- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
384 Courses in Cardiff delivered Live Online
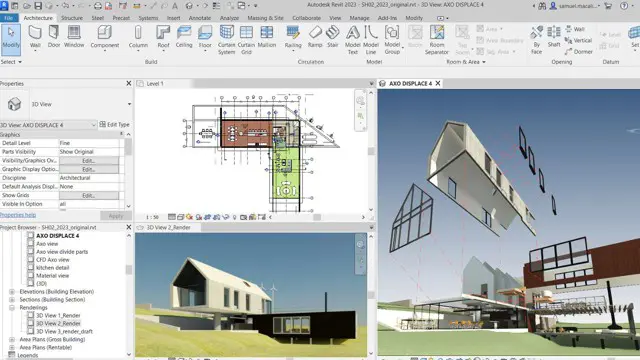
Revit MEP Training for 15 hours - Live and Online
By FirstScale Revit Consultant and Training
The Revit MEP course (£525), offers you individual learning (One to One) to improve your skills in Revit, and this course extends to 15 hours.

AutoCAD Essentials
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for This course is intended for individuals who want to gain basic and intermediate knowledge of working on AutoCAD Overview Upon successful completion of this course, students will be able to create basic and intermediate drawings utilizing the AutoCAD software In this course, you will learn to navigate the AutoCAD user interfaces and use the fundamental features of AutoCAD. You will learn to use the precision drafting tools in AutoCAD to develop accurate technical drawings. Utilizing the AutoCAD Software Startup Screen The Application Menu The AutoCAD User Interface AutoCAD Options [OP] Saving the Drawing ?Places? for Quicker Access of Drawings Wheel Mouse Tidbits The Governing Body of Workspaces Ribbon Management Layer Properties Manager Assigning a Linetype to a New Layer Off vs. Freeze Practical Features of Layer Walk Creating a Layer State Freezing Individual Layers with Layer Freeze Layer Lock Creating Drawings with AutoCAD Accuracy Measuring a Distance Measuring an Area Creating Basic Objects Object Selection Options Basic Editing Commands Polar Tracking Editing Polylines Variable Width Polyline Command Aliases Move and Copy with ?CTRL? Customizing Rollover Tooltips Cycle Through Stacked Objects Additional Selection Options Stretch Midpoint Between Two Points [M2P] Snap From Hatch Stuff Additional course details: Nexus Humans AutoCAD Essentials training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the AutoCAD Essentials course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Rhino 3D Evening Training
By London Design Training Courses
Who Should Attend Rhino 3D Evening Training Course? Click here for info. This Evening Course is for individuals seeking to learn 2D and 3D modeling skills in a supportive and creative learning environment. Whether you are new to Rhino or want to expand your existing knowledge, this course is for product, furniture, architectural, and jewelry design industries. Duration: 10 hrs Method: 1-on-1, Personalized attention Schedule: Tailor your own schedule hours of your choice, available from Mon to Sat between 9 am and 7 pm Course Inclusions: Free Lifetime email support: Enjoy the flexibility of a free lifetime email support. Expert Instruction: Learn from experienced architects, designers, and software professionals, ensuring top-notch teaching. Hands-On Learning: Engage in practical, hands-on lessons with personalized project work to apply your skills effectively. Digital Reference: Access valuable video tutorials and a digital reference book for convenient revision and continuous development. London Design Training Course Certificate of Completion: Receive a certificate upon course completion, enhancing your CV and LinkedIn profile. Free Career Guidance: Benefit from career guidance, including tips on job applications and setting up a creative business, to stand out in the competitive design industry. Rhino 3D Basic to Intermediate Training Course Course Duration: 10 hours Introduction to Rhino and Interface: Familiarizing with Rhino's command system and toolbar usage. Navigating the geometry menus, command line, and status bar efficiently. Understanding the Properties window and its functionalities. Managing file operations, including opening and saving files. Grasping the three entity types: curves, surfaces, and solids. Exploring various geometric elements, such as Bezier curves, B-splines, NURBS objects, isocurve surfaces, and mesh surfaces. Setting measurement units for accurate modeling. Navigation: Introducing the viewport and its features. Using construction planes to aid in modeling. Utilizing shading modes for better visualization. Learning essential viewport controls: pan, zoom, rotate, and reset. Workflow Basics: Creating basic objects like curves, surfaces, and solids. Performing fundamental transformations to manipulate objects. Organizing projects efficiently using layers. Drawing: 2D Geometry: Understanding the creation of lines, polylines, rectangles, polygons, arcs, circles, and ellipses. Drawing freeform curves for more creative designs. Modeling: 3D Surfaces: Comparing various 3D surface types. Utilizing extrusion to add features to models. Creating surfaces with loft, revolve, rail revolve, sweep rail, and network surface commands. Constructing complex surfaces with the Network Surface tool. Modeling: 3D Solids: Introducing solid modeling techniques. Creating solids with primitives and curves. Applying Boolean operators to create unique shapes. Editing solids using the solid edit tool. Transforming solids and incorporating modeling aids like Grid Snap, Ortho, and Planar. Editing and Transforming Objects: Using Fillet and Chamfer to edit corners. Employing curve Booleans for trimming and splitting. Mastering the Drag and Nudge tools for object movement and rotation. Copying, pasting, and grouping objects effectively. Scaling and duplicating objects with the Mirror command. Analysis and Degrees: Understanding degrees of curves and surfaces. Creating screen captures for quick proofs. Generating 2D views and rendering projects. Preparation for 3D Printing and Manufacturing: Preparing models for prototyping by ensuring closed gaps. Using the shell technique to create wall thickness suitable for 3D printing.

SC-200T00 Microsoft Security Operations Analyst
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The Microsoft Security Operations Analyst collaborates with organizational stakeholders to secure information technology systems for the organization. Their goal is to reduce organizational risk by rapidly remediating active attacks in the environment, advising on improvements to threat protection practices, and referring violations of organizational policies to appropriate stakeholders. Responsibilities include threat management, monitoring, and response by using a variety of security solutions across their environment. The role primarily investigates, responds to, and hunts for threats using Microsoft Sentinel, Microsoft Defender for Cloud, Microsoft 365 Defender, and third-party security products. Since the Security Operations Analyst consumes the operational output of these tools, they are also a critical stakeholder in the configuration and deployment of these technologies. Learn how to investigate, respond to, and hunt for threats using Microsoft Sentinel, Microsoft Defender for Cloud, and Microsoft 365 Defender. In this course you will learn how to mitigate cyberthreats using these technologies. Specifically, you will configure and use Microsoft Sentinel as well as utilize Kusto Query Language (KQL) to perform detection, analysis, and reporting. The course was designed for people who work in a Security Operations job role and helps learners prepare for the exam SC-200: Microsoft Security Operations Analyst. Prerequisites Basic understanding of Microsoft 365 Fundamental understanding of Microsoft security, compliance, and identity products Intermediate understanding of Windows 10 Familiarity with Azure services, specifically Azure SQL Database and Azure Storage Familiarity with Azure virtual machines and virtual networking Basic understanding of scripting concepts. 1 - Introduction to Microsoft 365 threat protection Explore Extended Detection & Response (XDR) response use cases Understand Microsoft Defender XDR in a Security Operations Center (SOC) Explore Microsoft Security Graph Investigate security incidents in Microsoft Defender XDR 2 - Mitigate incidents using Microsoft 365 Defender Use the Microsoft Defender portal Manage incidents Investigate incidents Manage and investigate alerts Manage automated investigations Use the action center Explore advanced hunting Investigate Microsoft Entra sign-in logs Understand Microsoft Secure Score Analyze threat analytics Analyze reports Configure the Microsoft Defender portal 3 - Protect your identities with Microsoft Entra ID Protection Microsoft Entra ID Protection overview Detect risks with Microsoft Entra ID Protection policies Investigate and remediate risks detected by Microsoft Entra ID Protection 4 - Remediate risks with Microsoft Defender for Office 365 Automate, investigate, and remediate Configure, protect, and detect Simulate attacks 5 - Safeguard your environment with Microsoft Defender for Identity Configure Microsoft Defender for Identity sensors Review compromised accounts or data Integrate with other Microsoft tools 6 - Secure your cloud apps and services with Microsoft Defender for Cloud Apps Understand the Defender for Cloud Apps Framework Explore your cloud apps with Cloud Discovery Protect your data and apps with Conditional Access App Control Walk through discovery and access control with Microsoft Defender for Cloud Apps Classify and protect sensitive information Detect Threats 7 - Respond to data loss prevention alerts using Microsoft 365 Describe data loss prevention alerts Investigate data loss prevention alerts in Microsoft Purview Investigate data loss prevention alerts in Microsoft Defender for Cloud Apps 8 - Manage insider risk in Microsoft Purview Insider risk management overview Create and manage insider risk policies Investigate insider risk alerts Take action on insider risk alerts through cases Manage insider risk management forensic evidence Create insider risk management notice templates 9 - Investigate threats by using audit features in Microsoft Defender XDR and Microsoft Purview Standard Explore Microsoft Purview Audit solutions Implement Microsoft Purview Audit (Standard) Start recording activity in the Unified Audit Log Search the Unified Audit Log (UAL) Export, configure, and view audit log records Use audit log searching to investigate common support issues 10 - Investigate threats using audit in Microsoft Defender XDR and Microsoft Purview (Premium) Explore Microsoft Purview Audit (Premium) Implement Microsoft Purview Audit (Premium) Manage audit log retention policies Investigate compromised email accounts using Purview Audit (Premium) 11 - Investigate threats with Content search in Microsoft Purview Explore Microsoft Purview eDiscovery solutions Create a content search View the search results and statistics Export the search results and search report Configure search permissions filtering Search for and delete email messages 12 - Protect against threats with Microsoft Defender for Endpoint Practice security administration Hunt threats within your network 13 - Deploy the Microsoft Defender for Endpoint environment Create your environment Understand operating systems compatibility and features Onboard devices Manage access Create and manage roles for role-based access control Configure device groups Configure environment advanced features 14 - Implement Windows security enhancements with Microsoft Defender for Endpoint Understand attack surface reduction Enable attack surface reduction rules 15 - Perform device investigations in Microsoft Defender for Endpoint Use the device inventory list Investigate the device Use behavioral blocking Detect devices with device discovery 16 - Perform actions on a device using Microsoft Defender for Endpoint Explain device actions Run Microsoft Defender antivirus scan on devices Collect investigation package from devices Initiate live response session 17 - Perform evidence and entities investigations using Microsoft Defender for Endpoint Investigate a file Investigate a user account Investigate an IP address Investigate a domain 18 - Configure and manage automation using Microsoft Defender for Endpoint Configure advanced features Manage automation upload and folder settings Configure automated investigation and remediation capabilities Block at risk devices 19 - Configure for alerts and detections in Microsoft Defender for Endpoint Configure advanced features Configure alert notifications Manage alert suppression Manage indicators 20 - Utilize Vulnerability Management in Microsoft Defender for Endpoint Understand vulnerability management Explore vulnerabilities on your devices Manage remediation 21 - Plan for cloud workload protections using Microsoft Defender for Cloud Explain Microsoft Defender for Cloud Describe Microsoft Defender for Cloud workload protections Enable Microsoft Defender for Cloud 22 - Connect Azure assets to Microsoft Defender for Cloud Explore and manage your resources with asset inventory Configure auto provisioning Manual log analytics agent provisioning 23 - Connect non-Azure resources to Microsoft Defender for Cloud Protect non-Azure resources Connect non-Azure machines Connect your AWS accounts Connect your GCP accounts 24 - Manage your cloud security posture management? Explore Secure Score Explore Recommendations Measure and enforce regulatory compliance Understand Workbooks 25 - Explain cloud workload protections in Microsoft Defender for Cloud Understand Microsoft Defender for servers Understand Microsoft Defender for App Service Understand Microsoft Defender for Storage Understand Microsoft Defender for SQL Understand Microsoft Defender for open-source databases Understand Microsoft Defender for Key Vault Understand Microsoft Defender for Resource Manager Understand Microsoft Defender for DNS Understand Microsoft Defender for Containers Understand Microsoft Defender additional protections 26 - Remediate security alerts using Microsoft Defender for Cloud Understand security alerts Remediate alerts and automate responses Suppress alerts from Defender for Cloud Generate threat intelligence reports Respond to alerts from Azure resources 27 - Construct KQL statements for Microsoft Sentinel Understand the Kusto Query Language statement structure Use the search operator Use the where operator Use the let statement Use the extend operator Use the order by operator Use the project operators 28 - Analyze query results using KQL Use the summarize operator Use the summarize operator to filter results Use the summarize operator to prepare data Use the render operator to create visualizations 29 - Build multi-table statements using KQL Use the union operator Use the join operator 30 - Work with data in Microsoft Sentinel using Kusto Query Language Extract data from unstructured string fields Extract data from structured string data Integrate external data Create parsers with functions 31 - Introduction to Microsoft Sentinel What is Microsoft Sentinel? How Microsoft Sentinel works When to use Microsoft Sentinel 32 - Create and manage Microsoft Sentinel workspaces Plan for the Microsoft Sentinel workspace Create a Microsoft Sentinel workspace Manage workspaces across tenants using Azure Lighthouse Understand Microsoft Sentinel permissions and roles Manage Microsoft Sentinel settings Configure logs 33 - Query logs in Microsoft Sentinel Query logs in the logs page Understand Microsoft Sentinel tables Understand common tables Understand Microsoft Defender XDR tables 34 - Use watchlists in Microsoft Sentinel Plan for watchlists Create a watchlist Manage watchlists 35 - Utilize threat intelligence in Microsoft Sentinel Define threat intelligence Manage your threat indicators View your threat indicators with KQL 36 - Connect data to Microsoft Sentinel using data connectors Ingest log data with data connectors Understand data connector providers View connected hosts 37 - Connect Microsoft services to Microsoft Sentinel Plan for Microsoft services connectors Connect the Microsoft Office 365 connector Connect the Microsoft Entra connector Connect the Microsoft Entra ID Protection connector Connect the Azure Activity connector 38 - Connect Microsoft Defender XDR to Microsoft Sentinel Plan for Microsoft Defender XDR connectors Connect the Microsoft Defender XDR connector Connect Microsoft Defender for Cloud connector Connect Microsoft Defender for IoT Connect Microsoft Defender legacy connectors 39 - Connect Windows hosts to Microsoft Sentinel Plan for Windows hosts security events connector Connect using the Windows Security Events via AMA Connector Connect using the Security Events via Legacy Agent Connector Collect Sysmon event logs 40 - Connect Common Event Format logs to Microsoft Sentinel Plan for Common Event Format connector Connect your external solution using the Common Event Format connector 41 - Connect syslog data sources to Microsoft Sentinel Plan for syslog data collection Collect data from Linux-based sources using syslog Configure the Data Collection Rule for Syslog Data Sources Parse syslog data with KQL 42 - Connect threat indicators to Microsoft Sentinel Plan for threat intelligence connectors Connect the threat intelligence TAXII connector Connect the threat intelligence platforms connector View your threat indicators with KQL 43 - Threat detection with Microsoft Sentinel analytics What is Microsoft Sentinel Analytics? Types of analytics rules Create an analytics rule from templates Create an analytics rule from wizard Manage analytics rules 44 - Automation in Microsoft Sentinel Understand automation options Create automation rules 45 - Threat response with Microsoft Sentinel playbooks What are Microsoft Sentinel playbooks? Trigger a playbook in real-time Run playbooks on demand 46 - Security incident management in Microsoft Sentinel Understand incidents Incident evidence and entities Incident management 47 - Identify threats with Behavioral Analytics Understand behavioral analytics Explore entities Display entity behavior information Use Anomaly detection analytical rule templates 48 - Data normalization in Microsoft Sentinel Understand data normalization Use ASIM Parsers Understand parameterized KQL functions Create an ASIM Parser Configure Azure Monitor Data Collection Rules 49 - Query, visualize, and monitor data in Microsoft Sentinel Monitor and visualize data Query data using Kusto Query Language Use default Microsoft Sentinel Workbooks Create a new Microsoft Sentinel Workbook 50 - Manage content in Microsoft Sentinel Use solutions from the content hub Use repositories for deployment 51 - Explain threat hunting concepts in Microsoft Sentinel Understand cybersecurity threat hunts Develop a hypothesis Explore MITRE ATT&CK 52 - Threat hunting with Microsoft Sentinel Explore creation and management of threat-hunting queries Save key findings with bookmarks Observe threats over time with livestream 53 - Use Search jobs in Microsoft Sentinel Hunt with a Search Job Restore historical data 54 - Hunt for threats using notebooks in Microsoft Sentinel Access Azure Sentinel data with external tools Hunt with notebooks Create a notebook Explore notebook code

Second Degree Usui Reiki Course You will be taught how to conduct a healing session; protocols, etc and how to perform distance healings. This course is comprehensive and detailed. You will have all the tools you need to start using Reiki on others and their pets. Upon completion of this comprehensive and insightful Reiki course, you can go on to get insurance to set up as a Reiki Practitioner and start seeing clients.

Cisco Implementing Segment Routing on Cisco IOS XR (SEGRTE201)
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for Systems engineers Network engineers Field engineers Technical support personnel Channel partners and resellers Overview After taking this course, you should be able to: Describe the key concepts of segment routing Implement and verify IGP segment routing Migrate an existing Multiprotocol Label Switching (MPLS) LDP-based network to segment routing Implement and verify TI-LFA segment routing Instantiate segment routing policies Instantiate multidomain segment routing policies Configure and verify BGP prefix segments and SR-based services The Implementing Segment Routing on Cisco IOS XR (SEGRTE201) v2.0 course covers the fundamental concepts of Segment Routing (SR), how to configure and verify segment routing within an Interior Gateway Protocol (IGP), and the interworking of Label Distribution Protocol (LDP) with segment routing. You will learn how to implement Topology-Independent Loop-Free Alternate (TI-LFA) using segment routing, and how to instantiate and verify segment routing traffic engineering policies. You will also learn how to implement segment routing within Border Gateway Protocol (BGP). Introduction to Segment Routing Examining Unified Fabric Routing Exploring Segment Routing Concepts Examining Segment Types Examining the Segment Routing Global Block (SRGB) IGP Segment Routing Implementation and Verification Examining the IGP Control Plane Examining SRGB and IGP Interactions Examining Prefix and Adjacency SIDs Intermediate System to Intermediate System (IS-IS) Multilevel and Open Shortest Path First (OSPF) Multi-Area Configuring and Verifying IS-IS SR Operation Configuring and Verifying OSPF SR Operation Segment Routing and LDP Interworking SR and LDP Interworking Data Plane Mapping Server Function and Configuration Interworking Deployment Models Topology Independent ? Loop Free Alternate Examining Classic LFA Examining TI-LFA Fundamentals Implementing and Verifying TI-LFA for SR Traffic Implementing and Verifying SR TI-LFA for LDP Traffic TI-LFA and SR LDP Interworking Segment Routing Policies ? Traffic Engineering (SR-TE) Exploring SR Policies Introducing the Anycast and Binding SIDs Enabling and Verifying SR Policies Instantiating SR Policies Instantiating SR Policies using BGP Dynamic Multidomain SR Policies Configuring and Verifying a Path Computation Element (PCE) Configuring and Verifying BGP Link-State (LS) Configuring Multidomain SR Policies with a PCE Configuring Multidomain SR Policies with On Demand Next-Hop (ODN) Segment Routing?Based Services Examining the BGP Prefix-SID Operation Configuring and Verifying the BGP Prefix SID Examining Egress Peer Engineering Examining the BGP Prefix-SID Operation SR Flexible Algorithm and Performance Measurement (PM) Delay SR-Enabled VPNs

Legionella/Water Quality Risk Management – General Awareness
By HYDROP E.C.S.
Our Legionella/Water Quality Risk Management – General Awareness course offers a basic introduction to Legionnaires' disease Management and Control.

Rhino 3d and V-Ray for Rhino Basic to Intermediate Training Course
By Real Animation Works
Rhino Basic to Intermediate Training Course

Medical Terminology Training Courses - Level 1
By Mediterm Training
An Introduction to Medical Terminology short course delivered online via Teams, suitable for anyone wishing to learn the basics of terminology. Dates of courses can be seen when clicking ‘register’ below. Level One – Introduction to Medical Terminology. “It's like a light has just been switched on and I now understand more of what I'm doing!” – Feedback from attendee of Level one course. This course is aimed at anyone who requires a knowledge of medical terminology in their role. It is suitable for administrative staff, health care workers, medical secretaries, managers, Allied Health Professionals, essentially anyone who may encounter medical terminology and wishes to develop their medical terminology knowledge further. We also offer sessions to those requiring an overview of medical terminology to support applications to study medicine, veterinary medicine or dentistry.We can train between 1-30 learners from any organisation. If you have a specific training request, please speak to us and we can accommodate your needs. We recently trained a group of sign language interpreters who found the training invaluable when working in medical environments.The sessions are delivered via Teams (2x 2 hour meetings) so are highly accessible, a webcam and microphone are required although not essential.The aim of the course is for learners to develop an understanding of medical terminology in an enjoyable, interactive and informative way so that they are better able to decipher and unravel the mystery of long medical words.The course covers the following topics:- Basics of medical terminology – word building Common Roots, prefixes and suffixes Anatomy and physiology via a virtual tour of the body Major bones of the body Prescription writing and abbreviations Classification of drugs Common Abbreviations Instruments and investigations Medical Specialities and personnel Blood tests At the end of the course students will have a clear understanding of medical terminology and are encouraged to use their newly learned skills in a series of quizzes and interactive games. All attendees are given a Certificate of Attendance and a comprehensive handout. Many people who attend these courses are keen to develop their skills further and may wish to proceed to the Level Two Intermediate Award in Medical Terminology. Medical Terminology Training Courses Established in 2006 and the UK’s largest provider of medical terminology training, we offer a range of courses to suit your needs from beginner through to advanced level. Our bespoke courses have been designed to suit the needs of healthcare professionals incorporating relevant terminology and content to directly benefit the workplace. Click 'more course information' below to view further details of each of our courses.

Revit One to One Basic to Advance Weekends Online or Face to Face
By Real Animation Works
Revit face to face training customised and bespoke. Online or Face to Face