- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1699 Computing courses in Cardiff delivered Live Online
VMware Data Center Virtualization: Core Technical Skills
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for Technical professionals with basic system administration skills and operators responsible for managing virtual machines using VMware ESXi⢠and VMware vCenter Server Overview By the end of the course, you should be able to meet the following objectives: Describe virtualization and virtual machines Describe vSphere components and the software-defined data center (SDDC) Explain the concepts of server, network, and storage virtualization Monitor network and datastore configurations in VMware vSphere Client⢠Deploy, configure, and clone virtual machines Migrate, monitor, and manage virtual machines Monitor tasks and events in VMware vSphere Client⢠Recognize how vSphere DRS and VMware vSphere High Availability improve performance and availability of a vSphere cluster This three-day, hands-on training course is an introduction to VMware vSphere©. In this course, you acquire the skills needed to perform Day 2 operational tasks that are typically assigned to the roles of operator or junior administrator in a vSphere environment. Course Introduction Introductions and course logistics Course objectives Virtualization and vSphere Concepts Describe how virtual machines (VMs) work Recognize the purpose of a hypervisor Describe how VMs share resources in a virtualized environment Recognize the components of an SDDC Describe the relationship between vSphere, the SDDC, and cloud computing Recognize the functions of the components in a vSphere environment Access and view vSphere graphical user interfaces Identify VMware solutions that integrate with vSphere in the SDDC Navigating the vSphere Client View and organize the inventory objects managed by vCenter Server Add and assign vSphere licenses Change the log level of vCenter Server Edit the startup policy of ESXi services Describe how vCenter Server roles and permissions work Add permissions to virtual machines Lifecycle of Virtual Machines Add and remove VM virtual hardware components Identify the purpose of different VM files Configure VM settings Create and delete virtual machines Recognize the benefits of installing VMware Tools? Install VMware Tools into a guest operating system Upgrade VMware Tools and VM hardware compatibility vSphere Networking Describe virtual networking Recognize ways that virtual switches connect VMs and ESXi hosts to the network View components and properties of a vSphere standard switch configuration View a vSphere distributed switch configuration in vSphere Client Recognize when and how to use the settings for the security networking policy Recognize when and how to use the settings for the traffic shaping networking policy Describe how the NIC teaming and failover policy helps maintain network connectivity Perform basic checks to diagnose VM connectivity issues vSphere Storage Describe the function of a datastore Recognize types of vSphere datastores View datastore information in vSphere Client Monitor datastore usage in vSphere Client Virtual Machine Management Recognize the benefits of using VM templates Create and update a VM template Deploy a VM from an existing template Clone a virtual machine Recognize how to use guest OS customization specifications Deploy VMs from a content library Deploy a virtual appliance from an OVF template Perform a hot and cold migrations of VMs Identify requirements for using VMware vSphere© Storage vMotion© Perform a vSphere Storage vMotion migration Identify use cases for VM snapshots Create and manage snapshots of a virtual machine Resource Monitoring Recognize the purpose of each type of VM resource control Configure the resource allocation settings of a VM Observe the behavior of virtual machines with different share values Manage and acknowledge vSphere alarms Use performance charts to monitor VM CPU and memory usage Monitor tasks and events in vSphere Client vSphere Clusters View information about the services that a vSphere cluster offers Recognize how vSphere HA responds to different types of failures Monitor vSphere HA during a host failure Describe how vSphere DRS works Interpret DRS scores given to VMs Recognize how to apply the appropriate vSphere DRS automation and migration threshold levels Describe how vSphere Fault Tolerance works Recognize how Enhanced vMotion Compatibility works Additional course details:Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware Data Center Virtualization: Core Technical Skills training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware Data Center Virtualization: Core Technical Skills course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

55324 Installation, Storage and Compute with Windows Server 2016
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is intended for information technology (IT) professionals who need to improve their expertise in Windows Server 2016 in the area of storage and compute functionality. Overview After completing this course, you will be able to: Configure and install Windows Server 2016 Manage Server Core, server upgrade and migration strategy Understand storage options Manage partition table formats Manage basic and dynamic disks, file systems Manage virtual hard disks, and drive hardware Manage disks and volumes Select and manage proper storage solutions for a specific scenario Storage Spaces and Data Deduplication implementation Configure and Manage Microsoft Hyper-V, virtual machines and Hyper-V containers Configure disaster recovery technologies Manage and Configure failover clustering for Hyper-V virtual machines Configure, plan and implement a Network Load Balancing (NLB) Work with deployment images This course is intended for information technology (IT) professionals who have basic knowledge of Windows Server. It is designed for professionals who have primary responsibility of managing storage and computing by using Windows Server 2016. Professionals who need to understand the scenarios, requirements, and storage and compute options that are available and applicable to Windows Server 2016.This course covers content that was in retired Microsoft Course 20740. Module 1: Installing, upgrading, and migrating servers and workloads Introducing Windows Server 2016 Preparing and installing Server Core Preparing for upgrades and migrations Migrating server roles and workloads Windows Server activation models Module 2: Configuring local storage Managing disks in Windows Server Managing volumes in Windows Server Module 3: Implementing enterprise storage solutions Overview of DAS, NAS, and SANs Comparing Fibre Channel, iSCSI, and Fibre Channel over Ethernet Understanding iSNS, DCB, and MPIO Configuring sharing in Windows Server 2016 Module 4: Implementing Storage Spaces and Data Deduplication Implementing Storage Spaces Managing Storage Spaces Implementing Data Deduplication Module 5: Installing and configuring Hyper-V and virtual machines Overview of Hyper-V Installing Hyper-V Configuring storage on Hyper-V host servers Configuring networking on Hyper-V host servers Configuring Hyper-V virtual machines Managing virtual machines Module 6: Deploying and managing Windows and Hyper-V containers Overview of containers in Windows Server 2016 Preparing for containers Installing, configuring, and managing containers by using Docker Module 7: Overview of high availability and disaster recovery Defining levels of availability Planning high availability and disaster recovery solutions with Hyper-V virtual machines Backing up and restoring by using Windows Server Backup High Availability with failover clustering in Windows Server 2016 Module 8: Implementing failover clustering Planning a failover cluster Creating and configuring a new failover cluster Maintaining a failover cluster Troubleshooting a failover cluster Implementing site high availability with stretch clustering Module 9: Implementing failover clustering with Windows Server 2016 Hyper-V Overview of yhe integration of Hyper-V Server 2016 with failover clustering Implementing Hyper-V VMs on failover clusters Key features for VMs in a clustered environment Module 10: Implementing Network Load Balancing Overview of NLB Configuring an NLB cluster Planning an NLB implementation Module 11: Creating and managing deployment images Introduction to deployment images Creating and managing deployment images by using MDT Virtual machine environments for different workloads Module 12: Managing, monitoring, and maintaining virtual machine installations WSUS overview and deployment options Update management process with WSUS Overview of Windows PowerShell DSC Overview of Windows Server 2016 monitoring tools Using Performance Monitor Monitoring event logs Additional course details: Nexus Humans 55324 Installation, Storage and Compute with Windows Server 2016 training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the 55324 Installation, Storage and Compute with Windows Server 2016 course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Learn everything you need to know to be fully competent with Window OS. This syllabus takes you around the basics and then on another deep dive into all the elements. Discover things you never knew and speed up your experience using Windows OS. Module 1: Introduction to Windows OS • Understanding the Windows operating system • Navigating the Windows interface • Customizing system settings and preferences Module 2: File Management • Managing files and folders in Windows Explorer • Copying, moving, and renaming files • Using the Recycle Bin and data recovery Module 3: Windows Built-in Apps • Using Microsoft Edge for web browsing • Effective web searching using search engines • Email management with Windows Mail • Calendar and task management with Windows Calendar Module 4: Software Installation and Updates • Installing and updating software applications • Managing and uninstalling programs • Windows Store and app installations Module 5: Microsoft Office Basics • Introduction to Microsoft Office suite • Using Microsoft Word for document creation • Basic spreadsheet management with Microsoft Excel Module 6: Microsoft Office Intermediate Skills • Advanced features in Microsoft Word • Creating and formatting spreadsheets in Microsoft Excel • Creating dynamic presentations with PowerPoint Module 7: Multimedia and Graphics • Basic image editing with Paint • Using Windows Photo app for photo management • Creating graphics with Paint 3D Module 8: Productivity and Collaboration • Using OneDrive for cloud-based storage and collaboration • Working with Windows Sticky Notes and To-Do • Collaborative editing with Microsoft Office Online Module 9: Troubleshooting and Maintenance • Identifying and resolving common Windows issues • Using Task Manager for performance monitoring • Maintenance tasks for Windows OS Module 10: Windows Security and Privacy • Overview of Windows security features • Online safety and privacy best practices • Protecting personal data and devices Module 11: Advanced Windows Features • Customizing the Windows Start Menu and Taskbar • Using Cortana for voice commands and search • Virtual desktops and advanced multitasking Module 12: Using AI and Chat GPT • Introduction to AI and Chat GPT technology • Exploring AI-powered features in Windows • Using Chat GPT for productivity and assistance Module 13: Browsing and Search Engines • Effective use of web browsers • Utilizing search engines for research • Online safety and privacy while browsing Module 14: Cybersecurity • Understanding cybersecurity threats • Protecting against malware and phishing attacks • Secure online practices and password management Module 15: Software Installation and Factory Reset • Installing and updating software applications • Factory resetting a Windows device • Data backup and recovery during resets Module 16: Final Projects and Assessment • Culminating projects showcasing Windows OS skills • Practical exams assessing Windows software knowledge and skills • Preparing for industry-recognized certifications (optional) Please note that the duration and depth of each module can vary depending on the level of expertise required and the specific needs of the learners. Additionally, it's important to adapt the curriculum to the learners' proficiency levels, whether they are A Level/GCSE students or adult learners with different experience levels.

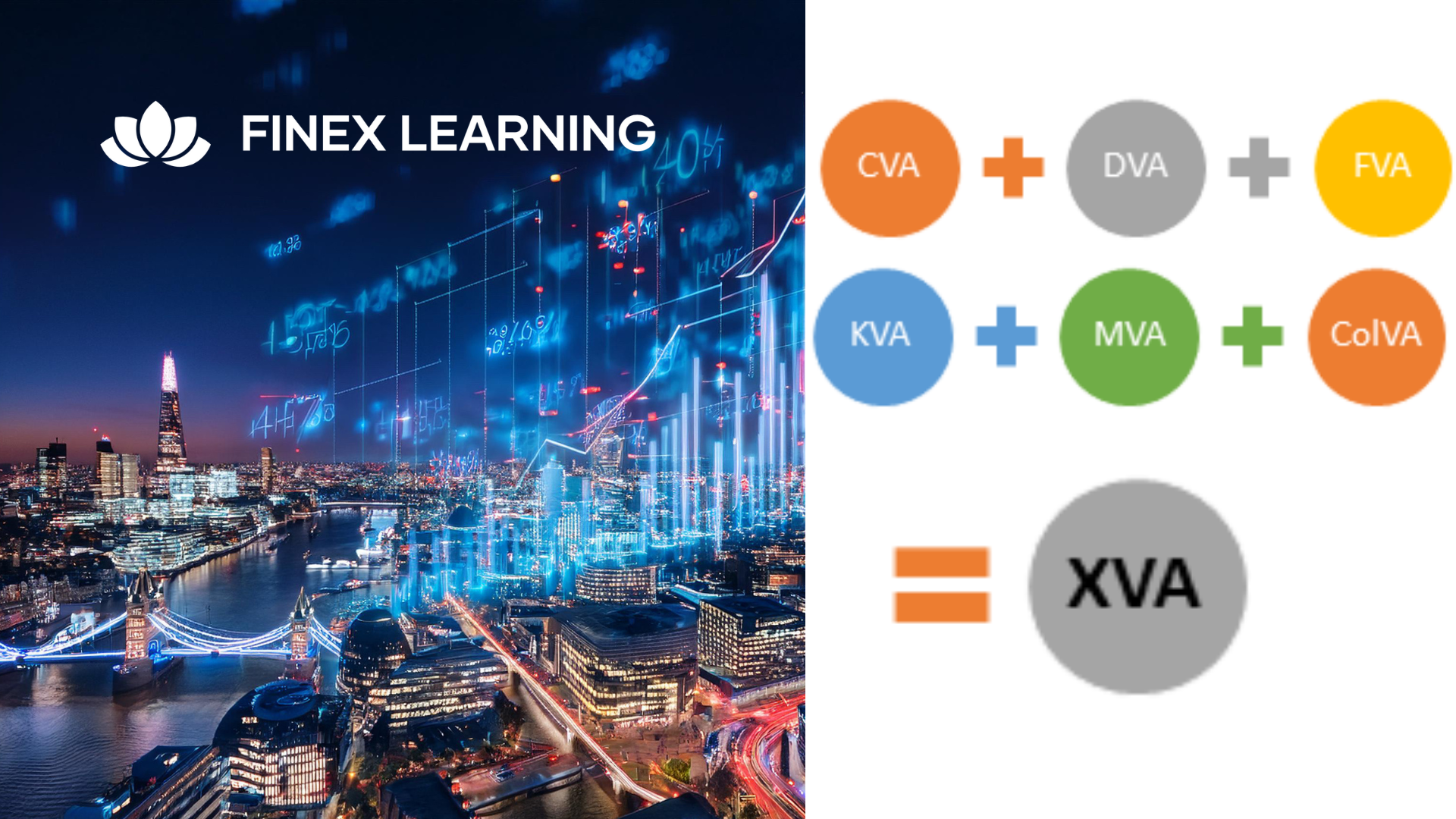
Overview This 1 day course focus on comprehensive review of the current state of the art in quantifying and pricing counterparty credit risk. Learn how to calculate each xVA through real-world, practical examples Understand essential metrics such as Expected Exposure (EE), Potential Future Exposure (PFE), and Expected Positive Exposure (EPE) Explore the ISDA Master Agreement, Credit Support Annexes (CSAs), and collateral management. Gain insights into hedging strategies for CVA. Gain a comprehensive understanding of other valuation adjustments such as Funding Valuation Adjustment (FVA), Capital Valuation Adjustment (KVA), and Margin Valuation Adjustment (MVA). Who the course is for Derivatives traders, structurers and salespeople xVA desks Treasury Regulatory capital and reporting Risk managers (market and credit) IT, product control and legal Quantitative researchers Portfolio managers Operations / Collateral management Consultants, software providers and other third parties Course Content To learn more about the day by day course content please click here To learn more about schedule, pricing & delivery options, book a meeting with a course specialist now
VMware Horizon 8: Deploy and Manage
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Operators, administrators, and architects for VMware Horizon should enroll in this course. These individuals are responsible for the creation, maintenance, and or delivery of remote and virtual desktop services. Additional duties can include the implementation, support, and administration of an organization's end-user computing infrastructure. Overview By the end of the course, you should be able to meet the following objectives: Recognize the features and benefits of Horizon Use VMware vSphere to create VMs to be used as desktops for Horizon Create and optimize Windows VMs to create Horizon desktops Install and configure Horizon Agent on Horizon desktop Configure and manage the VMware Horizon Client⢠systems and connect the client to a VMware Horizon desktop Configure, manage, and entitle desktop pools of full VMs Configure, manage, and entitle pools of instant-clone desktops Create and use Remote Desktop Services (RDS) desktops and application pools Monitor the Horizon environment using Horizon Console Dashboard and Horizon Help Desk Tool Identify Horizon Connection Server installation, architecture, and requirements. Describe the authentication and certification options for a Horizon environment Recognize the integration process and benefits of VMware Workspace ONE Access⢠and Horizon 8 Discuss performance and scalability options available in Horizon 8 Describe different security options for the Horizon environment VMware Horizon 8: Deploy and Manage is a five-day combination course of VMware Horizon 8: Skills for Virtual Desktop Management & VMware Horizon 8: Infrastructure Administration. This training collection gives you the hands-on skills to deliver virtual desktops and applications through a single virtual desktop infrastructure platform. You will build on your skills in configuring and managing VMware Horizon© 8 through a combination of lecture and hands-on labs. You learn how to configure and deploy pools of virtual machines and how to provide a customized desktop environment to end-users. Additionally, you will learn how to install and configure a virtual desktop infrastructure platform. You learn how to install and configure VMware Horizon© Connection Server?, VMware Unified Access Gateway?, how to configure a load balancer for use with Horizon, and how to establish Cloud Pod Architecture. Course Introduction Introductions and course logistics Course objectives Introduction to VMware Horizon Recognize the features and benefits of Horizon Describe the conceptual and logical architecture of Horizon Introduction to Use Case Define a use case for your virtual desktop and application infrastructure Convert customer requirements to use-case attributes vSphere for Horizon 8 Explain basic virtualization concepts Use VMware vSphere© Client? to access your Center Server system and VMware ESXi? hosts Create, provision, and remove a virtual machine VMware Horizon Desktops Create a Windows and a Linux virtual machine using vSphere Optimize and prepare Windows and Linux virtual machines to set up Horizon desktop VMs VMware Horizon Agents Outline the configuration choices when installing Horizon Agent on Windows and Linux virtual machines Create a gold master for Windows Horizon desktops VMware Horizon Pools Identify the steps to set up a template for desktop pool deployment List the steps to add desktops to the VMware Horizon© Connection Server? inventory Compare dedicated-assignment and floating-assignment pools Outline the steps to create an automated pool Define user entitlement Explain the hierarchy of global, pool-level, and user-level policies VMware Horizon Client Options Describe the different clients and their benefits Access Horizon desktop using various Horizon clients and HTML Configure integrated printing, USB redirection, and the shared folders option Configure session collaboration and media optimization for Microsoft Teams Creating and Managing Instant-Clone Desktop Pools List the advantages of instant clones Explain the provisioning technology used for instant clone desktop pools Set up an automated pool of instant clones Push updated images to instant clone desktop pools Creating RDS Desktop and Application Pools Explain the difference between an RDS desktop pool and an automated pool Compare and contrast an RDS session host pool, a farm, and an application pool Create an RDS desktop pool and an application pool Access RDS desktops and application from Horizon Client Use the instant clone technology to automate the build-out of RDSH farms Configure load-balancing for RDSHs on a farm Monitoring VMware Horizon Monitor the status of the Horizon components using the Horizon Administrator console dashboard Monitor desktop sessions using the HelpDesk tool Course Introduction Introductions and course logistics Course objectives Horizon Connection Server Recognize VMware Horizon reference architecture Identify the Horizon Connection Server supported features Identify the recommended system requirements for Horizon Connection Server Configure the Horizon event database Outline the steps for the initial configuration of Horizon Connection Server Discuss the ADAM database as a critical component of Horizon Connection Server installation Authentication and Certificates Compare the authentication options that Horizon Connection Server supports Describe the Smartcard authentication options that Horizon Connection Server supports Outline the steps to create a Horizon administrator and custom roles Describe the roles available in a Horizon environment Explain the role that certificates play for Horizon Connection Server Install and configure certificates for Horizon Connection Server Install and configure True SSO in a Horizon environment Workspace ONE Access & Virtual Application Management Recognize the features and benefits of Workspace ONE Access Recognize the Workspace ONE Access console features Explain identity management in Workspace ONE Access Explain access management in Workspace ONE Access Describe the Workspace ONE Access directory integration Describe the Workspace ONE Access directory integration Deploy virtual applications with Workspace services Horizon Protocols Compare the remote display protocols that are available in VMware Horizon Describe the BLAST Display Protocol Codecs Describe BLAST and PCoIP ADMX GPO common configurations Graphic Cards Describe the 3D rendering options available in Horizon 8 Compare vSGA and vDGA List the steps to configure graphics cards for use in a VMware Horizon environment Horizon Scalability Describe the purpose of a replica connection server Explain how multiple Horizon Connection Server instances in a pod maintain synchronization Explain Horizon Cloud Pod Architecture LDAP replication and VIPA Explain Horizon Cloud Pod Architecture scalability options Horizon Security Explain concepts relevant to secure Horizon connections Describe how to restrict Horizon connections. Discuss the benefits of using Unified Access Gateway List the two-factor authentication options that are supported by Unified Access Gateway List Unified Access Gateway firewall rules Describe the situation in which you might deploy Unified Access Gateway instances with one, two, or three network interfaces Additional course details:Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware Horizon 8: Deploy and Manage training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware Horizon 8: Deploy and Manage course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

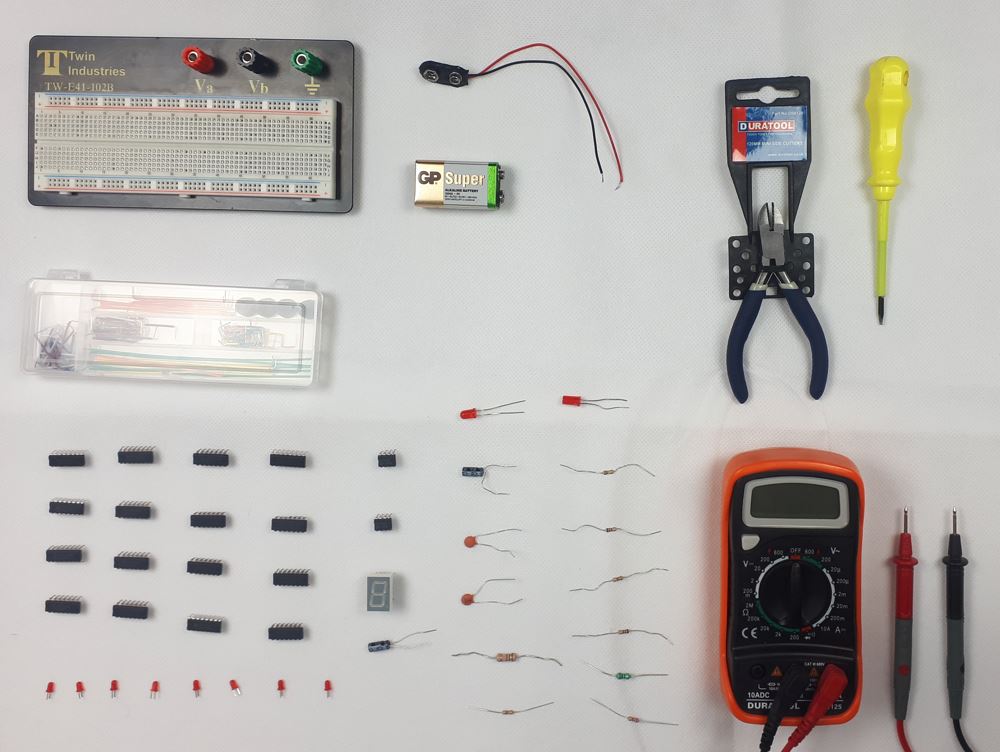
Digital Electronics Course Online
By Hi-Tech Training
This Digital Electronics Course is designed to give practical knowledge of the type of electronic circuitry used in a modern Computer System or in any type of Computer Controlled equipment such as Photocopiers, Cash Registers, Tablets, mobile phones and many other types of IT equipment. Digital Electronics involves the use of Silicon chips (Integrated Circuits). The internal structure of a computer is to a large extent comprised of Digital Electronic Circuits.
Information Assurance (STIG) Overview (TT8800)
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for The intended audience for this comprehensive course on Information Assurance and STIGs includes professionals with roles such as: IT professionals - System administrators, network engineers, and security analysts who are responsible for maintaining and securing IT infrastructure and web applications. Developers - Software engineers and web developers who design, implement, and maintain web applications, and need to integrate security best practices throughout the development process. Project teams - Cross-functional teams that collaborate on application development projects, including members from development, testing, and deployment teams. Technical leads - Senior software engineers or architects who oversee technical aspects of projects and ensure the implementation of secure design and coding practices. Project managers - Professionals responsible for planning, executing, and closing projects, ensuring that security requirements are met throughout the project lifecycle. Overview Working in an interactive learning environment, guided by our application security expert, you'll explore: The concepts and terminology behind defensive coding Threat Modeling as a tool in identifying software vulnerabilities based on realistic threats against meaningful assets The entire spectrum of threats and attacks that take place against software applications in today's world The role that static code reviews and dynamic application testing to uncover vulnerabilities in applications The vulnerabilities of programming languages as well as how to harden installations The basics of Cryptography and Encryption and where they fit in the overall security picture The requirements and best practices for program management as specified in the STIGS The processes and measures associated with the Secure Software Development (SSD) The basics of security testing and planning Understand the concepts and terminology behind defensive coding Understand Threat Modeling as a tool in identifying software vulnerabilities based on realistic threats against meaningful assets Learn the entire spectrum of threats and attacks that take place against software applications in today's world Discuss the role that static code reviews and dynamic application testing to uncover vulnerabilities in applications Understand the vulnerabilities of programming language as well as how to harden installations Understand the basics of Cryptography and Encryption and where they fit in the overall security picture Understand the fundamentals of XML Digital Signature and XML Encryption as well as how they are used within the web services arena Understand the requirements and best practices for program management as specified in the STIGS Understand the processes and measures associated with the Secure Software Development (SSD) Understand the basics of security testing and planning The Information Assurance (STIG) Overview is a comprehensive two-day course that delves into the realm of Information Assurance, empowering you to enhance your cybersecurity skills, understand the essentials of STIGs, and discover cutting-edge web application security practices. This immersive experience is tailored for IT professionals, developers, project teams, technical leads, project managers, testing/QA personnel, and other key stakeholders who seek to expand their knowledge and expertise in the evolving cybersecurity landscape. The course focuses on the intricacies of best practices for design, implementation, and deployment, inspired by the diverse and powerful STIGs, ultimately helping participants become more proficient in application security.The first half of the course covers the foundations of DISA's Security Technical Implementation Guides (STIGs) and learn the ethical approach to bug hunting, while exploring the language of cybersecurity and dissecting real-life case studies. Our expert instrtors will guide you through the importance of respecting privacy, working with bug bounty programs, and avoiding common mistakes in the field.The next half delves into the core principles of information security and application protection, as you learn how to identify and mitigate authentication failures, SQL injections, and cryptographic vulnerabilities. You?ll gain experience with STIG walkthroughs and discover the crucial steps for securing web applications.Throughout the course, you'll also explore the fundamentals of application security and development, including checklists, common practices, and secure development lifecycle (SDL) processes. You?ll learn from recent incidents and acquire actionable strategies to strengthen your project teams and IT organizations. You'll also have the opportunity to explore asset analysis and design review methodologies to ensure your organization is prepared to face future cybersecurity challenges. DISA's Security Technical Implementation Guides (STIGs) The motivations behind STIGs Requirements that the various software development roles must meet Implementing STIG requirements and guidelines Why Hunt Bugs? The Language of CyberSecurity The Changing Cybersecurity Landscape AppSec Dissection of SolarWinds The Human Perimeter Interpreting the 2021 Verizon Data Breach Investigation Report First Axiom in Web Application Security Analysis First Axiom in Addressing ALL Security Concerns Lab: Case Study in Failure Safe and Appropriate Bug Hunting/Hacking Working Ethically Respecting Privacy Bug/Defect Notification Bug Bounty Programs Bug Hunting Mistakes to Avoid Principles of Information Security Secuity Is a Lifecycle Issue Minimize Attack Surface Area Layers of Defense: Tenacious D Compartmentalize Consider All Application States Do NOT Trust the Untrusted Identification and Authentication Failures Applicable STIGs Quality and Protection of Authentication Data Proper hashing of passwords Handling Passwords on Server Side Session Management HttpOnly and Security Headers Lab: STIG Walk-Throughs Injection Applicable STIGs Injection Flaws SQL Injection Attacks Evolve Drill Down on Stored Procedures Other Forms of Server-Side Injection Minimizing Injection Flaws Client-side Injection: XSS Persistent, Reflective, and DOM-Based XSS Best Practices for Untrusted Data Lab: STIG Walk-Throughs Applications: What Next? Common Vulnerabilities and Exposures CWE/SANS Top 25 Most Dangerous SW Errors Strength Training: Project Teams/Developers Strength Training: IT Organizations Cryptographic Failures Applicable STIGs Identifying Protection Needs Evolving Privacy Considerations Options for Protecting Data Transport/Message Level Security Weak Cryptographic Processing Keys and Key Management Threats of Quantum Computing Steal Now, Crack Later Threat Lab: STIG Walk-Throughs Application Security and Development Checklists Checklist Overview, Conventions, and Best Practices Leveraging Common AppSec Practices and Control Actionable Application Security Additional Tools for the Toolbox Strength Training: Project Teams/Developers Strength Training: IT Organizations Lab: Recent Incidents SDL Overview Attack Phases: Offensive Actions and Defensive Controls Secure Software Development Processes Shifting Left Actionable Items Moving Forward Lab: Design Study Review Asset Analysis Asset Analysis Process Types of Application-Related Assets Adding Risk Escalators Discovery and Recon Design Review Asset Inventory and Design Assets, Dataflows, and Trust Boundaries Risk Escalators in Designs Risk Mitigation Options

Learn everything you need to know to be fully competent with Mac iOS. This syllabus takes you around the basics and then on another deep dive into all the elements. Discover things you never knew and speed up your experience using Mac iOS. Module 1: Introduction to Mac iOS and Hardware • Understanding the Mac ecosystem • Overview of Mac hardware components • Navigating the Mac interface Module 2: Mac Operating System (macOS) • Exploring the macOS interface • Customizing system preferences • File management and organization on macOS Module 3: Essential Mac Apps • Using Safari for web browsing • Effective web searching using search engines • Email management with Apple Mail • Calendar and task management with Apple Calendar Module 4: Software Installation and Updates • Installing and updating software applications • Managing and uninstalling programs • App Store and app installations Module 5: Productivity and Collaboration • Using iCloud for cloud-based storage and collaboration • Working with Notes, Reminders, and Messages • Collaborative document editing with iWork Module 6: Multimedia and Creativity • Basic image editing with Photos and Preview • Music creation with GarageBand • Creating multimedia presentations with Keynote Module 7: Troubleshooting and Maintenance • Identifying and resolving common Mac issues • Using Activity Monitor for performance monitoring • Maintenance tasks for macOS Module 8: Mac Security and Privacy • Overview of Mac security features • Online safety and privacy best practices • Protecting personal data and devices Module 9: Advanced Mac Features • Customizing the Dock and Menu Bar • Using Siri for voice commands and search • Continuity features for seamless device integration Module 10: Using AI and Chat GPT • Introduction to AI and Chat GPT technology • Exploring AI-powered features on Mac • Using Chat GPT for productivity and assistance Module 11: Browsing and Search Engines • Effective use of web browsers on macOS • Utilizing search engines for research • Online safety and privacy while browsing Module 12: Cybersecurity • Understanding cybersecurity threats • Protecting against malware and phishing attacks • Secure online practices and password management Module 13: Software Installation and Factory Reset • Installing and updating software applications • Factory resetting a Mac device • Data backup and recovery during resets Module 14: Final Projects and Assessment • Culminating projects showcasing Mac iOS skills • Practical exams assessing Mac software knowledge and skills • Preparing for industry-recognized certifications (optional) Please note that the duration and depth of each module can vary depending on the level of expertise required and the specific needs of the learners. Additionally, it's important to adapt the curriculum to the learners' proficiency levels, whether they are A Level/GCSE students or adult learners with different experience levels.
Microsoft Power BI: Data Analysis Practitioner (Second Edition) (v1.3)
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for This course is designed for professionals in a variety of job roles who are currently using desktop or web-based data management tools such as Microsoft Excel or SQL Server reporting services to perform numerical or general data analysis. They are responsible for connecting to cloud-based data sources, as well as shaping and combining data for the purpose of analysis. They are also looking for alternative ways to analyze business data, visualize insights, and share those insights with peers across the enterprise. This includes capturing and reporting on data to peers, executives, and clients. Overview In this course, you will analyze data with Microsoft Power BI. You will: Analyze data with self-service BI. Connect to data sources. Perform data cleaning, profiling, and shaping. Visualize data with Power BI. Enhance data analysis by adding and customizing visual elements. Model data with calculations. Create interactive visualizations. As technology progresses and becomes more interwoven with our businesses and lives, more data is collected about business and personal activities. This era of 'big data' is a direct result of the popularity and growth of cloud computing, which provides an abundance of computational power and storage, allowing organizations of all sorts to capture and store data. Leveraging that data effectively can provide timely insights and competitive advantages. Creating data-backed visualizations is key for data scientists, or any professional, to explore, analyze, and report insights and trends from data. Microsoft© Power BI© software is designed for this purpose. Power BI was built to connect to a wide range of data sources, and it enables users to quickly create visualizations of connected data to gain insights, show trends, and create reports. Power BI's data connection capabilities and visualization features go far beyond those that can be found in spreadsheets, enabling users to create compelling and interactive worksheets, dashboards, and stories that bring data to life and turn data into thoughtful action. Analyzing Data with Self-Service BI Topic A: Data Analysis and Visualization for Business Intelligence Topic B: Self-Service BI with Microsoft Power BI Connecting to Data Sources Topic A: Create Data Connections Topic B: Configure and Manage Data Relationships Topic C: Save Files in Power BI Performing Data Cleaning, Profiling, and Shaping Topic A: Clean, Transform, and Load Data with the Query Editor Topic B: Profile Data with the Query Editor Topic C: Shape Data with the Query Editor Topic D: Combine and Manage Data Rows Visualizing Data with Power BI Topic A: Create Visualizations in Power BI Topic B: Chart Data in Power BI Enhancing Data Analysis Topic A: Customize Visuals and Pages Topic B: Incorporate Tooltips Modeling Data with Calculations Topic A: Create Calculations with Data Analysis Expressions (DAX) Topic B: Create Calculated Measures and Conditional Columns Creating Interactive Visualizations Topic A: Create and Manage Data Hierarchies Topic B: Filter and Slice Reports Topic C: Create Dashboards Additional course details: Nexus Humans Microsoft Power BI: Data Analysis Practitioner (Second Edition) (v1.3) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Microsoft Power BI: Data Analysis Practitioner (Second Edition) (v1.3) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

VMware Horizon 8: Deploy and Manage plus App Volumes Fast Track
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Operators, administrators, and architects for VMware Horizon should enroll in this course. These individuals are responsible for the creation, maintenance, or delivery of remote and virtual desktop services. Additional duties can include the implementation, support, and administration of an organization's end-user computing infrastructure. Overview By the end of the course, you should be able to meet the following objectives: Recognize the features and benefits of VMware Horizon Use VMware vSphere to create VMs to be used as desktops for VMware Horizon Create and optimize Windows VMs to create VMware Horizon desktops Install and configure Horizon Agent on Horizon desktop Configure and manage the VMware Horizon Client⢠systems and connect the client to a VMware Horizon desktop Configure, manage, and entitle desktop pools of full VMs Configure, manage, and entitle pools of instant-clone desktops Create and use Remote Desktop Services (RDS) desktops and application pools Monitor the VMware Horizon environment using Horizon Console Dashboard and Horizon Help Desk Tool Identify Horizon Connection Server installation, architecture, and requirements. Describe the authentication and certification options for a VMware Horizon environment Recognize the integration process and benefits of VMware Workspace ONE Access⢠and Horizon 8 Discuss performance and scalability options available in Horizon 8 Describe different security options for the Horizon environment Describe the features and functions of App Volumes and Dynamic Environment Manager Demonstrate the architectures of App Volumes and Dynamic Environment Manager Install and configure App Volumes Create and deploy Application Packages and writable volumes Install and configure Dynamic Environment Manager Manage application configurations, user environment settings, and personalization settings This five-day accelerated, hands-on training course is a blend of VMware Horizon© 8: Skills for Virtual Desktop Management, VMware Horizon 8: Infrastructure Administration, and VMware App Volumes?, and VMware Dynamic Environment Manager?. Eight days of content are taught in five-days of extending learning.This training collection gives you the hands-on skills to deliver virtual desktops and applications through a single virtual desktop infrastructure platform. You build on your skills in configuring and managing VMware Horizon 8 through a combination of lecture and hands-on labs. You learn how to configure and deploy pools of virtual machines and how to provide a customized desktop environment to end-users.You learn how to install and configure a virtual desktop infrastructure platform. You learn how to install and configure VMware Horizon© Connection Server? and VMware Unified Access Gateway?. You also learn how to configure a load balancer for use with Horizon and how to establish Cloud Pod Architecture.Additionally, you learn how to use App Volumes to deliver applications and data to desktops and users in seconds and at scale. You gain skills in managing application life cycles from installation to update and replacement. You also learn how to use Dynamic Environment Manager to provide personalization and dynamic policy configuration across virtual, physical, and cloud-based environments to simplify end-user profile management. Course Introduction Introductions and course logistics Course objectives Introduction to VMware Horizon Recognize the features and benefits of Horizon Describe the conceptual and logical architecture of VMware Horizon Introduction to Use Case Define a use case for your virtual desktop and application infrastructure Convert customer requirements to use-case attributes vSphere for Horizon 8 Explain basic virtualization concepts Use vSphere Client to access your vCenter Server system and VMware ESXi? hosts Create, provision, and remove a virtual machine VMware Horizon Desktops Create a Windows and a Linux virtual machine using vSphere Optimize and prepare Windows and Linux virtual machines to set up VMware Horizon desktop VMs VMware Horizon Agents Outline the configuration choices when installing Horizon Agent on Windows and Linux virtual machines Create a gold master for Windows Horizon desktops VMware Horizon Pools Identify the steps to set up a template for desktop pool deployment List the steps to add desktops to the Horizon Connection Server inventory Compare dedicated-assignment and floating-assignment pools Outline the steps to create an automated pool Define user entitlement Explain the hierarchy of global, pool-level, and user-level policies VMware Horizon Client Options Describe the different clients and their benefits Access the VMware Horizon desktop using various VMware Horizon clients and HTML Configure integrated printing, USB redirection, and the shared folders option Configure session collaboration and media optimization for Microsoft Teams Creating and Managing Instant-Clone Desktop Pools List the advantages of instant clones Explain the provisioning technology used for instant-clone desktop pools Set up an automated pool of instant clones Push updated images to instant-clone desktop pools Creating RDS Desktop and Application Pools Explain the difference between an RDS desktop pool and an automated pool Compare and contrast an RDS session host pool, a farm, and an application pool Create an RDS desktop pool and an application pool Access RDS desktops and application from Horizon Client Use the instant clone technology to automate the build-out of RDSH farms Configure load-balancing for RDSHs on a farm Monitoring VMware Horizon Monitor the status of the VMware Horizon components using the Horizon Administrator console dashboard Monitor desktop sessions using the HelpDesk tool Horizon Connection Server Recognize VMware Horizon reference architecture Identify the Horizon Connection Server supported features Identify the recommended system requirements for Horizon Connection Server Configure the Horizon event database Outline the steps for the initial configuration of Horizon Connection Server Discuss the ADAM database as a critical component of the Horizon Connection Server installation VMware Horizon Authentication and Certificates Compare the authentication options that Horizon Connection Server supports Describe the Smartcard authentication options that Horizon Connection Server supports Outline the steps to create a VMware Horizon administrator and custom roles Describe the roles available in a VMware Horizon environment Explain the role that certificates play for Horizon Connection Server Install and configure certificates for Horizon Connection Server Install and configure True SSO in a VMware Horizon environment Workspace ONE Access and Virtual Application Management Recognize the features and benefits of Workspace ONE Access Recognize the Workspace ONE Access console features Explain identity management in Workspace ONE Access Explain access management in Workspace ONE Access Describe the Workspace ONE Access directory integration Describe the Workspace ONE Access directory integration Deploy virtual applications with Workspace services VMware Horizon Performance and Scalability Describe the purpose of a replica connection server Explain how multiple Horizon Connection Server instances in a pod maintain synchronization Describe the 3D rendering options available in VMware Horizon 8 List the steps to configure graphics cards for use in a VMware Horizon environment Configure a load balancer for use in a VMware Horizon environment Explain Horizon Cloud Pod Architecture LDAP replication and VIPA Explain Horizon Cloud Pod Architecture scalability options Managing VMware Horizon Security Explain concepts relevant to secure VMware Horizon connections Describe how to restrict VMware Horizon connections. Discuss the benefits of using Unified Access Gateway List the two-factor authentication options that are supported by Unified Access Gateway List Unified Access Gateway firewall rules Describe the situation in which you might deploy Unified Access Gateway instances with one, two, or three network interfaces Overview of Application and Profile Management Profile Management Application Management Overview of App Volumes App Volumes components App Volumes Installation Overview Requirements Installing and configuring App Volumes Manager Installing the App Volumes agent Working with Application Packages Packaging Applications Maintaining Applications Working with Writable Volumes Default writable volume templates Writable volume policies at creation Updating and rescanning writable volumes Working with AppStacks Enabling AppStacks Creating and provisioning AppStacks Assigning and updating AppStacks Overriding precedence in AppStacks Overview of Dynamic Environment Manager Features and benefits VMware Dynamic Environment Manager terminology User environment settings and scope User profile scenarios Install VMware Dynamic Environment Manager Infrastructure and system requirements VMware Dynamic Environment Manager Agent (FlexEngine) requirements Group Policy configuration Management Console configuration Management Console User Interface Personalize User Profile User environment configuration Application Configuration Management Predefined and user-customized application settings Using Application Profiler Using the Self-Support Tool Using the Helpdesk Support Tool VMware Horizon Smart Policies Scope of VMware Horizon Smart Policies Configure VMware Horizon Smart Policies settings Define Smart Policies conditions Additional course details:Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware Horizon 8: Deploy and Manage plus App Volumes Fast Track training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware Horizon 8: Deploy and Manage plus App Volumes Fast Track course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
