- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
684 Courses in Leeds delivered Live Online
AZ-104T00 Microsoft Azure Administrator
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for Azure Administrators. The Azure Administrator implements, manages, and monitors identity, governance, storage, compute, and virtual networks in a cloud environment. The Azure Administrator will provision, size, monitor, and adjust resources as appropriate. This course teaches IT Professionals how to manage their Azure subscriptions, secure identities, administer the infrastructure, configure virtual networking, connect Azure and on-premises sites, manage network traffic, implement storage solutions, create and scale virtual machines, implement web apps and containers, back up and share data, and monitor your solution. Prerequisites Successful Azure Administrators start this role with experience in virtualization, networking, identity, and storage. Understanding of on-premises virtualization technologies, including: VMs, virtual networking, and virtual hard disks. Understanding of network configurations, including TCP/IP, Domain Name System (DNS), virtual private networks (VPNs), firewalls, and encryption technologies. Understanding of Active Directory concepts, including users, groups, and role-based access control. Understanding of resilience and disaster recovery, including backup and restore operations. 1 - Configure Microsoft Entra ID Describe Microsoft Entra ID benefits and features Describe Microsoft Entra concepts Compare Active Directory Domain Services to Microsoft Entra ID Select Microsoft Entra editions Implement Microsoft Entra join Implement Microsoft Entra self-service password reset 2 - Configure user and group accounts Create user accounts Manage user accounts Create bulk user accounts Create group accounts Create administrative units 3 - Configure subscriptions Identify Azure regions Implement Azure subscriptions Obtain an Azure subscription Identify Azure subscription usage Implement Microsoft Cost Management Apply resource tagging Apply cost savings 4 - Configure Azure Policy Create management groups Implement Azure policies Create Azure policies Create policy definitions Create an initiative definition Scope the initiative definition Determine compliance 5 - Configure role-based access control Implement role-based access control Create a role definition Create a role assignment Compare Azure roles to Microsoft Entra roles Apply role-based access control Review fundamental Azure RBAC roles 6 - Configure Azure resources with tools Use the Azure portal Use Azure Cloud Shell Use Azure PowerShell Use Azure CLI 7 - Use Azure Resource Manager Review Azure Resource Manager benefits Review Azure resource terminology Create resource groups Create Azure Resource Manager locks Reorganize Azure resources Remove resources and resource groups Determine resource limits 8 - Configure resources with Azure Resource Manager templates Review Azure Resource Manager template advantages Explore the Azure Resource Manager template schema Explore the Azure Resource Manager template parameters Consider Bicep templates Review QuickStart templates 9 - Configure virtual networks Plan virtual networks Create subnets Create virtual networks Plan IP addressing Create public IP addressing Associate public IP addresses Allocate or assign private IP addresses 10 - Configure network security groups Implement network security groups Determine network security group rules Determine network security group effective rules Create network security group rules Implement application security groups 11 - Configure Azure DNS Identify domains and custom domains Verify custom domain names Create Azure DNS zones Delegate DNS domains Add DNS record sets Plan for Azure Private DNS zones Review Azure Private DNS zone scenarios 12 - Configure Azure Virtual Network peering Determine Azure Virtual Network peering uses Determine gateway transit and connectivity Create virtual network peering Extend peering with user-defined routes and service chaining 13 - Configure network routing and endpoints Review system routes Identify user-defined routes Determine service endpoint uses Determine service endpoint services Identify private link uses 14 - Configure Azure Load Balancer Determine Azure Load Balancer uses Implement a public load balancer Implement an internal load balancer Determine load balancer SKUs Create back-end pools Create health probes Create load balancer rules 15 - Configure Azure Application Gateway Implement Azure Application Gateway Determine Azure Application Gateway routing Configure Azure Application Gateway components 16 - Configure storage accounts Implement Azure Storage Explore Azure Storage services Determine storage account types Determine replication strategies Access storage Secure storage endpoints 17 - Configure Azure Blob Storage Implement Azure Blob Storage Create blob containers Assign blob access tiers Add blob lifecycle management rules Determine blob object replication Upload blobs Determine Blob Storage pricing 18 - Configure Azure Storage security Review Azure Storage security strategies Create shared access signatures Identify URI and SAS parameters Determine Azure Storage encryption Create customer-managed keys Apply Azure Storage security best practices 19 - Configure Azure Files and Azure File Sync Compare storage for file shares and blob data Manage Azure file shares Create file share snapshots Implement Azure File Sync Identify Azure File Sync components Deploy Azure File Sync 20 - Configure Azure Storage with tools Use Azure Storage Explorer Use the Azure Import/Export service Use the WAImportExport tool Use the AzCopy tool 21 - Configure virtual machines Review cloud services responsibilities Plan virtual machines Determine virtual machine sizing Determine virtual machine storage Create virtual machines in the Azure portal Connect to virtual machines 22 - Configure virtual machine availability Plan for maintenance and downtime Create availability sets Review update domains and fault domains Review availability zones Compare vertical and horizontal scaling Implement Azure Virtual Machine Scale Sets Create Virtual Machine Scale Sets Implement autoscale Configure autoscale 23 - Configure Azure App Service plans Implement Azure App Service plans Determine Azure App Service plan pricing Scale up and scale out Azure App Service Configure Azure App Service autoscale 24 - Configure Azure App Service Implement Azure App Service Create an app with App Service Explore continuous integration and deployment Create deployment slots Add deployment slots Secure your App Service app Create custom domain names Back up and restore your App Service app Use Azure Application Insights 25 - Configure Azure Container Instances Compare containers to virtual machines Review Azure Container Instances Implement container groups Review the Docker platform 26 - Configure file and folder backups Describe Azure Backup benefits Implement Backup Center for Azure Backup Configure Azure Recovery Services vault backup options Use the Microsoft Azure Recovery Services (MARS) agent Configure on-premises file and folder backups 27 - Configure virtual machine backups Explore options to protect virtual machine data Create virtual machine snapshots in Azure Backup Set up Azure Recovery Services vault backup options Back up your virtual machines Restore your virtual machines Implement System Center DPM and Azure Backup Server Compare the MARS agent and Azure Backup Server Implement soft delete for your virtual machines Implement Azure Site Recovery 28 - Configure Azure Monitor Describe Azure Monitor key capabilities Describe Azure Monitor components Define metrics and logs Identify monitoring data and tiers Describe activity log events Query the activity log 29 - Configure Azure alerts Describe Azure Monitor alerts Manage Azure Monitor alerts Create alert rules Create action groups 30 - Configure Log Analytics Determine Log Analytics uses Create a Log Analytics workspace Create Kusto (KQL) queries Structure Log Analytics queries 31 - Configure Network Watcher Describe Azure Network Watcher features Review IP flow verify diagnostics Review next hop diagnostics Visualize the network topology

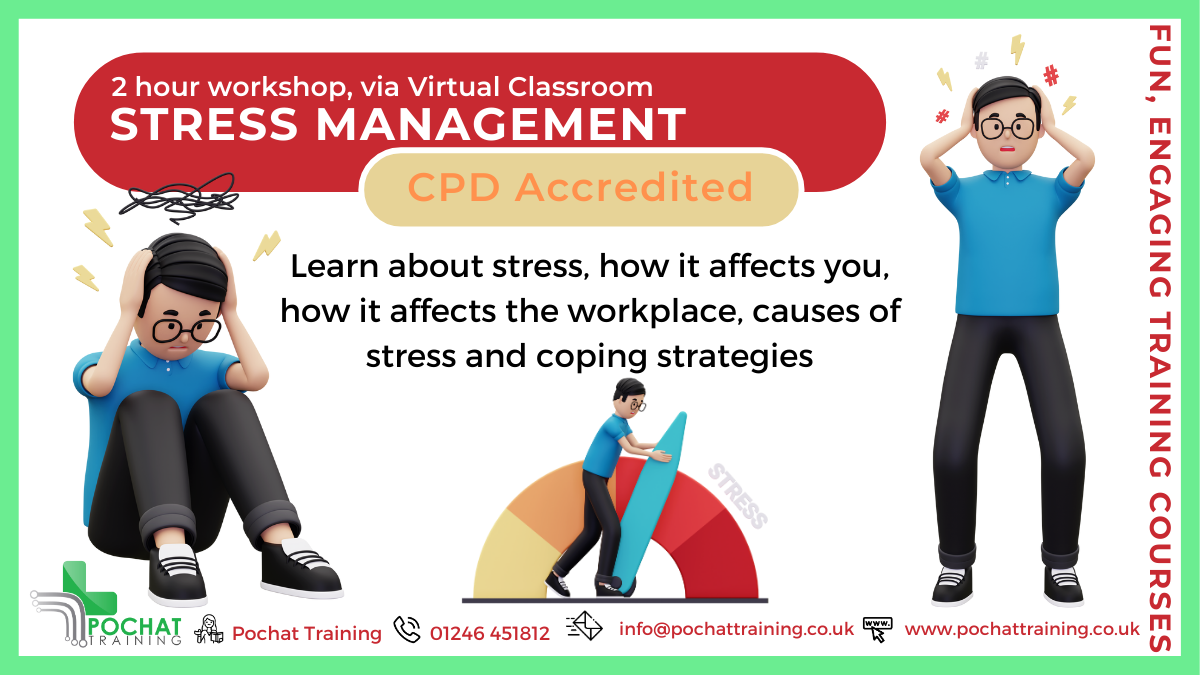
Tackle Stress Before It Tackles You! Work-related stress affects 875,000 people every year, and its impacts go beyond the workplace—affecting your mind, body, and personal life. But it doesn’t have to be this way. Join our Stress Management Workshops to: ✔️ Understand the difference between stress and pressure ✔️ Learn the causes of stress in and out of the workplace ✔️ Discover practical coping strategies and build mental resilience These workshops are packed with insights, tools, and strategies to help you take control of your stress levels and improve your well-being—personally and professionally. There are two different ones to choose from - a 2 hour workshop and a 4 hour workshop! Course Contents of 2 hour course: What is Stress Stress versus Pressure Statistics Absenteeism, Presenteeism and Leaveism Workplace Causes of Stress Personal Causes of Stress Short-Term and Long-Term Effects of Stress Coping Strategies Mental Resilience Benefits of this Workshop: In 2022/23. 875,000 people suffered from work-related stress, depression or anxiety The affects of stress are far reaching, affecting one's mind, body, social and personal life Become more aware of what stresses you, what is does to you and find ways to reduce those stress levels
Data Protection (GDPR) for Small Charities
By Computer Law Training
Straightforward GDPR training for small charities - because you want to get it right!

AWS Cloud Practitioner Essentials
By Nexus Human
Duration 1 Days 6 CPD hours This course is intended for Sales Legal Marketing Business analysts Project managers AWS Academy students Other IT-related professionals Overview Summarize the working definition of AWS Differentiate between on-premises, hybrid-cloud, and all-in cloud Describe the basic global infrastructure of the AWS Cloud Explain the six benefits of the AWS Cloud Describe and provide an example of the core AWS services, including compute, network, databases, and storage Identify an appropriate solution using AWS Cloud services with various use cases Describe the AWS Well-Architected Framework Explain the shared responsibility model Describe the core security services within the AWS Cloud Describe the basics of AWS Cloud migration Articulate the financial benefits of the AWS Cloud for an organization?s cost management Define the core billing, account management, and pricing models Explain how to use pricing tools to make cost-effective choices for AWS services This course is for individuals who seek an overall understanding of the Amazon Web Services (AWS) Cloud, independent of specific technical roles. You will learn about AWS Cloud concepts, AWS services, security, architecture, pricing, and support to build your AWS Cloud knowledge. This course also helps you prepare for the AWS Certified Cloud Practitioner exam. Prerequisites General IT technical knowledge, General IT business knowledge 1 - Introduction to Amazon Web Services Summarize the benefits of AWS Describe differences between on-demand delivery and cloud deployments Summarize the pay-as-you-go pricing model 2 - Compute in the Cloud Describe the benefits of Amazon Elastic Compute Cloud (Amazon EC2) at a basic level Identify the different Amazon EC2 instance types Differentiate between the various billing options for Amazon EC2 Describe the benefits of Amazon EC2 Auto Scaling Summarize the benefits of Elastic Load Balancing Give an example of the uses for Elastic Load Balancing Summarize the differences between Amazon Simple Notification Service (Amazon SNS) and Amazon Simple Queue Services (Amazon SQS) Summarize additional AWS compute options 3 - Global Infrastructure and Reliability Summarize the benefits of the AWS Global Infrastructure Describe the basic concept of Availability Zones Describe the benefits of Amazon CloudFront and Edge locations Compare different methods for provisioning AWS services 4 - Networking Describe the basic concepts of networking Describe the difference between public and private networking resources Explain a virtual private gateway using a real life scenario Explain a virtual private network (VPN) using a real life scenario Describe the benefit of AWS Direct Connect Describe the benefit of hybrid deployments Describe the layers of security used in an IT strategy Describe which services are used to interact with the AWS global network 5 - Storage and Databases Summarize the basic concept of storage and databases Describe benefits of Amazon Elastic Block Store (Amazon EBS) Describe benefits of Amazon Simple Storage Service (Amazon S3) Describe the benefits of Amazon Elastic File System (Amazon EFS) Summarize various storage solutions Describe the benefits of Amazon Relational Database Service (Amazon RDS) Describe the benefits of Amazon DynamoDB Summarize various database services 6 - Security Explain the benefits of the shared responsibility model Describe multi-factor authentication (MFA) Differentiate between the AWS Identity and Access Management (IAM) security levels Describe security policies at a basic level Explain the benefits of AWS Organizations Summarize the benefits of compliance with AWS Explain primary AWS security services at a basic level 7 - Monitoring and Analytics Summarize approaches to monitoring your AWS environment Describe the benefits of Amazon CloudWatch Describe the benefits of AWS CloudTrail Describe the benefits of AWS Trusted Advisor 8 - Pricing and Support Understand AWS pricing and support models Describe the AWS Free Tier Describe key benefits of AWS Organizations and consolidated billing Explain the benefits of AWS Budgets Explain the benefits of AWS Cost Explorer Explain the primary benefits of the AWS Pricing Calculator Distinguish between the various AWS Support Plans Describe the benefits of AWS Marketplace 9 - Migration and Innovation Understand migration and innovation in the AWS Cloud Summarize the AWS Cloud Adoption Framework (AWS CAF) Summarize six key factors of a cloud migration strategy Describe the benefits of various AWS data migration solutions, such as AWS Snowcone, AWS Snowball, and AWS Snowmobile Summarize the broad scope of innovative solutions that AWS offers Summarize the five pillars of the AWS Well-Architected Framewor 10 - AWS Certified Cloud Practitioner Basics Determine resources for preparing for the AWS Certified Cloud Practitioner examination Describe benefits of becoming AWS Certified

Offshore & Marine Supply Base Operations Management - For Servicing International E & P Fleet and Wind Farm Operations
By EnergyEdge - Training for a Sustainable Energy Future
About this Training Course The Oil & Gas E&P industry is evolving from deep sea exploration to renewable sources of energy through windfarms and solar fields offshore. In tandem, OSBs will need to evolve for sustainability and revival from stagnant traditional Supply Base Models. The changing role of OSBs is toward support services for decommissioning projects and LNG Floating Terminals. In addition, the new geographical regions of East and South Africa are coming up at a faster pace. All such operations are dependent upon a complex network of transport and supply in order to deliver the staff, materials, machinery, and crew provisions where and when needed. This 3 full-day course is curated to enhance the skills and competencies of passionate professionals to plan and organise resources, minimise turnaround time for the vessels engaged in support of Offshore E & P operations. Various hands-on exercises can equip the participants to implement viable and feasible approaches for safe and efficient management of OSBs in compliance with continuously evolving international best practices and Oil & Gas standards. This course is specially developed for investors, business owners, senior executives and professionals from the offshore & marine logistics industry, with the following objectives: To provide a firm understanding about the role of an Offshore & Marine Supply Base in support of Oil & Gas E & P fleet operations, in contrast with traditional merchant shipping logistics. To provide an in-depth knowledge about the range and diversity of services being offered by Offshore & Marine Supply Bases ('OSB') in the target regions. To equip with the knowledge and information required for taking investment decisions when venturing in Offshore E & P Sector. To introduce contemporary techniques and tools required to identify target customer segments while developing a new OSB or expanding operations of an existing OSB. To elaborate comparative management methodologies for OSB facilities and services management, based on deployment of ICT solutions so as to deliver value added services to the customers. To learn to identify methodologies for sales and distribution of services to the customers and non-paying users of the OSB. To identify relevant state legislation for licensing & governing an OSB, and enforce through contractual obligations, rights and responsibilities of the parties as clients of an OSB. To develop and implement Business Processes with built-in Performance Evaluation Metrics for achieving competitive advantage over the peers in the OSB segment. To develop and implement integrated OSB's Risk Management framework. This course can also be offered through Virtual Instructor Led Training (VILT) format. Training Objectives Upon completion of this course, the participants will be able to: Implement and comply with the QHSSSE regulations and national or Port Controls regime for safe handling of import & export cargo and movements of the vessels. Establish role and responsibilities of the Offshore Supply Base management team. Plan and organise resources so as to minimise turnaround time for the vessels engaged in support of Offshore E & P and Windfarms operations. Plan and organise OSB cranes, vehicles, MHE, spaces and relevant facilities for storage, movement, and custody transfer of various types of solid and liquid cargo, tools, shackles, bulk materials in open yards and ships' gears. Be aware of potential emergency situations and how to respond and coordinate with relevant internal and external agencies. Manage safety of personnel of sub-contractors, stevedores', tenants, and ship crew, when engaged in OSB operations. Differentiate between various ships, technical and functional characteristics, safety requirements and potential hazards of each operation. Build competency in developing and maintaining documentary evidence for traceability for all works executed during the specific period or operation. Develop techniques for performance monitoring and continuous improvements based on lessons learned from each operation at the Base as well as from reports about peers in the similar business. Target Audience This course is intended for: Operations Management personnel from existing OSBs, Ports, Logistics & Warehouses, Offshore Fields, E & P Infrastructure Support services providers. Professionals who are interested in OSB segment of the Offshore & Marine Oil & Gas Industry. Participants who have no prior knowledge about OSB Operations and are new to the Offshore Logistics And highly recommended for: Managers, Engineers, and Professionals assigned to lead new initiatives in Logistics Management of Offshore & Marine Segments of Oil & Gas Industry. Course Level Intermediate Trainer Principal Management Consultant Chartered Valuer and Appraiser (CVA) FACICA | FAMTAC | FAIADR | M.S.I.D | Member, AIEN LL.M. (IP Law), M. Sc. (Maritime Studies), M. Tech (Knowledge Engineering), MBA, First Class CoC (MCA, UK), B. E. (Elect) Your expert course leader during the last 47 year period, has worked and consulted in the industry verticals encompassing: Technology, Oil & Gas Exploration & Production, Petrochemical Process Plants and Power Plant Construction Projects, Logistics & Warehousing, Marine, Offshore, Oil & Gas Pipelines, Infrastructure Development Projects (Ports, Offshore Supply Bases, Oil & Gas Terminals and Airports etc), EPCIC Contracts, and Shipyards, in South East Asia, Africa, Middle East, Americas and Europe. He serves as the Principal Management Consultant with a management consultancy in Hong Kong and Singapore, specialising in the fields of corporate management consultancy, international contracts reviews and alternative dispute resolutions services. He undertakes special assignments for conducting audits and valuation of intangible properties involving proprietary processes for licensed production, and licensing of intellectual property rights (IP Rights) in patents, trademarks, and industrial designs. He is frequently engaged for assignments like due diligence, acquisitions, mergers, resolving various operational issues, technology transfer and agency services contracts reviews, cost controls, and enhancement of Supply Chain Management. He has been conferred the credentials of Chartered Valuer & Appraiser (CVA) by SAC and IVAS, in accordance with the international valuation standards setting body IVSC. His consulting experience includes Charterparty Management, Business Process Re-engineering, Diversifications, Corporate Development, Marketing, Complex Project Management, Feasibility Studies, Dispute Resolutions and Market Research. He has successfully assisted Marine and offshore E & P clients in managing contractual disputes arising from various international contracts for upgrading & conversion projects. He continues to be actively engaged in claims reviews, mediation, arbitration, litigation, and expert witness related assignments, arising from international contracts and Charterparty Agreements. He graduated with a Bachelor's degree in Electrical Engineering, MBA in General Management, Master of Technology in Knowledge Engineering, Master of Science in Maritime Studies, and LL.M. (IP Law). He also holds professional qualifications in Business Valuations and Appraisers for CVA, arbitration, law, and marine engineering, including the Chief Engineer's First-Class Certificate of Competency (MCA, UK). He is further qualified and accredited as Certified International Arbitrator, Chartered Arbitrator, Sports arbitrator under CAS Rules, WIPO Neutral, Australian Communications and Media Authority (ACMA) Bargaining Code Arbitrator, Accredited Adjudicator and Accredited Mediator (Malaysia). He is admitted to the international panels of arbitrators and neutrals with WIPO, Geneva; ACICA, AMTAC and ACMA, Australia; BVIAC (British Virgin Islands); JIAC (Jamaica); HKIAC Hong Kong; AIAC, Malaysia; AIADR, Malaysia; KCAB, Seoul, South Korea; ICA, Delhi, India; ICC (Singapore); SISV, Singapore; SCMA, Singapore; SCCA, Saudi Arabia; VIAC Vienna, Austria; Thailand Arbitration Centre (THAC), and Mediator with AIAC Malaysia, CMC, and SIMI Singapore. POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

AZ-500T00 Microsoft Azure Security Technologies
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is for Azure Security Engineers who are planning to take the associated certification exam, or who are performing security tasks in their day-to-day job. This course would also be helpful to an engineer that wants to specialize in providing security for Azure-based digital platforms and play an integral role in protecting an organization's data. This course provides IT Security Professionals with the knowledge and skills needed to implement security controls, maintain an organization?s security posture, and identify and remediate security vulnerabilities. This course includes security for identity and access, platform protection, data and applications, and security operations. Prerequisites AZ-104T00 - Microsoft Azure Administrator Security best practices and industry security requirements such as defense in depth, least privileged access, role-based access control, multi-factor authentication, shared responsibility, and zero trust model. Be familiar with security protocols such as Virtual Private Networks (VPN), Internet Security Protocol (IPSec), Secure Socket Layer (SSL), disk and data encryption methods. Have some experience deploying Azure workloads. This course does not cover the basics of Azure administration, instead the course content builds on that knowledge by adding security specific information. Have experience with Windows and Linux operating systems and scripting languages. Course labs may use PowerShell and the CLI. 1 - Manage identities in Microsoft Entra ID Secure users in Microsoft Entra ID Secure groups in Microsoft Entra ID Recommend when to use external identities Secure external identities Implement Microsoft Entra Identity protection 2 - Manage authentication by using Microsoft Entra ID Configure Microsoft Entra Verified ID Implement multifactor authentication (MFA) Implement passwordless authentication Implement password protection Implement single sign-on (SSO) Integrate single sign-on (SSO) and identity providers Recommend and enforce modern authentication protocols 3 - Manage authorization by using Microsoft Entra ID Configure Azure role permissions for management groups, subscriptions, resource groups, and resources Assign built-in roles in Microsoft Entra ID Assign built-in roles in Azure Create and assign a custom role in Microsoft Entra ID Implement and manage Microsoft Entra Permissions Management Configure Microsoft Entra Privileged Identity Management Configure role management and access reviews by using Microsoft Entra Identity Governance Implement Conditional Access policies 4 - Manage application access in Microsoft Entra ID Manage access to enterprise applications in Microsoft Entra ID, including OAuth permission grants Manage app registrations in Microsoft Entra ID Configure app registration permission scopes Manage app registration permission consent Manage and use service principals Manage managed identities for Azure resources Recommend when to use and configure a Microsoft Entra Application Proxy, including authentication 5 - Plan and implement security for virtual networks Plan and implement Network Security Groups (NSGs) and Application Security Groups (ASGs) Plan and implement User-Defined Routes (UDRs) Plan and implement Virtual Network peering or gateway Plan and implement Virtual Wide Area Network, including secured virtual hub Secure VPN connectivity, including point-to-site and site-to-site Implement encryption over ExpressRoute Configure firewall settings on PaaS resources Monitor network security by using Network Watcher, including NSG flow logging 6 - Plan and implement security for private access to Azure resources Plan and implement virtual network Service Endpoints Plan and implement Private Endpoints Plan and implement Private Link services Plan and implement network integration for Azure App Service and Azure Functions Plan and implement network security configurations for an App Service Environment (ASE) Plan and implement network security configurations for an Azure SQL Managed Instance 7 - Plan and implement security for public access to Azure resources Plan and implement Transport Layer Security (TLS) to applications, including Azure App Service and API Management Plan, implement, and manage an Azure Firewall, Azure Firewall Manager and firewall policies Plan and implement an Azure Application Gateway Plan and implement an Azure Front Door, including Content Delivery Network (CDN) Plan and implement a Web Application Firewall (WAF) Recommend when to use Azure DDoS Protection Standard 8 - Plan and implement advanced security for compute Plan and implement remote access to public endpoints, Azure Bastion and just-in-time (JIT) virtual machine (VM) access Configure network isolation for Azure Kubernetes Service (AKS) Secure and monitor AKS Configure authentication for AKS Configure security for Azure Container Instances (ACIs) Configure security for Azure Container Apps (ACAs) Manage access to Azure Container Registry (ACR) Configure disk encryption, Azure Disk Encryption (ADE), encryption as host, and confidential disk encryption Recommend security configurations for Azure API Management 9 - Plan and implement security for storage Configure access control for storage accounts Manage life cycle for storage account access keys Select and configure an appropriate method for access to Azure Files Select and configure an appropriate method for access to Azure Blob Storage Select and configure an appropriate method for access to Azure Tables Select and configure an appropriate method for access to Azure Queues Select and configure appropriate methods for protecting against data security threats, including soft delete, backups, versioning, and immutable storage Configure Bring your own key (BYOK) Enable double encryption at the Azure Storage infrastructure level 10 - Plan and implement security for Azure SQL Database and Azure SQL Managed Instance Enable database authentication by using Microsoft Entra ID Enable and monitor database audit Identify use cases for the Microsoft Purview governance portal Implement data classification of sensitive information by using the Microsoft Purview governance portal Plan and implement dynamic mask Implement transparent data encryption? Recommend when to use Azure SQL Database Always Encrypted 11 - Plan, implement, and manage governance for security Create, assign, and interpret security policies and initiatives in Azure Policy Configure security settings by using Azure Blueprint Deploy secure infrastructures by using a landing zone Create and configure an Azure Key Vault Recommend when to use a dedicated Hardware Security Module (HSM) Configure access to Key Vault, including vault access policies and Azure Role Based Access Control Manage certificates, secrets, and keys Configure key rotation Configure backup and recovery of certificates, secrets, and keys 12 - Manage security posture by using Microsoft Defender for Cloud Implement Microsoft Defender for Cloud Identify and remediate security risks by using the Microsoft Defender for Cloud Secure Score and Inventory Assess compliance against security frameworks and Microsoft Defender for Cloud Add industry and regulatory standards to Microsoft Defender for Cloud Add custom initiatives to Microsoft Defender for Cloud Connect hybrid cloud and multicloud environments to Microsoft Defender for Cloud Identify and monitor external assets by using Microsoft Defender External Attack Surface Management 13 - Configure and manage threat protection by using Microsoft Defender for Cloud Enable workload protection services in Microsoft Defender for Cloud, including Microsoft Defender for Storage, Databases, Containers, App Service, Key Vault, Resource Manager, and DNS Configure Microsoft Defender for Servers Configure Microsoft Defender for Azure SQL Database Manage and respond to security alerts in Microsoft Defender for Cloud Configure workflow automation by using Microsoft Defender for Cloud Evaluate vulnerability scans from Microsoft Defender for Server 14 - Configure and manage security monitoring and automation solutions Monitor security events by using Azure Monitor Configure data connectors in Microsoft Sentinel Create and customize analytics rules in Microsoft Sentinel Configure automation in Microsoft Sentinel Additional course details: Nexus Humans AZ-500T00 Microsoft Azure Security Technologies training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the AZ-500T00 Microsoft Azure Security Technologies course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Overview This course provides an explanation of the underlying concepts of the Risk-Based Maintenance approach, guidance on its relationship and integration within asset management and the overall risk management process. This course will show delegates how to develop an action plan for implementation into an effective and cost-efficient maintenance strategy.

AZ-801T00 Configuring Windows Server Hybrid Advanced Services
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This four-day course is intended for Windows Server Hybrid Administrators who have experience working with Windows Server and want to extend the capabilities of their on-premises environments by combining on-premises and hybrid technologies. Windows Server Hybrid Administrators who already implement and manage on-premises core technologies want to secure and protect their environments, migrate virtual and physical workloads to Azure Iaas, enable a highly available, fully redundant environment, and perform monitoring and troubleshooting. This course teaches IT Professionals to configure advanced Windows Server services using on-premises, hybrid, and cloud technologies. The course teaches IT Professionals how to leverage the hybrid capabilities of Azure, how to migrate virtual and physical server workloads to Azure IaaS, and how to secure Azure VMs running Windows Server. The course also teaches IT Professionals how to perform tasks related to high availability, troubleshooting, and disaster recovery. The course highlights administrative tools and technologies including Windows Admin Center, PowerShell, Azure Arc, Azure Automation Update Management, Microsoft Defender for Identity, Azure Security Center, Azure Migrate, and Azure Monitor. Prerequisites An understanding of the following concepts as related to Windows Server technologies: High availability and disaster recovery Automation Monitoring Troubleshooting 1 - Secure Windows Server user accounts Configure user account rights Protect user accounts with the Protected Users group Describe Windows Defender Credential Guard Block NTLM authentication Locate problematic accounts 2 - Hardening Windows Server Describe Local Password Administrator Solution Configure Privileged Access Workstations Secure domain controllers Analyze security configuration with Security Compliance Toolkit Secure SMB traffic 3 - Windows Server update management Explore Windows Update Outline Windows Server Update Services server deployment options Define Windows Server Update Services update management process Describe the process of Update Management 4 - Secure Windows Server DNS Implement split-horizon DNS Create DNS policies Implement DNS policies Secure Windows Server DNS Implement DNSSEC 5 - Implement Windows Server IaaS VM network security Implement network security groups and Windows IaaS VMs Implement adaptive network hardening Implement Azure Firewall and Windows IaaS VMs Implement Windows firewall with Windows Server IaaS VMs Choose the appropriate filtering solution Deploy and configure Azure firewall using the Azure portal Capture network traffic with network watcher Log network traffic to and from a VM using the Azure portal 6 - Audit the security of Windows Server IaaS Virtual Machines Describe Azure Security Center Enable Azure Security Center in hybrid environments Implement and assess security policies Protect your resources with Azure Security Center Implement Azure Sentinel 7 - Manage Azure updates Describe update management Enable update management Deploy updates View update assessments Manage updates for your Azure Virtual Machines 8 - Create and implement application allowlists with adaptive application control Describe adaptive application control Implement adaptive application control policies 9 - Configure BitLocker disk encryption for Windows IaaS Virtual Machines Describe Azure Disk Encryption and server-side encryption Configure Key Vault for Azure Disk Encryption Encrypt Azure IaaS Virtual Machine hard disks Back up and recover data from encrypted disks Create and encrypt a Windows Virtual Machine 10 - Implement change tracking and file integrity monitoring for Windows IaaS VMs Implement Change Tracking and Inventory Manage Change Tracking and Inventory Manage tracked files Implement File Integrity Monitoring Select and monitor entities Use File Integrity Monitoring 11 - Introduction to Cluster Shared Volumes Determine the functionality of Cluster Shared Volumes Explore the architecture and components of Cluster Shared Volumes Implement Cluster Shared Volumes 12 - Implement Windows Server failover clustering Define Windows Server failover clustering Plan Windows Server failover clustering Implement Windows Server failover clustering Manage Windows Server failover clustering Implement stretch clusters Define cluster sets 13 - Implement high availability of Windows Server VMs Select high-availability options for Hyper-V Consider network load balancing for Hyper-V VMs Implement Hyper-V VM live migration Implement Hyper-V VMs storage migration 14 - Implement Windows Server File Server high availability Explore the Windows Server File Server high-availability options Define Cluster Shared Volumes Implement Scale-Out File Server Implement Storage Replica 15 - Implement scale and high availability with Windows Server VM Describe virtual machine scale sets Implement scaling Implement load-balancing VMs Create a virtual machine scale set in the Azure portal Describe Azure Site Recovery Implement Azure Site Recovery 16 - Implement Hyper-V Replica Define Hyper-V Replica Plan for Hyper-V Replica Configure and implement Hyper-V Replica Define extended replication Define Azure Site Recovery Implement Site Recovery from on-premises site to Azure Implement Site Recovery from on-premises site to on-premises site 17 - Protect your on-premises infrastructure from disasters with Azure Site Recovery Azure Site Recovery overview Workloads supported for protection with Azure Site Recovery Run a disaster recovery drill Failover and failback 18 - Implement hybrid backup and recovery with Windows Server IaaS Describe Azure Backup Implement recovery vaults Implement Azure Backup policies Recover Windows IaaS Virtual Machines Perform file and folder recovery Perform backup and restore of on-premises workloads Manage Azure Virtual Machine backups with Azure Backup service 19 - Protect your Azure infrastructure with Azure Site Recovery What is Azure Site Recovery Prepare for disaster recovery with Azure Site Recovery Run a disaster recovery drill Failover and failback using Azure Site Recovery 20 - Protect your virtual machines by using Azure Backup Azure Backup features and scenarios Back up an Azure virtual machine by using Azure Backup Restore virtual machine data 21 - Active Directory Domain Services migration Examine upgrade vs. migration Upgrade a previous version of Active Directory Domain Services to Windows Server 2022 Migrate to Active Directory Domain Services in Windows Server 2022 from a previous version Explore the Active Directory Migration Tool 22 - Migrate file server workloads using Storage Migration Service Storage Migration Service overview and usage scenarios Storage migration requirements Migrate a server with Storage migration Evaluate storage migration considerations 23 - Migrate Windows Server roles Describe the Windows Server Migration Tools Install the Migration Tools Migrate roles using the Migration Tools 24 - Migrate on-premises Windows Server instances to Azure IaaS virtual machines Plan your migration Describe Azure Migrate Perform server assessment Assess physical servers with Azure Migrate Migrate Windows Server workloads by using Azure Migrate 25 - Upgrade and migrate Windows Server IaaS virtual machines Describe Azure Migrate Migrate Windows Server workloads by using Azure Migrate Describe storage migration Migrate file servers by using Storage Migration Service 26 - Containerize and migrate ASP.NET applications to Azure App Service Azure Migrate App Containerization overview 27 - Monitor Windows Server performance Use Performance Monitor to identify performance problems Use Resource Monitor to review current resource usage Review reliability with Reliability Monitor Implement a performance monitoring methodology Use Data Collector Sets to analyze server performance Monitor network infrastructure services Monitor virtual machines running Windows Server Monitor performance with Windows Admin Center Use System Insights to help predict future capacity issues Optimize the performance of Windows Server 28 - Manage and monitor Windows Server event logs Describe Windows Server event logs Use Windows Admin Center to review logs Use Server Manager to review logs Use custom views Implement event log subscriptions 29 - Implement Windows Server auditing and diagnostics Describe basic auditing categories Describe advanced categories Log user access Enable setup and boot event collection 30 - Troubleshoot Active Directory Recover objects from the AD recycle bin Recover the AD DS database Recover SYSVOL Troubleshoot AD DS replication Troubleshoot hybrid authentication issues 31 - Monitor Windows Server IaaS Virtual Machines and hybrid instances Enable Azure Monitor for Virtual Machines Monitor an Azure Virtual Machine with Azure Monitor Enable Azure Monitor in hybrid scenarios Collect data from a Windows computer in a hybrid environment Integrate Azure Monitor with Microsoft Operations Manager 32 - Monitor your Azure virtual machines with Azure Monitor Monitoring for Azure VMs Monitor VM host data Use Metrics Explorer to view detailed host metrics Collect client performance counters by using VM insights Collect VM client event logs 33 - Troubleshoot on-premises and hybrid networking Diagnose DHCP proble

C10M09 - Gas Extinguishing Detection & Electrical Actuation BS 6266 & BS 7273-1 (Online)
5.0(1)By Ember Compliance
Learners will develop knowledge of FD&FA systems and apply this to the provision of detection and electrical actuation for gas extinguishing systems.

