- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
20687 Basic courses
Negotiation skills (In-House)
By The In House Training Company
Any successful business manager will tell you that you never get the deal you deserve - you always get the deal you negotiate! This two-day workshop includes recent research and practical techniques from the Harvard Business School Negotiation Project and provides a unique opportunity to learn and practice these skills in a safe environment using up to date materials and life-like practice negotiation case studies. This course will help participants to: Understand the basics of negotiation Develop negotiating skills Increase their business acumen Develop their communication skills Learn the models, techniques and tools for an effective negotiation Identify the barriers to agreements Close the deal 1 What is negotiation? Key skills for negotiation Types of negotiation Win-lose negotiations versus Win-win negotiations Wise agreements and Principled Negotiation 2 Four key negotiating concepts BATNA - Best alternative to negotiated agreement Setting your reservation price ZOPA - Zone of possible agreement Creating and trading value 3 Business acumen Understanding pricing, gross margins and profit Knowing the key points on which to negotiate 4 A Four Phase Model for negotiation Nine steps to successful planning Discussing a deal - creating and claiming value Making and framing proposals Bargaining for the winning deal 5 Effective communication Effective questioning Active listening skills Understanding and interpreting body language Barriers to effective communication 6 Understanding influence and persuasion Influencing strategies Ten proven ways to influence people Six universal methods of persuasion Understanding why people do business with other people 7 Negotiating tactics Tactics for win-lose negotiations Tactics for win-win negotiations Effective team negotiating Understanding and using powerv What do you do when the other side has more power? 8 Barriers to agreement Common barriers to agreement The Negotiators Dilemma Dealing with die-hard negotiators Dealing with lack of trust 9 Potential barriers to cross-border agreements Understanding business methods and practice in other cultures Figuring out who has the power and who makes decisions Recognising and dealing with cultural differences What's OK here might not be OK there 10 Closing the deal Four steps to closing the winning deal

Commercial instinct (In-House)
By The In House Training Company
An insightful, enjoyable and experiential programme to help you analyse data and information and make a balanced decision based upon sound commercial reasoning. It will enable you to identify options, make decisions and take actions based on a thorough analysis combined with instinct and intuition to make a positive effect on profitability. This programme will help you: Identify ways to analyse data and sort relevant from irrelevant information Develop analytical and numerate thinking, and consider the financial implications of a decision Make decisions based on sound commercial reasoning - a mix of intuition and analysis Select from a range of tools to analyse a situation and apply these effectively Understand how costs and profits are calculated Use tried-and-tested techniques to manage and control your budgets Appreciate the fundamentals of financial analysis Focus on the bottom line Identify the basics of capital investment appraisal for your business Evaluate results and seek opportunities for improvement to your business 1 The commercial environment What do shareholders and investors want? What do managers want? Profit v non-profit organisations Investor expectations 2 Financial and non-financial information Risk and reward considerations Drivers of commercial decisions 3 Running a business A practical exercise to bring financial statements to life Different stakeholder interests in a business The impact and consequences of decisions on financial statements 4 Where do I make a difference to the organisation? How can I contribute to an improved business performance? Key performance indicators - measuring the right things A 'balanced scorecard' approach - it's not all about money! 5 A 'balanced scorecard' approach Analysing and reviewing my contribution to the business direction What is the current focus of my commercial decisions? Developing the business in the right way - getting the balance right! Where should/could it be in the future? Do my decisions support the overall vision and strategy? 6 Making commercial decisions Left-brain and right-brain thinking Convergent and divergent thinking Analysis and instinct Interactive case study exercise - emotional and rational decisions Reflection - what is my style of making decisions 7 Let's consider the customer! Identifying target markets Differentiating propositions and products Customer service considerations Marketing considerations and initiatives Pricing strategies and considerations 8 Strategic analysis The external environment The internal environment LEPEST analysis SWOT analysis Forecasting Group activity - analysing markets and the competition How do these improve your decisions? 9 Comparing performance Analysing key financial ratios Ways to compare performance and results Break-even analysis 10 Profit and loss accounts and budgeting Managing income and expenditure The budgeting process How does this link to the profit and loss account? Managing and controlling a cost centre/budget The role of the finance department Different ways of budgeting Incremental budgeting Zero-based budgeting 11 Understanding the balance sheet Purpose of balance sheets Understanding and navigating the content What does a balance sheet tell you? How do you affect your balance sheet? Links to the profit and loss account A practical team exercise that brings financial statements to life 12 Business decisions exercise How does this improve your decisions? A practical exercise to apply new knowledge and bring commercial thinking to to life The impact and consequences of decisions on financial statements 13 Working capital Why is this important? The importance of keeping cash flowing Business decisions that affect cash Calculating profit 14 Capital investment appraisal Capex v Opex Payback Return on investment The future value of money The concept of hurdle rate 15 Lessons learned and action planning So what? Recap and consolidation of learning The decisions that I need to consider Actions to achieve my plan

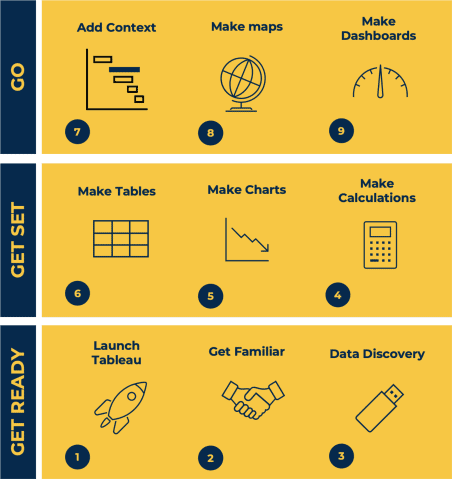
Tableau Desktop Training - Foundation
By Tableau Training Uk
This Tableau Desktop Training course is a jumpstart to getting report writers and analysts with little or no previous knowledge to being productive. It covers everything from connecting to data, through to creating interactive dashboards with a range of visualisations in two days of your time. For Private options, online or in-person, please send us details of your requirements: This Tableau Desktop Training course is a jumpstart to getting report writers and analysts with little or no previous knowledge to being productive. It covers everything from connecting to data, through to creating interactive dashboards with a range of visualisations in two days of your time. Having a quick turnaround from starting to use Tableau, to getting real, actionable insights means that you get a swift return on your investment of time and money. This accelerated approach is key to getting engagement from within your organisation so everyone can immediately see and feel the impact of the data and insights you create. This course is aimed at someone who has not used Tableau in earnest and may be in a functional role, eg. in sales, marketing, finance, operations, business intelligence etc. The course is split into 3 phases and 9 modules: PHASE 1: GET READY MODULE 1: LAUNCH TABLEAU Check Install & Setup Why is Visual Analytics Important MODULE 2: GET FAMILIAR What is possible How does Tableau deal with data Know your way around How do we format charts Dashboard Basics – My First Dashboard MODULE 3: DATA DISCOVERY Connecting to and setting up data in Tableau How Do I Explore my Data – Filters & Sorting How Do I Structure my Data – Groups & Hierarchies, Visual Groups How Tableau Deals with Dates – Using Discrete and Continuous Dates, Custom Dates Phase 2: GET SET MODULE 4: MAKE CALCULATIONS How Do I Create Calculated Fields & Why MODULE 5: MAKE CHARTS Charts that Compare Multiple Measures – Measure Names and Measure Values, Shared Axis Charts, Dual Axis Charts, Scatter Plots Showing Relational & Proportional Data – Pie Charts, Donut Charts, Tree Maps MODULE 6: MAKE TABLES Creating Tables – Creating Tables, Highlight Tables, Heat Maps Phase 3: GO MODULE 7: ADD CONTEXT Reference Lines and Bands MODULE 8: MAKE MAPS Answering Spatial Questions – Mapping, Creating a Choropleth (Filled) Map MODULE 9: MAKE DASHBOARDS Using the Dashboard Interface Dashboard Actions This training course includes over 25 hands-on exercises and quizzes to help participants “learn by doing” and to assist group discussions around real-life use cases. Each attendee receives a login to our extensive training portal which covers the theory, practical applications and use cases, exercises, solutions and quizzes in both written and video format. Students must use their own laptop with an active version of Tableau Desktop 2018.2 (or later) pre-installed. What People Are Saying About This Course “Excellent Trainer – knows his stuff, has done it all in the real world, not just the class room.”Richard L., Intelliflo “Tableau is a complicated and powerful tool. After taking this course, I am confident in what I can do, and how it can help improve my work.”Trevor B., Morrison Utility Services “I would highly recommend this course for Tableau beginners, really easy to follow and keep up with as you are hands on during the course. Trainer really helpful too.”Chelsey H., QVC “He is a natural trainer, patient and very good at explaining in simple terms. He has an excellent knowledge base of the system and an obvious enthusiasm for Tableau, data analysis and the best way to convey results. We had been having difficulties in the business in building financial reports from a data cube and he had solutions for these which have proved to be very useful.”Matthew H., ISS Group
BA (Hons) in Business Management with a Foundation Year
By Results Consortium
The BA (Hons) in Business Management with a Foundation Year, in collaboration with Leeds Trinity University, spans four years and is designed to empower students with the necessary academic skills and tools for confident study. Throughout the program, students engage in modules aimed at enhancing their academic abilities and gaining foundational knowledge in business operations and management principles, including insights into entrepreneurship and the basics of marketing. Upon the successful completion of the Foundation Year, students seamlessly transition to the first year of the Business Management BA (Hons) degree. The curriculum delves into the intricacies of organizational structures and operational strategies, covering fundamental aspects of accounting, finance, marketing, and providing opportunities to explore international business concepts. Developed in collaboration with employers, the program offers a comprehensive education in various facets of modern business management, addressing not only organizational challenges but also legal, ethical, and sustainability issues confronting companies in the contemporary business landscape.

Advanced Bookkeeping Excel Courses online | Excel Training in Campus
By Osborne Training
Why Join Digital Marketing Training Course at Osborne Training Osborne Training is well Recognised for quality Regular Lectures led by Industry Expert Tutors Unlimited Access to the State of the Art Virtual Learning Campus Exclusive Access to High quality study materials Flexible payment option available Join Digital Marketing Training course as Pure Online or Blended with Classroom Delivery Access to Digital Marketing Internship for 3 months at the end of the training Unlimited Tutorial Support from expert tutors Get a Student Discount Card from NUS* Get a Free Tablet PC for limited period* Practical Hands-on Projects, Practical focused Assignments and Group-work for greater skills enhancement and understanding real life issues for real life problems Once you complete the bookkeeping course, you will get a certificate from Osborne Training confirming your professional Digital Marketing Qualifications. What jobs could I qualify for? Senior Digital Marketing Manager Digital Marketing Coordinator Executive Digital Marketing Strategist Digital Marketing Consultant In these roles, you could earn on average more than £40,000 annually (source: Reed Salary Checker, UK). Moreover, many go on to become successful (Millionaire sometime) entrepreneur by offering Digital Marketing services or formulating successful Digital Marketing Strategy for their own business. Digital Marketing Qualifications Digital Marketing Qualifications at Osborne Training are developed in Association with Google. Osborne Training offers Total Digital Marketing Course which combines all major skills required to be a successful Digital Marketeer and you also have option to join a complementary Internship at the end of your course. In joining the Total Digital Marketing Course at Osborne Training, you will make one of the greatest decision of your career and can look forward to a successful career in digital marketing. Digital Marketing Course Overview Total Digital Marketing Course covers major areas of Digital Marketing to make you completely ready for the digital era. The Digital Marketing course comes with optional Internship at the end of the training making you highly employable. Practical focused and hands-on approach of the training method helps you to be ready to offer real life solutions for real life problems. Digital Marketing Training Course Content Basics of marketing Marketing In Digital Era All About Web Search Engine Optimization Search Engine Marketing Affiliate Marketing Social Media Marketing Email marketing and nurturing (inbound) Mobile app marketing Content marketing Web, mobile and app analytics Growth Hacking Creating robust digital marketing strategy

Handling challenging conversations
By Underscore Group
Learn the skills, knowledge and have the confidence to tackle difficult conversations in a productive way. Course overview Duration: 1 day (6.5 hours) Do you worry about how to give negative feedback or deal with performance issues? Are you concerned about giving bad news? This workshop is designed to give you the skills, knowledge and confidence to tackle these scenarios in a productive way. If you are a people manager, team leader or supervisor looking to make those challenging conversations less stressful and more effective, this workshop is for you. Lots of practical sessions will ensure you have the opportunity to relate your learning to your real life work situations. The one day session will use professional actors in the afternoon so that you can practice handling real-life challenging conversations. Objectives By the end of the course you will be able to: Deal with a wide range of challenging conversations Describe the preferred behavioural style for giving feedback State the most appropriate influencing technique to use in your situations Explain how to give successful constructive feedback Content What are challenging conversations What type of challenging conversations occur? Why do we find them challenging? Communication Practical exercise to demonstrate and act as a refresher of the fundamentals of communication Barriers to communication especially in a difficult discussion Choosing the right behavioural style Refresher of assertiveness and why it is important in this context Practical exercise demonstrating how behaviour breeds behaviour, and the impact of choosing an inappropriate style Steps to using assertive behaviour Influencing Cialdini’s model for influence How to use influencing techniques in handling challenging conversations Practical application Feedback Understanding feedback – positive vs. negative Using the ABCBC model for feedback Using the basics of emotional intelligence to give effective feedback Practical application Practical Activities Professional actors will work with you in small groups in the afternoon to practice real-life challenging conversations.

BPAS - BLS - Finsbury Park - Clare A
By Emergency Care Gateway
BLS Training First Aid Training Mandatory Training

Baby & Child First Aid - Combined Learning
By Mini First Aid North Nottinghamshire, Grantham & Sleaford
The 3-hour Baby & Child First Aid class covers CPR, Choking, Bumps, Burns, Breaks, Bleeding, Febrile Seizures and Meningitis & Sepsis Awareness and will give everyone who attends the peace of mind they deserve.

This is a step by step digital workshop that will be sent directly to your inbox for you to keep forever. All my workshops are suitable for beginners and the more experienced artist. I have 25 years experience delivering workshops to all ages and abilities. I use raku sculpture clay and finish with oxides but any clay can be used including air dry clay for people who do not have a kiln. I am happy to answer any questions via my facebook page or here.

Let’s Talk About Trauma
By Empowerful Living
A free, interactive session for women, about trauma and how to heal from it.
Search By Location
- Basic Courses in London
- Basic Courses in Birmingham
- Basic Courses in Glasgow
- Basic Courses in Liverpool
- Basic Courses in Bristol
- Basic Courses in Manchester
- Basic Courses in Sheffield
- Basic Courses in Leeds
- Basic Courses in Edinburgh
- Basic Courses in Leicester
- Basic Courses in Coventry
- Basic Courses in Bradford
- Basic Courses in Cardiff
- Basic Courses in Belfast
- Basic Courses in Nottingham