- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1353 Courses delivered Live Online
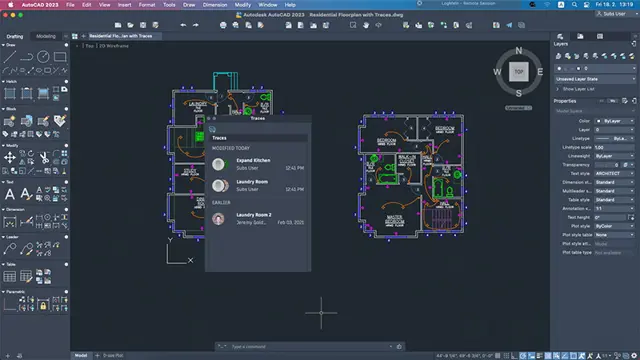
CAD Courses | Bespoke 1-2-1 in London
By Real Animation Works
Learn CAD in 10 hrs
Unity 3D One-Day Course (One-to-One)
By Real Animation Works
Photoshop basic to fundamentals Training Course bespoke and customized

Mental Health First Aid Course
By Cavity Dental Training
Train as a Mental Health First Aider (MHFAider®) and receive three years of certification, plus access to ongoing benefits. This course is ideal for individuals who would like to become an MHFAider® to gain the knowledge and skills to spot signs of people experiencing poor mental health, be confident to start a conversation and signpost a person to appropriate support. In addition to the course, you will become part of the largest MHFAider® community in England, gaining access to resources, ongoing learning and 24/7 digital support through our MHFAider Support App®, to give you the tools and knowledge you need to carry out the role effectively and confidently, whether that be in your workplace, a volunteer role, or in the community. Choose between our upcoming courses dates, which include 4 half day morning sessions: March 4th including 5th 6th 7th April 15th including 16th 17th 18th Course Outcomes As an MHFAider® you will be able to: Recognise those that may be experiencing poor mental health and provide them with first-level support and early intervention Encourage a person to identify and access sources of professional help and other supports Practise active listening and empathy Have a conversation with improved mental health literacy around language and stigma Discuss the MHFAider® role in depth, including boundaries and confidentiality Practise self-care Know how to use the MHFAider Support App® Know how to access a dedicated text service provided by Shout and ongoing learning opportunities with MHFA England Course Format Online course structured across four flexible sessions. Each session is a maximum of 3hrs 45mins Learners will be trained over four live sessions with an MHFA England Instructor Member, covering 14 hours of content in total. Learning takes place through a mix of instructor led training, group discussions, individual and group activities. Each session builds on the previous, enabling the learner to gain confidence in supporting others with a Mental Health First Aid action plan. We limit numbers to 16 people per course so that instructors can keep people safe and supported while they learn. We strive for all of our learning content to be as accessible and inclusive as possible. Course Takeaways Everyone who completes this course gets: A hard copy workbook to support their learning throughout the course A digital manual to refer to whenever they need it after completing the course A wallet-sized reference card with the Mental Health First Aid action plan A digital MHFAider® certificate Access to the MHFAider Support App® for three years Access to ongoing learning opportunities, resources and exclusive events The opportunity to be part of the largest MHFAider® community in England

Oracle Database 12c R2 - Backup and Recovery Workshop Ed 3
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Data Warehouse Administrator Database Administrators Support Engineer Technical Administrator Technical Consultant Overview Use Oracle Flashback Technologies to recover from human error Use Recovery Manager (RMAN) to create backups and perform recovery operations Use the Data Recovery Advisor to diagnose and repair failures Plan effective backup and recovery procedures Describe the Oracle Database architecture components related to backup and recovery operations Perform an encrypted database backup and restore Perform tablespace point-in-time recovery Configure the database for recoverability Describe Cloud Tooling for Backup and Recovery Describe Oracle Database backup methods and recovery operations that can be used to resolve database failure In this Oracle Database 12c R2: Backup and Recovery Workshop, students learn how to perform backup and recovery based on the related Oracle Database architecture components. Various backup, failure, restore, and recovery scenarios are provided so that students learn to evaluate their own recovery requirements and develop an appropriate strategy for backup and recovery procedures. This course includes an interactive workshop, with scenarios that provide participants with opportunities to diagnose and recover from several failure situations. Introduction Curriculum Context Assess your recovery requirements Categories of failures Oracle backup and recovery solutions Oracle Maximum Availability Architecture Oracle Secure Backup Benefits of using Oracle Data Guard Basic Workshop Architecture Getting Started Core Concepts of the Oracle Database, critical for Backup and Recovery Oracle DBA Tools for Backup and Recovery Connecting to Oracle Recovery Manager (RMAN) Configuring for Recoverablility RMAN commands Configuring and managing persistent settings Using the Fast Recovery Area (FRA) Control File Redo Log File Archiving Logs Using the RMAN Recovery Catalog Creating and Configuring the Recovery Catalog Managing Target Database Records in the Recovery Catalog Using RMAN Stored Scripts Maintaining and Protecting the Recovery Catalog Virtual Private Catalogs Backup Strategies and Terminology Backup Solutions Overview and Terminology Balancing Backup and Restore Requirements Backing Up Read-Only Tablespaces Data Warehouse Backup and Recovery: Best Practices Additional Backup Terminology Performing Backups RMAN Backup Types Incrementally Updated Backups Fast Incremental Backup Block Change Tracking Oracle-Suggested Backup Reporting on Backups Managing Backups Improving Your Backups Compressing Backups Using a Media Manager Backup and Restore for Very Large Files Creating RMAN Multi-section Backups, Proxy Copies, Duplexed Backup Sets and Backups of Backup Sets Creating and Managing Archival Backups Backing Up Recovery Files Backing Up the Control File to a Trace File Cataloging Additional Backup Files Using RMAN-Encrypted Backups Creating RMAN-Encrypted Backups Using Transparent-Mode Encryption Using Password-Mode Encryption Using Dual-Mode Encryption Diagnosing Failures Reducing Problem Diagnosis Time Automatic Diagnostic Repository Data Recovery Advisor Handling Block Corruption Restore and Recovery Concepts Restoring and Recovering Instance Failure and Instance/Crash Recovery Media Failure Complete Recovery (Overview) Point-in-Time Recovery (Overview) Recovery with the RESETLOGS Option Performing Recovery, Part I RMAN Recovery in NOARCHIVELOG Mode Performing Complete Recovery (of critical and noncritical data files) Restoring ASM Disk Groups Recovery with Image Files Performing Point-in-Time (PITR) or Incomplete Recovery Performing Recovery, Part II Recovery of Server Parameter File, Control File (One and All) Redo Log File Loss and Recovery Password Authentication File Re-creation Index, Read-Only Tablespace, and Temp file Recovery Restoring the Database to a New Host Disaster Recovery Restoring RMAN Encrypted Backups RMAN and Oracle Secure Backup Oracle Secure Backup Overview and Interface Options RMAN and OSB: Overview and Basic Process Flow Starting with Oracle Secure Backup Configuring Oracle Secure Backup for RMAN RMAN Backup and Restore Operations Oracle Secure Backup Jobs Displaying OSB log files and transcripts for RMAN activities Using Flashback Technologies Flashback Technology: Overview and Setup Using Flashback Technology to Query Data Flashback Table Flashback Transaction (Query and Back out) Flashback Drop and the Recycle Bin Flashback Data Archive Using Flashback Database Flashback Database Architecture Configuring Flashback Database Performing Flashback Database Best Practices for Flashback Database Transporting Data Transporting Data Across Platforms Transporting Data with Backup Sets Database Transport: Using Data Files Performing Point-in-Time Recovery When to use TSPITR TSPITR Architecture Performing RMAN TS Point-in-time Recovery Recovering Tables from Backups Duplicating a Database Using a Duplicate Database Duplicating Database with 'push' and 'pull' techniques Choosing Database Duplication Techniques Creating a Backup-up Based Duplicate Database Understanding the RMAN Duplication Operation RMAN Troubleshooting and Tuning Interpreting RMAN Message Output Tuning Principles Diagnosing Performance Bottlenecks RMAN Multiplexing Restore and Recovery Performance Best Practices Cloud Tooling for Backup and Recovery Backup Destinations Customize Backup Configuration On-Demand Backup and Recovery Oracle Backup Cloud Service Installing the Backup Module Backup and Recovery Workshop Workshop Structure and Approach Business Requirements for Database Availability and Procedures Diagnosing the Failures

Spring Boot Quick Start | Core Spring, Spring AOP, Spring Boot 2.0 and More (TT3322)
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for This introduction to Spring development course requires that incoming students possess solid Java programming skills and practical hands-on Java experience. This class is geared for experienced Java developers who are new to Spring, who wish to understand how and when to use Spring in Java and JEE applications. Overview Working in a hands-on learning environment, led by our expert practitioner, students will: Explain the issues associated with complex frameworks such as JEE and how Spring addresses those issues Understand the relationships between Spring and JEE, AOP, IOC and JDBC. Write applications that take advantage of the Spring container and the declarative nature of assembling simple components into applications. Understand how to configure the Spring Boot framework Understand and work on integrating persistence into a Spring application Explain Spring's support for transactions and caching Work with Spring Boot to facilitate Spring setup and configuration Apply Aspect Oriented Programming (AOP) to Spring applications Become familiar with the conditionally loading of bean definitions and Application Contexts Understand how to leverage the power of Spring Boot Use Spring Boot to create and work with JPA repositories Introduction to Spring Boot | Spring Boot Quick Start is a hands-on Spring training course geared for experienced Java developers who need to understand what the Spring Boot is in terms of today's systems and architectures, and how to use Spring in conjunction with other technologies and frameworks. This leading-edge course provides added coverage of Spring's Aspect-Oriented Programming and the use of Spring Boot. Students will gain hands-on experience working with Spring, using Maven for project and dependancy management, and, optionally, a test-driven approach (using JUnit) to the labs in the course. The Spring framework is an application framework that provides a lightweight container that supports the creation of simple-to-complex components in a non-invasive fashion. Spring's flexibility and transparency is congruent and supportive of incremental development and testing. The framework's structure supports the layering of functionality such as persistence, transactions, view-oriented frameworks, and enterprise systems and capabilities. This course targets Spring Boot 2 , which includes full support for Java SE 11 and Java EE 8. Spring supports the use of lambda expressions and method references in many of its APIs. The Spring Framework Understand the value of Spring Explore Dependency Injection (DI) and Inversion of Control (IoC) Introduce different ways of configuring collaborators Spring as an Object Factory Initializing the Spring IoC Container Configuring Spring Managed Beans Introduce Java-based configuration The @Configuration and @Bean annotations Define bean dependencies Bootstrapping Java Config Context Injection in Configuration classes Using context Profiles Conditionally loading beans and configurations Bean Life-Cycle Methods Defining Bean dependencies Introduce Spring annotations for defining dependencies Explore the @Autowired annotation Stereotype Annotations Qualifying injection points Lifecycle annotations Using properties in Java based configuration The @Value annotation Using the Candidate Components Index Introduction to Spring Boot Introduce the basics of Spring Boot Explain auto-configuration Introduce the Spring Initializr application Bootstrapping a Spring Boot application Working with Spring Boot Provide an overview of Spring Boot Introduce starter dependencies Introduce auto-configuration @Enable... annotations Conditional configuration Spring Boot Externalized Configuration Bootstrapping Spring Boot Introduction to Aspect Oriented Programming Aspect Oriented Programming Cross Cutting Concerns Spring AOP Spring AOP in a Nutshell @AspectJ support Spring AOP advice types AspectJ pointcut designators Spring Boot Actuator Understand Spring Boot Actuators Work with predefined Actuator endpoints Enabling Actuator endpoints Securing the Actuator Developing in Spring Boot Introduce Spring Boot Devtools Enable the ConditionEvaluationReport Debugging Spring Boot applications Thymeleaf Provide a quick overview of Thymeleaf Introduce Thymeleaf templates Create and run a Spring Thymeleaf MVC application Additional course details: Nexus Humans Spring Boot Quick Start | Core Spring, Spring AOP, Spring Boot 2.0 and More (TT3322) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Spring Boot Quick Start | Core Spring, Spring AOP, Spring Boot 2.0 and More (TT3322) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Cisco Meeting Server Advanced (COLLAB350)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for The primary audience for this course is as follows: Channel partners and reseller engineers installing, configuring, and maintaining scalable and resilient deployments of Cisco Meeting Server Channel partners and reseller engineers providing presales support for scalable and resilient Cisco Meeting Server deployments Customer engineers supporting scalable and resilient Cisco Meeting Server deployments Overview Upon completion of this course, the learner should be able to meet the following objectives: Cisco Meeting Server API commands Scalable and resilient deployments Customization Recording In this 3-day course Cisco Meeting Server Advanced (COLLAB350), you will learn advanced techniques in installing, troubleshooting, and maintaining a single server and single server split deployment of Cisco Meeting Servers. The recently purchased Acano collaboration hardware and software includes video and audio-bridging technology that allows customers to connect video systems from multiple vendors across both cloud and hybrid environments. Cisco has incorporated Acano collaboration technologies into the new Meeting Server tool. Module 1: Reviewing Cisco Meeting Server Intermediate Component parts of a Cisco Meeting Solution Configuration steps for a Cisco Meeting Solution Module 2: APIs Purpose of APIs Benefits of APIs Types of APIs Function of the GET, POST, PUT, and DELETE commands Module 3: Configuring Software with an API How a user can interact with software using an API Download and install Chrome Postman Other API software Download the Cisco Meeting Server API guide Module 4: Configuring Spaces with the Cisco Meeting Server API Cisco Meeting Server API structure Use Chrome Postman for information on calls and spaces with the GET command Use Chrome Postman to post a new call space with the POST command Use Chrome Postman to place changes in a space, including adding a member, with the PUT command Use Chrome Postman to delete a space with the DELETE command Module 5: Customization Configuration Create and modify a user profile and assign users Create and modify a dual-tone multifrequency (DTMF) profile and apply to a user profile Modify the interactive voice response (IVR), color scheme, and background Module 6: Planning a Resilient and Scalable Cisco Meeting Server Deployment Resilient server solutions Scalable server solutions Geographically dispersed configurations and GeoDNS Domain Name System (DNS) records required for a resilient and scalable solution Certificate requirements for a resilient and scalable solution Module 7: Configuring a Database Cluster Relationship between cluster master and cluster slaves in a database cluster Certificate requirements for a secure database cluster Configure the certificates for a database cluster Configure a database cluster Module 8: Configuring a Call Bridge Cluster Relationship between the Call Bridge and the Database How cross-cluster spaces behave Configure certificates for Call Bridge clustering Storage of configuration when entering with the API and the individual web interfaces for Lightweight Directory Access Protocol (LDAP) and Call Bridge clustering Configure a Call Bridge Cluster Connect XMPP server to multiple Call Bridges Module 9: Configuring Load Balancers and Trunks Relationship between the XMPP server, Trunk and Load Balancer Configure certificates for multiple trunks and load balancers Configure multiple Trunks to multiple Load Balancers Module 10: Configuring Multiple Web Bridges Relationship between multiple Web Bridges and Call Bridges Internal and external DNS records support for both internal and external Web Bridges Configure certificates for multiple Web Bridges Configure multiple Web bridges Connect multiple Call Bridges to multiple Web Bridges Module 11: Configuring Multiple TURN Servers Relationship between multiple TURN servers and multiple Call Bridges Configure certificates for multiple TURN servers Configure multiple TURN servers Connect multiple Call Bridges to multiple TURN servers Module 12: Configuring Multiple Recorders Features of the recording capability Software, hardware, and licensing requirements for recording DNS records Configure the Recorder Relationship between multiple Recorders and multiple Call Bridges Configure a Call Bridge to use a Recorder Configure certificates for multiple Recorders servers Configure multiple Recorder servers Connect multiple Call Bridges to multiple Recorder servers Module 13: Integrating with a Resilient and Scalable Cisco Meeting Server Deployment Integration with Cisco TelePresence Video Communication Server (VCS) or Cisco Unified Communications Manager and multiple Call Bridges Integration with Cisco Expressway technology and multiple Call Bridges Integration with Microsoft Skype for Business and multiple Call Bridges Integration with Cisco TelePresence Management Suite and multiple Call Bridges Module 14: Deploying an H.323 Gateway Cisco preferred architecture for H.323 and Session Initiation Protocol (SIP) interoperability Functionality of the Cisco Meeting Server H.323 gateway Configuration the Cisco Meeting Server H.323 gateway Module 15: Multitenancy Options Purpose of the multitenancy capabilities Options for multitenancy capabilities on the Cisco Meeting Server Module 16: Customization Options Options available to customize Cisco Meeting Apps License keys required for customization Web Server requirements for customization Options available to customize recorded messaging Customization options available for invitation text

Symantec Data Loss Prevention 14.0 - Administration
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for anyone responsible for conf iguring, maintaining, and troubleshooting Symantec Data Loss Prevention. Additionally, this course is intended for technical users responsible for creating and maintaining Symantec Data Loss Prevention policies and the incident response structure. Overview At the completion of the course, you will be able to: Enforce server, detection servers, and DLP Agents as well as reporting, workflow, incident response management, policy management and detection, response management, user and role administration, directory integration, and filtering. This course is designed to provide you with the fundamental know ledge to configure and administer the Symantec Data Loss Prevention Enforce platform. Introduction to Symantec Data Loss Prevention Symantec Data Loss Prevention overview Symantec Data Loss Prevention architecture Navigation and Reporting Navigating the user interface Reporting and analysis Report navigation, preferences, and features Report filters Report commands Incident snapshot Incident Data Access Hands-on labs: Become familiar with navigation and tools in the user interface. Create, filter, summarize, customize, and distribute reports. Create users, roles, and attributes. Incident Remediation and Workflow Incident remediation and w orkf low Managing users and attributes Custom attribute lookup User Risk Summary Hands-on labs: Remediate incidents and configure a user?s reporting preferences Policy Management Policy overview Creating policy groups Using policy templates Building policies Policy development best practices Hands-on labs: Use policy templates and policy builder to configure and apply new policies Response Rule Management Response rule overview Configuring Automated Response rules Configuring Smart Response rules Response rule best practices Hands-On Labs: Create and use Automated and Smart Response rules Described Content Matching DCM detection methods Hands-on labs: Create policies that include DCM and then use those policies to capture incidents Exact Data Matching and Directory Group Matching Exact data matching (EDM) Advanced EDM Directory group matching (DGM) Hands-on labs: Create policies that include EDM and DGM, and then use those policies to capture incident Indexed Document Matching Indexed document matching (IDM) Hands-on labs: Create policies that include IDM rules and then use those policies to capture incidents Vector Machine Learning Vector Machine Learning (VML) Hands-on labs: Create a VML profile, import document sets, and create a VML policy Network Monitor Review of Network Monitor Protocols Traffic filtering Network Monitor best practices Hands-On Labs: Apply IP and L7 filters Network Prevent Network Prevent overview Introduction to Network Prevent (Email) Introduction to Network Prevent (Web) Hands-On Labs: Configure Network Prevent (E-mail) response rules, incorporate them into policies, and use the policies to capture incidents Mobile Email Monitor and Mobile Prevent Introduction to Mobile Email Monitor Mobile Prevent overview Configuration VPN configuration Policy and Response Rule Creation Reporting and Remediation Troubleshooting Network Discover and Network Protect Network Discover and Network Protect overview Configuring Discover targets Configuring Box cloud targets Protecting data Auto-discovery of servers and shares Running and managing scans Reports and remediation Network Discover and Network Protect best practices Hands-on labs: Create and run a filesystem target using various response rules, including quarantining Endpoint Prevent Endpoint Prevent overview Detection capabilities at the Endpoint Configuring Endpoint Prevent Creating Endpoint response rules Viewing Endpoint Prevent incidents Endpoint Prevent best practices Managing DLP Agents Hands-on labs: Create Agent Groups and Endpoint response rules, monitor and block Endpoint actions, view Endpoint incidents, and use the Enforce console to manage DLP Agents Endpoint Discover Endpoint Discover overview Creating and running Endpoint Discover targets Using Endpoint Discover reports and reporting features Hands-on labs: Create Endpoint Discover targets, run Endpoint Discover targets, and view Endpoint Discover incidents Enterprise Enablement Preparing for risk reduction Risk reduction DLP Maturity model System Administration Server administration Language support Incident Delete Credential management Troubleshooting Diagnostic tools Troubleshooting scenario Getting support Hands-on labs: Interpret event reports and traffic reports, configure alerts, and use the Log Collection and Configuration tool Additional course details: Nexus Humans Symantec Data Loss Prevention 14.0 - Administration training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Symantec Data Loss Prevention 14.0 - Administration course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Performance: Planning the Way Out of Life Changes.
By believe-IN. Make It Happen!®
believe-IN Webinar Series: Plan the Way Out Life Changes. Webinar 3 – Performance: Planning the Way Out of Life Changes.

C Plus Plus and Programming Basics for Non-Programmers (TTCP2000)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for anyone who is new to software development and wants, or needs, to gain an understanding of the fundamentals of coding and basics of C++ and object-oriented programming concepts. This course is for Non-Developers, or anyone who wants to have a basic understanding of and learn how to code C++ applications and syntax Overview Companies are constantly challenged to keep their applications, development projects, products, services (and programmers!) up to speed with the latest industry tools, skills, technologies and practices to stay ahead in the ever-shifting markets that make up today's fiercely competitive business landscape. The need for application, web and mobile developers and coders is seemingly endless as technologies regularly change and grow to meet the modern needs of demanding industries and clients. C++ and Programming Basics for Non-Programmers is a five-day, basic-level training course geared for IT candidates who have little or no prior experience in computer programming. Throughout this gentle introduction to programming and C++, students will learn to create applications and libraries using C++ using best practices and sound OO development techniques for writing object-oriented programs in C++. Special emphasis is placed on object-oriented concepts and best practices throughout the training. Fundamentals of the Program Development Cycle Computer Architecture The Notion of Algorithms Source Code vs. Machine Code Compile-Time vs. Run-Time Software Program Architecture Standalone Client/Server Distributed Web-Enabled IDE (Interactive Development Environment) Concepts Looping Constructs Counter-Controlled Repetition Sentinel-Controlled Repetition Nested Control Constructs break and continue Statements Structured Programming Best Practices Writing Methods (Functions) Static vs. Dynamic Allocation Declaring Methods Declaring Methods with Multiple Parameters Method-Call Stack Scope of Declarations Argument Promotion and Casting Designing Methods for Reusability Method Overloading Arrays Purpose of Arrays Declaring and Instantiating Arrays Passing Arrays to Methods Multidimensional Arrays Variable-Length Argument Lists Using Command-Line Arguments Using Environment Variables Deeper Into Classes and Objects Controlling Access to Class Members Referencing the Current Object Using this Overloading Constructors Default and No-Argument Constructors Composition of Classes Garbage Collection and Destructors The finalize Method Static Class Members Defining Classes Using Inheritance Application Development Fundamentals Structure of a C++ Program Memory Concepts Fundamental Data Type Declarations Fundamental I/O Concepts Fundamental Operators Arithmetic Operators Logical Operators Precedence and Associativity Building and Deploying a C++ Program Superclasses and Subclasses Advantages of Using Inheritance protected Class Members Constructors in Subclasses Increasing Convenience by Using Polymorphism Purpose of Polymorphic Behavior The Concept of a Signature Abstract Classes and Methods final Methods and Classes Purpose of Interfaces Using and Creating Interfaces Common Interfaces of the C++ API Files and Streams Concept of a Stream Class File Sequential Access Object Serialization to/from Sequential Access Files Fundamental Searching and Sorting Introduction to Searching Algorithms Linear Search Binary Search Introduction to Sorting Algorithms Selection Sort Insertion Sort Merge Sort Fundamental Data Structures Dynamic Memory Allocation Linked Lists Stacks Queues Trees Exception Handling Types of Exceptions Exception Handling Overview Introduction to Classes and Objects Classes, Objects and Methods Object Instances Declaring and Instantiating a C++ Object Declaring Methods set and get Methods Initiating Objects with Constructors Primitive Types vs. Reference Types Flow Control Conditional Constructs Exception Class Hierarchy Extending Exception Classes When to Throw or Assert Exceptions Formatted Output printf Syntax Conversion Characters Specifying Field Width and Precision Using Flags to Alter Appearance Printing Literals and Escape Sequences Formatting Output with Class Formatter Strings, Characters and Regular Expressions Fundamentals of Characters and Strings String Class String Operations StringBuilder Class Character Class StringTokenizer Class Regular Expressions Regular Expression Syntax Pattern Class Matcher Class Fundamental GUI Programming Concepts Overview of Swing Components Displaying Text and Graphics in a Window Event Handling with Nested Classes GUI Event Types and Listener Interfaces Mouse Event Handling Layout Managers Additional course details: Nexus Humans C Plus Plus and Programming Basics for Non-Programmers (TTCP2000) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the C Plus Plus and Programming Basics for Non-Programmers (TTCP2000) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Confident Career Conversations - CV Writing & Interview Skills
By Mpi Learning - Professional Learning And Development Provider
This course is for anyone wishing to understand their strengths and development areas and those who are seeking assistance to progress their careers and convey their abilities confidently.
