- Professional Development
- Medicine & Nursing
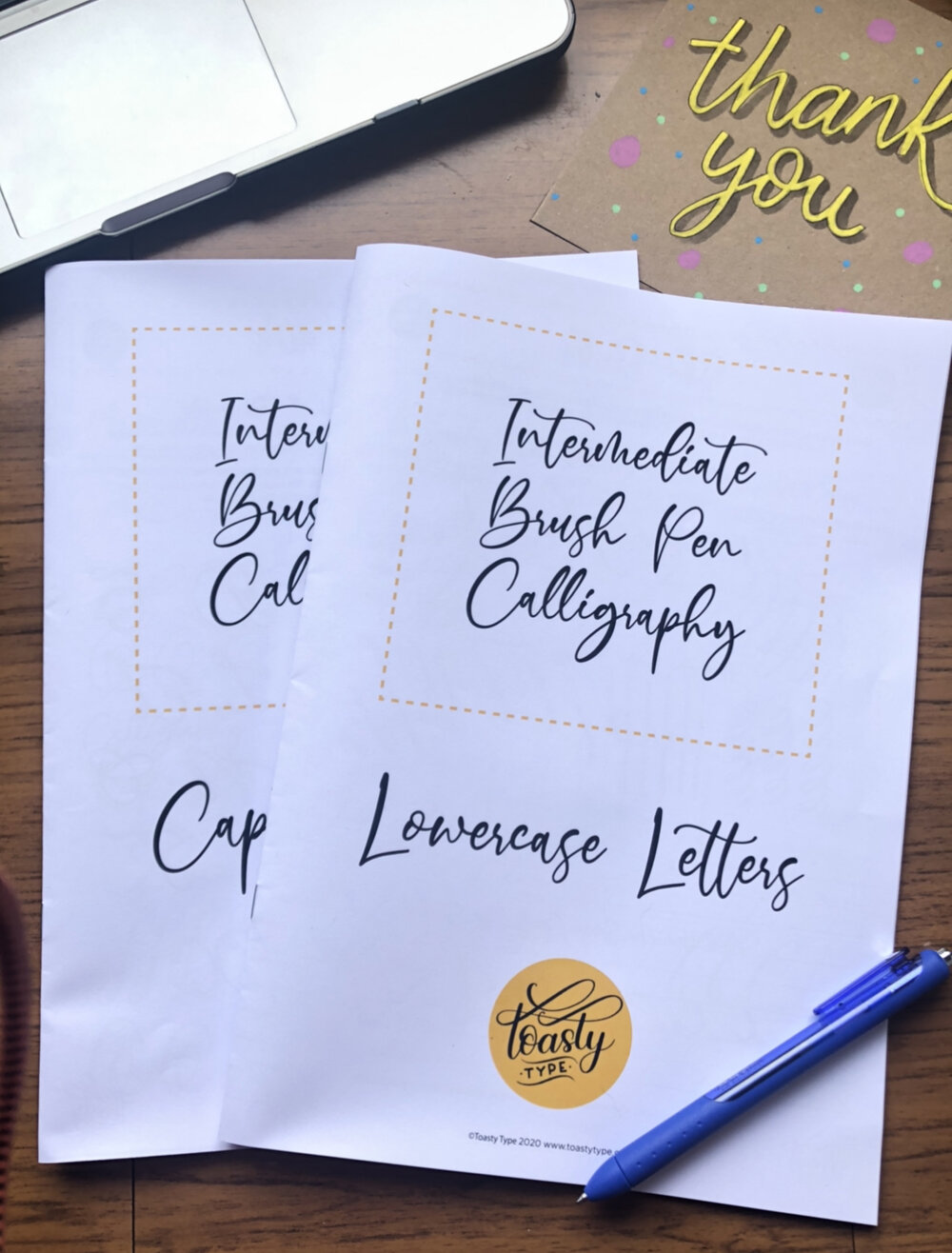
- Arts & Crafts
- Health & Wellbeing
- Personal Development
548 Courses in Cardiff delivered Live Online
Master Yourself in Talking with Strangers
By NextGen Learning
Master Yourself in Talking with Strangers Course Overview This course, Master Yourself in Talking with Strangers, is designed to empower learners with essential communication skills to confidently initiate and sustain conversations with unfamiliar people. It explores effective techniques to overcome social anxiety, build rapport quickly, and engage meaningfully in diverse social settings. Through structured guidance, learners will develop greater self-awareness and adaptability in interactions, enhancing their personal and professional relationships. By the end of the course, participants will be equipped with the tools to initiate conversations naturally, listen actively, and respond with confidence, making social interactions more rewarding and less daunting. Course Description Master Yourself in Talking with Strangers offers an in-depth exploration of the skills necessary to communicate effectively with new acquaintances. Topics include understanding body language, mastering conversation openers, managing nervousness, and cultivating empathy. Learners will engage with practical strategies for navigating different social contexts and recognising cues that facilitate connection. This course provides a supportive learning environment aimed at increasing social confidence and emotional intelligence. By completing this programme, participants will enhance their interpersonal skills, enabling smoother introductions, more engaging dialogues, and the ability to foster new relationships in both personal and professional spheres. Master Yourself in Talking with Strangers Curriculum Module 01: Course Overview Module 02: The Formula Module 03: Summary Module 04: End (See full curriculum) Who Is This Course For? Individuals seeking to improve their confidence in social interactions. Professionals aiming to enhance networking and communication skills. Beginners with an interest in developing interpersonal abilities. Anyone looking to overcome social anxiety and connect more easily with others. Career Path Customer Service Representative Sales and Marketing Executive Networking and Business Development Specialist Public Relations Officer Community Engagement Coordinator

"Self Care" - A Key To Happiness
By NextGen Learning
"Self Care" - A Key To Happiness Course Overview: "Self Care: A Key To Happiness" is a comprehensive course designed to provide learners with essential strategies and techniques to improve their well-being and mental health. Focusing on the importance of self-care in maintaining happiness, this course equips participants with practical tools to manage stress, set boundaries, and enhance their emotional resilience. It explores various self-care practices, including mindfulness, relaxation techniques, and the significance of a balanced lifestyle. By the end of the course, learners will gain the ability to integrate self-care into their daily routines, leading to increased overall happiness, productivity, and life satisfaction. Course Description: This course delves deeper into the concept of self-care, exploring the connection between mental and physical health. Participants will learn effective methods for self-awareness, stress management, and emotional well-being. Key topics include mindfulness practices, relaxation exercises, understanding emotional triggers, and cultivating a positive mindset. The course also examines the role of nutrition, sleep, and exercise in maintaining a balanced and happy life. Learners will be guided on how to create personalised self-care plans tailored to their unique needs, ensuring long-term success. Upon completion, students will have gained valuable skills in self-regulation, resilience-building, and sustainable happiness. "Self Care" - A Key To Happiness Curriculum: Module 01: About this Course Module 02: Full Course Module 03: Next Steps Module 04: Extra Content for YOU (See full curriculum) Who is this course for? Individuals seeking to enhance their well-being and happiness Professionals aiming to improve their stress management and mental resilience Beginners with an interest in mental health and self-care Those seeking balance and mindfulness in their daily lives Career Path Mental Health Support Worker Wellness Coach Health and Well-being Consultant Personal Development Trainer Employee Wellness Program Manager

Cisco ASA Essentials (ASAE)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Students who need to know how to implement and manage Cisco ASA 5500-X. Overview Upon successful completion of this course, students should be able to do the following:? Technology and features of the Cisco ASA? Cisco ASA product family? How ASAs protect network devices from attacks? Bootstrap the security appliance? Prepare the security appliance for configuration via the Cisco Adaptive Security Device Manager (ASDM)? Launch and navigate ASDM? Essential security appliance configuration using ASDM and the command-line interface (CLI)? Configure dynamic and static address translations? Configure access policy based on ACLs? Use object groups to simplify ACL complexity and maintenance? Use the Modular Policy Framework to provide unique policies to specific data flows? Handle advanced protocols with application inspection? Troubleshoot with syslog and tcp ping? Configure the ASA to work with Cisco Secure ACS 5.2 for RADIUS-based AAA of VPNs? Implement site-to-site IPsec VPN? Implement remote access IPsec and SSL VPNs using the Cisco AnyConnect 3.0 Secure Mobility Client? Work with the 5.x Legacy Cisco IPsec VPN client and Anyconnect VPN client? Deploy clientless SSL VPN access, including smart tunnels, plug-ins, and web-type ACLs? Configure access control policies to implement your security policy across all classes of VPN? Configure Active/Standby failover for both firewall and VPN high availability Student will gain the essential skills required to configure, maintain, and operate Cisco ASA 5500-X Series Adaptive Security Appliances based on ASA Software v9.x. Cisco ASA Essentials ? Lesson 1: Evaluating Cisco ASA Technologies ? Lesson 2: Identifying Cisco ASA Families Basic Connectivity and Device Management ? Lesson 1: Preparing the Cisco ASA for Network Integration ? Lesson 2: Managing Basic Cisco ASA Network Settings ? Lesson 3: Configuring Cisco ASA Device Management Features Network Integration ? Lesson 1: Configuring Cisco ASA NAT Features ? Lesson 2: Configuring Cisco ASA Basic Access Control Features Cisco ASA Policy Control ? Lesson 1: Cisco ASA Modular Policy Framework ? Lesson 2: Configuring Cisco ASA Connection Policy Cisco ASA VPN Architecture and Common Components ? Lesson 1: Implementing Profiles, Group Policies, and User Policies ? Lesson 2: Implementing PKI Services Cisco ASA Clientless Remote Access SSL VPN Solutions ? Lesson 1: Deploying Basic Clientless VPN Solutions ? Lesson 2: Deploying Advanced Application Access for Clientless SSL VPNs Cisco AnyConnect Remote Access SSL Solutions ? Lesson 1: Deploying a Basic Cisco AnyConnect Full-Tunnel SSL VPN Solution Cisco ASA Remote Access IPsec VPNs ? Lesson 1: Deploying Cisco Remote Access VPN Clients ? Lesson 2: Deploying Basic Cisco Remote Access IPsec VPN Solutions Cisco ASA Site-to-Site IPsec VPN Solutions ? Lesson 1: Deploying Basic Site-to-Site IPsec VPNs ? Lesson 2: Deploying Advanced Site-to-Site IPsec VPNs Cisco ASA High Availability and Virtualization ? Lesson 1: Configuring Cisco ASA Active/Standby High Availability Labs Lab 1: Prepare the ASA for Administration Lab 2: Fundamental ASA Configuration Lab 3: Network Address Translation (NAT) Lab 4: Basic Access Control Lab 5: Basic Protocol Inspection Lab 6: Licensing, ACS, and Public CA Lab 7: Basic Clientless SSL VPN Lab 8: Clientless SSL VPN - Thin Apps Lab 9: Basic AnyConnect Full Tunnel SSL VPN Lab 10: Remote Access IPSec VPN Lab 11: IPSec Site-to-Site VPN Lab 12: Active/Standby Failover

VMware Horizon 8: Virtual Desktop Troubleshooting
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Experienced system operators, administrators, and integrators responsible for managing and maintaining VMware Horizon solutions Overview By the end of the course, you should be able to meet the following objectives: Implement a structured approach to troubleshooting Resolve common issues that occur in a VMware Horizon environment Troubleshoot issues with linked and instant clones Configure the Windows client Identify the correct log level for gathering logs Optimize protocols for best end-user experience This two-day course builds your skills in resolving common issues that occur in a VMware Horizon© environment. You engage in a series of lab exercises to bring existing environment issues to resolution. The exercises mirror real-world troubleshooting use cases. These exercises equip learners with the knowledge and practical skills to manage typical challenges faced by virtual desktop administrators and operators. Course Introduction Introductions and course logistics Course objectives Overview of Virtual Desktop Troubleshooting Structured approach to troubleshooting configuration and operational problems Applying troubleshooting methods Documenting the steps to resolving the problem Command-Line Tools and Backup Options Using command-line tools Backing-up and restoring VMware Horizon databases Troubleshooting Horizon Linked Clone Desktops Describe the components that make up a VMware Horizon desktop Explain how the View Agent Direct-Connection plug-In is useful for diagnosing problems Highlight the best practice for optimizing a VMware Horizon desktop Troubleshoot common problems with VMware Horizon desktops Troubleshooting Instant Clone Discuss how instant clones are created Discuss what gets logged when an instant clone is created Discuss the keywords to look for in the logs when troubleshooting instant clones Discuss how to troubleshoot problems with instant clones Windows Client Correctly configure the Windows Client Identify the correct log level for gathering logs Enable the required SSL configuration level for the environment Ports and Protocols Discuss the key ports on a Horizon Environment Discuss protocols used in the Horizon Environment Understand the benefit of optimizing Blast Become familiar with the optimization features for Blast Implement GPO changes for Blast Become familiar with the causes for Black Screens Discuss how to troubleshoot Black Screen problems Identify problems encountered when applying GPOs Discuss how to troubleshoot GPO-related problems Additional course details:Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware Horizon 8: Virtual Desktop Troubleshooting training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware Horizon 8: Virtual Desktop Troubleshooting course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

VMware App Volumes and Dynamic Environment Manager: Configure and Manage
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for Operators, administrators, and architects for VMware Horizon who are responsible for the creation, maintenance, and delivery of remote and virtual desktop services Overview By the end of the course, you should be able to meet the following objectives: Describe the features, functions, and architecture of App Volumes Create and deliver application packages in App Volumes Deliver App Volumes published applications to virtual desktops and on-demand, using Horizon Run the App Volumes Application Capture Command-Line Program using appcapture.exe Perform advanced configuration of App Volumes Scale App Volumes to multiple locations and sites Describe the features, functions, and architecture of VMware Dynamic Environment Manager Manage application configurations, user environment settings, and personalization settings using VMware Dynamic Environment Manager Create predefined configurations for applications by using the Application Profiler Create predefined configurations for applications by using the Application Profiler Manage multiple environments using VMware Dynamic Environment Manager. Enable and synchronize the offline use of VMware Dynamic Environment Manager by using SyncTool Using VMware Horizon Smart Policies on the VMware Horizon platform This three-day course builds your skills in application management with VMware App Volumes? and VMware Dynamic Environment Manager?. You learn how to use App Volumes to deliver applications and data to desktops and users in seconds and at scale. You gain skills in managing application life cycles across installation, update, and replacement. You also learn how to use VMware Dynamic Environment Manager to provide personalization and dynamic policy configuration across virtual, physical, and cloud-based environments to simplify end-user profile management. Course Introduction Introductions and course logistics Course objectives Overview of App Volumes Explain features and benefits of App Volumes Identify benefits of VMware ThinApp© Identify App Volumes components and architecture Manage application management stages using App Volumes. Working with Application Packages Differentiate between Application, Package and Program Create an Application Package Assign an Application to an entity Use markers to assign the new version of an Application Package Differentiate between Classic and On-Demand delivery of applications Update an Application with a new Package Published Applications Identify the benefits of delivering Published Applications On-Demand List the steps and prerequisites for creating Published Applications on Demand Integrate Horizon Connection Server and App Volumes Manager Associate App Volumes Manager with an automated farm Add Application Pools from App Volumes Manager Advanced App Volumes Configuration Perform advanced configuration of App Volumes Scale App Volumes to multiple locations and sites Run the App Volumes Application Capture Command-Line Program using appcapture.exe Overview of VMware Dynamic Environment Manager Explain features and benefits of Dynamic Environment Manager Identify the components of Dynamic Environment Manager architecture Differentiate between user profile scenarios Management Console User Interface Configure Personalization settings Create Condition sets Perform Application migration Configure User environment settings Advanced Dynamic Environment Manager Configuration Scale Dynamic Environment Manager to multiple locations and sites Use Silos Run the App Volumes Application Capture Command-Line Program using appcapture.exe Application Configuration Management Predefined and user-customized application settings Using Application Profiler Privilege Elevation SyncTool Identify the features of SyncTool Implement SyncTool VMware Horizon Smart Policies Identify the scope of Horizon Smart Policies Configure Horizon Smart Policies settings Define Smart Policies Conditions

Symantec ProxySG 6.6 Basic Administration (BCCPA)
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for The ProxySG 6.6 Basic Administration course is intended for students who wish to master the fundamentals of the ProxySG. It is designed for students who have not taken any previous training courses about the ProxySG. Overview Describe the major Secure Web Gateway functions of the ProxySG.License and configure a ProxySG.Deploy a ProxySG in either explicit or transparent mode.Use the Visual Policy Manager to write policies to manage web filtering, authentication, and SSL traffic management.Use ProxySG access logs to generate reports. The ProxySG 6.6 Basic Administration course is an introduction to deployment options and management of the individual key features offered using the ProxySG 6.6 solution. Introduction to the Symantec ProxySG Secure Web Gateway Describe the functions of a proxy server Differentiate proxy servers from firewalls Describe the key features and benefits of the ProxySG List the various ProxySG models Access online Symantec community resources ProxySG Security Deployment Options Describe the three network deployment methods Describe the three possible roles of the ProxySG ProxySG Management Console Describe the relationship between the Management Console and the ProxySG CLI Describe the primary function of the major areas of the Management Console Use the Management Console to access on-box help and Symantec product documentation Traffic Interception Using Proxy Services Understand the functions of proxy services, listeners, and proxy types Describe the three most common proxy services Explain how the intercept and bypass settings affect what happens to network traffic passing through the ProxySG Explain the function of common global proxy service settings Hypertext Transfer Protocol Understand how a connection is initiated over the transport layer Identify the components of an HTTP URL Explain the two types of HTTP messages: request and response Identify common response codes Introduction to the Visual Policy Manager Describe the relationship among the VPM, CPL, and the Management Console Describe the default processing order for policy layers and rules Describe triggers and actions that can be used in writing policy Identify the types of objects that the VPM supports Describe some of the best practices to be followed when using the VPM to create policy Filtering Web Content Describe the main concepts of web filtering Describe the primary category databases Describe the category types available to policy Describe how WebFilter and WebPulse work together Using Threat Intelligence to Defend the Network Understand Intelligence Services as provided by the Global Intelligence Network Understand Geolocation and Threat Risk Levels and how they can be used in policy Ensuring Safe Downloads Describe how malware can be transmitted via HTTP Explain the methods, advantages, and disadvantages of file type detection Describe some of the considerations in deciding what content to block as possible malware sources Notifying User of Internet Usage Policies Explain the function and various components of built-in and custom exception pages Describe the function of Notify User objects Identify the types of pages that can be sent to users by using Notify User objects Describe splash pages and coaching pages using Notify User objects in the VPM Access Logging on the ProxySG Describe, at a high level, how the ProxySG performs access logging Describe the components of a ProxySG access log facility Identify default log facilities and log formats Describe common use cases for periodic and continuous uploading of access logs

Aruba Networks - Implementing Aruba Campus Switching Solutions, Rev. 17.41 (IACSS)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Typical candidates for this course are IT Professionals who will deploy and manage networks based on HPE?s ArubaOS-Switches. Overview Upon completion of this course, students will be able to: Implement spanning tree protocol and loop protections Ensure redundancy for a network?s default gateway by configuring VRRP on Aruba switches Implement and manage an VSF fabric Deploy ArubaOS switches in single-area and multi-area OSPF systems Use Internet Group Management Protocol (IGMP) to optimize forwarding of multicasts within VLANs Implement PIM-DM to route multicast traffic Establish and monitor BGP sessions between your routers and ISP routers Define ACLs and identify the criteria by which ACLs select traffic Configure ACLs on ArubaOS switches to select given traffic Implement 802.1X on ArubaOS switch ports Configure captive portal authentication on ArubaOS switches to integrate them with an Aruba ClearPass solution Configure tunneled-node on ArubaOS switches Configure ArubaOS switches to select traffic, apply the appropriate QoS marking, and place the traffic in the proper priority queues Implement DHCP snooping and ARP protection to defend networks against DHCP exploits, ARP snooping, and ARP poisoning attacks Implement the proper port security measures for various use cases Implement connection rate filtering to provide a first layer of protection against viruses and worms This course teaches students how to implement and operate enterprise-level Aruba campus switching solutions. Hand-on labs gives students experience with ArubaOS-Switches, including securing access, redundancy technologies such as Multiple Spanning Tree Protocol (MSTP), link aggregation techniques including Link Aggregation Protocol (LACP) and switch virtualization with HPE?s Virtual SwitchingFramework (VSF). Students will also learn to configure dynamic routing with Open Shortest Path First (OSPF) and Border Gateway Protocol (BGP), network optimization via Quality of Service (QoS), IP multicast routing leveraging Protocol Independent Multicast (PIM), and protecting the network using Access Control Lists (ACLs). This course is approximately 30% lecture and 70% hands on lab exercises. Introduction to Aruba SolutionsData Link Layer Redundancy TechnologiesVirtual Router Redundancy Protocol (VRRP)Aruba Backplane Stacking and Advanced Virtual Switch Framework (VSF)Advanced Open Shortest Path First (OSPF)Internet Group Management Protocol (IGMP)Border Gateway Protocol (BGP)Access Control Lists (ACLs)MAC AuthenticationCaptive Portal and Other Guest OptionsIntegrating with Aruba Mobility SolutionsSecure Device ManagementQuality of Service (QoS)Additional Security Features Additional course details: Nexus Humans Aruba Networks - Implementing Aruba Campus Switching Solutions, Rev. 17.41 (IACSS) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Aruba Networks - Implementing Aruba Campus Switching Solutions, Rev. 17.41 (IACSS) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Ayurveda Diploma
By NextGen Learning
Course Overview The Ayurveda Diploma course offers a comprehensive exploration into the ancient science of natural healing and holistic wellbeing. Learners will gain a deep understanding of Ayurvedic principles, healing methods, medicinal herbs, and lifestyle practices that promote health and balance. This course emphasises the timeless relevance of Ayurveda in modern living, introducing key concepts such as daily routines, diet, exercise, and herbal remedies. Designed to enrich personal wellbeing or enhance professional skills, the course delivers valuable knowledge on preventive health measures through Ayurvedic lifestyle guidance. By the end of the programme, learners will be well-equipped to apply Ayurvedic principles to daily life, advise on basic remedies, and pursue further study or career opportunities within the holistic health sector. The Ayurveda Diploma not only provides theoretical knowledge but also nurtures a mindful approach towards health and self-care, empowering individuals to make informed wellness choices for themselves and others. Course Description The Ayurveda Diploma delves into the fundamental theories and practices of Ayurveda, offering a structured introduction to its core concepts. Throughout the course, learners will explore Ayurvedic healing methods, the role of herbs and oils, daily routines, yogic practices, and dietary guidelines rooted in traditional wisdom. Each module is carefully designed to build a comprehensive understanding of how Ayurveda views the mind-body connection and the pathways to maintaining balance and vitality. Participants will discover how to identify common ailments and understand the herbal remedies used within Ayurvedic practice, as well as the principles behind creating a healthful kitchen and lifestyle. The course provides an engaging and enriching learning experience, supported by clear explanations and accessible content, making it ideal for individuals at all levels of prior knowledge. Upon completion, learners will have developed a broad skill set that can support further professional development or enhance personal wellbeing initiatives. Course Modules Module 01: Introduction to Ayurveda Module 02: An Overview of Ayurvedic Healing Methods Module 03: Medicinal Herbs and Remedies for Common Ailments Module 04: Daily routines, Exercise & Yoga Module 05: Ayurvedic Herbs & Oils Module 06: Herbal Remedies for Home Use Module 07: The Herbal Kitchen Module 08: Ayurvedic Dietary Guidelines Module 09: Ayurvedic Lifestyle: The Ultimate Preventive Medicine (See full curriculum) Who is this course for? Individuals seeking to enhance their knowledge of natural health and wellbeing. Professionals aiming to broaden their expertise in holistic health practices. Beginners with an interest in Ayurveda, herbal medicine, or wellness sectors. Health enthusiasts looking to incorporate traditional healing methods into modern living. Career Path Ayurvedic Wellness Advisor Holistic Health Consultant Health and Wellness Coach Complementary Therapy Practitioner Herbal Remedy Specialist Lifestyle and Nutrition Consultant

Cisco Securing Networks with Cisco Firepower Next Generation Firewall v1.0 (SSNGFW)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Security administrators Security consultants Network administrators System engineers Technical support personnel Cisco integrators and partners Overview After taking this course, you should be able to: Describe key concepts of NGIPS and NGFW technology and the Cisco Firepower Threat Defense system, and identify deployment scenarios Perform initial Cisco Firepower Threat Defense device configuration and setup tasks Describe how to manage traffic and implement Quality of Service (QoS) using Cisco Firepower Threat Defense Describe how to implement NAT by using Cisco Firepower Threat Defense Perform an initial network discovery, using Cisco Firepower to identify hosts, applications, and services Describe the behavior, usage, and implementation procedure for access control policies Describe the concepts and procedures for implementing security intelligence features This course gives you knowledge and skills to use and configure Cisco© Firepower Threat Defense technology, beginning with initial device setup and configuration and including routing, high availability, Cisco Adaptive Security Appliance (ASA) to Cisco Firepower Threat Defense migration, traffic control, and Network Address Translation (NAT). You will learn how to implement advanced Next-Generation Firewall (NGFW) and Next-Generation Intrusion Prevention System (NGIPS) features, including network intelligence, file type detection, network-based malware detection, and deep packet inspection. You will also learn how to configure site-to-site VPN, remote-access VPN, and Secure Sockets Layer (SSL) decryption before moving on to detailed analysis, system administration, and troubleshooting. Cisco Firepower Threat Defense Overview Examining Firewall and IPS Technology Firepower Threat Defense Features and Components Examining Firepower Platforms Examining Firepower Threat Defense Licensing Cisco Firepower Implementation Use Cases Cisco Firepower NGFW Device Configuration Firepower Threat Defense Device Registration FXOS and Firepower Device Manager Initial Device Setup Managing NGFW Devices Examining Firepower Management Center Policies Examining Objects Examining System Configuration and Health Monitoring Device Management Examining Firepower High Availability Configuring High Availability Cisco ASA to Firepower Migration Migrating from Cisco ASA to Firepower Threat Defense Cisco Firepower NGFW Traffic Control Firepower Threat Defense Packet Processing Implementing QoS Bypassing Traffic Cisco Firepower NGFW Address Translation NAT Basics Implementing NAT NAT Rule Examples Implementing NAT Cisco Firepower Discovery Examining Network Discovery Configuring Network Discovery Implementing Access Control Policies Examining Access Control Policies Examining Access Control Policy Rules and Default Action Implementing Further Inspection Examining Connection Events Access Control Policy Advanced Settings Access Control Policy Considerations Implementing an Access Control Policy Security Intelligence Examining Security Intelligence Examining Security Intelligence Objects Security Intelligence Deployment and Logging Implementing Security Intelligence File Control and Advanced Malware Protection Examining Malware and File Policy Examining Advanced Malware Protection Next-Generation Intrusion Prevention Systems Examining Intrusion Prevention and Snort Rules Examining Variables and Variable Sets Examining Intrusion Policies Site-to-Site VPN Examining IPsec Site-to-Site VPN Configuration Site-to-Site VPN Troubleshooting Implementing Site-to-Site VPN Remote-Access VPN Examining Remote-Access VPN Examining Public-Key Cryptography and Certificates Examining Certificate Enrollment Remote-Access VPN Configuration Implementing Remote-Access VPN SSL Decryption Examining SSL Decryption Configuring SSL Policies SSL Decryption Best Practices and Monitoring Detailed Analysis Techniques Examining Event Analysis Examining Event Types Examining Contextual Data Examining Analysis Tools Threat Analysis System Administration Managing Updates Examining User Account Management Features Configuring User Accounts System Administration Cisco Firepower Troubleshooting Examining Common Misconfigurations Examining Troubleshooting Commands Firepower Troubleshooting