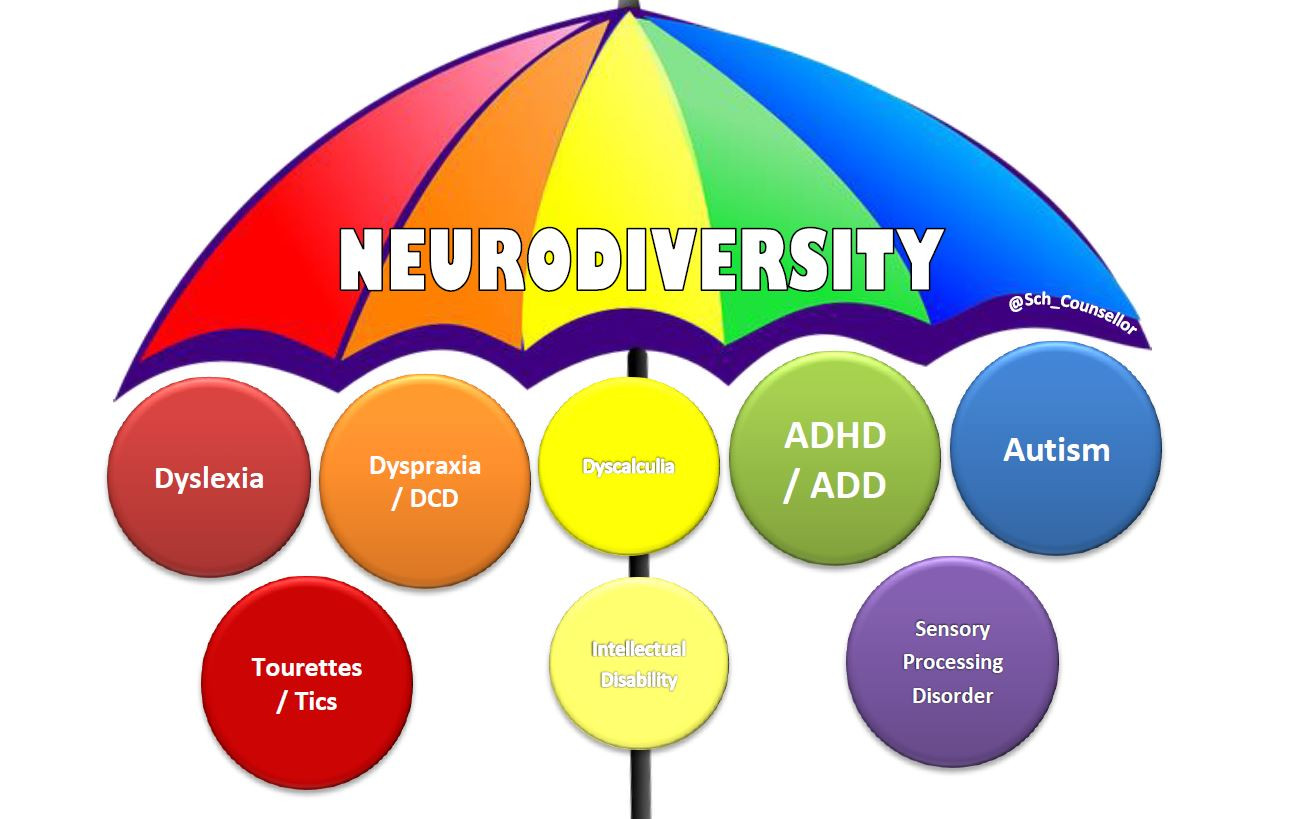
EMDR With Neurodivergent Clients 26th of September 2025
By Dr Jonathan Hutchins
A workshop on EMDR with clients who are Neurodivergent on 13th of May 2025.
XML primer training course description This course has been designed for web and intranet developers who want to accelerate their learning of XML and its applications without the grind of book learning. Although a basic knowledge of HTML and JavaScript is assumed, it is also assumed you know very little about XML and how to use it. On completion of this course you should understand the benefits of using XML and be able to design XML solutions where applicable to your company's Internet/intranet requirements. The course will be particularly beneficial if you want to know how to communicate data to diverse applications over the Internet or company intranet. What will you learn Write XML. Debug XML. Examine existing code and determine its function. XML primer training course details Who will benefit: Anyone working with XML. Prerequisites: HTML5 development fundamentals Duration 3 days XML primer training course contents The origins of XML Markup languages, SGML, document type definitions and validity, introducing XML, IE and XML, accessing content and adding style. Basic XML XML document structure, elements and attributes, grammar, well formed documents, other XML elements and references. Document Type Definition (DTDs) Creating a DTD, basic declaration, declaring elements, content definitions, entities, entity declarations, notations, defining attributes, attribute types, forcing inclusion or exclusion of DTD sections, validation. Namespaces Declaring namespaces, scoping, removing and changing namespaces, qualified names, attribute namespaces. An introduction to schemas Constructing schemas, defining the root element and its contents,<ELEMENTTYPE>, defining root element contents, adding attributes definitions, <ATTRIBUTETYPE>, <ELEMENT>, <ATTRIBUTE>. XML & the Document Object Model (DOM) What the DOM offers, DOM and W3C. Basic DOM concepts XML documents as trees, terminology of tree elements. Key DOM Objects: The document object and its creation, base objects, IE specifics, the XML node hierarchy. Programming DOM Viewing a DOM model as XML, getting the root element of a document, iterating nodes of a DOM, basic node properties, collection objects, searching for specific values, filtering a nodelist by tagname, more filtering methods, selecting nodes from their attributes. Amending Content and Structure Creating/saving a DOM as XML, changing content/structure, dynamically building a DOM. Using ASP and other techniques ASP techniques, HTTPREQUEST object, XSL, transforming and formatting XML. Formatting Using CSS. CSS And XML. XSL Transformations - XSLT Introduction, the XSL root element, applying XSL stylesheets to XML, XSL elements and operations, instructions - creating text nodes and applying templates, a 'drill-down' approach, simple output formatting, pattern filters - patterns based on position, the Match and Select attributes and their patterns, formatting output, creating new XML in output.

Complete C# programming training course description This training course teaches developers the programming skills that are required for developers to create Windows applications using the C# language. Students review the basics of C# program structure, language syntax, and implementation details, and then consolidate their knowledge throughout the week as they build an application that incorporates several features of the .NET Framework. What will you learn Use the syntax and features of C#. Create and call methods, catch and handle exceptions, and describe the monitoring requirements of large-scale applications. Implement a typical desktop application. Create class, define and implement interfaces, and create and generic collections. Read and write data to/from files. Build a GUI using XAML. Complete C# programming training course details Who will benefit: Programmers wishing to learn C#. Prerequisites: Developers attending this course should already have gained some limited experience using C# to complete basic programming tasks. Duration 5 days Complete C# programming training course contents Review of C# Syntax Overview of Writing Applications using C#, Datatypes, Operators, and Expressions. C# Programming Language Constructs. Hands on Developing the Class Enrolment Application. Methods, exceptions and monitoring apps Creating and Invoking Methods. Creating Overloaded Methods and Using Optional and Output Parameters. Handling Exceptions. Monitoring Applications. Hands on Extending the Class Enrolment Application Functionality. Developing a graphical application Implementing Structs and Enums. Organizing Data into Collections. Handling Events. Hands on Writing the Grades Prototype Application. Classes and Type-safe collections Creating Classes. Defining and Implementing Interfaces. Implementing Type-safe Collections. Hands on Adding Data Validation and Type-safety to the Grades Application. Class hierarchy using Inheritance Class hierarchies. Extending .NET framework classes. Creating generic types. Hands on Refactoring common functionality into the User Class. Reading and writing local data Reading and Writing Files. Serializing and Deserializing Data. Performing I/O Using Streams. Hands on Generating the Grades Report. Accessing a Database Creating and using entity data models. Querying and updating data by using LINQ. Hands on Retrieving and modifying grade data. Accessing remote data Accessing data across the web and in the cloud. Hands on Modifying grade data in the Cloud. Designing the UI for a graphical applicatione Using XAML to design a User Interface. Binding controls to data. Styling a UI. Hands on Customizing Student Photographs and Styling the Application. Improving performance and responsiveness Implementing Multitasking by using tasks and Lambda Expressions. Performing operations asynchronously. Synchronizing concurrent data access. Hands on Improving the responsiveness and performance of the application. Integrating with unmanaged code Creating and using dynamic objects. Managing the Lifetime of objects and controlling unmanaged resources. Hands on Upgrading the grades report. Creating reusable types and assemblies Examining Object Metadata. Creating and Using Custom Attributes. Generating Managed Code. Versioning, Signing and Deploying Assemblies. Hands on Specifying the Data to Include in the Grades Report. Encrypting and Decrypting Data Implementing Symmetric Encryption. Implementing Asymmetric Encryption. Hands on Encrypting and Decrypting Grades Reports.

Level 7 Diploma In Health And Social Care Management Pathway To MSc In Health And Social Care Management
4.9(261)By Metropolitan School of Business & Management UK
Level 7 Diploma In Health And Social Care Management Pathway To MSc In Health And Social Care Managemen Level 7 Diploma in Health and Social Care Management (QCF) – 6 - 8 Months Credits: 120 Credits The objective of the Level 7 Diploma in Health and Social Care Management qualification is to develop learners’ understanding of policy, management theory and practice in health and social care. It provides learners with an opportunity to engage with the challenges facing professionals, services users and policymakers in their own country. It will provide knowledge that underpins the ability to work as an effective manager in the hospitals/social care industry. It combines both theoretical and practical knowledge in the health and social care profession.This programme is a Pathway programme to MSc in Health and Social Care Management. Course Details Successful completion of the Level 7 Diploma in Health and Social Care Management qualification enables learners to progress into or within employment and/or continue their study towards a relevant Master’s programme with advanced standing.The Level 7 Diploma in Health and Social Care Management qualification consists of 6 mandatory units for a combined total of 120 credits, 1200 hours Total Qualification Time (TQT) and 600 Guided Learning Hours (GLH) for the completed qualification.Modules: Health and Social Care Leadership Managing People in Health and Social Care Managing Finance in Health and Social Care Health and Social Care Strategies and Policies Leading Change in Health and Social Care Research Methods for Healthcare Professionals Accreditation All MSBM courses are accredited by the relevant partners and awarding bodies. Please refer to MSBM accreditation in about us for more details. University Progression University Top-up On completion of this course, students have the opportunity to complete a Master degree programme from a range of UK universities. The top-up programme can be studied online or on campus. The top-up comprises the final 60 credits which consist of either a dissertation or a dissertation and one module. (The course tuition fee listed above does NOT include the top-up fees) University Progression Click here to see University routes and fee information for progression. Entry Requirements For entry onto the Level 7 Diploma in Health and Social Care Management leading to the MSc Health and Social Care Management qualification, learners must possess: An honours degree in related subject or UK level 6 diploma or equivalent overseas qualification i.e. Bachelors Degree or Higher National Diploma OR Mature learners (over 25) with at least 5 years of management experience if they do not possess the above qualification (this is reviewed on a case by case basis) Workshops Workshops are conducted by live webinars for all students. Visa Requirements There is no Visa requirement for this programme.

CompTIA Network+
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for entry-level computer support professionals with a basic knowledge of computer hardware, software, and operating systems who wish to increase their knowledge and understanding of networking concepts and acquire the required skills to prepare for a career in network support or administration, or who wish to prepare for the CompTIA Network+ certification. CompTIA Network+ is the first certification IT professionals specializing in network administration and support should earn. Network+ is aimed at IT professionals with job roles such as network administrator, network technician, network installer, help desk technician, and IT cable installer. This course is also designed for students who are seeking the CompTIA Network+ certification and who want to prepare for the CompTIA Network+ N10-008 Certification Exam. Overview In this course, you will describe the major networking technologies and systems of modern networks and configure, manage, and troubleshoot modern networks. Explain the OSI and TCP/IP Models. Explain properties of network traffic. Install and configure switched networks. Configure IP networks. Install and configure routed networks. Configure and monitor ports and protocols. Explain network application and storage issues. Monitor and troubleshoot networks. Explain network attacks and mitigations. Install and configure security devices. Explain authentication and access controls. Deploy and troubleshoot cabling solutions. Implement and troubleshoot wireless technologies. Compare and contrast WAN technologies. Use remote access methods. Identify site policies and best practices. CompTIA's Network+ certification is a foundation-level certification designed for IT professionals with around one year of experience, whose job role is focused on network administration. The CompTIA Network+ exam will certify the successful candidate has the knowledge and skills required to troubleshoot, configure, and manage common network devices; establish basic network connectivity; understand and maintain network documentation; identify network limitations and weaknesses; and implement network security, standards, and protocols. The candidate will have a basic understanding of enterprise technologies, including cloud and virtualization technologies. The Official CompTIA© Network+© (Exam N10-008): will teach you the fundamental principles of installing, configuring, and troubleshooting network technologies and help you to progress a career in network administration. In this course, you will build on your existing user-level knowledge and experience with personal computer operating systems and networks to master the fundamental skills and concepts that you will need to use on the job in any type of networking career. Prerequisites CompTIA A+ Certification (Exams 220-1001 and 220-1002) 1 - Explaining the OSI and TCP/IP Models Topic A: Explain OSI Model Layers Topic B: Explain the TCP/IP Suite 2 - Explaining Properties of Network Traffic Topic A: Explain Media Types and Access Methods Topic B: Deploy Ethernet Standards Topic C: Configure and Monitor Network Interfaces 3 - Installing and Configuring Switched Networks Topic A: Install and Configure Hubs and Bridges Topic B: Install and Configure Switches Topic C: Compare and Contrast Network Topologies Topic D: Compare and Contrast Network Types 4 - Configuring IP Networks Topic A: Configure IPv4 Addressing Components Topic B: Test IP Interfaces with Command Line Tools Topic C: Configure IPv4 Subnets Topic D: Configure Private and Public IPv4 Addressing Schemes Topic E: Configure IPv6 Addressing Components Topic F: Configure DHCP Services 5 - Installing and Configuring Routed Networks Topic A: Explain Characteristics of Routing Topic B: Install and Configure Routers 6 - Configuring and Monitoring Ports and Protocols Topic A: Explain the Uses of Ports and Protocols Topic B: Use Port Scanners and Protocol Analyzers Topic C: Explain the Use of Name Resolution Services Topic D: Configure DNS and IPAM Services 7 - Explaining Network Application and Storage Services Topic A: Explain the Uses of Network Applications Topic B: Explain the Uses of Voice Services and Advanced Networking Devices Topic C: Explain the Uses of Virtualization and Network Storage Services Topic D: Summarize the Concepts of Cloud Services 8 - Monitoring and Troubleshooting Networks Topic A: Monitor Network Interfaces and Logs Topic B: Explain Network Troubleshooting Methodology Topic C: Troubleshoot Common Network Services Issues 9 - Explaining Networking Attacks and Mitigations Topic A: Summarize Common Networking Attacks Topic B: Explain the Characteristics of VLANs Topic C: Explain the Characteristics of NAT and Port Forwarding 10 - Installing and Configuring Security Devices Topic A: Install and Configure Firewalls and Proxies Topic B: Explain the Uses of IDS/IPS and UTM 11 - Explaining Authentication and Access Controls Topic A: Explain Authentication Controls and Attacks Topic B: Explain the Uses of Authentication Protocols and Directory Services Topic C: Explain the Uses of Port Security and NAC Topic D: Implement Network Device Hardening Topic E: Explain Patch Management and Vulnerability Scanning Processes 12 - Deploying and Troubleshooting Cabling Solutions Topic A: Deploy Structured Cabling Systems Topic B: Deploy Twisted Pair Cabling Solutions Topic C: Test and Troubleshoot Twisted Pair Cabling Solutions Topic D: Deploy Fiber Optic Cabling Solutions 13 - Implementing and Troubleshooting Wireless Technologies Topic A: Install and Configure Wireless Technologies Topic B: Troubleshoot Wireless Performance Issues Topic C: Secure and Troubleshoot Wireless Connectivity 14 - Comparing and Contrasting WAN Technologies Topic A: Compare and Contrast WAN Core Service Types Topic B: Compare and Contrast WAN Subscriber Service Types Topic C: Compare and Contrast WAN Framing Service Types Topic D: Compae and Contrast Wireless and IoT WAN Technologies 15 - Using Remote Access Methods Topic A: Use Remote Access VPNs Topic B: Use Remote Access Management Methods 16 - Identifying Site Policies and Best Practices Topic A: Manage Networks with Documentation and Diagrams Topic B: Summarize the Purposes of Physical Security Devices Topic C: Compare and Contrast Business Continuity and Disaster Recovery Concepts Topic D: Identify Policies and Best Practices

Junos Operating System training course description This course provides students with the foundational knowledge required to work with the Junos OS and to configure Junos devices. The course provides a brief overview of the Junos device families and discusses the key architectural components of the software. The course then delves into foundational routing knowledge and configuration examples including general routing concepts, routing policy, and firewall filters. Delegates will gain experience in configuring and monitoring the Junos OS and monitoring basic device operations. This course is based on Junos OS Release 15.1X49. What will you learn Describe the design architecture of the Junos OS. Navigate within the Junos CLI and perform tasks within the CLI operational and configuration modes. Configure and monitor network interfaces. Navigate within the Junos J-Web interface. Identify where you might use firewall filters. Explain basic routing operations and concepts. Identify key factors in Juniper Networks' security. Junos Operating System training course details Who will benefit: This course benefits individuals responsible for configuring and monitoring devices running the Junos OS. Prerequisites: TCP/IP foundation for engineers Duration 3 days Junos Operating System training course contents Junos Operating System Fundamentals The Junos OS Traffic Processing Overview of Junos Devices User Interface Options-The Junos CLI User Interface Options The Junos CLI: CLI Basics The Junos CLI: Operational Mode The Junos CLI: Configuration Mode User Interface Options-The J-Web Interface The J-Web GUI Configuration Lab 1: User Interface Options Initial Configuration Factory-Default Configuration Initial Configuration Interface Configuration Lab 2: Initial System Configuration Secondary System Configuration User Configuration and Authentication System Logging and Tracing Network Time Protocol Archiving Configurations SNMP Lab 3: Secondary System Configuration Operational Monitoring and Maintenance Monitoring Platform and Interface Operation Network Utilities Maintaining the Junos OS Password Recovery System Clean-Up Lab 4: Operational Monitoring and Maintenance Interface Configuration Examples Review of the Interface Configuration Hierarchy Interface Configuration Examples Using Configuration Groups Routing Fundamentals Routing Concepts: Overview of Routing Routing Concepts: The Routing Table Routing Concepts: Routing Instances Static Routing Dynamic Routing Lab 5: Routing Fundamentals Routing Policy Routing Policy Overview Case Study: Routing Policy Lab 6: Routing Policy Firewall Filters Firewall Filters Overview Case Study: Firewall Filters Unicast Reverse-Path-Forwarding Checks Lab 7: Firewall Filters Class of Service CoS Overview Traffic Classification Traffic Queueing Traffic Scheduling Case Study: CoS Lab 8: Class of Service JTAC Procedures Opening a Support Case Customer Support Tools Transferring Files to JTAC Juniper Security Concepts Security Challenges Juniper's Security Focus Appendix A: IPv6 Fundamentals IPv6 Addressing Protocols and Services Configuration

Special Executive Master's Programme in Research Methodology
4.9(261)By Metropolitan School of Business & Management UK
Special Executive Masters Programme (S.E.M.P) This programme is geared at enhancing professionals' careers. The SEMP is an encapsulated Senior Management Programmes are short certificate modules designed for anyone who would benefit from more in-depth business knowledge delivered in a short and intensive programme What makes us different? We are a world class business school located in the heart of London, Dubai, Islamabad and Lagos. We are one of the fastest growing British business schools with a stylish blended learning model that is both online and on campus. Learn more about the programme Special Executive Master's Programme in Research Methodology Course Overview The MSBM Special Executive Masters Programmes (SEMP) allows you to update your skills, develop new skills, and explore and develop interests in a wide range of topics. These courses can be taken as personal or professional development and may enhance your employability. Organizations and Individuals that are at the peak of their business, and are blossoming or flourishing need to conduct research so as to maintain their position in the industry, or advance further and also to keep their competitors at bay. Organizations arm themselves with crucial information that will allow them to make informed business decisions when they invest in research. One needs to find out crucial information about one’s competitors, know how successful they are, what they do and do not offer, how one may be able to fill the gaps in their offering, and how to give one’s business a competitive advantage. Research Methodology will enable students to relate business to such areas as identifying your target customers, marketplace trends, production processes, and financial practices, help you predict trends, project sales, spot opportunities, and avoid potential problems. Understanding the nature of different types of business research will help you use data to maximize your sales and profits. Research Methodology is the most commonly recognized and utilized social science for studying large populations. Demand is growing worldwide for professionals who can influence social issues and conditions by conducting surveys, analyzing data, and reporting results. Help fill the growing need and enhance your career with the SEMP Research Methodology online certificate program. Course Details Mode of Study Using Web-based technology, this program provides self-paced, individualized instruction that can be taken anywhere and anytime an individual has access to a computer and the Internet. This Programme is suitable for successful professionals or specialists in the private, public, or voluntary sectors who have new management responsibilities and need to quickly expand their management knowledge. This Programme serves as a refresher course for those who have had their Masters a long time ago and need quick reminders and professional/ academic updates while it serves as a primer for those very experienced Professionals who never made time out for their masters yet they require the academic and practical relevance of this master’s experience. It is a short executive training that runs online for 3 months. Candidates will run 2 months of active lectures and series of assignments and 1 month for their dissertation. Upon successful completion of the Programme, candidates will be awarded a Continuing Professional Development (CPD) certificate in the specific Programme they have completed. What is a CPD Course? Continuing Professional Development (CPD) is the means by which professionals maintain and enhance their knowledge and skills. The world is constantly moving at a very fast pace so undertaking CPD is essential to support a professional in his/her current role as well as helping them with career progression. CPD is all about upgrading knowledge, skills, and capabilities to remain effective and compliant. A CPD course is an investment that you make in yourself. It’s a way of planning your development that links learning directly to practice. CPD can help you keep your skills and knowledge up to date and prepare you for greater responsibilities. It can boost your confidence, strengthen your professional credibility, and help you become more creative in tackling new challenges. Why SEMP Research Methodology? The Survey Research Methods online certificate program is ideal for individuals who routinely produce, analyze, or utilize survey data. Individuals who work in government, nonprofit and research organizations will benefit from this program. Completion of this program will enhance employment opportunities for expanding professions that demand evidence-based research regarding social issues and conditions. This fully online program will afford you the opportunity to: Update your research skills and demonstrate knowledge in Mixed Methods Research Add a valuable credential to your resume/vitae to help advance your career Complete the certificate in as little time as possible Basic knowledge of designing a survey The skills necessary to conduct and manage a survey project An understanding of the statistical procedures used to process and analyze survey data Who should enrol in this online Certificate Program? This non-credit-bearing course is designed to benefit professionals at all levels who want to contribute to their organization’s performance. It is ideal for directors and company executives who want to update their research skills and understand the statistical procedures and basic knowledge of how to design a survey in order for their organization to lead within its industry. The SEMP Research Methodology Certificate program is open to anyone interested in gaining and improving upon their organizational research skills. Accreditation The content of this course has been independently certified as conforming to universally accepted Continuous Professional Development (CPD) guidelines. Entry Requirements There are no strict entry requirements for this course. Work experience will be added advantage to understanding the content of the course. Workshops This is a self-study programme with unlimited tutor support. You will never be more than a message or phone call away from our tutors. Visa Requirements There are no Visa Requirements for this Course as it's an Online Course.

LNG Markets, Pricing, Trading & Risk Management
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course The LNG market is developing from a fully based market on long-term contracts, to a more flexible market based on a portfolio of contracts of different durations. The increase of LNG demand, fuelled by South Korea, Japan and several other emerging economies, are creating a base for a more flexible market, where the LNG spot market will be playing a key role. Changes in the LNG market can be identified in the following areas: development of terminals and plant sizes, increased integration throughout the supply chain, diversification of supply sources, increased contractual flexibility and increased geographical distance. This is creating the foundation for the development of the LNG spot market right here in Asia today. This 3 full-day intensive intermediate level course will give you cutting-edge knowledge needed in today's complex LNG market. Increase your knowledge and understanding of the LNG market and spot trading aspects by attending this course. Training Objectives By the end of this course, participants will be able to: Leverage on the current and global drivers of the world Natural gas and LNG markets Understand regional LNG pricing effects and who the key buyers and new sellers are Appreciate the trading structures of LNG and how to structure its risk management Understand the workings and future outlook of the Asian LNG Spot market Discover and exploit the arbitrage trading opportunities between the different markets Learn what LNG derivatives are and how it will become available for hedging and proprietary trading purposes Target Audience This course will benefit: LNG market development executives are drawn from both technical and non-technical (commercial, finance and legal) backgrounds. Participants in an LNG market development team, perhaps with expertise in one area of gas development, will benefit from the course by obtaining a good grounding of all other areas. The course is pitched at an intermediate level, although those with a basic knowledge will be able to grasp most of the concepts covered. Course Level Intermediate Trainer Your course leader is a skilled and accomplished professional with over 25 years of extensive C-level experience in the energy markets worldwide. He has strong expertise in all the aspects of (energy) commodity markets, international sales, marketing of services, derivatives trading, staff training and risk management within dynamic and high-pressure environments. He received a Master's degree in Law from the University of Utrecht in 1987. He started his career at the NLKKAS, the Clearing House of the Commodity Futures Exchange in Amsterdam. After working for the NLKKAS for five years, he was appointed as Member of the Management Board of the Agricultural Futures Exchange (ATA) in Amsterdam at the age of 31. While working for the Clearing House and exchange, he became an expert in all the aspects of trading and risk management of commodities. In 1997, he founded his own specialist-consulting firm that provides strategic advice about (energy) commodity markets, trading and risk management. He has advised government agencies such as the European Commission, investment banks, major utilities, and commodity trading companies and various energy exchanges and market places in Europe, CEE countries, North America and Asia. Some of the issues he has advised on are the development and implementation of a Risk Management Framework, investment strategies, trading and hedging strategies, initiation of Power Exchanges (APX) and other trading platforms, the set-up of (OTC) Clearing facilities, and feasibility and market studies like for the Oil, LNG and the Carbon Market. The latest additions are (Corporate) PPAs and Artificial Intelligence for energy firms. He has given numerous seminars, workshops and (in-house) training sessions about both the physical and financial trading and risk management of commodity and carbon products. The courses have been given to companies all over the world, in countries like Japan, Singapore, Thailand, United Kingdom, Germany, Poland, Slovenia, Czech Republic, Malaysia, China, India, Belgium and the Netherlands. He has published several articles in specialist magazines such as Commodities Now and Energy Risk and he is the co-author of a book called A Guide to Emissions Trading: Risk Management and Business Implications published by Risk Books in 2004. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

TEMA & HTRI Heat Exchanger Design & Cost Saving Management – Virtual Instructor Led Training (VILT)
By EnergyEdge - Training for a Sustainable Energy Future
Acquire in-depth knowledge of heat exchanger design and cost-saving management with EnergyEdge's TEM & HTRI course. Join our virtual instructor-led training to stay ahead in the industry.

RESILIA Foundation: In-House Training
By IIL Europe Ltd
RESILIA™ Foundation: In-House Training AXELOS RESILIA™: Cyber Resilience Best Practice is designed to help commercial and government organizations around the world prevent, detect, and correct any impact cyber attacks will have on the information required to do business. Adding RESILIA to the existing AXELOS global best practice portfolio, including ITIL® and PRINCE2®, brings a common cyber resilience best practice for security, IT service management, and business. Active cyber resilience is achieved through people, process, and technology. The RESILIA™ Foundation course starts with the purpose, key terms, the distinction between resilience and security, and the benefits of implementing cyber resilience. It introduces risk management and the key activities needed to address risks and opportunities. Further, it explains the relevance of common management standards and best practice frameworks to achieve cyber resilience. Subsequently, it identifies the cyber resilience processes, the associated control objectives, interactions, and activities that should be aligned with corresponding ITSM activities. In the final part of the course, it describes the segregation of duties and dual controls related to cyber resilience roles and responsibilities. What you will Learn At the end of this course, you will be able to: Demonstrate your knowledge of the purpose, benefits, and key terms of cyber resilience Demonstrate your knowledge of the risk management and the key activities needed to address risks and opportunities Demonstrate your knowledge of the purpose of a management system and how best practices and standards can contribute Demonstrate your knowledge of the cyber resilience strategy, the associated control objectives, and their interactions with ITSM activities Demonstrate your knowledge of cyber resilience design, the associated control objectives, and their interactions with ITSM activities Demonstrate your knowledge of cyber resilience transition, the associated control objectives, and their interactions with ITSM activities Demonstrate your knowledge of cyber resilience operation, the associated control objectives, and their interactions with ITSM activities Demonstrate your knowledge of cyber resilience continual improvement, the associated control objectives, and their interactions with ITSM activities Demonstrate your knowledge of the purpose and benefits of segregation of duties and dual controls Course Introduction Course Learning Objectives Course Agenda Activities Course Book Structure RESILIA Certification Introduction to Cyber Resilience What is Cyber Resilience? Defining Cyber Resilience Balancing in Cyber Resilience Characteristics of Cyber Resilience Risk Management Understanding Risk Management: Discussion Defining Risk Management Addressing Risks and Opportunities Managing Cyber Resilience Why and What of Management Systems? Management Systems Common Management Standards and Frameworks Cyber Resilience Strategy What is Strategy? Cyber Resilience Strategy and Activities Security Controls at Cyber Resilience Strategy Interaction Between ITSM Processes and Cyber Resilience Cyber Resilience Design Why Cyber Resilience Design? Cyber Resilience Design Activities Security Controls at Cyber Resilience Design Aligning ITSM Processes with Cyber Resilience Processes Cyber Resilience Transition Why Cyber Resilience Transition? Basics of Cyber Resilience Transition Cyber Resilience Transition: Controls Interaction Between ITSM Processes and Cyber Resilience Cyber Resilience Operation The Purpose of Cyber Resilience Operation Security Controls in Cyber Resilience Operation Interaction Between IT Processes and Cyber Resilience Interaction Between ITSM Functions and Cyber Resilience Cyber Resilience Continual Improvement Continual or Continuous Improvement Maturity Models Continual Improvement Controls The Seven-Step Improvement Process The ITIL CSI Approach Cyber Resilience Roles & Responsibilities Segregating Duties Dual Controls
