- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
2179 Courses delivered Live Online
SC-100T00 Microsoft Cybersecurity Architect
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for experienced cloud security engineers who have taken a previous certification in the security, compliance and identity portfolio. Specifically, students should have advanced experience and knowledge in a wide range of security engineering areas, including identity and access, platform protection, security operations, securing data, and securing applications. They should also have experience with hybrid and cloud implementations. Beginning students should instead take the course SC-900: Microsoft Security, Compliance, and Identity Fundamentals. This is an advanced, expert-level course. Although not required to attend, students are strongly encouraged to have taken and passed another associate level certification in the security, compliance and identity portfolio (such as AZ-500, SC-200 or SC-300) before attending this class. This course prepares students with the expertise to design and evaluate cybersecurity strategies in the following areas: Zero Trust, Governance Risk Compliance (GRC), security operations (SecOps), and data and applications. Students will also learn how to design and architect solutions using zero trust principles and specify security requirements for cloud infrastructure in different service models (SaaS, PaaS, IaaS). Prerequisites Highly recommended to have attended and passed one of the associate level certifications in the security, compliance and identity portfolio (such as AZ-500T00 Microsoft Azure Security Technologies, SC-200T00: Microsoft Security Operations Analyst, or SC-300T00: Microsoft Identity and Access Administrator.) Advanced experience and knowledge in identity and access, platform protection, security operations, securing data and securing applications. Experience with hybrid and cloud implementations. 1 - Introduction to Zero Trust and best practice frameworks Zero Trust initiatives Zero Trust technology pillars part 1 Zero Trust technology pillars part 2 2 - Design solutions that align with the Cloud Adoption Framework (CAF) and Well-Architected Framework (WAF) Define a security strategy Cloud Adoption Framework secure methodology Design security with Azure Landing Zones The Well-Architected Framework security pillar 3 - Design solutions that align with the Microsoft Cybersecurity Reference Architecture (MCRA) and Microsoft cloud security benchmark (MCSB) Design solutions with best practices for capabilities and controls Design solutions with best practices for attack protection 4 - Design a resiliency strategy for common cyberthreats like ransomware Common cyberthreats and attack patterns Support business resiliency Ransomware protection Configurations for secure backup and restore Security updates 5 - Case study: Design solutions that align with security best practices and priorities Case study description Case study answers Conceptual walkthrough Technical walkthrough 6 - Design solutions for regulatory compliance Translate compliance requirements into a security solution Address compliance requirements with Microsoft Purview Address privacy requirements with Microsoft Priva Address security and compliance requirements with Azure policy Evaluate infrastructure compliance with Defender for Cloud 7 - Design solutions for identity and access management Design cloud, hybrid and multicloud access strategies (including Azure AD) Design a solution for external identities Design modern authentication and authorization strategies Align conditional access and Zero Trust Specify requirements to secure Active Directory Domain Services (AD DS) Design a solution to manage secrets, keys, and certificates 8 - Design solutions for securing privileged access The enterprise access model Design identity governance solutions Design a solution to secure tenant administration Design a solution for cloud infrastructure entitlement management (CIEM) Design a solution for privileged access workstations and bastion services 9 - Design solutions for security operations Design security operations capabilities in hybrid and multicloud environments Design centralized logging and auditing Design security information and event management (SIEM) solutions Design solutions for detection and response Design a solution for security orchestration, automation, and response (SOAR) Design security workflows Design threat detection coverage 10 - Case study: Design security operations, identity and compliance capabilities Case study description Case study answers Conceptual walkthrough Technical walkthrough 11 - Design solutions for securing Microsoft 365 Evaluate security posture for collaboration and productivity workloads Design a Microsoft 365 Defender solution Design configurations and operational practices for Microsoft 365 12 - Design solutions for securing applications Design and implement standards to secure application development Evaluate security posture of existing application portfolios Evaluate application threats with threat modeling Design security lifecycle strategy for applications Secure access for workload identities Design a solution for API management and security Design a solution for secure access to applications 13 - Design solutions for securing an organization's data Design a solution for data discovery and classification using Microsoft Purview Design a solution for data protection Design data security for Azure workloads Design security for Azure Storage Design a security solution with Microsoft Defender for SQL and Microsoft Defender for Storage 14 - Case study: Design security solutions for applications and data Case study description Case study answers Conceptual walkthrough Technical walkthrough 15 - Specify requirements for securing SaaS, PaaS, and IaaS services Specify security baselines for SaaS, PaaS, and IaaS services Specify security requirements for web workloads Specify security requirements for containers and container orchestration 16 - Design solutions for security posture management in hybrid and multicloud environments Evaluate security posture by using Microsoft Cloud Security Benchmark Design integrated posture management and workload protection Evaluate security posture by using Microsoft Defender for Cloud Posture evaluation with Microsoft Defender for Cloud secure score Design cloud workload protection with Microsoft Defender for Cloud Integrate hybrid and multicloud environments with Azure Arc Design a solution for external attack surface management 17 - Design solutions for securing server and client endpoints Specify server security requirements Specify requirements for mobile devices and clients Specify internet of things (IoT) and embedded device security requirements Secure operational technology (OT) and industrial control systems (ICS) with Microsoft Defender for IoT Specify security baselines for server and client endpoints Design a solution for secure remote access 18 - Design solutions for network security Design solutions for network segmentation Design solutions for traffic filtering with network security groups Design solutions for network posture management Design solutions for network monitoring 19 - Case study: Design security solutions for infrastructure Case study description Case study answers Conceptual walkthrough Technical walkthrough Additional course details: Nexus Humans SC-100T00 Microsoft Cybersecurity Architect training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the SC-100T00 Microsoft Cybersecurity Architect course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

TETRA training course description This 2 day training course covers the network architecture required for TETRA. It also looks at the Air Interface, TETRA Functions and Procedures. What will you learn Describe the TETRA Architecture Describe the Air Interface Explain the TETRA Functions Explain the TETRA Procedures TETRA training course details Who will benefit: Anyone working with TETRA. Prerequisites: None. Duration 2 days TETRA training course contents Introduction History of PMR, ETSI development, Tetra function, Tetra markets, Tetra standards, Tetra supplier base, Tetra Release 1, Tetra Release 2. Network Architecture Mobile network Identity, Mobile stations, Base station, Switching & Management, Addresses & Identitie. Air Interface Modulation, TDMA Format, FD, Framin, Burst format, Traffic Channel TCH, Dedicated Channel DCC, Common Control Channel CCC, Signalling Channel SCH, Logical Control mapping LCM, Protocol stack, Voice coded. TETRA Functions Trunked mode operation, User hierarchies, Individual calling, Group calling, Supplementary services, Voice and Data, Data services, Direct mode operation, Tetra WAP, Circuit mode priorities, Circuit mode data, Packet mode data, Discrete and Ambient listening. Automatic vehicle locator. TETRA Procedures MS operational modes, Mobility management, Cell selection, Security & Authentication, Decryption options, Cell setup, Channel assignment, Network management - internal, Network management -external, PSTN Gateway, ISDN Gateway, Control Room Gateway.

Upstream Petroleum Economics, Risk and Fiscal Analysis
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course The 3-day hands-on petroleum economics training course provides a comprehensive overview of the practices of exploration and development petroleum economics and its application in valuing oil and gas assets to aid corporate decisions. Participants will gain a thorough understanding of the principles of economic analysis as well as practical instruction in analytical techniques used in the industry. The participants will learn how to construct economic models, to include basic fiscal terms, production and cost profiles and project timing. The resulting model will provide insights of how the various inputs affect value. Example exercises will be used throughout the course. Training Objectives Upon completion of this course, participants will be able to: Understand and construct petroleum industry cash flow projections Calculate, understand and know how to apply economic indicators Learn and apply risk analysis to exploration and production investments Evaluate and model fiscal/PSC terms of countries worldwide Target Audience The following oil & gas company personnel will benefit from the knowledge shared in this course: Geologists Explorationists Reservoir Engineers Project Accountants Contract Negotiators Financial Analysts New Venture Planners Economists Course Level Basic or Foundation Intermediate Trainer Your expert trainer has over 40 years' experience as a petroleum economist in the upstream oil and gas industry. He has presented over 230 oil and gas industry short courses worldwide on petroleum economics, risk, production sharing contracts (PSC) and fiscal analysis. In over 120 international oil industry consulting assignments, he has advised companies and governments in the Asia Pacific region on petroleum PSC and fiscal terms. He has prepared many independent valuations of petroleum properties and companies for acquisition and sale, as well as economics research reports on the oil and gas industry and including commercial support for oil field operations and investments worldwide. He has been involved in projects on petroleum royalties, design of petroleum fiscal terms, divestment of petroleum assets, and economic evaluation of assets and discoveries since the early 1990s to date. He has been working on training, consultancy, research and also advisory works in many countries including USA, UK, Denmark, Switzerland, Australia, New Zealand, Indonesia, India, Iran, Malaysia, Thailand, Vietnam, Brunei, Egypt, Libya, and South Africa. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

HSPA and HSPA+ training course description HSDPA (High Speed Downlink Packet Access) and HSUPA (High Speed Uplink Packet Access) provide speeds of upto 14Mbps downlink and 5Mbps uplink. This theory-based course provides an overview of the 3GPP R5 and R6 HSDPA/HSUPA standards and the technologies which are involved. The HSPA+ R7 enhancements are also covered. What will you learn Explain the relationship between HSPA and UMTS. Describe the benefits of HSPA/HSPA+ Explain the HSPA/HSPA+ technical enhancements. Explain packet flows in HSPA/HSPA+. Recognise the migration issues involved with HSPA/HSPA+ HSPA and HSPA+ training course details Who will benefit: Anyone working with HSPA. Prerequisites: Essential UMTS Duration 2 days HSPA and HSPA+ training course contents UMTS review UMTS architecture, components, interfaces, protocols, W-CDMA, standards, 3GPPr5, 3GPPr6, evolution to HSDPA and HSPA. HSPA basics What is HSDPA, what is HSUPA, key features, system capacities, data rates, delays. Key concepts: Adaptive modulation and coding (AMC), QPSK, 16QAM, HARQ, MAC-hs, multiplexing, subframes. HSPA channels Logical, transport, physical channels, dedicated vs. shared channels, HS-PDSCH, HS-SCCH, HS-DPCCH, code multiplexing, E-DCH, Enhanced DPCCH. MAC-architecture Controlling HS-DSCH, flow control, buffering, priority queues, packet scheduling, fast packet scheduling, Selecting modulation and coding. HARQ: Packet retransmissions, Incremental redundancy, comparison with ARQ, TFRC. MAC-d, MAC-c/sh, MAC-hs, MAC-es, MAC-e. HSPA migration HSDPA in the Radio Access Network (RAN), reuse of existing UMTS components, changes required, Impact on Iub/Iur interfaces, new and modified NBAP procedures, backwards compatibility. Packet flows Packet data session setup, simultaneous voice and data, QoS, TCP flow control, WCDMA packet scheduler, mobility procedures. HSPA phase 2 (3GPP r6) What is evolved HSPA? Speeds. Multiple Input Multiple Output (MIMO). Optional all IP architecture. R8 and LTE.

Ansible training course description The course focusses on the use of ansible for network devices instead of its usual server use case. The course progresses from the basics of ansible and playbooks onto using network specific modules including NAPALM. The use Jinja2 templating with ansible is also studied. Hands on sessions with ansible configuring routers and switches follow all major sections. What will you learn Automate tasks with ansible. Write ansible playbooks. Configure network devices with ansible. Troubleshoot network devices with ansible. Use ansible network modules. Use jinja2 templates with ansible. Ansible training course details Who will benefit: Network engineers. Prerequisites: TCP/IP Foundation Duration 2 days Ansible training course contents What is ansible? The language, the engine, the framework. Uses of ansible, orchestration. Hands on Installing ansible, enabling SSH on network devices. Ansible architecture How ansible 'normally' works, Agentless, SSH, ansible and Python, modules, how ansible work on network devices, Configuration management, inventories, playbooks, modules, ansible.cfg. Hands on Getting started, running ad hoc commands. Playbooks ansible-playbook, users, YAML, plays, tasks, modules. ansible-vault. Hands on Running playbooks. More playbooks Handlers, variables, environmental variables, playbook variables, inventory variables, variable scope and precedence, accessing variables, facts, ansible vault. Conditionals, wait_for. Hands on Using variables and conditions in playbooks. Inventories /etc/ansible/hosts, inventory variables, static inventories, dynamic inventories. Hands on Inventories and variables. Ansible network modules Built in modules, custom modules, return values. ansible-doc -l. connection: local, Cisco modules, Juniper module, Hands on Using modules for your network devices. Ansible templatings The template module, the assemble module, jinja2 templates, for, if else. Hands on Configuring network devices from templates. Roles and includes Dynamic includes, Handler includes, playbook includes. Roles, role parts: handlers, files, templates, cross platform roles, ansible galaxy. Hands on includes example, building roles. Ansible and NAPALM Installation, napalm-ansible, NAPALM modules: napalm_diff-yang, napalm_get_facts, napalm_install_config, napalm_parse_yang, napalm_ping, napalm_translate_yang, napalm_validate. Hands on Using NAPALM modules in ansible.

Junos Service Provider Switching training course description This course provides students with an overview of switching concepts such as LANs, Layer 2 address learning, bridging, virtual LANs (VLANs), provider bridging, VLAN translation, spanning-tree protocols, and Ethernet Operation, Administration, and Maintenance (OAM). This course also covers Junos operating system-specific implementations. Junos Service Provider Switching is an intermediatelevel course. What will you learn Describe carrier Ethernet. Describe the function of an Ethernet LAN. Implement VLAN tagging. Describe the components of provider bridging. Identify and use available tools to resolve network issues. Configure and monitor Ethernet OAM, ERP, LAG, STP, the RSTP, the MSTP, and the VSTP. Junos Service Provider Switching training course details Who will benefit: Individuals responsible for configuring and monitoring devices running the Junos OS. Prerequisites: Junos Intermediate Routing Duration 2 days Junos Service Provider Switching training course contents Ethernet Switching and Virtual LANs Ethernet LANs Bridging Configuring and Monitoring VLANs Automating VLAN Administration Configuring and Monitoring IRB Layer 2 Address Learning and Forwarding Layer 2 Firewall Filtering Ethernet Switching and VLANs Lab Virtual Switches Routing Instances Overview Configuring and Monitoring Virtual Switches Interconnecting Routing Instances Logical Systems Virtual Switches Lab Provider Bridging Expanding the Bridged Network Provider Bridging Configuring and Monitoring Provider Bridging Provider Bridging Lab Spanning-Tree Protocols Overview of STP Overview of RSTP Overview of MSTP Overview of VSTP Configuring and Monitoring Spanning-Tree Protocols Understanding BPDU, Loop, and Root Protection MSTP Lab Ethernet OAM OAM Overview LFM CFM Configuring and Monitoring Ethernet OAM Ethernet OAM Lab High Availability and Network Optimization ERP Overview Configuring and Monitoring ERP Link Aggregation Group Overview Configuring and Monitoring a LAG MC-LAG Overview Configuring and Monitoring an MC-LAG High Availability and Network Optimization Lab Troubleshooting and Monitoring Introduction to Troubleshooting and Monitoring Troubleshooting and Monitoring Tools Troubleshooting Case Study: Network Congestion Troubleshooting and Monitoring Lab Appendix A: Carrier Ethernet Ethernet in the WAN Ethernet Standards Organizations MX Series Layer 2 Features Appendix B: Deprecated Syntaxes Appendix C: MX Series Overview

Best Practices Procurement for Carbon Offsets in the Energy Industry
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course More energy companies today are setting ambitious net-zero targets and are expected to pour billions into the voluntary carbon offset market by the end of this decade. To get to net zero emissions, companies will need to balance emissions with nature and technology-based offsets. Markets are the best tool for connecting carbon sources and sinks. Many countries will not have enough supply inside their borders and will need to co-operate with those who have extra greenhouse gas removal potential. The energy industry is in search of effective climate tools as pressure mounts from investors and consumers for more progress on fighting rising emissions. Corporations fighting to cut their carbon footprint have for years focused on internal reduction measures. Many are now adding to that effort by turning to carbon credits, a process made easier as verification and registration tools mature. One particular category of carbon offsets leads the way: high-quality, nature-based carbon credits. These represent the largest category of carbon credit projects in the voluntary carbon market, comprising nearly half of credits issued. Public concern about this practice focused on the additionality, leakage, and integrity of carbon offsets that are created through reforestation, land preservation, carbon capture and other projects. Lack of standardization and government regulation has also increased uncertainty for all participants in carbon markets, creating risks for developers of credit-generating projects and offset purchasers. Demand for higher-quality offsets will value projects that were subjected to due diligence and rely upon reputable third-party verification. Companies purchasing offsets generated by permanent and quantifiable projects will therefore be in the best position moving forward. In this highly interactive training course, your course instructor will guide you through the latest developments and best procurement practices to successfully operate in the voluntary carbon market. Training Objectives At the end of this course, the participants will be able to: Discover the current state of the carbon economy Gain insights into the voluntary carbon market Learn about the different type carbon credits available Examine how companies can reach net zero target by using carbon offsets Uncover best practices in carbon credit procurement strategy Learn the pricing dynamics carbon credits Examine how to identify and ensure high quality credits Obtain key learning from flawed carbon offset projects Target Audience This course is intended for: Energy transition team leaders Carbon credit procurement professionals ESG strategy team leaders Finance and accounting professionals Low carbon business analysts or economists Corporate business sustainability professionals Legal, compliance and regulatory professionals Carbon trading professionals Course Level Intermediate Trainer Your expert course leader is a skilled and accomplished professional with over 25 years of extensive C-level experience in the energy markets worldwide. He has a strong expertise in all the aspects of (energy) commodity markets, international sales, marketing of services, derivatives trading, staff training and risk management within dynamic and high-pressure environments. He received a Master's degree in Law from the University of Utrecht in 1987. He started his career at the NLKKAS, the Clearing House of the Commodity Futures Exchange in Amsterdam. After working for the NLKKAS for five years, he was appointed as Member of the Management Board of the Agricultural Futures Exchange (ATA) in Amsterdam at the age of 31. While working for the Clearing House and exchange, he became an expert in all the aspects of trading and risk management of commodities. In 1997, he founded his own specialist-consulting firm that provides strategic advice about (energy) commodity markets, trading and risk management. He has advised government agencies such as the European Commission, investment banks, major utilities and commodity trading companies and various energy exchanges and market places in Europe, CEE countries, North America and Asia. Some of the issues he has advised on are the development and implementation of a Risk Management Framework, investment strategies, trading and hedging strategies, initiation of Power Exchanges (APX) and other trading platforms, the set-up of (OTC) Clearing facilities, and feasibility and market studies like for the Oil, LNG and the Carbon Market. The latest additions are (Corporate) PPAs and Artificial Intelligence for energy firms. He has given numerous seminars, workshops and (in-house) training sessions about both the physical and financial trading and risk management of commodity and carbon products. The courses have been given to companies all over the world, in countries like Japan, Singapore, Thailand, United Kingdom, Germany, Poland, Slovenia, Czech Republic, Malaysia, China, India, Belgium and the Netherlands. He has published several articles in specialist magazines such as Commodities Now and Energy Risk and he is the co-author of a book called A Guide to Emissions Trading: Risk Management and Business Implications published by Risk Books in 2004. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

ITIL© 4 Specialist - Create Deliver and Support (CDS)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Delegates attending this course must have successfully achieved the ITIL 4 Foundation Qualification; your certificate must be presented as documentary evidence to gain admission to this course. Ideally, candidates should have at least two years of professional experience working in IT Service Management. The ITIL 4 CDS Qualification would most likely suit the following delegates: Individuals continuing their journey in service management ITSM managers and aspiring ITSM managers ITSM practitioners managing the operation of IT-enabled & digital products and services, and those responsible for the end-to-end delivery Existing ITIL qualification holders wishing to develop their knowledge The above list is a suggestion only; individuals may wish to attend based on their own career aspirations, personal goals or objectives. Delegates may take as few or as many Intermediate qualifications as they require, and to suit their needs. Overview The course includes core concepts describing how different types of work (value streams) are built, tested and delivered ?end-to-end? from beginning to end and with continual iterations and feedback loops. There is also a focus on areas such as testing, knowledge, customer and employee feedback, new technologies, supplier sourcing, and ways of managing work. During this course, you will: Understand how to plan and build a service value stream to create, deliver and support services Know how relevant ITIL practices contribute to creation, delivery, and support across the SVS and value streams Know how to create, deliver and support services Understand how to integrate different value streams and activities to create, deliver and support IT-enabled products and services, and relevant practices, methods, and tools Understand service performance, service quality, and improvement methods. This course begins your journey toward the ITIL Managing Professional designation. You will acquire insight that will allow you to integrate different value streams and activities to create, deliver and support IT-enabled products and services. Armed with this knowledge and skill set, you will be confident in running those IT-enabled services, teams and workflows successfully. This class includes an exam voucher. Prerequisites ITIL© 4 Foundation 1 - PLANNING AND BUILDING A SERVICE VALUE STREAM Tackling the concepts and challenges related to SVS Using the ?shift left? approach The true value of information and technology across the SVS 2 - CONTRIBUTING TO CREATION, DELIVERY AND SUPPORT Using the value stream to design, develop and transition new services Adding to a value stream by leveraging ITIL practices Providing user support Furthering the value stream for support through ITIL practices 3 - CREATING, DELIVERING AND SUPPORTING SERVICES Coordinate, prioritize and structure activities The value of buy vs. build, sourcing, and service integration and management

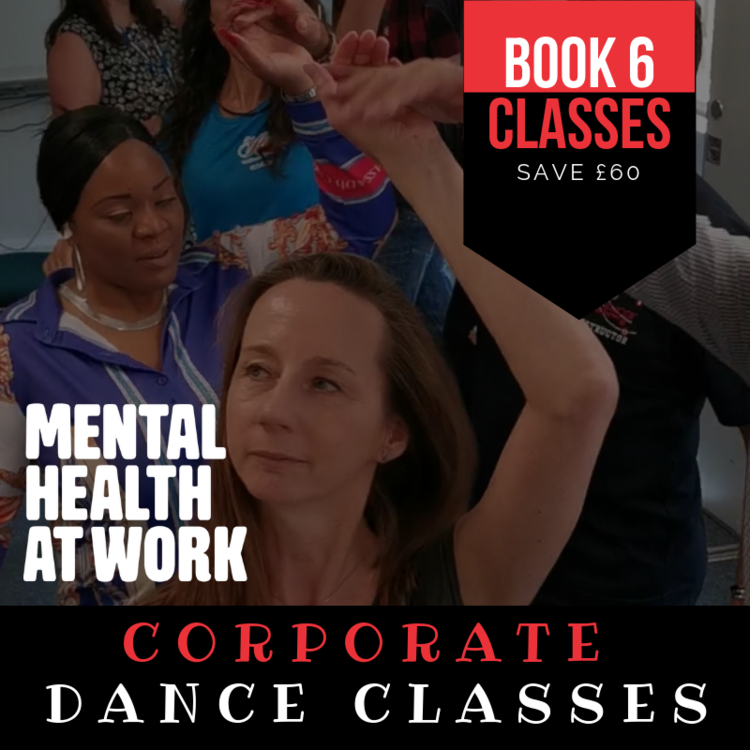
HOW DANCING CAN IMPROVE YOUR MENTAL AND PHYSICAL HEALTH Move your body to your favourite tunes – it’s the ultimate feel-good exercise and has some surprising effects on both the body and mind Music and dance have been fundamental parts of the human experience for thousands of years. No matter what your favourite tune may be, music can have a huge effect on your wellbeing – Charles Darwin even thought that our ability to make and understand rhythmic beats worked as an early form of communication. Whether or not we still share messages through music, we all know that it can change our mood and studies have shown that we share a natural sense of rhythm (no matter how much you might protest). Dance is therefore a natural outlet, and one which can do a lot to make us feel good. Club Azucar offers corporate dance packages for the workplace in order for your organisation (Companies, Institutions & Schools) not only function at its best, but to be happy and healthy in life. These are the expected benefits for the individual employee which have been also confirmed by the participants: Physical Health: Salsa/Zumba or any Latin Dance Classes improves mobility, coordination / motor skills and fitness level.while being a low-impact exercise which includes people of all ages, abilities and fitness levels Mental Health: Dancing requires full concentration so for one hour away from their desk ,participants will experience reduced stress levels, , feel refreshed and more alert and able to concentrate better following the lesson Music in combination with physical exercise has an uplifting effect through the release of endorphins and dopamine in the body & brain Learning a new skill is proven to train your brain, contribute to prevention of dementia and give the confidence to face new tasks and challenges in other areas of work and life The patience and encouragement of the teachers has furthered this new confidence and sense of achievement and contributed to participants’ belief in themselves and their ability to take themselves out of their “comfort zones” and take on new challenges Getting to know each other in a social rather than work context and learning a new skill together, dancing and laughing together, gives participants a sense of belonging and furthers team buildingDo you want more proof? Get involved and hire us!!! Booking Terms & Conditions 1. The above prices are only for Greater London 2. Fees are non refundable 3. Courses are subject to availability from both parties 4. Train, plane. petrol, or any sort of transport fares are to be refunded. 5. Cancellation must be before 24 hours every class
55215 SharePoint Online Power User
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is intended for both novice and experienced SharePoint users who wish to make full use of SharePoint Online. Overview #NAME? This course delivers the complete site owner story from start to finish in an engaging and practical way to ensure you have the confidence to plan and create new sites or manage your existing sites in SharePoint Online. Your goal is to learn how to make SharePoint online relevant to your team by using a sites functionality to help you share information and collaborate with your colleagues. During the class, you will also learn best practices and ?what not to do? as you watch live, interactive demonstrations and put theory into practice with hands on exercises in SharePoint Online. 1 - An Introduction to SharePoint Online Introducing Office 365 and SharePoint Getting started with Office 365 The cloud revolution Login to Office 365 What is Office 365 Using the app launcher What is SharePoint Office 365 settings Introducing Office 365 Groups Delve Ownership and Access OneDrive 2 - Creating Sites Planning your sites Create new subsites The Office 365 tenant Site templates Web addresses Apply a them Site collections Building your navigation Create a new site Delete subsites Team site navigation User interface: classic vs modern Site contents: classic vs modern Where does classic come from? 3 - Creating and Managing Web Pages The types of pages found in SharePoint Classic SharePoint pages Modern SharePoint pages How to use classic team site pages Create news and site pages Review features of publishing sites Web parts Save, publish, share and delete pages Communication sites 4 - Working with Apps An introduction to apps Co-authoring Marketplace apps Check In ? Out Adding apps to a site Edit and view file properties Create and manage columns Quick edit view Public and personal views File commands Managing app settings Copy link and Share Content approval Folders Major and minor versioning The recycle bin Document sets Alerts Working with files in a library OneDrive sync Create, Upload and edit files Working with classic lists 5 - Building processes with Flow and PowerApps What are business processes? Design and publish a Flow Classic tools for designing processes Getting started with PowerApps in SharePoint Design and test a classic workflow Enhance data capture with PowerApps Getting started with Flow in SharePoint Test a Flow and PowerApps enriched list 6 - Customizing Security Office 365 Group access Share a file Updating Office 365 Group Security Remove a user Managing access to SharePoint Customizing SharePoint security New sites private vs public Create permission levels and groups Setup access requests Security inheritance Share a site Security best practices 7 - Working with Search Delve Search tips An introduction to SharePoint search Accessing classic search Search in folders, libraries and sites Promoted results Search results 8 - Enterprise Content Management Managed metadata service Information management policies An introduction to content types The records center Create and manage content type In-place records management Deploy content types The content organizer Using content types in apps Durable links The content type hub
