- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
178 Courses in Cardiff delivered Live Online
IPsec training course description This hands on course focuses on IPsec VPNs. Rather than focusing on one implementation this course concentrates on the technologies and protocols of IPsec. Starting with an overview of the complete IPsec architecture the course then moves onto ESP packet analysis along with encryption and authentication provided. IKEv1 and IKEv2 are both covered in detail. Having covered IPsec with pre shared keys the course then moves onto IPsec with certificates followed by IPsec issues. The course is vendor neutral with hands on with both Cisco and Microsoft implementations. What will you learn Explain how IPsec works. Explain the role of AH, ESP and IKE. Configure IPsec. Troubleshoot IPsec. IPsec training course details Who will benefit: Technical staff working with IPsec. Prerequisites: Definitive IP VPNs for engineers. Duration 3 days IPsec training course contents What is IPsec? How to spell IPsec, IPsec is IP security, confidentiality, integrity, authenticity, replay protection, what is a VPN? Network layer security, IPsec and IPv4, IPsec and IPv6, the suite of protocols, the standard, IPsec RFCs, IPsec history. Hands on Analysis of 'normal' IP packets. IPsec architecture The IPsec protocols, AH vs ESP, Why two headers? transport mode, tunnel mode, Remote access VPNs, site to site VPNs, security associations, SA database, Security Parameters Index, implementations: Host tack, Bump in the Stack, Bump in the Wire. Hands on Configuring IPsec. AH What AH does, the stack, The AH header, What is authenticated? Device authentication. AH in transport mode, AH in tunnel mode. Hands on AH packet analysis. ESP What ESP does, the ESP header, ESP in transport mode, ESP in tunnel mode, ESP and SA, ESP and SPI. Hands on ESP packet analysis, policy configuration. IPsec encryption IPsec is a framework, standard algorithms, ESP keys, the role of IKE, key lifetimes, how IKE generates the keys, DES, 3DES, AES, cipher block chaining, counter mode, other encryption. Hands on Encryption configuration. IPsec authentication Authentication types, IPsec authentication, Authentication algorithms: MD5, keyed SHA-1, HMAC-MD5, HMAC-SHA-1, HMAC-RIPEMD, other authentication algorithms. Hands on Authentication configuration. IKE Internet Key Exchange, IKE and the SAD, the two phase negotiation, ISAKMP, ISAKMP header, pre shared keys, digital signatures, public key encryption, Diffie Hellman, proposals, counter proposals, nonces, identities, phase 1 negotiation: main mode, aggressive mode, base mode. Phase 2 negotiation: quick mode, new group mode. Hands on IKE packet analysis. More IKE PFS, IKE and dynamic addresses, XAUTH, hybrid authentication, CRACK, ULA, PIC. User level authentication. IKE renegotiation, heartbeats. Hands on Troubleshooting IPsec. IKEv2 The IKEv2 exchange, IKE_SA_INIT, IKE_AUTH, CREATE_CHILD_SA, IKEv2 packets, the informational exchange. Comparing IKev1 vs IKE v2. Hands on IKEv2 configuration and analysis. PKI What is PKI?, Digital certificates, Certificate authorities, CA servers, RA, VA, certificates, CA hierarchy, CRLs, certificate formats. Hands on installing and configuring certificate servers. IPsec issues NAT, IPsec overhead and fragmentation. Summary IPsec strengths and weaknesses. Where to get further information.

Business Audit - Assessing Your Systems, Operations, Finances, Marketing & Sales
By Dan Roberts
In this half-day virtual 1-2-1 session with Dan – you will have your coaching business analysed and dissected by Dan. After a comprehensive Q&A, which will be completed before the day, Dan will honestly discuss the strengths, weaknesses and opportunities for each of the key ‘business’ aspects of your coaching business. This includes looking at all your systems (or where there should be systems), operational management, Finances (including cash flow, accounts and budgeting) KPIs, Marketing plans, referral systems and any Sales funnels. His advice will align with your ambitions and will give you the practical insights, unpleasant truth bombs and encouragement you need to have a healthy, thriving business.
An Introduction to Emotional Intelligence at Work
By Workplace Innovation Europe
This CPD accredited short course is for everyone who wants to work more effectively with their collaeagues. It will help strengthen personal competencies including listening and communication, understanding and engaging with different perspectives, and working together to create a positive culture in the office or on the shopfloor.

Navigating The Modern Workforce - Diversity, Culture, Generations
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Team leaders, managers, executives and other business professionals who lead others will benefit from this course. Overview Learn to lead in a world of diversity Engage and empower our multi-generational workforce Leverage culture as the new strategic differentiator Develop your path to leadership success In this course, students will learn how to capitalize on the strengths of your diverse team while directing and guiding them to even greater achievements. Private classes on this topic are available. We can address your organization?s issues, time constraints, and save you money, too. Contact us to find out how. 1. A Complex World of Diversity Working in Fluid Dynamic Environments Understanding the New Transient Workforce Addressing the Need for a New Type of Leadership Leading with Authenticity Developing Required Skills and Competencies Decentralizing Power 2. Making Difference Your Strategic Advantage Engaging in the 21st Century Measuring Engagement and Taking Advantage of High Engagement Overcoming Challenges to Employee Engagement Embracing Difference and Bridging Boundaries Developing Cultural Intelligence and Responding Effectively to Cultural Differences Applying SCARF to Direct Behavior 3. Leveraging Change as the New Normal Understanding and Applying Emotional Intelligence Motivating Others Key Areas of Interest - Behavioral and Cognitive, Psychodynamic and Humanistic, and Personality Types Developing Your Leadership Psychological Toolkit Identifying Drivers - Desires and Expectations The Impact of an Environment of Trust Meeting the Needs of the Social Brain Promoting Involvement 4. Creating Leaders for the Future Facing the Challenges of a Modern Leader Avoiding Cultural Pitfalls Creating a Common Culture for All Leading Fluid Teams Seeking Diverse Perspectives Soliciting Feedback Utilizing Various Leadership Styles - Storytelling, Adaptive, and Connective Building a Sustainable Vision, Developing a Path, and Creating a Passion for Excellence Additional course details: Nexus Humans Navigating The Modern Workforce - Diversity, Culture, Generations training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Navigating The Modern Workforce - Diversity, Culture, Generations course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Cyber security training course description This cyber security course focusses on the network side of security. Technologies rather than specific products are studied focussing around the protection of networks using firewalls and VPNs. What will you learn Describe: - Basic security attacks - RADIUS - SSL - VPNs Deploy firewalls and secure networks Explain how the various technologies involved in an IP VPN work. Describe and implement: - L2TP - IPsec - SSL - MPLS, L3, VPNs. Cyber security training course details Who will benefit: Anyone working in the security field. Prerequisites: TCP/IP foundation for engineers Duration 5 days Cyber security training course contents Security review Denial of service, DDOS, data manipulation, data theft, data destruction, security checklists, incident response. Security exploits IP spoofing, SYN attacks, hijacking, reflectors and amplification, keeping up to date with new threats. Hands on port scanning, use a 'hacking' tool. Client and Server security Windows, Linux, Log files, syslogd, accounts, data security. Hands on Server hardening. Firewall introduction What is a firewall? Firewall benefits, concepts. HAnds on launching various attacks on a target. Firewall types Packet filtering, SPI, Proxy, Personal. Software firewalls, hardware firewalls. Firewall products. Hands on Simple personal firewall configuration. Packet filtering firewalls Things to filter in the IP header, stateless vs. stateful filtering. ACLs. Advantages of packet filtering. Hands on Configuring packet filtering firewalls. Stateful packet filtering Stateful algorithms, packet-by-packet inspection, application content filtering, tracks, special handling (fragments, IP options), sessions with TCP and UDP. Firewall hacking detection: SYN attacks, SSL, SSH interception. Hands on SPI firewalls. Proxy firewalls Circuit level, application level, SOCKS. Proxy firewall plusses and minuses. Hands on Proxy firewalls. Firewall architectures Small office, enterprise, service provider, what is a DMZ? DMZ architectures, bastion hosts, multi DMZ. Virtual firewalls, transparent firewalls. Dual firewall design, high availability, load balancing, VRRP. Hands on Resilient firewall architecture. Testing firewalls Configuration checklist, testing procedure, monitoring firewalls, logging, syslog. Hands on Testing firewalls. Encryption Encryption keys, Encryption strengths, Secret key vs Public key, algorithms, systems, SSL, SSH, Public Key Infrastructures. Hands on Password cracking. Authentication Types of authentication, Securid, Biometrics, PGP, Digital certificates, X.509 v3, Certificate authorities, CRLs, RADIUS. Hands on Using certificates. VPN overview What is a VPN? What is an IP VPN? VPNs vs. Private Data Networks, Internet VPNs, Intranet VPNs, Remote access VPNs, Site to site VPNs, VPN benefits and disadvantages. VPN Tunnelling VPN components, VPN tunnels, tunnel sources, tunnel end points, tunnelling topologies, tunnelling protocols, which tunnelling protocol? Requirements of tunnels. L2TP Overview, components, how it works, security, packet authentication, L2TP/IPsec, L2TP/PPP, L2 vs L3 tunnelling. Hands on Implementing a L2TP tunnel. IPsec AH, HMAC, ESP, transport and tunnel modes, Security Association, encryption and authentication algorithms, manual vs automated key exchange, NAT and other issues. Hands on Implementing an IPsec VPN. SSL VPNs Layer 4 VPNs, advantages, disadvantages. SSL. TLS. TLS negotiation, TLS authentication. TLS and certificates. Hands on Implementing a SSL VPN. MPLS VPNs Introduction to MPLS, why use MPLS, Headers, architecture, label switching, LDP, MPLS VPNs, L2 versus L3 VPNs. Point to point versus multipoint MPLS VPNs. MBGP and VRFs and their use in MPLS VPNs. Hands on Implementing a MPLS L3 VPN. Penetration testing Hacking webservers, web applications, Wireless networks and mobile platforms. Concepts, threats, methodology. Hands on Hacking tools and countermeasures.

Group Coaching Programme
By British School of Coaching
An intensive group coaching programme for qualified and certified coaches who want to add group coaching as an offer in their practice.

Thriving at Work: A Neurodivergent Perspective
By Emergent Learning
Target Audience This course is for people who are either neurodivergent or working with neurodivergent colleagues. It will help you work more effectively by understanding the needs and recognising the strengths of neurodivergence. This will help you develop strategies to support performance and enhance wellbeing in the workplace. Duration 1 Day Course Overview This course is designed for teams with neurodivergent professionals who want to better navigate work environments, build on their strengths, and manage friction in everyday tasks. Through practical tools, reflection, and real-life strategies, you'll gain greater clarity and confidence in how you work best — and how to advocate for what you need to thrive. Participants will explore a range of neurodivergent profiles and learn how to adapt communication, adjust workflows, reduce workplace triggers, and advocate for a fairer and more inclusive culture. This course is designed by highly qualified learning design experts, assisted and guided by a Doctoral & Masters level leadership team. Working closely with subject matter leaders with extensive domain experience, this course is built on sound scientific & academic rigour and applied real world experience. Run in a cohort-based, activity-led format, it goes beyond theory to provide practical methods and frameworks that you can immediately apply in your workplace. Course Objectives Recognise how neurodivergent traits shape focus, energy, and work patterns Develop strategies and adjustments that support strengths and reduce friction Communicate needs and preferences to improve collaboration and confidence High Level Topics Neurodiversity and Workplace Impact Working with Strengths and Challenges Strategies for Everyday Success

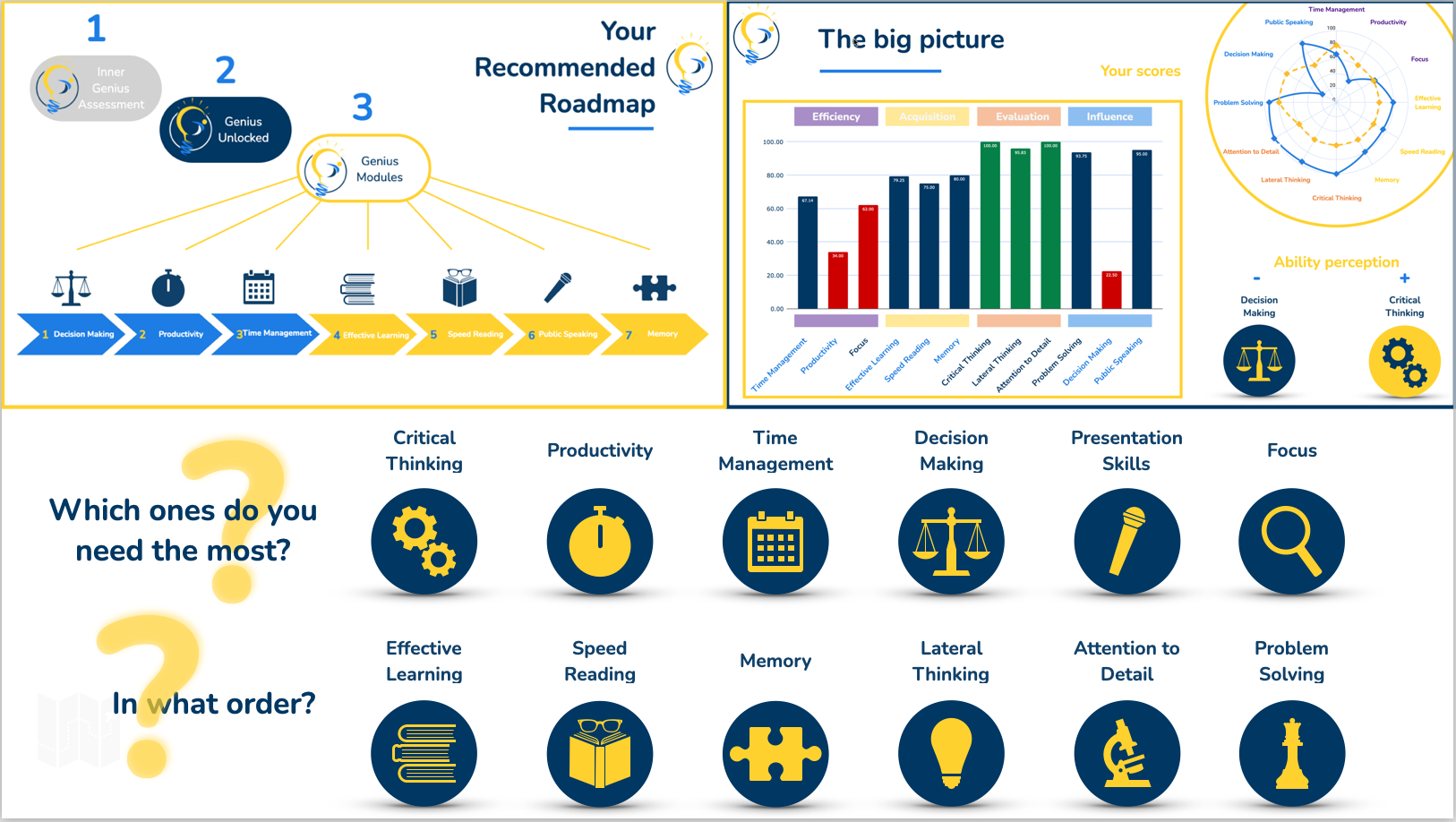
Cognitive Assessment
By inGeniusly
Prioritising and creating order is the first step towards your success. There may be some skills that are fundamental to your results, while others are not something you should focus your efforts on. The Inner Genius Assessment is the perfect tool for you to identify your own personal roadmap.