- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
254 Courses delivered Live Online
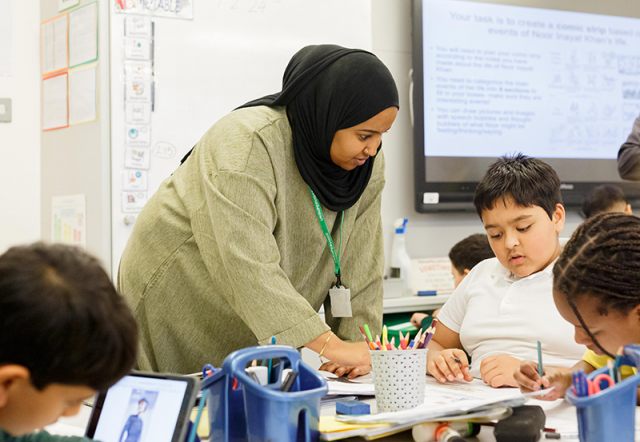
How to help young people who self harm
By Human Givens College
– how to react, support and move forward Discover how you can best help a young person who self-harms – gain the insights and skills you need to approach this distressing subject respectfully and safely, a better understanding of what self-harm is, why young people self-harm, and much more… Date: Tues 14th May 2024 Accredited CPD Certificate: 3.5 hours Length: 3.5 hours (with breaks) Start time: 9.15am GMT (until 1.30pm) "This is one of the best self-harm trainings I’ve had, honestly..."EMILY LOVE, PRIMARY PREVENTION WORKER Live Online Webinar – Join Emily Gajewski – an expert in helping people overcome self-harm – for her live webinar on Tuesday 14th May 2024. All you need is a quiet place to watch, a computer or tablet and a strong internet signal, the rest is easy. Book your place and we’ll email you confirmation – you’ll receive your Zoom link the day before the event. RECORDING – the training is recorded in case anyone experiences technical difficulties – or you can’t attend on the day – so you will also get a recording for a limited time afterwards to maximise your learning. Want to attend but can’t make this date? Then please register your interest below – and we’ll email you when a new date is available. The aim of this live online training with Emily Gajewski, a highly experienced psychotherapist specialising in treating self-harm, is to give you a thorough, in-depth understanding of why young people self-harm and how to approach/react when helping someone in both the short and long term, including the essential skills most likely to effectively support the young person on their journey to find less harmful ways of coping – the webinar focuses on the most evidence-based knowledge and skills in this area. It will also help you find ways of calming yourself in moments of overwhelm to ensure that you can be as supportive and helpful as you’d like to be. Why you should attend With the ever changing, uncertain world we live in creating a vast amount of pressure on children – emotionally and physically – more children and teenagers are experiencing extremely stressful, distressing situations, with many looking for coping mechanisms to help them deal with their negative thoughts, feelings and emotions. Self harm (including self injury) is hugely on the increase and rates are higher than ever since Covid-19 and the long periods of isolation and uncertainty young people have experienced in ‘lock downs’. A survey of 61 secondary school children by charity Place2Be, shows self-harm reports increased by 77%, from 48 to 85, from August to September 2021. Finding the right words to approach self-harming can be difficult – this online webinar was created to help you (parents, carers, teachers) approach this topic with empathy and confidence. Discovering that a young person you are caring for is self harming can be an extremely stressful situation. When we are highly emotional, it can cause us to react in desperate ways, which are often not helpful or supportive to the young person, even if our intentions are totally well-meaning. “A really helpful, caring approach – it has clarified so much for me and I can now see a sensible way forward.”MARTIN, PARENT. This course is relevant to a range of self-harming behaviours including: self-injury cutting, ripping or carving skin burning skin punching or hitting themselves scratching or pinching (including dermatillomania) poisoning themselves with tablets or liquids (or similar) over-eating and under-eating (anorexia or bulimia) biting yourself (dermatophagia) inserting objects into your body overdosing, exercising excessively pulling your hair (trichotillomania) getting into fights where you know you will get hurt What you will learn What is self-harm? Why young people self-harm How common is self-harming How to approach the subject (building rapport, trust…) How to react if your child (or any young person) tells you they are self harming (what not to say and do) The distinction between self harm and a suicide attempt The addictive element to self harm How to help a young person break the addictive pattern Helping a child in the short- and long term The influence of social media and peers Keeping your child safe Looking after yourself (managing stress, anxiety and worry for the household) Finding professional help View booking details Who this training is suitable for Parents, other family members and/or carers of children and young people who are at risk of self harming or currently self harming. Anyone who works with young people and needs to know how best to help when someone discloses that they self-harm or who they suspect may be self-harming. Therapists and counsellors who want to gain a better understanding so they can support families with a member who self harms. Course Programme The ‘How to help young people who self harm’ live online webinar starts at 9.15am and runs until 1.30pm (GMT). 9.15am Join the Zoom meeting 9.30am Understanding self harm 10.45am Comfort break and discussion 10.55am How to approach self harm and be most helpful 12.00pm Comfort break and discussion 12.10pm Creating the optimal conditions for recovery 1.30pm Webinar ends This course has been independently accredited by the internationally recognised CPD Standards Office for 3.5 hours of CPD training. On completion of this training you’ll receive CPD certificates from the College and the CPD Standards Office.
Cisco Implementing Cisco Collaboration Conferencing v2.0 (CLCNF)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Deployment engineer Network engineer Sales engineer Overview After taking this course, you should be able to: Describe the Cisco conferencing architecture including cloud, hybrid, and on-premises conferencing Describe the physical deployment options and deployment models for Cisco Meeting Server, including Cisco Meeting Server 1000, 2000, and virtual machine Configure a Cisco Meeting Server single combined deployment for Web-Real Time Communications (WebRTC) endpoints within the enterprise Use APIs and the Cisco Meeting Server API Guide to configure profiles using Postman and the Webadmin API tool Configure a scalable and resilient deployment of Cisco Meeting Server with three servers for WebRTC endpoints within the enterprise Configure a scalable and resilient deployment of Cisco Meeting Server to support standard Session Initiation Protocol (SIP) and WebRTC connectivity outside the enterprise Configure a scalable and resilient deployment of Cisco Meeting Server to support recording and streaming of conferences Configure Cisco Unified Communications Manager and Cisco Meeting Server to support Rendezvous, Scheduled, and Ad-hoc conferencing for Cisco Unified CM registered endpoints Configure Cisco Meeting Server to integrate with a preconfigured on-premise Microsoft Skype for Business installation Install Cisco TelePresence Management Suite (Cisco TMS) and Cisco TelePresence Management Suite for Microsoft Exchange (Cisco TMSXE) on a single Microsoft Windows 2012 server and connect to an existing SQL environment Install and integrate Cisco Meeting Management with Cisco TMS and Cisco Meeting Server Set up and manage a scheduled conference with Cisco TMS and Cisco Meeting Management Capture and analyze logs from Cisco Meeting Server and Cisco Meeting Manager to diagnose faults, including a SIP connection error The Implementing Cisco Collaboration Conferencing (CLCNF) v1.0 course focuses on Cisco© on-premises conferencing architecture and solutions. You will gain knowledge and skills to design and implement common conferencing deployment scenarios of Cisco Meeting Server, its integration with call control features such as Cisco Unified Communications Manager and Cisco Expressway, and other Cisco collaboration conferencing devices.This course offers lessons and hands-on labs to prepare you for the 300-825 Implementing Cisco Collaboration Conferencing (CLCNF) exam. Course outline Describing Cisco Conferencing Architecture Configuring a Single Combined Deployment Installing Cisco Meeting Server Using APIs with Cisco Meeting Server Configuring a Cisco Meeting Server Scalable and Resilient Deployment Configuring Business to Business (B2B) and WebRTC Firewall Traversal Connectivity for Cisco Meeting Server Configuring Recording and Streaming with Cisco Meeting Server Troubleshooting Cisco Meeting Server Integrating Cisco Meeting Server with Cisco Unified CM Integrating Cisco Meeting Server with Microsoft Skype for Business Installing and Operating Cisco TMS and Cisco TMSXE Installing and Integrating Cisco Meeting Management Additional course details: Nexus Humans Cisco Implementing Cisco Collaboration Conferencing v2.0 (CLCNF) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Cisco Implementing Cisco Collaboration Conferencing v2.0 (CLCNF) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

SC-200T00 Microsoft Security Operations Analyst
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The Microsoft Security Operations Analyst collaborates with organizational stakeholders to secure information technology systems for the organization. Their goal is to reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders. Responsibilities include threat management, monitoring, and response by using a variety of security solutions across their environment. The role primarily investigates, responds to, and hunts for threats using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security products. Since the Security Operations Analyst consumes the operational output of these tools, they are also a critical stakeholder in the configuration and deployment of these technologies. Learn how to investigate, respond to, and hunt for threats using Microsoft Sentinel, Microsoft Defender for Cloud, and Microsoft 365 Defender. In this course you will learn how to mitigate cyberthreats using these technologies. Specifically, you will configure and use Microsoft Sentinel as well as utilize Kusto Query Language (KQL) to perform detection, analysis, and reporting. The course was designed for people who work in a Security Operations job role and helps learners prepare for the exam SC-200: Microsoft Security Operations Analyst. Prerequisites Basic understanding of Microsoft 365 Fundamental understanding of Microsoft security, compliance, and identity products Intermediate understanding of Windows 10 Familiarity with Azure services, specifically Azure SQL Database and Azure Storage Familiarity with Azure virtual machines and virtual networking Basic understanding of scripting concepts. 1 - Introduction to Microsoft 365 threat protection Explore Extended Detection & Response (XDR) response use cases Understand Microsoft Defender XDR in a Security Operations Center (SOC) Explore Microsoft Security Graph Investigate security incidents in Microsoft Defender XDR 2 - Mitigate incidents using Microsoft 365 Defender Use the Microsoft Defender portal Manage incidents Investigate incidents Manage and investigate alerts Manage automated investigations Use the action center Explore advanced hunting Investigate Microsoft Entra sign-in logs Understand Microsoft Secure Score Analyze threat analytics Analyze reports Configure the Microsoft Defender portal 3 - Protect your identities with Microsoft Entra ID Protection Microsoft Entra ID Protection overview Detect risks with Microsoft Entra ID Protection policies Investigate and remediate risks detected by Microsoft Entra ID Protection 4 - Remediate risks with Microsoft Defender for Office 365 Automate, investigate, and remediate Configure, protect, and detect Simulate attacks 5 - Safeguard your environment with Microsoft Defender for Identity Configure Microsoft Defender for Identity sensors Review compromised accounts or data Integrate with other Microsoft tools 6 - Secure your cloud apps and services with Microsoft Defender for Cloud Apps Understand the Defender for Cloud Apps Framework Explore your cloud apps with Cloud Discovery Protect your data and apps with Conditional Access App Control Walk through discovery and access control with Microsoft Defender for Cloud Apps Classify and protect sensitive information Detect Threats 7 - Respond to data loss prevention alerts using Microsoft 365 Describe data loss prevention alerts Investigate data loss prevention alerts in Microsoft Purview Investigate data loss prevention alerts in Microsoft Defender for Cloud Apps 8 - Manage insider risk in Microsoft Purview Insider risk management overview Create and manage insider risk policies Investigate insider risk alerts Take action on insider risk alerts through cases Manage insider risk management forensic evidence Create insider risk management notice templates 9 - Investigate threats by using audit features in Microsoft Defender XDR and Microsoft Purview Standard Explore Microsoft Purview Audit solutions Implement Microsoft Purview Audit (Standard) Start recording activity in the Unified Audit Log Search the Unified Audit Log (UAL) Export, configure, and view audit log records Use audit log searching to investigate common support issues 10 - Investigate threats using audit in Microsoft Defender XDR and Microsoft Purview (Premium) Explore Microsoft Purview Audit (Premium) Implement Microsoft Purview Audit (Premium) Manage audit log retention policies Investigate compromised email accounts using Purview Audit (Premium) 11 - Investigate threats with Content search in Microsoft Purview Explore Microsoft Purview eDiscovery solutions Create a content search View the search results and statistics Export the search results and search report Configure search permissions filtering Search for and delete email messages 12 - Protect against threats with Microsoft Defender for Endpoint Practice security administration Hunt threats within your network 13 - Deploy the Microsoft Defender for Endpoint environment Create your environment Understand operating systems compatibility and features Onboard devices Manage access Create and manage roles for role-based access control Configure device groups Configure environment advanced features 14 - Implement Windows security enhancements with Microsoft Defender for Endpoint Understand attack surface reduction Enable attack surface reduction rules 15 - Perform device investigations in Microsoft Defender for Endpoint Use the device inventory list Investigate the device Use behavioral blocking Detect devices with device discovery 16 - Perform actions on a device using Microsoft Defender for Endpoint Explain device actions Run Microsoft Defender antivirus scan on devices Collect investigation package from devices Initiate live response session 17 - Perform evidence and entities investigations using Microsoft Defender for Endpoint Investigate a file Investigate a user account Investigate an IP address Investigate a domain 18 - Configure and manage automation using Microsoft Defender for Endpoint Configure advanced features Manage automation upload and folder settings Configure automated investigation and remediation capabilities Block at risk devices 19 - Configure for alerts and detections in Microsoft Defender for Endpoint Configure advanced features Configure alert notifications Manage alert suppression Manage indicators 20 - Utilize Vulnerability Management in Microsoft Defender for Endpoint Understand vulnerability management Explore vulnerabilities on your devices Manage remediation 21 - Plan for cloud workload protections using Microsoft Defender for Cloud Explain Microsoft Defender for Cloud Describe Microsoft Defender for Cloud workload protections Enable Microsoft Defender for Cloud 22 - Connect Azure assets to Microsoft Defender for Cloud Explore and manage your resources with asset inventory Configure auto provisioning Manual log analytics agent provisioning 23 - Connect non-Azure resources to Microsoft Defender for Cloud Protect non-Azure resources Connect non-Azure machines Connect your AWS accounts Connect your GCP accounts 24 - Manage your cloud security posture management? Explore Secure Score Explore Recommendations Measure and enforce regulatory compliance Understand Workbooks 25 - Explain cloud workload protections in Microsoft Defender for Cloud Understand Microsoft Defender for servers Understand Microsoft Defender for App Service Understand Microsoft Defender for Storage Understand Microsoft Defender for SQL Understand Microsoft Defender for open-source databases Understand Microsoft Defender for Key Vault Understand Microsoft Defender for Resource Manager Understand Microsoft Defender for DNS Understand Microsoft Defender for Containers Understand Microsoft Defender additional protections 26 - Remediate security alerts using Microsoft Defender for Cloud Understand security alerts Remediate alerts and automate responses Suppress alerts from Defender for Cloud Generate threat intelligence reports Respond to alerts from Azure resources 27 - Construct KQL statements for Microsoft Sentinel Understand the Kusto Query Language statement structure Use the search operator Use the where operator Use the let statement Use the extend operator Use the order by operator Use the project operators 28 - Analyze query results using KQL Use the summarize operator Use the summarize operator to filter results Use the summarize operator to prepare data Use the render operator to create visualizations 29 - Build multi-table statements using KQL Use the union operator Use the join operator 30 - Work with data in Microsoft Sentinel using Kusto Query Language Extract data from unstructured string fields Extract data from structured string data Integrate external data Create parsers with functions 31 - Introduction to Microsoft Sentinel What is Microsoft Sentinel? How Microsoft Sentinel works When to use Microsoft Sentinel 32 - Create and manage Microsoft Sentinel workspaces Plan for the Microsoft Sentinel workspace Create a Microsoft Sentinel workspace Manage workspaces across tenants using Azure Lighthouse Understand Microsoft Sentinel permissions and roles Manage Microsoft Sentinel settings Configure logs 33 - Query logs in Microsoft Sentinel Query logs in the logs page Understand Microsoft Sentinel tables Understand common tables Understand Microsoft Defender XDR tables 34 - Use watchlists in Microsoft Sentinel Plan for watchlists Create a watchlist Manage watchlists 35 - Utilize threat intelligence in Microsoft Sentinel Define threat intelligence Manage your threat indicators View your threat indicators with KQL 36 - Connect data to Microsoft Sentinel using data connectors Ingest log data with data connectors Understand data connector providers View connected hosts 37 - Connect Microsoft services to Microsoft Sentinel Plan for Microsoft services connectors Connect the Microsoft Office 365 connector Connect the Microsoft Entra connector Connect the Microsoft Entra ID Protection connector Connect the Azure Activity connector 38 - Connect Microsoft Defender XDR to Microsoft Sentinel Plan for Microsoft Defender XDR connectors Connect the Microsoft Defender XDR connector Connect Microsoft Defender for Cloud connector Connect Microsoft Defender for IoT Connect Microsoft Defender legacy connectors 39 - Connect Windows hosts to Microsoft Sentinel Plan for Windows hosts security events connector Connect using the Windows Security Events via AMA Connector Connect using the Security Events via Legacy Agent Connector Collect Sysmon event logs 40 - Connect Common Event Format logs to Microsoft Sentinel Plan for Common Event Format connector Connect your external solution using the Common Event Format connector 41 - Connect syslog data sources to Microsoft Sentinel Plan for syslog data collection Collect data from Linux-based sources using syslog Configure the Data Collection Rule for Syslog Data Sources Parse syslog data with KQL 42 - Connect threat indicators to Microsoft Sentinel Plan for threat intelligence connectors Connect the threat intelligence TAXII connector Connect the threat intelligence platforms connector View your threat indicators with KQL 43 - Threat detection with Microsoft Sentinel analytics What is Microsoft Sentinel Analytics? Types of analytics rules Create an analytics rule from templates Create an analytics rule from wizard Manage analytics rules 44 - Automation in Microsoft Sentinel Understand automation options Create automation rules 45 - Threat response with Microsoft Sentinel playbooks What are Microsoft Sentinel playbooks? Trigger a playbook in real-time Run playbooks on demand 46 - Security incident management in Microsoft Sentinel Understand incidents Incident evidence and entities Incident management 47 - Identify threats with Behavioral Analytics Understand behavioral analytics Explore entities Display entity behavior information Use Anomaly detection analytical rule templates 48 - Data normalization in Microsoft Sentinel Understand data normalization Use ASIM Parsers Understand parameterized KQL functions Create an ASIM Parser Configure Azure Monitor Data Collection Rules 49 - Query, visualize, and monitor data in Microsoft Sentinel Monitor and visualize data Query data using Kusto Query Language Use default Microsoft Sentinel Workbooks Create a new Microsoft Sentinel Workbook 50 - Manage content in Microsoft Sentinel Use solutions from the content hub Use repositories for deployment 51 - Explain threat hunting concepts in Microsoft Sentinel Understand cybersecurity threat hunts Develop a hypothesis Explore MITRE ATT&CK 52 - Threat hunting with Microsoft Sentinel Explore creation and management of threat-hunting queries Save key findings with bookmarks Observe threats over time with livestream 53 - Use Search jobs in Microsoft Sentinel Hunt with a Search Job Restore historical data 54 - Hunt for threats using notebooks in Microsoft Sentinel Access Azure Sentinel data with external tools Hunt with notebooks Create a notebook Explore notebook code

Introduction to Yoga and Beneficial Practical Parapsychology Course
By Integral Studies Academy
Immerse yourself in the ancient practice of yoga, a transformative journey that extends far beyond the mere physical postures. Our comprehensive yoga sessions are meticulously curated and led by seasoned professionals, offering a serene sanctuary tailored for the demands of modern-day professionals yearning for holistic balance and wellness. Delve into innate human abilities such as intuition, telepathy, clairvoyance, lucid dreaming, and energy healing. Uncover these dormant gifts existing within and enjoy awakening them fully.
DevSecOps Practitioner (DevOps Institute)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for The target audience for the DevSecOps Practitioner course are professionals including: Anyone focused on implementing or improving DevSecOps practices in their organization Anyone interested in modern IT leadership and organizational change approaches Business Managers Business Stakeholders Change Agents Consultants DevOps Practitioners IT Directors IT Managers IT Team Leaders Product Owners Scrum Masters Software Engineers Site Reliability Engineers System Integrators Tool Providers Overview After completing this course, students will be able to: Comprehend the underlying principles of DevSecOps Distinguish between the technical elements used across DevSecOps practices Demonstrate how practical maturity concepts can be extended across multiple areas. Implement metric-based assessments tied to your organization. Recognize modern architectural concepts including microservice to monolith transitions. Recognize the various languages and tools used to communicate architectural concepts. Contrast the options used to build a DevSecOps infrastructure through Platform as a Service, Server-less construction, and event-driven mediums Prepare hiring practices to recognize and understand the individual knowledge, skills, and abilities required for mature Dev Identify the various technical requirements tied to the DevSecOps pipelines and how those impact people and process choices. Review various approaches to securing data repositories and pipelines. Analyze how monitoring and observability practices contribute to valuable outcomes. Comprehend how to implement monitoring at key points to contribute to actionable analysis. Evaluate how different experimental structures contribute to the 3rd Way. Identify future trends that may affect DevSecOps The DevSecOps Practitioner course is intended as a follow-on to the DevSecOps Foundation course. The course builds on previous understanding to dive into the technical implementation. The course aims to equip participants with the practices, methods, and tools to engage people across the organization involved in reliability through the use of real-life scenarios and case stories. Upon completion of the course, participants will have tangible takeaways to leverage when back in the office such as implementing DevSecOps practices to their organizational structure, building better pipelines in distributed systems, and having a common technological language. This course positions learners to successfully complete the DevSecOps Practitioner certification exam. DevSecOps Advanced Basics Why Advance Practices? General Awareness People-Finding Them Core Process Technology Overview Understanding Applied Metrics Metric Terms Accelerating People-Reporting and Recording Integrating Process Technology Automation Architecting and Planning for DevSecOps Architecture Basics Finding an Architect Reporting and Recording Environments Process Accelerating Decisions Creating a DevSecOps Infrastructure What is Infrastructure? Equipping the Team Design Challenges Monitoring Infrastructure Establishing a Pipeline Pipelines and Workflows Engineers and Capabilities Continuous Engagement Automate and Identify Observing DevSecOps Outcomes Observability vs. Monitoring Who gets which Report? Setting Observation Points Implementing Observability Practical 3rd Way Applications Revisiting 3rd Way Building Experiments Getting the Most from the Experiment The Future of DevOps Looking Towards the Future Staying Trained Innovation What, and from Who? Post-Class Assignments/Exercises Extended advanced reading associated with Case Stories from the course Additional course details: Nexus Humans DevSecOps Practitioner (DevOps Institute) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the DevSecOps Practitioner (DevOps Institute) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

7-Day Meditation Challenge
By Drama2Calmer Mindfulness
Kickstart or invigorate your mindfulness practice! Commit to joining a live guided meditation every morning for seven days.

PL-200T00 Microsoft Power Platform Functional Consultant
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for A Microsoft Power Platform Functional Consultant is responsible for creating and configuring apps, automations, and solutions. They act as the liaison between users and the implementation team. The functional consultant promotes utilization of solutions within an organization. The functional consultant may perform discovery, engage subject matter experts and stakeholders, capture requirements, and map requirements to features. They implement components of a solution including application enhancements, custom user experiences, system integrations, data conversions, custom process automation, and simple visualizations. This course will teach you to use Microsoft Power Platform solutions to simplify, automate, and empower business processes for organizations in the role of a Functional Consultant. A Microsoft Power Platform Functional Consultant is responsible for creating and configuring apps, automations, and solutions. They act as the liaison between users and the implementation team. The functional consultant promotes utilization of solutions within an organization. The functional consultant may perform discovery, engage subject matter experts and stakeholders, capture requirements, and map requirements to features. They implement components of a solution including application enhancements, custom user experiences, system integrations, data conversions, custom process automation, and simple visualizations. This course may contain a 1-day Applied Workshop. This workshop will allow you to practice your Functional Consultant skills by creating an end-to-end solution to solve a problem for a fictitious company. The solution will include a Microsoft Dataverse database, Power Apps canvas app, and Power Automate flows. Prerequisites Experience as an IT professional or student Working knowledge of Microsoft Power Platform and its key components Knowledge of Microsoft Dataverse (or general data modeling) and security concepts 1 - Describe the business value of the Microsoft Power Platform Explore Microsoft Power Platform Describe the business value of the Power Platform Explore connectors and Microsoft Dataverse Describe how Power Platform works with Microsoft 365 apps and services Explore how Power Platform works with Microsoft Teams Describe how Power Platform works with Microsoft Dynamics 365 apps Describe how Power Platform solutions consume Microsoft Azure services Explore how Microsoft Power Platform apps work together Use Artificial Intelligence to increase productivity 2 - Core components of Power Pages Get started with Power Pages Core tools and components of Power Pages Overview of Power Pages security Overview of Power Pages extensibility 3 - Explore Power Pages templates Site design templates Scenario-based templates Dynamics 365 Power Pages site templates 4 - Explore Power Pages design studio Work with pages Page components Site styling and templates 5 - Explore Power Pages design studio data and security features Data workspace in Power Pages design studio Power Pages security features 6 - Introduction to Power Pages administration Power Pages administrative tools Set up workspace in Power Pages design studio 7 - Get started building with Power BI Use Power BI Building blocks of Power BI Tour and use the Power BI service 8 - Get data with Power BI Desktop Overview of Power BI Desktop Explore Power BI Desktop Connect to data sources Get data from Excel Transform data to include in a report Combine data from multiple sources Clean data to include in a report 9 - Model data in Power BI How to manage your data relationships Create calculated columns Optimize data models Create measures Create calculated tables Explore time-based data 10 - Use visuals in Power BI Create and customize simple visualizations Create slicers Map visualizations Matrices and tables Create scatter, waterfall, and funnel charts Modify colors in charts and visuals Page layout and formatting 11 - Explore data in Power BI Quick insights in Power BI Create and configure a dashboard Ask questions of your data with natural language Create custom Q&A suggestions Share dashboards with your organization Display visuals and tiles in full screen Edit tile details and add widgets Get more space on your dashboard 12 - Publish and share in Power BI Publish Power BI Desktop reports Print and export dashboards and reports Introducing Power BI Mobile Create workspaces in Power BI Build apps Use apps Integrate OneDrive for Business with Power BI Publish to web 13 - Create and manage workspaces in Power BI Distribute a report or dashboard Monitor usage and performance Recommend a development life cycle strategy Troubleshoot data by viewing its lineage Configure data protection 14 - Manage semantic models in Power BI Use a Power BI gateway to connect to on-premises data sources Configure a semantic model scheduled refresh Configure incremental refresh settings Manage and promote semantic models Troubleshoot service connectivity Boost performance with query caching (Premium) 15 - Create dashboards in Power BI Configure data alerts Explore data by asking questions Review Quick insights Add a dashboard theme Pin a live report page to a dashboard Configure a real-time dashboard Set mobile view 16 - Implement row-level security Configure row-level security with the static method Configure row-level security with the dynamic method 17 - Create tables in Dataverse Table characteristics Table relationships Dataverse logic and security Dataverse auditing Dual-write vs. virtual tables 18 - Manage tables in Dataverse Identify tables and table types in Dataverse Create a custom table Enable attachments within a table Licensing requirements for each table type 19 - Create and manage columns within a table in Dataverse Define columns in Microsoft Dataverse Column types in Microsoft Dataverse Add a column to a table Create a primary name column Restrictions that apply to columns in a table Create an auto numbering column Create an alternate key 20 - Create a relationship between tables in Dataverse Relate one or more tables - Introduction Relationship types that are available in Microsoft Dataverse Create a one-to-many relationship between tables Create a many-to-many relationship between tables Edit or delete relationships 21 - Working with choices in Dataverse Define choice column Standard choices column 22 - Get started with security roles in Dataverse Understand environment roles Adding or disabling an environment user Understand security concepts in Dataverse Understand user security roles and security role defaults Check the roles that a user belongs to Configure Dataverse teams for security Configure Dataverse group teams for security 23 - Use administration options for Dataverse Use Microsoft Power Platform Admin Center portal Tenant storage capacity Advanced Customization options in Power Apps Portal Enable and disable auditing 24 - Manage Dynamics 365 model-driven app settings and security Configure role-based security Manage teams and business units Explore settings and customizations 25 - Introduction to Microsoft Power Platform security and governance Identify Microsoft Power Platform environments Data Loss Prevention policies Microsoft Power Platform Center of Excellence Starter Kit 26 - Get started with model-driven apps in Power Apps Introducing model-driven apps Components of model-driven apps Design model-driven apps Incorporate business process flows 27 - Configure forms, charts, and dashboards in model-driven apps Forms overview Form elements Configure multiple forms Use specialized form components Configure views overview Configure grids Create and edit views Configure charts overview Dashboards overview Use interactive streams and tiles 28 - Get started with Power Apps canvas apps Power Apps building blocks Ways to build Power Apps Power Apps related technologies Additional Power Apps related technologies Designing a Power Apps app 29 - Connect to other data in a Power Apps canvas app Overview of the different data sources Work with action-based data sources Power Automate is a companion to Power Apps 30 - How to build the UI in a canvas app in Power Apps Use themes to quickly change the appearance of your app Branding a control Icons Images Personalization Using the tablet or phone form factors 31 - Manage apps in Power Apps Power Apps review 32 - Build your first app with Power Apps and Dataverse for Teams Create your first app with the hero template Customize your app with Power Apps Studio Publish your app Install template apps 33 - Access Dataverse in Power Pages websites Use lists to display multiple Dataverse records Use forms to interact with Dataverse data 34 - Authentication and user management in Power Pages Power Pages authentication settings User registration in Power Pages Authentication management for Power Pages users Power Pages authentication providers 35 - Power Pages maintenance and troubleshooting Power Pages website maintenance Power Pages website troubleshooting 36 - Define and create business rules in Dataverse Define business rules - Introduction Define the components of a business rule Create a business rule 37 - Get started with Power Automate Introducing Power Automate Troubleshoot flows 38 - Use the Admin center to manage environments and data policies in Power Automate Administer flows Export and import flows Learn how to distribute button flows 39 - Use Dataverse triggers and actions in Power Automate Dataverse triggers Query data Create, update, delete, and relate actions 40 - Extend Dataverse with Power Automate Set up a flow and configure its trigger Email Dataverse record Add to-do items Test and run your flow 41 - Introduction to expressions in Power Automate Get started with expressions Notes make things easier Types of functions Write complex expressions 42 - Build your first Power Automate for desktop flow Set up the environment Explore Power Automate for desktop Create your first Power Automate for desktop flow Record Power Automate for desktop actions Edit and test recorded actions 43 - Run a Power Automate for desktop flow in unattended mode Set up an unattended desktop flow Create a new cloud flow that calls an existing flow in unattended mode Perform a test run Best practices 44 - Optimize your business process with process advisor Get familiar with process advisor Create your first recording Edit recordings and group actions Analyze recordings and interpret results Automation recommendations 45 - Get started with Microsoft Copilot Studio bots Get started working with environments Create bots and work with the Microsoft Copilot Studio interface Create topics Test bots Publish bots and analyze performance 46 - Enhance Microsoft Copilot Studio bots Use Power Automate to add actions Transfer conversations to agents by using Omnichannel for Customer Service Create topics for existing support content Analyze bot performance 47 - Manage topics in Microsoft Copilot Studio Work with bot topics Branch a topic Create topics for existing support content Work with system fallback topics Manage topics 48 - Manage Power Virtual Agents Environments in Microsoft Copilot Studio Bot topics permissions Bot entities and flow permissions Monitor and diagnose Administer and manage Export and import bots Authentication 49 - Get started building with Power BI Use Power BI Building blocks of Power BI Tour and use the Power BI service 50 - Get data with Power BI Desktop Overview of Power BI Desktop Explore Power BI Desktop Connect to data sources Get data from Excel Transform data to include in a report Combine data from multiple sources Clean data to include in a report 51 - Model data in Power BI How to manage your data relationships Create calculated columns Optimize data models Create measures Create calculated tables Explore time-based data 52 - Use visuals in Power BI Create and customize simple visualizations Create slicers Map visualizations Matrices and tables Create scatter, waterfall, and funnel charts Modify colors in charts and visuals Page layout and formatting 53 - Explore data in Power BI Quick insights in Power BI Create and configure a dashboard Ask questions of your data with natural language Create custom Q&A suggestions Share dashboards with your organization Display visuals and tiles in full screen Edit tile details and add widgets Get more space on your dashboard 54 - Publish and share in Power BI Publish Power BI Desktop reports Print and export dashboards and reports Introducing Power BI Mobile Create workspaces in Power BI Build apps Use apps Integrate OneDrive for Business with Power BI Publish to web 55 - Manage solutions in Power Apps and Power Automate Add and remove apps, flows, and entities in a solution Edit a solution-aware app, flow, and table Build and deploy a complex solution with flows, apps, and entities Automate solution management 56 - Load/export data and create data views in Dataverse View data in a table Create or edit views of data in a table Load data into a table Export data from a table Add, update, or delete data in a table by using Excel Import data using Power Query Generate a new dataflow from an Excel Template Dataflow and Azure integration 57 - Get started with AI Builder Choose an AI capability Create your first model Ways to use your models 58 - Manage models in AI Builder Model lifecycle Manage model versions Share your models 59 - Use AI Builder in Power Automate AI Builder in Power Automate saves time Advanced usage of AI Builder in Power Automate 60 - Functional Consultant skills Create entity relationship diagrams Create and document mock-ups Document functional requirements and artifacts Complete fit-gap analysis Discuss stakeholder management responsibilities Understand industry accelerators Define Application Lifecycle Management Participate in testing Evaluate options Define connectors Understand Power Apps component framework 61 - Solution Architect series: Plan application lifecycle management for Power Platform Key considerations for ALM Solutions Configuration and reference data Release process ALM with Azure DevOps

Historical Association webinar series: Practical approaches to disciplinary concepts in primary history Presenter: Emmy Quinn This session will give teachers tips on how to explore similarity and difference in a meaningful way in the primary classroom. It will look at introducing the concept in Key Stage 1 to more developed use of it in Key Stage 2, for example similarity and difference in the earliest civilisations. The session will show how to demonstrate that similarity and difference can be nuanced and will support with getting children to move beyond basic ideas To use your corporate webinar offer for this webinar please complete this form: https://forms.office.com/e/95945xGxdh
Managing Agile Projects Using TFS 2017
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is designed for project managers, Scrum masters, business analysts, and team leaders looking to effectively manage their development projects using Team Foundation Server 2017. Overview The course also demonstrates how TFS facilitates the use of storyboards to prototype experiences, request stakeholder feedback, foster team collaboration, and generate reports. The final two modules of the course provide an overview of how testers and developers can work effectively using appropriate tools in the Visual Studio family. In this course, attendees will plan a new software development project and go through the steps to initiate the project using Visual Studio 2017. This includes recording requirements, creating a product backlog, and estimating effort for backlog items. Introducing the Microsoft Visual Studio 2017 Family What?s new in Visual Studio 2017 Overview of the Visual Studio 2017 family Overview of product features Project workflow across the Visual Studio 2017 suite of products Initiating a New Project Organizing projects in TFS Understanding process templates Creating a new team project Setting team project properties Switching between team projects Work Item Primer Overview of work items Traceability between work items Searching and creating custom queries Work item charting and pinning charts Work item tagging Configuring project notifications Creating our Product Backlog Examining requirement types Creating backlog items Creating requirement hierarchies using features The importance of acceptance criteria Agile Estimation Introduction to estimation Using story points Planning Poker and other popular estimation techniques Adding your estimates to TFS work items Working from the Product Backlog Introducing the Kanban board Entering and editing details on the Kanban board Customizing columns, including using split columns and limiting WIP Recording our Definition of Done (DoD) Understanding the Cumulative Flow Diagram Working in Sprints Specifying your sprint schedule and your team capacity Selecting items for the sprint backlog using forecasting Decomposing requirements into tasks Using burndown charts to track progress Monitoring work using the task board Working with unparented work items Retrospectives The importance of retrospectives Conducting an efficient sprint retrospective What you should avoid in your retrospective Working with TFS Teams Configuring teams in our team project Managing work from a master backlog Allocating work to our teams Configuring iterations for TFS teams Enhancing Requirements Using Storyboards Overview of storyboarding capabilities Creating a storyboard to illustrate a requirement Linking a storyboard to a work item Getting Stakeholder Feedback Introducing the Microsoft Feedback Client Using the Microsoft Feedback Client to provide rich feedback to the team Adding continuous feedback into your workflow Fostering Team Collaboration An overview of the various clients The use of email in sharing information Choosing the appropriate client tool Creating and Customizing Reports Overview of reporting architecture Reviewing the out of the box reports Adding new reports Creating ad hoc reports using Excel Overview of Agile Testing The role of the tester in a sprint planning meeting A lap around web-based test management Creating a test plan Creating manual test cases from requirements Overview of Agile Development Using My Work to select tasks from the sprint backlog Understanding the value of linking changesets to work items The importance of unit testing Creating a continuous integration build Additional course details: Nexus Humans Managing Agile Projects Using TFS 2017 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Managing Agile Projects Using TFS 2017 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

