- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
ITIL 4 Specialist: High Velocity IT: In-House Training
By IIL Europe Ltd
ITIL® 4 Specialist: High Velocity IT: In-House Training The ITIL® 4 Specialist: High-Velocity IT module is part of the Managing Professional stream for ITIL® 4. Candidates need to pass the related certification exam for working towards the Managing Professional (MP) designation. This course is based on the ITIL® 4 Specialist: High-Velocity IT exam specifications from AXELOS. With the help of ITIL® 4 concepts and terminology, exercises, and examples included in the course, candidates acquire the relevant knowledge required to pass the certification exam. This module addresses the specifics of digital transformation and helps organizations to evolve towards a convergence of business and technology, or to establish a new digital organization. It was designed to enable practitioners to explore the ways in which digital organizations and digital operating models function in high-velocity environments. Working practices such as Agile and Lean, and technical practices and technologies such as Cloud, Automation, and Automatic Testing are included. What You Will Learn At the end of this course, participants will be able to: Understand concepts regarding the high-velocity nature of the digital enterprise, including the demand it places on IT. Understand the digital product lifecycle in terms of the ITIL operating model. Understand the importance of the ITIL guiding principles and other fundamental concepts for delivering high-velocity IT. Know how to contribute to achieving value with digital products. Course Introduction Let's Get to Know Each Other Course Learning Objectives Target Audience Characteristics ITIL® 4 Certification Scheme Course Components Course Agenda Module-End Exercises Exam Details Introduction to High-Velocity IT High-Velocity IT Digital Technology Digital Organizations Digital Transformation High-Velocity IT Approaches Relevance of High-Velocity IT Approaches High-Velocity IT Approaches in Detail High-Velocity IT Operating Models Introduction ITIL® Perspective High-Velocity IT Aspects High-Velocity IT Applications ITIL® Building Blocks for High-Velocity IT Digital Product Lifecycle Service Value Streams Four Dimensions of Service Management ITIL® Management Practices High-Velocity IT Culture Key Behavior Patterns ITIL® Guiding Principles Supporting Models and Concepts for Purpose Ethics Design Thinking Supporting Models and Concepts for People Reconstructing for Service Agility Safety Culture Stress Prevention Supporting Models and Concepts for Progress Working in Complex Environments Lean Culture ITIL® Continual Improvement Model High-Velocity IT Objectives and Techniques High-Velocity IT Objectives High-Velocity IT Techniques Techniques for Valuable Investments Prioritization Techniques Minimum Viable Products and Services Product / Service Ownership A/B Testing Techniques for Fast Developments Basic Concepts Related to Fast Development Infrastructure as Code Reviews Continual Business Analysis Continuous Integration / Continuous Delivery (CI/CD) Continuous Testing Kanban Techniques for Resilient Operations Introduction to Resilient Operations Technical Debt Chaos Engineering Definition of Done Version Control Algorithmic IT Operations ChatOps Site Reliability Engineering (SRE) Techniques for Co-created Value Basic Concepts of Co-created Value Service Experience Techniques for Assured Conformance DevOps Audit Defense Toolkit DevSecOpsPeer Review

Business Analysis Fundamentals: In-House Training
By IIL Europe Ltd
Business Analysis Fundamentals: In-House Training This course is part of IIL's Business Analysis Certificate Program (BACP), a program designed to help prepare individuals to pass the IIBA® Certification exam to become a Certified Business Analysis Professional (CBAP™). This course teaches participants the overall process of business analysis and where it fits in the bigger picture of the project life cycle and the business context. The course is interactive and combines discussion, active workshops, and demonstrations of techniques. The goal is bottom-line results that cut through the real-world problems facing people seeking to improve the way they operate to develop new and improved systems and products or otherwise deliver results through project performance. What you will Learn At the end of this program, you will be able to: Define the solution scope Work with the development team in the systems testing stage Ensure the solution is usable in the business environment Foundation Concepts Defining the business analyst (BA) function The role of the BA as change agent An introduction to the BABOK® Guide BA roles and relationships through the project life cycle (PLC) Business Analysis Planning and Monitoring Overview of business analysis planning and monitoring (BAP&M) Business analysis planning and monitoring - process and tools Business analysis planning and monitoring - roles and responsibilities Business analysis planning and monitoring - governance, information management, and performance improvement Elicitation and Collaboration Overview of elicitation and collaboration Elicitation and collaboration techniques Requirements Life Cycle Management Overview of requirements life cycle management Requirements life cycle management task details Strategy Analysis Overview of strategy analysis Analyze current state Define future state Assess risks Define change strategy Requirements Analysis and Design Definition Overview of requirements analysis and design definition (RA&DD) The anatomy of requirements RA&DD task descriptions RA&DD techniques Solution Evaluation Overview of solution evaluation Solution evaluation tasks Solution evaluation in development stages Underlying Competencies Overview of underlying competencies (UC) Underlying competencies

Advanced Java training course description A tour of the more advanced features of Java following on from the Introduction to Java course. JDBC and JavaBeans are covered in separate courses. What will you learn Use Java to implement OOA/D. Use within Java programs - Internationalisation - Object serialisation - Reflection - RMI - Swing - JAR files Write Servlets and Java Server Pages Advanced Java training course details Who will benefit: Those wishing to program in Java. Prerequisites: Introduction to Java programming Duration 5 days Advanced Java training course contents What you should already know OO features in Java Static initialisers, object destruction, finalisation, constructor chaining, shadowing, Abstract classes and interfaces, inner classes, nested classes, member classes, local classes, anonymous classes. Internationalisation Locales, Unicode, local customs, localising messages. Object Serialisation Simple and custom serialisation, class versioning. Reflection Obtaining class and member information. RMI Restrictions, RMI architecture, Stubs, skeletons, rmic, the registry server, The RMI API. Swing An overview, examples, comparison vs. AWT, data transfer cut & paste. Servlets Servlet API, Java Web server, The servlet life cycle, chaining servlets, Hybrid servlets. JAR files and signed applet JAR files and signed applet

M.D.D I LET MY PARTNERS TREAT ME BADLY PACKAGE (SINGLES)
4.9(27)By Miss Date Doctor Dating Coach London, Couples Therapy
Confidence Training Emotional Intelligence Training Dating Coach Support Daily Social skills examination Dating history analysis Red flag Training and Dating Coach Self-assessment and analysis Insecurities and pinpoint dating issues and problems 4 weeks of coaching Overview of dating skills Dating advice for singles https://relationshipsmdd.com/product/i-let-my-partners-treat-me-badly-package/

Microsoft security training course description A hands on training course focusing on security in the Microsoft environment. The course progresses from patch management onto the use of Microsoft security tools. Then server, desktop and network security are studied in the Microsoft environment. What will you learn Use Microsoft security tools. Secure Microsoft servers. Secure Microsoft desktops. Secure Microsoft networks. Microsoft security training course details Who will benefit: Technical server support staff. Technical desktop support staff. Technical network staff. Technical security staff. Prerequisites: Supporting Windows server 2016 Networking Microsoft systems. Duration 3 days Microsoft security training course contents Introduction Security threats, Microsoft defaults, admin accounts, security patches, patch management, patch tools. Hands on: Studying Microsoft defaults, applying security patches. Microsoft security tools Microsoft updates, WSUS, Inventory tool, baseline security analyser, URLscan, EventCombMT, Cipher security tool, Port reporter, PortQry. Tools hackers use. Hands on: Using Microsoft security tools. Server security Checklists, core server security, AD, Member server security, Domain controller security, Specific roles. Hands on Hardening Microsoft servers, security templates. Active Directory Admin authority in AD, group policy, trust and authentication. Desktop security Checklists, core client security, anti virus software, anti spyware software, firewalls, securing clients with AD, securing clients with group policy, software restriction policies. Hands on Securing Microsoft desktops. Network security Checklist, IP security, VPNs, PKI, certificate authorities, RAS, RRAS, IAS. Hands on: VPN configuration, IAS configuration. Monitoring Auditing, authorisation and logons, tracking, system monitoring, detecting attacks. Hands on: Monitoring Microsoft systems. Summary Microsoft security response centre, security advisories.

Objective-C programming training course description A hands on introduction that will allow you to master Objective-C and start using it to write powerful native applications for even the newest Macs and iOS devices! Using The step-by-step approach, will let you get comfortable with Objective-C's unique capabilities and Apple's Xcode 5 development environment. Make the most of Objective-C objects and messaging. Work effectively with design patterns, collections, blocks, foundation classes, threading, Git and a whole lot more. Every session builds on what you've already learned, giving a rock-solid foundation for real-world success! What will you learn Use Xcode 5. Declare classes, instance variables, properties, methods, and actions. Use arrays, dictionaries, and sets. Expand and extend classes with protocols, delegates, categories, and extensions. Use Apple's powerful classes and frameworks. Objective-C programming training course details Who will benefit: Developers wanting to learn Objective-C. Prerequisites: Software development fundamentals. Duration 5 days Objective-C programming training course contents PART 1: GETTING STARTED WITH OBJECTIVE-C The Developer Program: Objective-C, enrolling as an Apple Developer, setting up the development environment, Xcode. Your first project. OO programming with Objective-C: OO projects, Frameworks, classes and instances, encapsulation, accessors, Inheritance. OO features in Objective-C: Messages, methods, working with id, nesting messages, method signatures and parameters. allocating and initializing objects. Using Xcode: Xcode, source code control, git and Xcode, Using a Remote Repository. Compiler Directives: Projects, Compiler Directives, Prefix headers, main.m, .h files. PART 2: OBJECTIVE-C BASICS Messaging in a Testbed App: Setting Up the Testbed Apps, Adding a Text Field and Connecting It to Your Code, Sending a Message to the Text Field, Reviewing the Message Syntax. Declaring a Class in an Interface File: Context, Creating an Instance Variable with id, What Happens When Execution Stops, dynamic binding, Creating an Instance Variable for with the Class Name and with a Superclass Name, instance variable visibility. Properties in an Interface File: Interface Variables vs Properties, Declared Properties, Using Attributes. Implementing Properties. @synthesize, @dynamic. Methods in an Interface File: Methods in a Class, class and instance methods, Method declaration, returning complex data structures from Methods. Actions in an Interface File: Actions, Actions in OS X and iOS, disconnecting actions. Routing messages with selectors: Receiver and selector objects in messages, Objective-C Runtime, SEL and @selector (), performSelector, NSInvocation, testing whether an Instance can respond to a selector. Building on the Foundation: The Foundation Framework, Foundation Classes, Foundation Paradigms and Policies; Mutability, class clusters, notifications. Defining a Class in Implementation Files: Projects, dynamic typing, creating a new App, implementing a method, expanding Classses with init Methods. Organizing Data with Collections: Collecting Objects, Property Lists, Runtime, comparing the Collection Classes, Creating a Collection, Objective-C Literal Syntax, Enumerating collections, Testing Membership in a Collection, Accessing an Object in a Collection. Managing Memory and Runtime Objects: Managing objects in memory, managing reference counts manually and with ARC, variable qualifiers, variable autorelease. PART 3: EXPANDING AND EXTENDING CLASSES Protocols and Delegates: Subclassing, Protocols, Delegates, Looking Deeper Inside Protocols. Categories and Extensions: Comparing categories and protocols, categories vs subclasses, working with categories, class extensions, informal protocols. Associative References and Fast Enumeration: Objective-C 2.0 Time-Saving Features, Extending Classes by Adding Instance Variables (Sort of), Using Fast Enumeration. Blocks: Revisiting Blocks, Callbacks, Blocks, Exploring Blocks in Cocoa, Cocoa Blocks and Memory. PART 4: BEYOND THE BASICS Handling Exceptions and Errors: Exception and Error classes: NSException, NSError, Identifying exceptions, throwing exceptions, catching exceptions. Queues and Threading: Getting Started with Concurrency, Introducing Queues, Dispatch Sources, Using Dispatch Queues. Working with the Debugger: Logging Information, Console Logs, NSLog, Smart Breakpoints, enhancing breakpoints with messages. Using Xcode Debug Gauges for Analysis: Debug Gauges, Monitoing CPU and memory utilization, monitoring energy, Using Instruments. PART 5: OPTIONAL TOPICS C Syntax Summary: Data Types, Control Structures. Apps, Packages, and Bundles: Project Bundles, lproj Files, Asset Catalogs, plist Files, Precompiled Header Files (.pch). Archiving and Packaging Apps for Development and Testing: Archiving.

Exploration & Production (E&P) Accounting Level 3
By EnergyEdge - Training for a Sustainable Energy Future
About this training course This highly interactive 5-day training is aimed at those who wish to take their E&P accounting skills to a more advanced level than our introductory course, E&P Accounting - Level 1, and our intermediate course, E&P Accounting - Level 2. It will help equip you for more demanding analytical roles within your organisation. Training Objectives After the completion of this training course, participants will be able to: Carry out and manage the day-to-day financial accounting activities associated with participation in E&P joint ventures Prepare, analyse and present information for effective financial reporting Understand the impact of a comprehensive range of activities on the financial statements of an upstream oil and gas company Practically apply IFRS in accounting for a wide range of typical oil and gas industry activities Target Audience This is an advanced level course designed for: those who have already attended E&P Accounting - Level 1 and E&P Accounting - Level 2, or those who can demonstrate, by a combination of relevant experience and previous study, sufficient prior knowledge to contribute and benefit from attending this workshop Course Level Advanced Training Methods Training Method - Scenario Based Learning Learning centers around highly realistic E&P company scenarios. A computer-based simulation is used to plan, record and report the progress of your company through several years of international E&P activities. Teams of 2 - 3 people participate in the financial management of these activities, including Operator and Non-operator accounting, recording of transactions, updating of financial statements and analysis of results. The highly interactive laptop-based scenario approach will enable you to follow the impact of each activity from initiation through to final results and analysis of company performance. You will need to bring with you to the course your own laptop PC with MS Excel⢠pre-installed. Prior knowledge of spreadsheet techniques is assumed. Trainer will provide various Excel files which participants may retain at the end of the course. Course Duration: 5 days in total (35 hours). Training Schedule 0830 - Registration 0900 - Start of training 1030 - Morning Break 1045 - Training recommences 1230 - Lunch Break 1330 - Training recommences 1515 - Evening break 1530 - Training recommences 1700 - End of Training The maximum number of participants allowed for this training course is 25. Trainer Your expert course leader has more than 30 years of experience in the international oil and gas industry, covering all areas of Finance and Audit, including involvement in Commercial roles. During her 19 years with ENI she worked in Italy, Netherlands, Egypt and UK and was CFO for 2 major ENI subsidiaries. She has delivered training courses in Accounting, Audit, Economics and Commercial topics in many Countries. She has a Degree in Economics & Accounting and is a Certified Chartered Accountant. She is also a Chartered Auditor and an International Petroleum Negotiator. Outside of work, she is inspired by the beauty of nature and art, helping disadvantaged people, sports (football, golf) and her cat. Courses Delivered Internationally: E&P Accounting, Auditing in the Oil & Gas Industry Cost Control & Budgeting Introduction to the Oil & Gas Industry Petroleum Project Economics Contracts Strategy International O&G Exploitation Contracts POST TRAINING COACHING SUPPORT (OPTIONAL) To further optimise your learning experience from our courses, we also offer individualized 'One to One' coaching support for 2 hours post training. We can help improve your competence in your chosen area of interest, based on your learning needs and available hours. This is a great opportunity to improve your capability and confidence in a particular area of expertise. It will be delivered over a secure video conference call by one of our senior trainers. They will work with you to create a tailor-made coaching program that will help you achieve your goals faster. Request for further information post training support and fees applicable Accreditions And Affliations

CWSP training course description A hands-on training course concentrating solely on WiFi security with an emphasis on the delegates learning the necessary knowledge and skills to pass the CWSP exam. The course progresses from simple authentication, encryption and key management onto in depth coverage of 802.X and EAP along with many other security solutions such as access control, intrusion prevention and secure roaming. What will you learn Demonstrate the threats to WiFi networks. Secure WiFi networks. Configure: WPA2 RADIUS 802.1x EAP Pass the CWSP exam. CWSP training course details Who will benefit: Technical network staff. Technical security staff. Prerequisites: Certified Wireless Network Associate. Duration 5 days CWSP training course contents WLAN Security overview Standards, security basics, AAA, 802.11 security history. Hands on WLAN connectivity. Legacy 802.11 security Authentication: Open system, shared key. WEP. VPNs. MAC filters. SSID segmentation, SSID cloaking. Hands on Analysing 802.11 frame exchanges, viewing hidden SSIDs. Encryption Basics, AES, TKIP, CCMP, WPA, WPA2. Hands on Decrypting 802.11 data frames. 802.11 layer 2 authentication 802.1X: Supplicant, Authenticator, Authentication server. Credentials. Legacy authentication. EAP, Weak EAP protocols, Strong EAP protocols: EAP -PEAP, EAP-TTLS, EAP-TLS, EAP-FAST. Hands on Analysing 802.1X/EAP frames. 802.11 layer 2 dynamic key generation Robust Security Network. Hands on Authentication and key management. SOHO 802.11 security WPA/WPA2 personal, Preshared Keys, WiFi Protected Setup (WPS). Hands on PSK mapping. WLAN security infrastructure DS, Autonomous APs, WLAN controllers, split MAC, mesh, bridging, location based access control. Resilience. Wireless network management system. RADIUS/LDAP servers, PKI, RBAC. Hands on 802.1X/EAP configuration. RADIUS configuration. 802.11 Fast secure roaming History, RSNA, OKC, Fast BSS transition, 802.11k. Hands on Roaming. Wireless security risks Rogue devices, rogue prevention. Eavesdropping, DOS attacks. Public access and hotspots. Hands on Backtrack. WiFi security auditing Layer 1 audit, layer 2 audit, pen testing. WLAN security auditing tools. WiFi security monitoring Wireless Intrusion Detection and Prevention Systems. Device classification, WIDS/WIPS analysis. Monitoring. 802.11w. Hands on Laptop spectrum analysers. VPNs, remote access, guest access Role of VPNs in 802.11, remote access, hotspots, captive portal. Wireless security policies General policy, functional policy, recommendations.

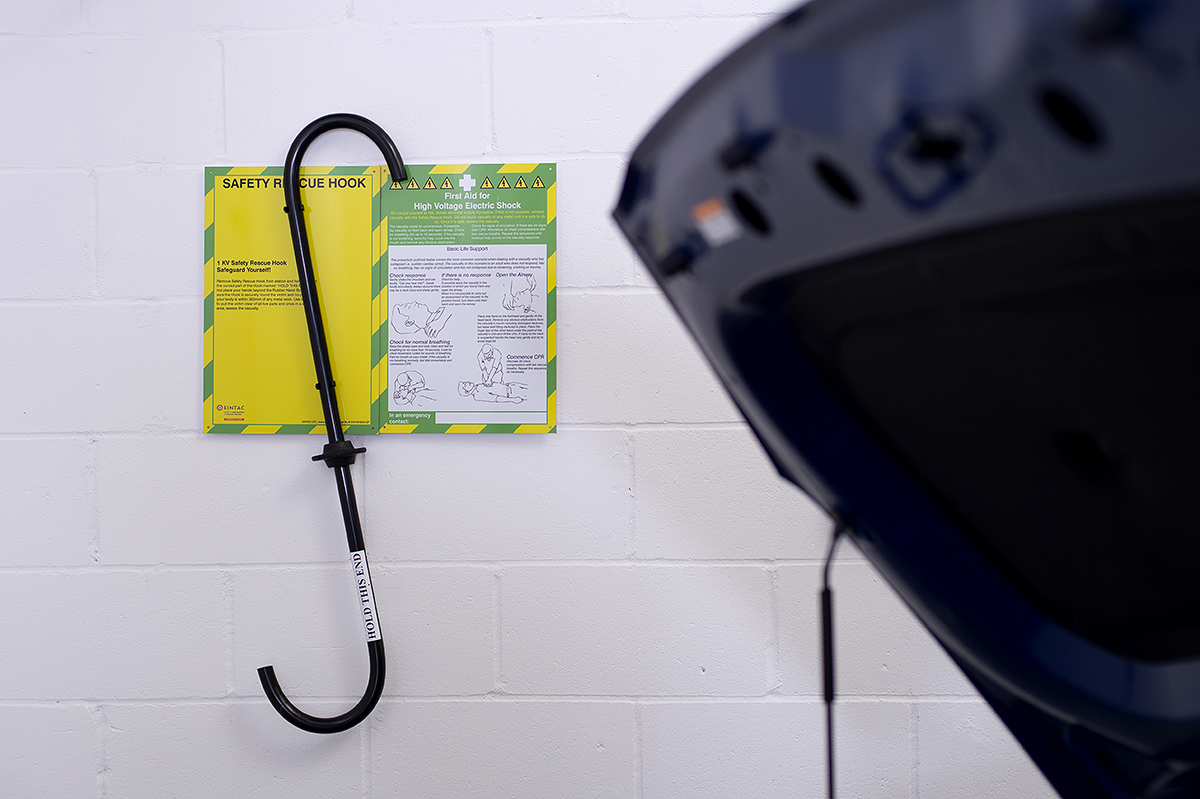
EINTAC IMI Level 2 Award In Electric/Hybrid Vehicle Hazard Management For Emergency And Recovery Personnel
By EINTAC Ltd
This IMI qualification is designed for those personnel who in the course of their daily work may encounter damaged electric/hybrid vehicles. It contains the knowledge required to work safely around the electric/hybrid vehicles high and low voltage electrical system and electric drive train systems. On completing this qualification those personnel will have gained knowledge of both low and high voltage technologies and an understanding of their dangers. The content of this qualification has been designed to give learners the knowledge and skills required to work safely around Electric/Hybrid vehicles during emergency and recovery situations.
Advanced Process Safety Engineering
By EnergyEdge - Training for a Sustainable Energy Future
Enhance your knowledge in process safety engineering with EnergyEdge's advanced classroom training course. Register now to secure your spot!
Search By Location
- #Training Courses in London
- #Training Courses in Birmingham
- #Training Courses in Glasgow
- #Training Courses in Liverpool
- #Training Courses in Bristol
- #Training Courses in Manchester
- #Training Courses in Sheffield
- #Training Courses in Leeds
- #Training Courses in Edinburgh
- #Training Courses in Leicester
- #Training Courses in Coventry
- #Training Courses in Bradford
- #Training Courses in Cardiff
- #Training Courses in Belfast
- #Training Courses in Nottingham