- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
DevOps Leader (DOL)©
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for The target audience for the DevOps Leader course are professionals including: Anyone starting or leading a DevOps cultural transformation program, Anyone interested in modern IT leadership and organizational change approaches, Business Managers, Business Stakeholders, Change Agents, Consultants, DevOps Consultants, DevOps Engineers, IT Directors, IT Managers, IT Team, Leaders, Lean Coaches, Practitioners, Product Owners, Scrum Masters, System Integrators, Tool Providers Overview The learning objectives for DOL include a practical understanding of: - DevOps and time to market - The business and IT perspectives - Key differences between DevOps IT and traditional IT - Planning and organizing - Understanding performance and culture - Measurement differences - Designing a DevOps organization - Focusing on what matters - Ideas for organizing workflows - Sharing information - Defining meaningful metrics - Value stream mapping - The Spotify Squad model - Managing culture change - Popular tools and key practices - Putting it all together The DevOps Leader course is a unique and practical experience for participants who want to take a transformational leadership approach and make an impact within their organization by implementing DevOps. Leading people through a cultural transformation requires new skills, innovative thinking, and transformational leadership. Leaders up, down and across the IT organization must align and collaborate to break down silos and evolve the organization. The course highlights the human dynamics of cultural change and equips participants with practices, methods, and tools to engage people across the DevOps spectrum through the use of real-life scenarios and case studies. Upon completion of the course, participants will have tangible takeaways to leverage when back in the office such as understanding Value Stream Mapping. Prerequisites DevOps Foundation 1 - DevOps and Time What Is DevOps? Why Do DevOps Companies Doing DevOps The Magic Equation 2 - Key Differences Between DevOps IT and Traditional IT What Sets DevOps IT apart from Traditional IT How DevOps IT is Organized Differently How to Perform to a Different Standard How to Use Different Measurements 3 - Becoming a DevOps organization Transformational Leadership Redesigning An Organization for DevOps Design Principles Focus Work Information Metrics 4 - Value Stream Mapping What is Value Stream Mapping? Why Do We Need to Use this Framework? Types of Maps How to Create a Value Stream Map? Types of Data to Collect How to Handle Exceptions 5 - Value Stream Mapping Exercise 6 - Squad Organizational Model Conway's Law The Problem with Silos Spotify?s Squad Organization Model (Structure, Roles) Squads Tribes Chapters Guilds How to Reorganize in Order to Move to this Model 7 - Managing Culture Change What is Culture and How Does it Impact Performance? Types of IT Culture Cultural Traits of a DevOps Organization How to Manage Change 8 - Culture and its Impact on Performance Types of IT Culture What is a DevOps Culture How To Manage Change The Three Phases Of Change Types of Changes That Need to be Implemented 9 - Popular DevOps Tools and Practices DevOps Tools Periodic Table Top DevOps Tool Categories Common and Popular Practices 10 - Building a Business Case 11 - Bringing it all Together 12 - Additional Sources of Information 13 - Exam Preparations Exam Requirements, Question Weighting, and Terminology List Sample Exam Review Additional course details: Nexus Humans DevOps Leader (DevOps Institute) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the DevOps Leader (DevOps Institute) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

SC-400T00 Administering Information Protection and Compliance in Microsoft 365
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The information protection administrator translates an organization?s risk and compliance requirements into technical implementation. They are responsible for implementing and managing solutions for content classification, data loss prevention (DLP), information protection, data lifecycle management, records management, privacy, risk, and compliance. They also work with other roles that are responsible for governance, data, and security to evaluate and develop policies to address an organization's risk reduction and compliance goals. This role assists workload administrators, business application owners, human resources departments, and legal stakeholders to implement technology solutions that support the necessary policies and controls. Learn how to protect information in your Microsoft 365 deployment. This course focuses on data lifecycle management and information protection and compliance within your organization. The course covers implementation of data loss prevention policies, sensitive information types, sensitivity labels, data retention policies, Microsoft Purview Message Encryption, audit, eDiscovery, and insider risk among other related topics. The course helps learners prepare for the Microsoft Information Protection Administrator exam (SC-400). Prerequisites Foundational knowledge of Microsoft security and compliance technologies. Basic knowledge of information protection concepts. Understanding of cloud computing concepts. Understanding of Microsoft 365 products and services. 1 - Introduction to information protection and data lifecycle management in Microsoft Purview Know your data Protect your data Prevent data loss Govern your data 2 - Classify data for protection and governance Data classification overview Classify data using sensitive information types Classify data using trainable classifiers Review sensitive information and label usage Explore labeled and sensitive content Understand activities related to your data 3 - Create and manage sensitive information types Compare built-in versus custom sensitive information types Create and manage custom sensitive information types Describe custom sensitive information types with exact data match Implement document fingerprinting Create keyword dictionary 4 - Understand Microsoft 365 encryption Learn how Microsoft 365 data is encrypted at rest Understand service encryption in Microsoft Purview Explore customer key management using Customer Key Learn how data is encrypted in-transit 5 - Deploy Microsoft Purview Message Encryption Implement Microsoft Purview Message Encryption Implement Microsoft Purview Advanced Message Encryption Use Microsoft Purview Message Encryption templates in mail flow rules 6 - Protect information in Microsoft Purview Information protection overview Configure sensitivity labels Configure sensitivity label policies Configure auto-labeling policies Manage, monitor, and remediate information protection 7 - Apply and manage sensitivity labels Apply sensitivity labels to Microsoft Teams, Microsoft 365 groups, and SharePoint sites Plan on-premises labeling Configure on-premises labeling for the Unified Labeling Scanner Apply protections and restrictions to email and files Monitor label performance using label analytics 8 - Prevent data loss in Microsoft Purview Data loss prevention overview Identify content to protect Define policy settings for your DLP policy Test and create your DLP policy Prepare Endpoint DLP Manage DLP alerts in the Microsoft Purview compliance portal View data loss prevention reports Implement the Microsoft Purview Extension 9 - Configure DLP policies for Microsoft Defender for Cloud Apps and Power Platform Configure data loss prevention policies for Power Platform Integrate data loss prevention in Microsoft Defender for Cloud Apps Configure policies in Microsoft Defender for Cloud Apps Manage data loss prevention violations in Microsoft Defender for Cloud Apps 10 - Manage data loss prevention policies and reports in Microsoft 365 Configure data loss prevention for policy precedence Implement data loss prevention policies in test mode Explain data loss prevention reporting capabilities Manage permissions for data loss prevention reports Manage and respond to data loss prevention policy violations 11 - Manage the data lifecycle in Microsoft Purview Data Lifecycle Management overview Configure retention policies Configure retention labels Configure manual retention label policies Configure auto-apply retention label policies Import data for Data Lifecycle Management Manage, monitor, and remediate Data Lifecycle Management 12 - Manage data retention in Microsoft 365 workloads Explain retention in Exchange Online Explain retention in SharePoint Online and OneDrive Explain retention in Microsoft Yammer Activate archive mailboxes in Microsoft Exchange Apply mailbox holds in Microsoft Exchange Recover content in Microsoft Exchange 13 - Manage records in Microsoft Purview Records management overview Import a file plan Configure retention labels Configure event driven retention Manage, monitor, and remediate records 14 - Explore compliance in Microsoft 365 Plan for security and compliance in Microsoft 365 Plan your beginning compliance tasks in Microsoft Purview Manage your compliance requirements with Compliance Manager Examine the Compliance Manager dashboard Analyze the Microsoft Compliance score 15 - Search for content in the Microsoft Purview compliance portal Explore Microsoft Purview eDiscovery solutions Create a content search View the search results and statistics Export the search results and search report Configure search permissions filtering Search for and delete email messages 16 - Manage Microsoft Purview eDiscovery (Standard) Explore Microsoft Purview eDiscovery solutions Implement Microsoft Purview eDiscovery (Standard) Create eDiscovery holds Search for content in a case Export content from a case Close, reopen, and delete a case 17 - Manage Microsoft Purview eDiscovery (Premium) Explore Microsoft Purview eDiscovery (Premium) Implement Microsoft Purview eDiscovery (Premium) Create and manage an eDiscovery (Premium) case Manage custodians and non-custodial data sources Analyze case content 18 - Manage Microsoft Purview Audit (Standard) Explore Microsoft Purview Audit solutions Implement Microsoft Purview Audit (Standard) Search the audit log Export, configure, and view audit log records Use audit log searching to investigate common support issues 19 - Prepare Microsoft Purview Communication Compliance Plan for communication compliance Identify and resolve communication compliance workflow Case study--Configure an offensive language policy Investigate and remediate communication compliance alerts 20 - Manage insider risk in Microsoft Purview Insider risk management overview Create and manage insider risk policies Investigate insider risk alerts Take action on insider risk alerts through cases Manage insider risk management forensic evidence Create insider risk management notice templates 21 - Implement Microsoft Purview Information Barriers Explore Microsoft Purview Information Barriers Configure information barriers in Microsoft Purview Examine information barriers in Microsoft Teams Examine information barriers in OneDrive Examine information barriers in SharePoint 22 - Manage regulatory and privacy requirements with Microsoft Priva Create and manage risk management policies Investigate and remediate risk management alerts Create rights requests Manage data estimate and retrieval for rights requests Review data from rights requests Get reports from rights requests 23 - Implement privileged access management Case study--Implementing privileged access management 24 - Manage Customer Lockbox Manage Customer Lockbox requests

DP-300T00 Administering Microsoft Azure SQL Solutions
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The audience for this course is data professionals managing data and databases who want to learn about administering the data platform technologies that are available on Microsoft Azure. This course is also valuable for data architects and application developers who need to understand what technologies are available for the data platform with Azure and how to work with those technologies through applications. This course provides students with the knowledge and skills to administer a SQL Server database infrastructure for cloud, on-premises and hybrid relational databases and who work with the Microsoft PaaS relational database offerings. Additionally, it will be of use to individuals who develop applications that deliver content from SQL-based relational databases. Prerequisites In addition to their professional experience, students who take this training should have technical knowledge equivalent to the following courses: AZ-900T00 Microsoft Azure Fundamentals DP-900T00 Microsoft Azure Data Fundamentals 1 - Prepare to maintain SQL databases on Azure Describe Microsoft Intelligent Data Platform roles Understand SQL Server in an Azure virtual machine Design Azure SQL Database for cloud-native applications Explore Azure SQL Database Managed Instance 2 - Deploy IaaS solutions with Azure SQL Explain IaaS options to deploy SQL Server in Azure Understand hybrid scenarios Explore performance and security Explain high availability and disaster recovery options 3 - Deploy PaaS solutions with Azure SQL Explain PaaS options for deploying SQL Server in Azure Explore single SQL database Deploy SQL database elastic pool Understand SQL database hyperscale Examine SQL managed instance Describe SQL Edge 4 - Evaluate strategies for migrating to Azure SQL Understand compatibility level Understand Azure preview features Describe Azure database migration options 5 - Migrate SQL workloads to Azure SQL databases Choose the right SQL Server Instance option in Azure Migrate SQL Server to Azure SQL Database offline Migrate SQL Server to Azure SQL Database online Load and move data to Azure SQL Database 6 - Migrate SQL workloads to Azure Managed Instances Evaluate migration scenarios to SQL Database Managed Instance Migrate to SQL Database Managed Instance Load and Move data to SQL Database Managed Instance 7 - Configure database authentication and authorization Describe Active Directory and Azure Active Directory Describe authentication and identities Describe Security Principals Describe database and object permissions Identify authentication and authorization failures 8 - Protect data in-transit and at rest Explore Transparent Data Encryption Configure server and database firewall rules Explain object encryption and secure enclaves Enable encrypted connections Describe SQL injection Understand Azure Key Vault 9 - Implement compliance controls for sensitive data Explore data classification Explore server and database audit Implement Dynamic Data Masking Implement Row Level security Understand Microsoft Defender for SQL Explore Azure SQL Database Ledger Implement Azure Purview 10 - Describe performance monitoring Describe performance monitoring tools Describe critical performance metrics Establish baseline metrics Explore extended events Describe Azure SQL Insights Explore Query Performance Insight 11 - Configure SQL Server resources for optimal performance Explain how to optimize Azure storage for SQL Server virtual machines Describe virtual machine resizing Optimize database storage Control SQL Server resources 12 - Configure databases for optimal performance Explore database maintenance checks Describe database scoped configuration options Describe automatic tuning Describe intelligent query processing 13 - Explore query performance optimization Understand query plans Explain estimated and actual query plans Describe dynamic management views and functions Explore Query Store Identify problematic query plans Describe blocking and locking 14 - Evaluate performance improvements Describe wait statistics Tune and maintain indexes Understand query hints 15 - Explore performance-based design Describe normalization Choose appropriate data types Design indexes 16 - Automate deployment of database resources Describe deployment models in Azure Automate deployment by using Azure Resource Manager templates and Bicep Automate deployment by using PowerShell Automate deployment by using Azure CLI 17 - Create and manage SQL Agent jobs Create a SQL Server maintenance plan Describe task status notifications 18 - Manage Azure PaaS tasks using automation Explore Elastic jobs Understand Azure Automation Build an automation runbook Automate database workflows by using Logic Apps Monitor automated tasks 19 - Describe high availability and disaster recovery strategies Describe recovery time objective and recovery point objective Explore high availability and disaster recovery options Describe Azure high availability and disaster recovery features for Azure Virtual Machines Describe high availability and disaster recovery options for PaaS deployments Explore an IaaS high availability and disaster recovery solution Describe hybrid solutions 20 - Explore IaaS and PaaS solutions for high availability and disaster recovery Describe failover clusters in Windows Server Configure Always-on availability groups Describe temporal tables in Azure SQL Database Describe active geo-replication for Azure SQL Database Explore auto-failover groups for Azure SQL Database and Azure SQL Managed Instance 21 - Back up and restore databases Back up and restore SQL Server running on Azure virtual machines Back up a SQL Server virtual machine Back up and restore a database using Azure SQL Database Additional course details: Nexus Humans DP-300T00: Administering Microsoft Azure SQL Solutions training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the DP-300T00: Administering Microsoft Azure SQL Solutions course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Lubricants Blending and Quality Assurance (Accredited by the United Kingdom Lubricants Association (UKLA))
By EnergyEdge - Training for a Sustainable Energy Future
About this Virtual Instructor Led Training (VILT) Accredited by the United Kingdom Lubricants Association (UKLA), this 4 half-day Virtual Instructor Led Training (VILT) course will provide an in-depth understanding of the principles, economics and flexibility of lubricant blending plants and how to operate a lubricants blending plant efficiently and economically. The latest developments and trends in lubricant blending and the advantages and disadvantages of lubricant blending equipment, facilities and operations will be discussed. The importance of testing components and products for each blend, lubricant blend quality control and product quality management will also be explained. The VILT course will also clarify the importance of lubricant product filling, packaging and warehouse storage, strategies for optimising existing lubricant blending plant facilities and how to avoid or minimise problems with lubricant blending and product quality. The VILT course is recognised under the UKLA Continuing Professional Development (CPD) scheme for Registered Lubricant Professional. *There will be an examination for this VILT. Training Objectives This VILT course will enable you to: Learn about Mineral Oil Base Oils; API Groups I, II and III: Properties and Characteristics Acquire the knowledge about Synthetic Base Oils; API Groups IV and V: Properties and Characteristics Learn about Lubricant Additives: Properties and Characteristics Know the Lubricant Formulation and Ease of Blending Explore the Blending Plant Design: Grassroots Plants and Upgrading Existing Plants Learn about Blending Plant Equipment and Facilities and Their Operation Understand the Lubricant Blending Issues: Avoiding Problems Test and Analyse Base Oils and Additives Test and Analyse Blended Lubricants Explore the importance of Product Quality Control Understand the process of Lubricant Packaging and Filling Understand the process of Lubricant Storage Learn about Product Quality Management Target Audience This VILT course will be useful and applicable for: Middle and Senior managers to understand how and why to design and operate an efficient and profitable lubricant blending plant. Blending plant operators and specialists to improve and optimise current blending plant operations. Manufacturers of lubricants will understand how and why high quality components and effective testing during the entire blending process are important to final lubricant product quality and performance. Lubricant formulators will understand the importance of close communication and co-operation with blending plant managers and operators to minimise blending costs and to thereby maximise product profitability. Course Level Intermediate Training Methods The VILT course will be delivered online in 4 half-day sessions comprising 4 hours per day, with 2 breaks of 10 minutes per day. Course Duration: 4 half-day sessions, 4 hours per session (16 hours in total). Trainer Your expert course leader (CChem, MRC) has worked as Sales, Technical Marketing Manager and Company Director with over 50 years of broad experience in the lubricants, fuels, petroleum additives, with four leading companies Chevron, Ethyl Petroleum Additives Ltd, Texaco Limited and Kuwait Petroleum (GB) Ltd. His major recent responsibilities have been concerned with leading the Oil Industry Association United Kingdom Lubricants Association, and acting in an advisory capacity as Technical Director to the Association. He has acquired a wide experience in technical, marketing and sales within the oil industry. The related experience gained with the oil additives industry has provided him with special additional insights. He has also led the Certificate of Lubricant Competence course for the United Kingdom Lubricants Association (UKLA) for 11 years. He is a Chartered Chemist and a Member of the Royal Society of Chemistry. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information about post training coaching support and fees applicable for this. Accreditions And Affliations

Fundamentals of Dermatology
By BBO Training
Course Description:This intensive two-day course on the Fundamentals of Dermatology for Primary Care is highly relevant for healthcare professionals in primary care, especially those lacking dermatology in their post-registration training. The course offers an opportunity to advance in practice, gain relevant competencies, and enhance clinical confidence for improved patient care.Introduction:Understanding dermatology care is vital in general practice, given that 10-15% of the primary care workload involves dermatology. Common skin conditions have a significant psychological impact on patients. The course emphasizes the importance of proper skin assessment, accurate diagnosis, and effective patient self-management for better treatment outcomes.Day One:- 09:15 AM: Coffee and registration- 09:30 AM: Introduction and course objectives- 09:40 AM: Anatomy and physiology of normal skin- 10:00 AM: Pathophysiology of acne, eczema, and psoriasis - understanding skin changes- 10:45 AM: Coffee break- 11:00 AM: The language of dermatology - effective description- 11:45 AM: Skin assessment and history-taking - recording observations- 13:00 PM: Lunch break- 13:45 PM: Recognizing skin changes: skin lesions and skin cancer - addressing concerns- 14:00 PM: Hyper and hypo pigmentation - understanding variations- 14:30 PM: Screening for skin cancer and promoting sun safety- 15:00 PM: Dermatology resources and guidelines - accessing information- 16:00 PM: Action plan, evaluation, and resources- 16:15 PM: CloseDay Two:- 09:15 AM: Welcome back and course work review- 09:30 AM: Managing acne in primary care - practical applications and treatments- 10:30 AM: Managing psoriasis in primary care - topical treatment and demonstrations- 10:45 AM: Coffee break- 11:00 AM: Managing eczema in primary care - practical challenges and solutions- 11:45 AM: Understanding patient self-management and psycho-social aspects- 12:30 PM: Lunch break- 13:30 PM: Practical emollient workshop - exploring patient preferences- 14:15 PM: Skin infections - recognition, diagnosis, and management- 14:45 PM: Genital skin conditions - Update on lichen sclerosis recognition and treatment- 15:30 PM: Practice reviews, competencies, and reflective discussion- 16:15 PM: CloseCourse Aim:To equip primary care healthcare professionals with evidence-based knowledge and practical confidence to elevate dermatology care, improve patient support for common skin conditions, and ensure appropriate secondary care referral.Learning Outcomes (Day 1):- Develop a Strong Foundation: Understand skin anatomy and physiology for a comprehensive grasp of normal skin characteristics.- Decipher Pathophysiology: Discern the intricacies of common dermatology conditions, such as acne, eczema, and psoriasis, understanding the underlying skin changes that drive these conditions.- Master the Language of Dermatology: Gain proficiency in describing dermatological observations accurately, facilitating effective communication and reporting.- Harness the Power of Assessment: Elevate skin assessment and history-taking skills, honing the ability to document observations and pertinent patient history with precision.- Recognise Skin Changes: Sharpen the skill of identifying skin lesions and potential indicators of skin cancer, equipped with the expertise to navigate the "when to worry" challenge.- Explore Pigmentation Variations: Delve into hyper and hypo pigmentation, understanding conditions like dermatosis papulosa nigra, sebaceous hyperplasia, solar lentigo, and freckles.- Promote Sun Safety and Dermatology Education: Grasp strategies for skin cancer screening and sun safety healthcare education, contributing to proactive patient care.- Navigate Dermatology Resources: Gain insight into valuable dermatology resources and guidelines, empowering continuous learning beyond the course.Learning Outcomes (Day 2):- Enhance Practical Skills: Gain hands-on experience in managing common skin conditions like acne, psoriasis, and eczema using both over-the-counter and topical treatments.- Empower Patient Support: Engage with patients to gain insights into their experiences of self-managing chronic skin conditions, focusing on psycho-social aspects and effective coping strategies.- Immerse in Practical Emollient Workshop: Participate in a tactile workshop to understand patient preferences and choices in emollient usage.- Refine Diagnostic Skills: Develop the ability to recognize, diagnose, and manage skin infections effectively, improving overall dermatological care.- Master Genital Skin Conditions: Gain updated knowledge on recognising and treating genital skin conditions like lichen sclerosis, enhancing expertise in a specialized area.- Reflect and Consolidate: Engage in reflective discussions, reviewing competencies gained during the course and integrating newfound insights.Course Conclusion:Conclude the two-day course with a profound sense of accomplishment, armed with enriched dermatological knowledge, practical skills, and patient-centered strategies that will positively influence your professional practice.

DP-203T00 Data Engineering on Microsoft Azure
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The primary audience for this course is data professionals, data architects, and business intelligence professionals who want to learn about data engineering and building analytical solutions using data platform technologies that exist on Microsoft Azure. The secondary audience for this course includes data analysts and data scientists who work with analytical solutions built on Microsoft Azure. In this course, the student will learn how to implement and manage data engineering workloads on Microsoft Azure, using Azure services such as Azure Synapse Analytics, Azure Data Lake Storage Gen2, Azure Stream Analytics, Azure Databricks, and others. The course focuses on common data engineering tasks such as orchestrating data transfer and transformation pipelines, working with data files in a data lake, creating and loading relational data warehouses, capturing and aggregating streams of real-time data, and tracking data assets and lineage. Prerequisites Successful students start this course with knowledge of cloud computing and core data concepts and professional experience with data solutions. AZ-900T00 Microsoft Azure Fundamentals DP-900T00 Microsoft Azure Data Fundamentals 1 - Introduction to data engineering on Azure What is data engineering Important data engineering concepts Data engineering in Microsoft Azure 2 - Introduction to Azure Data Lake Storage Gen2 Understand Azure Data Lake Storage Gen2 Enable Azure Data Lake Storage Gen2 in Azure Storage Compare Azure Data Lake Store to Azure Blob storage Understand the stages for processing big data Use Azure Data Lake Storage Gen2 in data analytics workloads 3 - Introduction to Azure Synapse Analytics What is Azure Synapse Analytics How Azure Synapse Analytics works When to use Azure Synapse Analytics 4 - Use Azure Synapse serverless SQL pool to query files in a data lake Understand Azure Synapse serverless SQL pool capabilities and use cases Query files using a serverless SQL pool Create external database objects 5 - Use Azure Synapse serverless SQL pools to transform data in a data lake Transform data files with the CREATE EXTERNAL TABLE AS SELECT statement Encapsulate data transformations in a stored procedure Include a data transformation stored procedure in a pipeline 6 - Create a lake database in Azure Synapse Analytics Understand lake database concepts Explore database templates Create a lake database Use a lake database 7 - Analyze data with Apache Spark in Azure Synapse Analytics Get to know Apache Spark Use Spark in Azure Synapse Analytics Analyze data with Spark Visualize data with Spark 8 - Transform data with Spark in Azure Synapse Analytics Modify and save dataframes Partition data files Transform data with SQL 9 - Use Delta Lake in Azure Synapse Analytics Understand Delta Lake Create Delta Lake tables Create catalog tables Use Delta Lake with streaming data Use Delta Lake in a SQL pool 10 - Analyze data in a relational data warehouse Design a data warehouse schema Create data warehouse tables Load data warehouse tables Query a data warehouse 11 - Load data into a relational data warehouse Load staging tables Load dimension tables Load time dimension tables Load slowly changing dimensions Load fact tables Perform post load optimization 12 - Build a data pipeline in Azure Synapse Analytics Understand pipelines in Azure Synapse Analytics Create a pipeline in Azure Synapse Studio Define data flows Run a pipeline 13 - Use Spark Notebooks in an Azure Synapse Pipeline Understand Synapse Notebooks and Pipelines Use a Synapse notebook activity in a pipeline Use parameters in a notebook 14 - Plan hybrid transactional and analytical processing using Azure Synapse Analytics Understand hybrid transactional and analytical processing patterns Describe Azure Synapse Link 15 - Implement Azure Synapse Link with Azure Cosmos DB Enable Cosmos DB account to use Azure Synapse Link Create an analytical store enabled container Create a linked service for Cosmos DB Query Cosmos DB data with Spark Query Cosmos DB with Synapse SQL 16 - Implement Azure Synapse Link for SQL What is Azure Synapse Link for SQL? Configure Azure Synapse Link for Azure SQL Database Configure Azure Synapse Link for SQL Server 2022 17 - Get started with Azure Stream Analytics Understand data streams Understand event processing Understand window functions 18 - Ingest streaming data using Azure Stream Analytics and Azure Synapse Analytics Stream ingestion scenarios Configure inputs and outputs Define a query to select, filter, and aggregate data Run a job to ingest data 19 - Visualize real-time data with Azure Stream Analytics and Power BI Use a Power BI output in Azure Stream Analytics Create a query for real-time visualization Create real-time data visualizations in Power BI 20 - Introduction to Microsoft Purview What is Microsoft Purview? How Microsoft Purview works When to use Microsoft Purview 21 - Integrate Microsoft Purview and Azure Synapse Analytics Catalog Azure Synapse Analytics data assets in Microsoft Purview Connect Microsoft Purview to an Azure Synapse Analytics workspace Search a Purview catalog in Synapse Studio Track data lineage in pipelines 22 - Explore Azure Databricks Get started with Azure Databricks Identify Azure Databricks workloads Understand key concepts 23 - Use Apache Spark in Azure Databricks Get to know Spark Create a Spark cluster Use Spark in notebooks Use Spark to work with data files Visualize data 24 - Run Azure Databricks Notebooks with Azure Data Factory Understand Azure Databricks notebooks and pipelines Create a linked service for Azure Databricks Use a Notebook activity in a pipeline Use parameters in a notebook Additional course details: Nexus Humans DP-203T00 Data Engineering on Microsoft Azure training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the DP-203T00 Data Engineering on Microsoft Azure course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Architecting on AWS
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is intended for solutions architects, solution-design engineers, developers seeking an understanding of AWS architecting and individuals seeking the AWS Solutions Architect-Associate certification. Overview Identify AWS architecting basic practices. Explore using the AWS management tools: The AWS Console, Command Line Interface (CLI), and CloudFormation in a lab environment. Examine the enforcement of accounts security using policies. Identify the elements that build an elastic, secure, virtual network that includes private and public subnets. Practice building an AWS core networking infrastructure. Determine strategies for a layered security approach to Virtual Private Cloud (VPC) subnets. Identify strategies to select the appropriate compute resources based on business use-cases. Practice building a VPC and adding an Elastic Cloud Compute (EC2) instance in a lab environment. Practice installing an Amazon Relational Database Service (RDS) instance and an Application Load Balancer (ALB) in the VPC you created. Compare and contrast AWS storage products and services, based on business scenarios. Compare and contrast the different types of AWS database services based on business needs. Practice building a highly available, auto-scaling database layer in a lab. Explore the business value of AWS monitoring solutions. Identify the role of monitoring, event driven load balancing, and auto scaling responses, based on usage and needs. Identify and discuss AWS automation tools that will help you build, maintain and evolve your infrastructure. Discuss network peering, VPC endpoints, gateway and routing solutions based on use-cases. Discuss hybrid networking configurations to extend and secure your infrastructure. Discuss the benefits of microservices as an effective decoupling strategy to power highly available applications at scale. Explore AWS container services for the rapid implementation of an infrastructure-agnostic, portable application environment. Identify the business and security benefits of AWS serverless services based on business examples. Practice building a serverless infrastructure in a lab environment. Discuss the ways in which AWS edge services address latency and security. Practice building a CloudFront deployment with an S3 backend in a lab environment. Explore AWS backup, recovery solutions, and best practices to ensure resiliency and business continuity. Build a highly available and secure cloud architecture based on a business problem, in a project-based facilitator-guided lab. Architecting on AWS is for solutions architects, solution-design engineers, and developers seeking an understanding of AWS architecting. In this course, you will learn to identify services and features to build resilient, secure and highly available IT solutions on the AWS Cloud. Architectural solutions differ depending on industry, types of applications, and business size. AWS Authorized Instructors emphasize best practices using the AWS Well-Architected Framework, and guide you through the process of designing optimal IT solutions, based on real-life scenarios. The modules focus on account security, networking, compute, storage, databases, monitoring, automation, containers, serverless architecture, edge services, and backup and recovery. At the end of the course, you will practice building a solution and apply what you have learned with confidence. Prerequisites AWS Cloud Practitioner Essentials classroom or digital training, or Working knowledge of distributed systems Familiarity with general networking concepts Familiarity with IP addressing Working knowledge of multi-tier architectures Familiarity with cloud computing concepts 0 - Introductions & Course Map review Welcome and course outcomes 1 - Architecting Fundamentals Review AWS Services and Infrastructure Infrastructure Models AWS API Tools Securing your infrastructure The Well-Architected Framework Hands-on lab: Explore Using the AWS API Tools to Deploy an EC2 Instance 2 - Account Security Security Principals Identity and Resource-Based Policies Account Federation Introduction to Managing Multiple Accounts 3 - Networking, Part 1 IP Addressing Amazon Virtual Private Cloud (VPC), Patterns and Quotas Routing Internet Access Network Access Control Lists (NACLs) Security Groups 4 - Compute Amazon Elastic Cloud Compute (EC2) EC2 Instances and Instance Selection High Performance Computing on AWS Lambda and EC2, When to Use Which Hands-On Lab: Build Your Amazon VPC Infrastructure 5 - Storage Amazon S3, Security, Versioning and Storage Classes Shared File Systems Data Migration Tools 6 - Database Services AWS Database Solutions Amazon Relational Database Services (RDS) DynamoDB, Features and Use Cases Redshift, Features, Use Cases and Comparison with RDS Caching and Migrating Data Hands-on Lab: Create a Database Layer in Your Amazon VPC Infrastructure 7 - Monitoring and Scaling Monitoring: CloudWatch, CloudTrail, and VPC Flow Logs Invoking Events 8 - Automation CloudFormation AWS Systems Manager 9 - Containers Microservices Monitoring Microservices with X-Ray Containers 10 - Networking Part 2 VPC Peering & Endpoints Transit Gateway Hybrid Networking Route 53 11 - Serverless Architecture Amazon API Gateway Amazon SQS, Amazon SNS Amazon Kinesis Data Streams & Kinesis Firehose Step Functions Hands-on Lab: Build a Serverless Architecture 12 - Edge Services Edge Fundamentals Amazon CloudFront AWS Global Accelerator AWS Web Application Firewall (WAF), DDoS and Firewall Manager AWS Outposts Hands-On Lab: Configure an Amazon CloudFront Distribution with an Amazon S3 Origin 13 - Backup and Recovery Planning for Disaster Recovery AWS Backup Recovery Strategie Additional course details: Nexus Humans Architecting on AWS training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Architecting on AWS course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

UNDERSTANDING RULES OF ORIGIN
By Export Unlocked Limited
This course will explain all aspects of the rules of origin and trade agreements and how to understand and comply with them to help companies be more competitive in export markets.

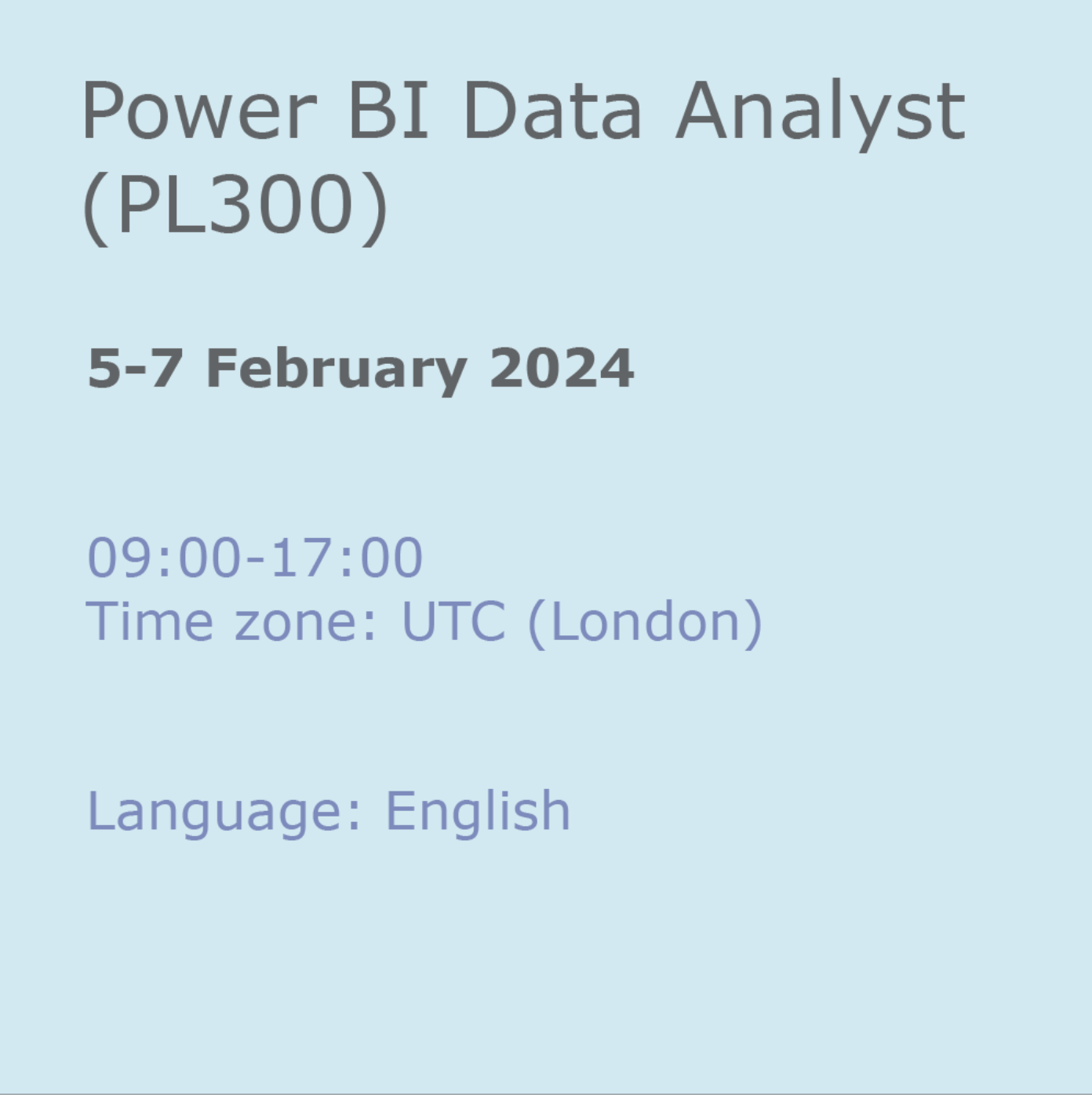
Power BI Data Analyst (PL300)
By Online Productivity Training
OVERVIEW This official Microsoft Power BI training course will teach you how to connect to data from many sources, clean and transform it using Power Query, create a data model consisting of multiple tables connected with relationships and build visualisations and reports to show the patterns in the data. The course will explore formulas created using the DAX language, including the use of advanced date intelligence calculations. Additional visualisation features including interactivity between the elements of a report page are covered as well as parameters and row-level security, which allows a report to be tailored according to who is viewing it. The course will also show how to publish reports and dashboards to a workspace on the Power BI Service. COURSE BENEFITS: Learn how to clean, transform, and load data from many sources Use database queries in Power Query to combine tables using append and merge Create and manage a data model in Power BI consisting of multiple tables connected with relationships Build Measures and other calculations in the DAX language to plot in reports Manage advanced time calculations using date tables Optimise report calculations using the Performance Analyzer Manage and share report assets to the Power BI Service Prepare for the official Microsoft PL-300 exam using Microsoft Official Courseware WHO IS THE COURSE FOR? Data Analysts with little or no experience of Power BI who wish to upgrade their knowledge to include Business Intelligence Management Consultants who need to conduct rapid analysis of their clients’ data to answer specific business questions Analysts who need to upgrade their organisation from a simple Excel or SQL-based management reporting system to a dynamic BI system Data Analysts who wish to develop organisation-wide reporting in the form of web reports or phone apps Marketers in data-intensive organisations who wish to build visually appealing, dynamic charts for their stakeholders to use COURSE OUTLINE Module 1 Getting Started With Microsoft Data Analytics Data analytics and Microsoft Getting Started with Power BI Module 2 Get Data In Power BI Get data from various data sources Optimize performance Resolve data errors Lab: Prepare Data in Power BI Desktop Module 3 Clean, Transform And Load Data In Power BI Data shaping Data profiling Enhance the data structure Lab: Load Data in Power BI Desktop Module 4 Design A Data Model In Power BI Introduction to data modelling Working with Tables Dimensions and Hierarchies Lab: Model Data in Power BI Desktop Module 5 Create Model Calculations Using DAX In Power BI Introduction to DAX Real-time Dashboards Advanced DAX Lab 1: Create DAX Calculations in Power BI Desktop, Part 1 Lab 2: Create DAX Calculations in Power BI Desktop, Part 2 Module 6 Optimize Model Performance Optimize the data model for performance Optimize DirectQuery models Module 7 Create Reports Design a Report Enhance the Report Lab 1: Design a Report in Power BI Desktop, Part 1 Lab 2: Design a Report in Power BI Desktop, Part 2 Module 8 Create Dashboards Create a Dashboard Real-time Dashboards Enhance a Dashboard Lab: Create a Power BI Dashboard Module 9 Perform Advanced Analytics Advanced analytics Data Insights through AI Visuals Lab: Perform Data Analysis in Power BI Desktop Module 10 Create And Manage Workspaces Creating Workspaces Sharing and managing assets Module 11 Manage Datasets In Power BI Parameters Datasets Module 12 Row-Level Security Security in Power BI Lab: Enforce Row-Level Security
SC-100T00 Microsoft Cybersecurity Architect
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for experienced cloud security engineers who have taken a previous certification in the security, compliance and identity portfolio. Specifically, students should have advanced experience and knowledge in a wide range of security engineering areas, including identity and access, platform protection, security operations, securing data, and securing applications. They should also have experience with hybrid and cloud implementations. Beginning students should instead take the course SC-900: Microsoft Security, Compliance, and Identity Fundamentals. This is an advanced, expert-level course. Although not required to attend, students are strongly encouraged to have taken and passed another associate level certification in the security, compliance and identity portfolio (such as AZ-500, SC-200 or SC-300) before attending this class. This course prepares students with the expertise to design and evaluate cybersecurity strategies in the following areas: Zero Trust, Governance Risk Compliance (GRC), security operations (SecOps), and data and applications. Students will also learn how to design and architect solutions using zero trust principles and specify security requirements for cloud infrastructure in different service models (SaaS, PaaS, IaaS). Prerequisites Highly recommended to have attended and passed one of the associate level certifications in the security, compliance and identity portfolio (such as AZ-500T00 Microsoft Azure Security Technologies, SC-200T00: Microsoft Security Operations Analyst, or SC-300T00: Microsoft Identity and Access Administrator.) Advanced experience and knowledge in identity and access, platform protection, security operations, securing data and securing applications. Experience with hybrid and cloud implementations. 1 - Introduction to Zero Trust and best practice frameworks Zero Trust initiatives Zero Trust technology pillars part 1 Zero Trust technology pillars part 2 2 - Design solutions that align with the Cloud Adoption Framework (CAF) and Well-Architected Framework (WAF) Define a security strategy Cloud Adoption Framework secure methodology Design security with Azure Landing Zones The Well-Architected Framework security pillar 3 - Design solutions that align with the Microsoft Cybersecurity Reference Architecture (MCRA) and Microsoft cloud security benchmark (MCSB) Design solutions with best practices for capabilities and controls Design solutions with best practices for attack protection 4 - Design a resiliency strategy for common cyberthreats like ransomware Common cyberthreats and attack patterns Support business resiliency Ransomware protection Configurations for secure backup and restore Security updates 5 - Case study: Design solutions that align with security best practices and priorities Case study description Case study answers Conceptual walkthrough Technical walkthrough 6 - Design solutions for regulatory compliance Translate compliance requirements into a security solution Address compliance requirements with Microsoft Purview Address privacy requirements with Microsoft Priva Address security and compliance requirements with Azure policy Evaluate infrastructure compliance with Defender for Cloud 7 - Design solutions for identity and access management Design cloud, hybrid and multicloud access strategies (including Azure AD) Design a solution for external identities Design modern authentication and authorization strategies Align conditional access and Zero Trust Specify requirements to secure Active Directory Domain Services (AD DS) Design a solution to manage secrets, keys, and certificates 8 - Design solutions for securing privileged access The enterprise access model Design identity governance solutions Design a solution to secure tenant administration Design a solution for cloud infrastructure entitlement management (CIEM) Design a solution for privileged access workstations and bastion services 9 - Design solutions for security operations Design security operations capabilities in hybrid and multicloud environments Design centralized logging and auditing Design security information and event management (SIEM) solutions Design solutions for detection and response Design a solution for security orchestration, automation, and response (SOAR) Design security workflows Design threat detection coverage 10 - Case study: Design security operations, identity and compliance capabilities Case study description Case study answers Conceptual walkthrough Technical walkthrough 11 - Design solutions for securing Microsoft 365 Evaluate security posture for collaboration and productivity workloads Design a Microsoft 365 Defender solution Design configurations and operational practices for Microsoft 365 12 - Design solutions for securing applications Design and implement standards to secure application development Evaluate security posture of existing application portfolios Evaluate application threats with threat modeling Design security lifecycle strategy for applications Secure access for workload identities Design a solution for API management and security Design a solution for secure access to applications 13 - Design solutions for securing an organization's data Design a solution for data discovery and classification using Microsoft Purview Design a solution for data protection Design data security for Azure workloads Design security for Azure Storage Design a security solution with Microsoft Defender for SQL and Microsoft Defender for Storage 14 - Case study: Design security solutions for applications and data Case study description Case study answers Conceptual walkthrough Technical walkthrough 15 - Specify requirements for securing SaaS, PaaS, and IaaS services Specify security baselines for SaaS, PaaS, and IaaS services Specify security requirements for web workloads Specify security requirements for containers and container orchestration 16 - Design solutions for security posture management in hybrid and multicloud environments Evaluate security posture by using Microsoft Cloud Security Benchmark Design integrated posture management and workload protection Evaluate security posture by using Microsoft Defender for Cloud Posture evaluation with Microsoft Defender for Cloud secure score Design cloud workload protection with Microsoft Defender for Cloud Integrate hybrid and multicloud environments with Azure Arc Design a solution for external attack surface management 17 - Design solutions for securing server and client endpoints Specify server security requirements Specify requirements for mobile devices and clients Specify internet of things (IoT) and embedded device security requirements Secure operational technology (OT) and industrial control systems (ICS) with Microsoft Defender for IoT Specify security baselines for server and client endpoints Design a solution for secure remote access 18 - Design solutions for network security Design solutions for network segmentation Design solutions for traffic filtering with network security groups Design solutions for network posture management Design solutions for network monitoring 19 - Case study: Design security solutions for infrastructure Case study description Case study answers Conceptual walkthrough Technical walkthrough Additional course details: Nexus Humans SC-100T00 Microsoft Cybersecurity Architect training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the SC-100T00 Microsoft Cybersecurity Architect course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
