- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
6022 Computing & IT courses
ITIL 4 Specialist: Drive Stakeholder Value: Virtual In-House Training
By IIL Europe Ltd
ITIL® 4 Specialist: Drive Stakeholder Value: Virtual In-House Training The ITIL® 4 Specialist: Drive Stakeholder Value module is part of the Managing Professional stream for ITIL 4. Candidates need to pass the related certification exam for working towards the Managing Professional (MP) designation. This course is based on the ITIL® 4 Specialist: Drive Stakeholder Value exam specifications from AXELOS. With the help of ITIL® 4 concepts and terminology, exercises, and examples included in the course, candidates acquire the relevant knowledge required to pass the certification exam. What You Will Learn The learning objectives of the course are based on the following learning outcomes of the ITIL® 4 Specialist: Drive Stakeholder Value exam specification: Understand how customer journeys are designed Know how to target markets and stakeholders Know how to foster stakeholder relationships Know how to shape demand and define service offerings Know how to align expectations and agree on details of services Know how to onboard and offboard customers and users Know how to act together to ensure continual value co-creation (service consumption / provisioning) Know how to realize and validate service value Customer Journey Purpose of the Module Purpose of Mastering the Customer Journey Touchpoints and Service Interactions Module Topics Mapping the Customer Journey Designing the Customer Journey Measuring and Improving the Customer Journey Customer Journey Step 1: Explore Purpose of the Module Purpose of the Explore Step Module Topics Understanding Service Consumers Understanding Service Providers Understanding and Targeting Markets Customer Journey Step 2: Engage Purpose of the Module Purpose of the Engage Step Aspects of Service Value Module Topics Service Relationship Types Building Service Relationships Building and Sustaining Trust and Relationships Analyzing Customer Needs Managing Suppliers and Partners Customer Journey Step 3: Offer Purpose of the Module Purpose of Shaping Demand and Service Offerings Module Topics Managing Demand and Opportunities Specifying and Managing Customer Requirements Designing Service Offerings and User Experience Selling and Obtaining Service Offerings Customer Journey Step 4: Agree Purpose of the Module Purpose of Aligning Expectations and Agreeing on Services Module Topics Agreeing on and Planning Value Co-Creation Negotiating and Agreeing on a Service Customer Journey Step 5: Onboard Purpose of the Module Purpose of Onboarding and Offboarding ITIL® Management Practices Module Topics Planning Onboarding Fostering Relationships with Users Providing User Engagement and Delivery Channels Enabling Users for Service Elevating Mutual Capabilities Offboarding Customer Journey Step 6: Co-create Purpose of the Module Purpose of Service Provision and Consumption Module Topics Service Mindset Ongoing Service Interactions Nurturing User Communities Customer Journey Step 7: Realize Purpose of the Module Measuring Service Value Purpose of Value Capturing and Customer Journey Improvement Realizing Service Value in Different Settings Module Topics Tracking Value Realization Assessing and Reporting Value Realization Evaluating Value Realization and Improving Customer Journeys Realizing Value for the Service Provider

55133 PowerShell for System Center Configuration Manager Administrators
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This course is intended for IT professionals who need to manage the day-to-day environment of an SCCM 2012 SP1 or newer environment. Knowledge of the workings of a standalone primary SCCM site and basic PowerShell experience is recommended. Overview Create additional site system roles on existing or new servers. Modify high level site settings. Create and modify Discovery Methods, Boundaries and Boundary Groups. Create Collections using any of the membership rules available. Delegate authority through Roles and Scopes. Install the Configuration Manager client, modify client settings and restrict access to site systems. Deploy software to clients. Deploy software updates to clients. Configure compliance settings targeted against collections. Modify settings that govern monitoring functions such as Alerts and Status Settings. Work with Task Sequences for Operating System Deployment. Write basic PowerShell scripts using cmdlets learned and scripting constructs to accomplish configuration tasks. This course provides students with the knowledge and skills needed to use PowerShell for System Center Configuration Manager (SCCM) administration. In this course, students learn how to access the PowerShell cmdlets included with SCCM 2012 R2 and use them to perform configuration tasks for a primary site. Individual cmdlets will be used in working with objects such as Boundaries, Boundary Groups, Collections, Software Deployment, Patching, Compliance Settings, OSD Task Sequences, and many others. Basic scripting will also be covered so that students can learn how to put PowerShell to use when working with large sets of objects. Prerequisites Basic Windows and Active Directory knowledge. Conceptual knowledge of Configuration Manager objects and how they interact. Basic experience performing configuration tasks in ECM using the graphical console. Experience working from a command prompt. Basic knowledge of the fundamentals of Windows PowerShell. 1 - REVIEW OF SYSTEM CENTER CONFIGURATION MANAGER CONCEPTS Architecture of an System Center 2012 Configuration Manager Installation Managing Assets Content Delivery and Management Security, Monitoring, and Remote Management 2 - MANAGING RESOURCES Implementing Discovery Organizing Resources with Collections Working with Boundaries 3 - WORKING WITH CLIENTS Installing the Configuration Manager Client Managing Client Settings Managing Client Operations Monitoring Client Status 4 - DISTRIBUTING SOFTWARE Configure the Software Distribution Components Working with Distribution Points Creating Content for Distribution Deploying Software Applications 5 - UPDATING SYSTEMS WITH WSUS AND SCCM Integrating Configuration Manager and WSUS Managing Updates through Software Update Groups Creating and Deploying Update Packages Working with Automatic Deployment Rules 6 - HOW POWERSHELL CAN MANAGE COMPLIANCE SETTINGS Creating Compliance Settings Objects Deploying and Monitor the Baseline 7 - CONFIGURING OPERATING SYSTEM DEPLOYMENT OBJECTS Preparing the OSD Environment Working with Task Sequences 8 - WORKING AT THE SITE LEVEL Modify the Site Adding Site System Roles Adding a Secondary Site 9 - SECURITY AND MONITORING Configuring Role Based Administration Implementing Endpoint Protection Configuring Monitoring Options 10 - USING POWERSHELL SCRIPTING TO AUTOMATE SCCM TASKS Review of Scripting Constructs Introduction to the Configuration Manager WMI Classes

NCSP 800-171 Specialist
By IIL Europe Ltd
The NCSP® 800-171 Specialist accredited (APMG International), certified (NCSC/GCHQ-UK), and recognized (DHS-CISA-USA) certification course teaches Digital Business, Operational Stakeholders, Auditors, and Risk Practitioners a Fast-Track approach to adopting and adapting the 800-171 controls in the context of a NIST Cybersecurity Framework program. This course looks at the impact of adapting a principled approach to the enterprise risk management (ERM) framework to better support cybersecurity decisions, establishing the context for the selected informative reference (IR). It guides participants on the best approach to adapting, implementing, and operating (AIO) a comprehensive cybersecurity program that can be integrated into the existing organizational capabilities and incorporates the selected IR. NCSP® 800-171 Specialist introduces the integration of typical enterprise capabilities with cybersecurity from the selected cybersecurity IR perspective. The overall approach places these activities into a systems-thinking context by introducing the service value management system (SVMS), including governance, assurance, and the Z-X model. With this in place, the course presents the approach to adapt, implement, operate, and improve the organizational cybersecurity posture that builds on the application of the FastTrack™ concept presented in the NCSP Practitioner course. The NIST Cybersecurity Professional (NCSP®) program is the industry's first accredited certification training program that teaches organizations how to build a Digital Value Management Overlay System capable of leveraging the NIST Cybersecurity Framework to deliver the secure, digital business outcomes expected by executives, government regulators, and legal advisors.

Mac Support for PC Technicians
By Influential Training
Mac Support for PC, PC and Mac Support, PC to Mac support

IT: CompTIA with Cyber Security Career Oriented Job Focused Program - Money Back Guarantee
4.9(27)By Apex Learning
Defend, Excel, Succeed: Unleash Your Potential with IT: CompTIA with Cyber Security program. Dive into IT excellence and cyber resilience with our exclusive IT: CompTIA with Cyber Security program. Elevate your career prospects and knowledge with our comprehensive curriculum to pave the way for success. Our IT: CompTIA with Cyber Security program is a stepping stone, guiding you toward a fulfilling career. With technology shaping industries, the demand for skilled professionals is at an all-time high. This program, spanning multiple courses, is tailored to equip you with the expertise employers demand across diverse sectors. Delve into cutting-edge subjects such as CompTIA A+, Cloud Computing, Cybersecurity Analyst, PenTest+, and more. Moreover, we're your dedicated partners in this exciting IT: CompTIA with Cyber Security program. Our goal isn't just to teach you; it's to support you 24/7 so you can get closer to your dream job. We're so confident with our program that we offer a 100% money-back guarantee, ensuring your complete satisfaction. Learning Outcomes: By completing this IT: CompTIA with Cyber Security program, you will gain the following: Master CompTIA A+ essentials (220-1001 and 220-1002). Understand Cloud Computing principles (CompTIA Cloud+). Analyse and counteract cybersecurity threats (CompTIA CySA+). Conduct ethical hacking with CompTIA PenTest+. Attain a robust grasp of IT fundamentals and networking. Excel in Linux systems and Bash scripting. Develop skills in incident handling and response. Cultivate cyber awareness through online courses Explore Linux & ethical hacking using Kali Linux Master Bash scripting, Linux, and shell programming Become a skilled IT support technician Progress to network security level 2 & functional IT skills Craft a compelling CV and master job searching Ace interviews with expert guidance Navigate video job interviews effectively Create a standout LinkedIn profile Courses Included in the Program Enrol in our IT: CompTIA with Cyber Security program and gain access to a 25 comprehensive set of courses, including: => Course 01: CompTIA A+ (220-1001) => Course 02: CompTIA A+ (220-1002) => Course 03: Cloud Computing / CompTIA Cloud+ (CV0-002) => Course 04: CompTIA CySA+ Cybersecurity Analyst (CS0-002) => Course 05: CompTIA PenTest+ (Ethical Hacking) => Course 06: CompTIA Security+ (SY0-601) => Course 07: CompTIA IT Fundamentals ITF+ (FCO-U61) => Course 08: CompTIA Networking - Level 4 => Course 09: CompTIA Healthcare IT Technician => Course 10: Cyber Security Incident Handling and Incident Response => Course 11: Cyber Security Advanced Training => Course 12: Cyber Security Awareness Training | Online Course => Course 13: Learn Linux in 5 Days => Course 14: Ethical Hacking with Kali Linux => Course 15: Bash Scripting, Linux and Shell Programming => Course 16: IT Support Technician Training => Course 17: Network Security Level 2 => Course 18: Functional Skills IT => Course 19: Data Protection and Data Security Level 2 => Course 20: Learning Computers and Internet Level 2 => Course 21: Career Development Plan Fundamentals => Course 22: CV Writing and Job Searching => Course 23: Interview Skills: Ace the Interview => Course 24: Video Job Interview for Job Seekers => Course 25: How to Create a Professional LinkedIn Profile Enrol in our highly regarded IT: CompTIA with Cyber Security program, featuring a job-relevant curriculum that ensures your skills align with employer expectations across various sectors. Don't miss this opportunity - your success story starts now! For any query, please feel free to contact us, and we will be glad to assist you. Venture on a transformative journey through our IT: CompTIA with Cyber Security program, meticulously crafted to empower you with cutting-edge IT skills and cybersecurity expertise. Elevate your career prospects with a curriculum designed to meet industry demands, providing a comprehensive understanding of the IT landscape. Why Choose Us? What sets us apart is our unwavering commitment to your success. Here's what you gain by joining our IT: CompTIA with Cyber Security program: Updated Materials: Stay current with industry trends: Our IT: CompTIA with Cyber Security program ensures you have access to the most up-to-date materials, guaranteeing a curriculum that reflects the latest technological advancements. Dive into the cutting-edge knowledge that empowers you to navigate the dynamic IT terrain confidently, equipping you for success in the fast-paced world of information technology. Flexible Timing: Learn at your own pace:Life can be unpredictable, but your learning journey doesn't have to be. Flexibility is critical with our IT: CompTIA with Cyber Security program. Learn at your own pace, whether you're a full-time professional, a student, or someone managing various commitments. Our program adapts to your schedule, allowing you to delve into the intricacies of IT and cyber security without compromising your existing responsibilities. No Hidden Cost: Certification and course materials are inclusive. Transparency is the cornerstone of our IT: CompTIA with Cyber Security program. We believe in providing a seamless learning experience without any financial surprises. Your enrollment covers the comprehensive certification process and all necessary course materials. Say goodbye to hidden costs and embrace a straightforward, all-inclusive educational journey. Money-Back Guarantee: Enjoy peace of mind within 14 days: With our IT: CompTIA with Cyber Security program, your peace of mind is our priority. Take the first two weeks to explore the curriculum and experience the quality of our offerings. If, for any reason, you feel this program isn't the right fit for you, enjoy the reassurance of our 100% money-back guarantee within 14 days of enrollment. Lifetime Access: Continued learning at your fingertips:Our commitment to your growth extends beyond completing the program. Enrol in IT: CompTIA with Cyber Security and gain lifetime access to course materials and updates. Keep your knowledge current, revisit critical concepts, and stay connected to the ever-evolving world of IT. Your journey doesn't end; it evolves with you. 24/7 Support: Assistance whenever you need it:Our IT: CompTIA with Cyber Security program provides 24/7 support, ensuring that assistance is readily available whenever you need it. Whether you have questions about the curriculum, encounter technical issues, or seek guidance on your learning path, our dedicated support team is just a message away, ready to provide the help you need. CPD 250 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This IT: CompTIA with Cyber Security program is for individuals who are: Aspiring IT professionals. Seeking to specialise in cybersecurity. Eager to enhance networking skills. Wishing to enter the healthcare IT sector. Interested in ethical hacking and penetration testing. Requirements No prior experience is required to enrol in IT: CompTIA with Cyber Security program. Career path Upon completion of IT: CompTIA with Cyber Security program, explore a multitude of career paths, including: Cybersecurity Analyst: £30,000 - £50,000 IT Support Technician: £25,000 - £40,000 Cloud Computing Specialist: £35,000 - £55,000 Network Security Specialist: £30,000 - £50,000 Healthcare IT Technician: £28,000 - £45,000 Linux Systems Administrator: £35,000 - £60,000 Certificates CPD Accredited (e-Certificate) Digital certificate - Included CPD Accredited (Hard Copy Certificate) Hard copy certificate - Included e-Transcript Digital certificate - Included Hard Copy Transcript Hard copy certificate - Included Student ID Card Digital certificate - Included

QLS Endorsed Game Developer Bundle
By Imperial Academy
Game development is a symphony of code, graphics, and creativity, culminating in an epic journey for the player

Web Developer QLS Endorsed Bundle
By Imperial Academy
10 QLS Endorsed Courses for Web Developer | 10 Endorsed Certificates Included | Lifetime Access | Tutor Support

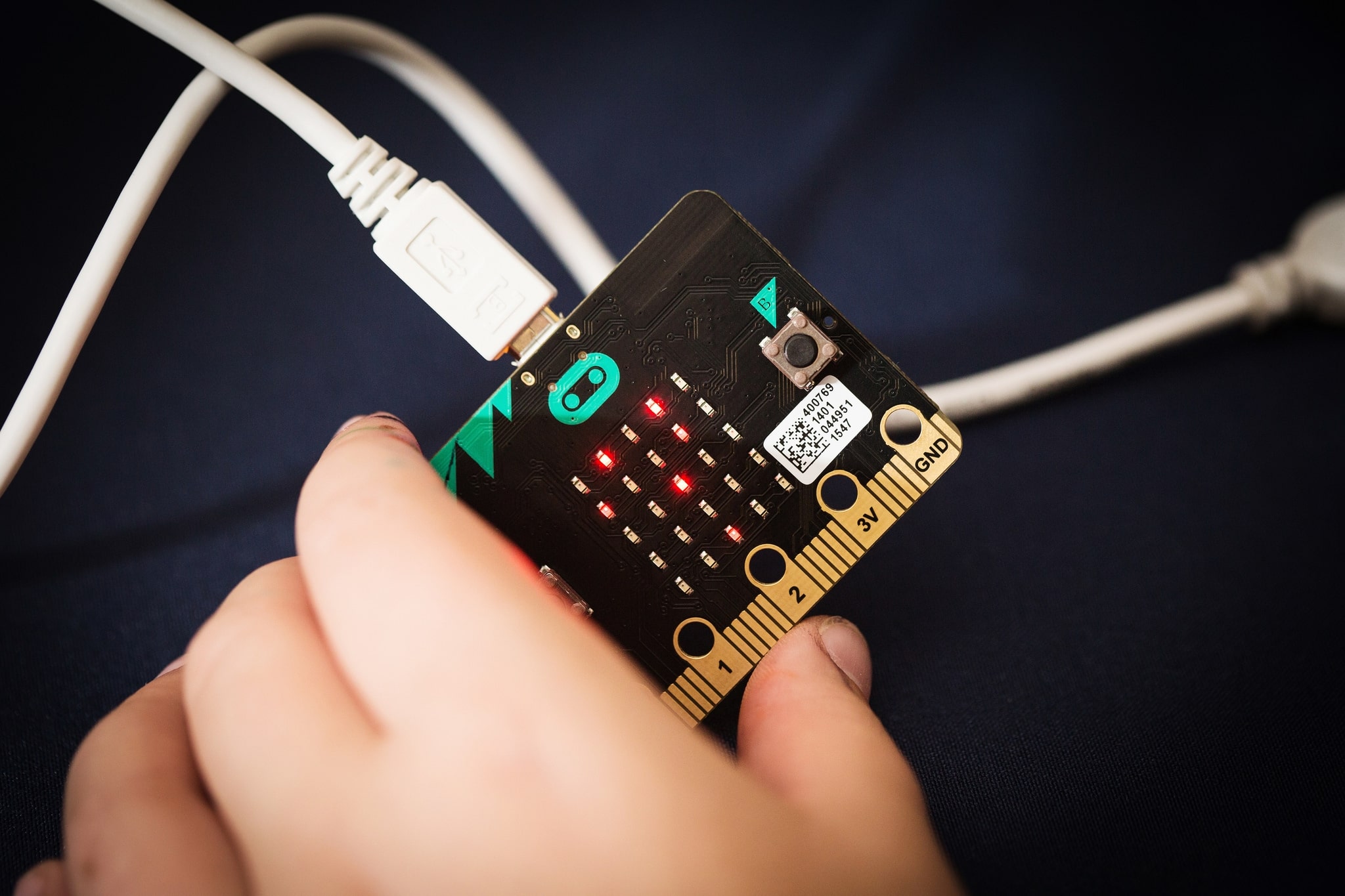
BBC micro:bit Coding Workshop
By Code Created (Coding Workshops for Schools)
For pupils aged 9 - 16 | Delivered in UK Schools by Real World App and Games Developers Our micro:bit Workshop teaches your class about the micro:bit, making some apps and games with them during the workshop (we bring our own micro:bits too if your school doesn't yet have any!). We’ll introduce them to MakeCode, the coding language that the micro:bit uses, and teach them the fundamentals of coding before we work on some really fun projects! For older students, we can even use Python with the micro:bit!
PL-100T00 Microsoft Power Platform App Maker
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for The App Maker builds solutions to simplify, automate, and transform tasks and processes for themselves and their team where they have deep expertise in the solution business domain. They have basic data modeling, user experience design, requirements analysis, and process analysis skills. The App Maker creates and enforces business processes, structures digital collection of information, improves efficiency of repeatable tasks, and automates business processes. The App Maker uses the Maker tools of Power Platform to solve business problems. They may use advanced features of Microsoft apps and third-party productivity tools. The App Maker is aware of the capabilities and limitations of available tools and understands how to apply them. The App Maker is self-directed, and solution focused. They may not have formal IT training but are comfortable using technology to solve business problems with a personal growth mindset. They understand the operational need and have a vision of the desired outcome. They approach problems with phased and iterative strategies. This course will teach you how to build apps with low-code techniques to simplify, automate, and transform business tasks and processes using Microsoft Power Platform. This course contains a 1-day Applied Workshop. This workshop will allow you to practice your App Maker skills by creating an end-to-end solution to solve a problem for a fictitious company. The solution will include a Microsoft Dataverse database, Power Apps canvas app, and Power Automate flows. 1 - Get started with Microsoft Power Platform for app makers Identify components Create apps Get started with Microsoft Dataverse Work with Copilot in Microsoft Power Platform 2 - Create tables in Dataverse Table characteristics Table relationships Dataverse logic and security Dataverse auditing Dual-write vs. virtual tables 3 - Create and manage columns within a table in Dataverse Define columns in Microsoft Dataverse Column types in Microsoft Dataverse Add a column to a table Primary name column Restrictions that apply to columns in a table Create an auto numbering column Create an alternate key 4 - Load/export data and create data views in Dataverse View data in a table Create or edit views of data in a table Dataverse data import options Load data into a table Dataverse data export options Export Add, update, or delete data in a table by using Excel Import data using Power Query 5 - Export data from Dataverse and use Microsoft Excel to edit records Export data to Excel Edit and update data in Excel 6 - Get started with Microsoft Dataverse for Teams Dataverse for Teams vs Dataverse Provision your first Dataverse environment Create your first table to store data 7 - Build your first app with Power Apps and Dataverse for Teams Create your first app with the hero template Customize your app with Power Apps Studio Publish your app Install template apps 8 - Build your first workflow with Power Automate and Dataverse for Teams Types of workflows that Power Automate can build in Dataverse Schedule a flow 9 - Create reports with Power BI and Dataverse for Teams Connect to and transform Dataverse for Teams data from Power BI Create a Power BI report Publish the report Share the data 10 - Get started building with Power BI Use Power BI Building blocks of Power BI Tour and use the Power BI service 11 - Explore what Power BI can do for you What can I do with the Power BI service as a consumer? View content in the Power BI service Collaborate and share in Power BI Find and view dashboards and reports 12 - Create and manage workspaces in Power BI Distribute a report or dashboard Monitor usage and performance Recommend a development life cycle strategy Troubleshoot data by viewing its lineage Configure data protection 13 - Manage semantic models in Power BI Use a Power BI gateway to connect to on-premises data sources Configure a semantic model scheduled refresh Configure incremental refresh settings Manage and promote semantic models Troubleshoot service connectivity Boost performance with query caching (Premium) 14 - Create dashboards in Power BI Configure data alerts Explore data by asking questions Review Quick insights Add a dashboard theme Pin a live report page to a dashboard Configure a real-time dashboard Set mobile view 15 - Implement row-level security Configure row-level security with the static method Configure row-level security with the dynamic method 16 - Create dashboards in Power BI Configure data alerts Explore data by asking questions Review Quick insights Add a dashboard theme Pin a live report page to a dashboard Configure a real-time dashboard Set mobile view 17 - Secure, publish, and share data in Power BI Share and use reports in Power BI Row-level security Publish a report to a Power BI workspace Share reports and user experience Protect data in Power BI Data refresh and alerts 18 - Embed Power BI content Embed Power BI reports Embed other Power BI content types Optimize the embedding experience 19 - How to build your first model-driven app with Dataverse Model-driven apps, powered by Microsoft Dataverse Explore sample apps 20 - Get started with model-driven apps in Power Apps Introducing model-driven apps Components of model-driven apps Design model-driven apps Incorporate business process flows 21 - Configure forms, charts, and dashboards in model-driven apps Forms overview Form elements Configure multiple forms Use specialized form components Configure views overview Configure grids Create and edit views Configure charts overview Dashboards overview Use interactive streams and tiles 22 - Manage Dynamics 365 model-driven app settings and security Configure role-based security Manage teams and business units Explore settings and customizations 23 - Use specialized components in a model-driven form Create business process flows Embed a canvas app in a model-driven form Add a timeline in a model-driven form Create a report in a model-driven form 24 - Get started with Power Apps canvas apps Start Power Apps Power Apps data sources Use Power Apps with Power Automate and Power BI Designing a Power Apps app 25 - Customize a canvas app in Power Apps Improve your app by making basic customizations Explore controls and screens in canvas apps 26 - How to build the User Interface in a canvas app in Power Apps Use themes to quickly change the appearance of your app Brand a control Icons Images Personalization Build for phones or tablets 27 - Navigation in a canvas app in Power Apps Understanding navigation The Navigate and Back functions More ways to use the Navigate function 28 - Manage apps in Power Apps Power Apps review 29 - Build a mobile-optimized app from Power Apps Learn about mobile-optimized apps Identify components to make a canvas app mobile-optimized Create a mobile-optimized app that uses responsive designs Identify performance considerations for a mobile-optimized canvas app 30 - Use and understand Controls in a canvas app in Power Apps Core properties of controls Entering and displaying data with text controls Additional controls for enhancing your app's usability Media Modern controls Work with component libraries 31 - Create formulas to change properties in a Power Apps canvas app Formulas overview Use a formula to modify the format of controls Use formulas to perform calculations Use a control to modify the property of other controls Conditional formatting Functions for validating data 32 - Use imperative development techniques for canvas apps in Power Apps Imperative versus declarative development The three types of variables in Power Apps Global variables Contextual variables Collections Additional variable concepts 33 - Manage apps in Power Apps Power Apps review 34 - Create formulas to change properties in a Power Apps canvas app Formulas overview Use a formula to modify the format of controls Use formulas to perform calculations Use a control to modify the property of other controls Conditional formatting Functions for validating data 35 - Create formulas to change behaviors in a Power Apps canvas app Formulas and functionality Understanding true and false Understanding control behaviors and actions Performing multiple actions in a formula Control the display mode through a formula Use controls and functions to create a dynamic formula 36 - Author a basic formula that uses tables and records in a Power Apps canvas app Records and tables Using the Table function Store a table Filter your table Use the lookup function to return a record Additional table functions 37 - Build a canvas app for a real estate solution with Copilot in Power Apps 38 - Get started with Power Automate Introducing Power Automate Create your first flow Troubleshoot flows 39 - Build approval flows with Power Automate Provide solutions to real-world scenarios. 40 - Build flows to manage user information 41 - Power Automate's deep integration across multiple data sources 42 - Use the Admin center to manage environments and data policies in Power Automate Administer flows Export and import flows Learn how to distribute button flows 43 - Use AI Builder in Power Automate AI Builder in Power Automate saves time Advanced usage of AI Builder in Power Automate 44 - Optimize your business process with process advisor Get familiar with process advisor Create your first recording Edit recordings and group actions Analyze recordings and interpret results Automation recommendations 45 - Optimize your business process with process advisor Get familiar with process advisor Create your first recording Edit recordings and group actions Analyze recordings and interpret results Automation recommendations 46 - Build flows for a real estate solution using Copilot in Power Automate When to use Copilot in Power Automate 47 - Use Dataverse triggers and actions in Power Automate Dataverse triggers Query data Create, update, delete, and relate actions 48 - Create tables in Dataverse Table characteristics Table relationships Dataverse logic and security Dataverse auditing Dual-write vs. virtual tables 49 - Create and manage columns within a table in Dataverse Define columns in Microsoft Dataverse Column types in Microsoft Dataverse Add a column to a table Primary name column Restrictions that apply to columns in a table Create an auto numbering column Create an alternate key 50 - Get started with Power Apps canvas apps Start Power Apps Power Apps data sources Use Power Apps with Power Automate and Power BI Designing a Power Apps app 51 - How to build the User Interface in a canvas app in Power Apps Use themes to quickly change the appearance of your app Brand a control Icons Images Personalization Build for phones or tablets 52 - Get started with Power Automate Introducing Power Automate Create your first flow Troubleshoot flows 53 - Challenge Project - Build a booking requests app with Power Apps and Power Automate Prepare

Jamf 240 Course: Apple device management with Jamf School
By Influential Training
Jamf training, Jamf 240 course, Jamf course

Search By Location
- Computing & IT Courses in London
- Computing & IT Courses in Birmingham
- Computing & IT Courses in Glasgow
- Computing & IT Courses in Liverpool
- Computing & IT Courses in Bristol
- Computing & IT Courses in Manchester
- Computing & IT Courses in Sheffield
- Computing & IT Courses in Leeds
- Computing & IT Courses in Edinburgh
- Computing & IT Courses in Leicester
- Computing & IT Courses in Coventry
- Computing & IT Courses in Bradford
- Computing & IT Courses in Cardiff
- Computing & IT Courses in Belfast
- Computing & IT Courses in Nottingham