- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1738 Basic courses delivered Live Online
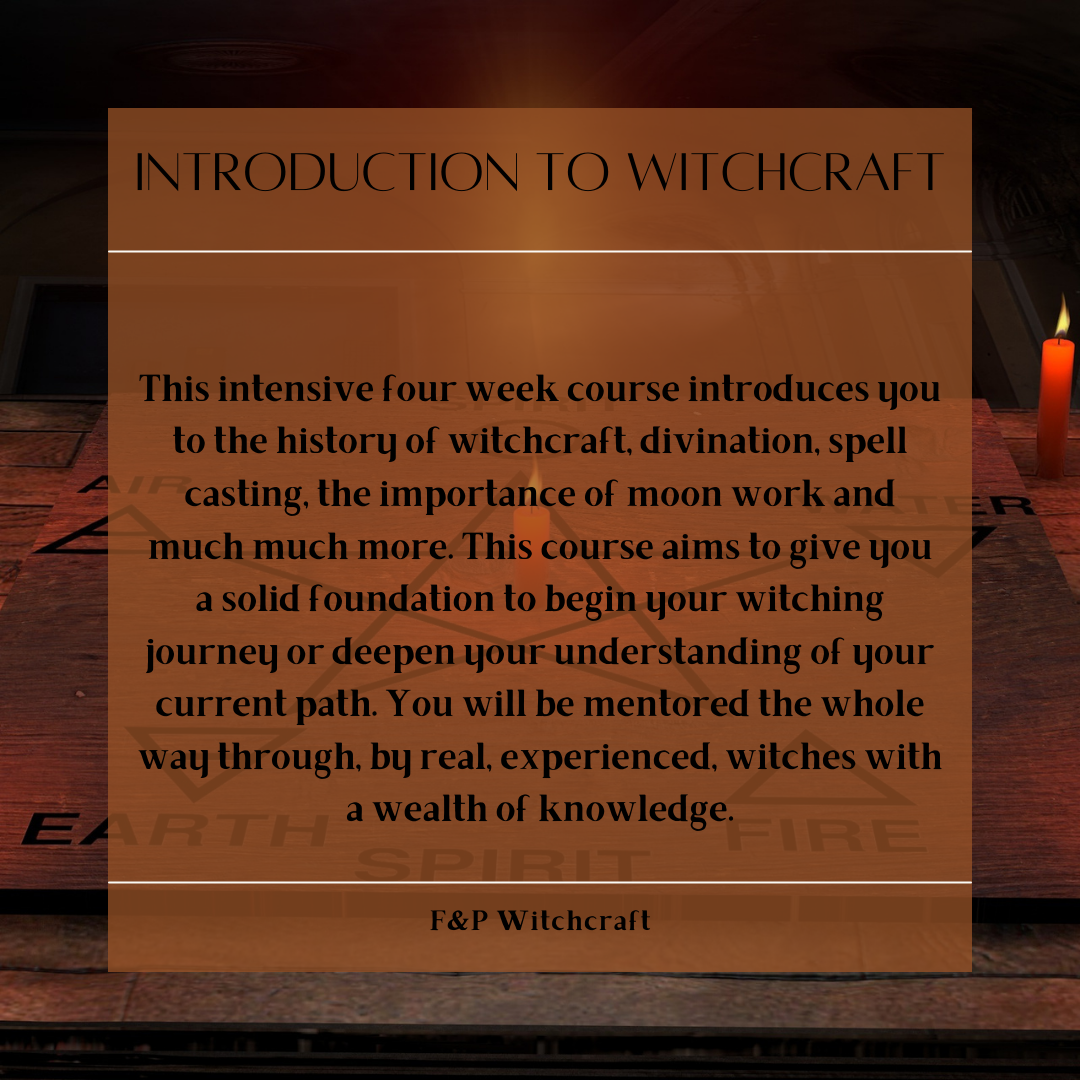
Introduction to Witchcraft
By F&P Witchcraft
This is a 12 month course, that covers all the basics you need to know about witchcraft! Debunking the silly myths that surround us, and giving you the information and confidence to start your witchcraft path!
Italian Language Course for Beginners
By NextGen Learning
Course Overview The Italian Language Course for Beginners offers an exciting introduction to the Italian language, designed to build a strong foundation in communication skills for everyday use. This course covers essential vocabulary, pronunciation, grammar, and conversational phrases, allowing learners to engage confidently in basic Italian dialogues. Through a structured and accessible approach, it provides valuable linguistic and cultural knowledge that can enhance travel experiences, support personal enrichment, or broaden career opportunities. Learners will benefit from step-by-step lessons that gradually develop listening, speaking, reading, and writing abilities. By the end of the course, participants will have gained the competence to hold simple conversations, understand common expressions, and navigate everyday situations with ease. Whether pursuing a personal passion or preparing for future opportunities, this course equips learners with essential Italian language skills that can be applied in various social, educational, and professional contexts. Course Description This comprehensive Italian Language Course for Beginners guides learners through the foundational elements of Italian in an engaging and supportive environment. Covering a range of topics from everyday greetings and basic sentence structure to practical vocabulary and common expressions, the course ensures a balanced development of communication skills. Participants will explore pronunciation techniques, grammatical rules, and essential conversational scenarios relevant to travel, dining, shopping, and social interactions. Lessons are carefully designed to foster gradual progression, enabling learners to build confidence as they advance. Interactive activities and real-world examples enhance understanding and retention, while cultural insights provide additional depth to the learning experience. By the conclusion of the course, learners will possess a strong entry-level proficiency in Italian, capable of managing simple conversations and understanding key aspects of the language. This course is ideal for those seeking to expand their linguistic abilities and cultural knowledge within a structured, beginner-friendly framework. Course Modules Module 01: Lesson 1 Module 02: Lesson 2 Module 03: Lesson 3 Module 04: Lesson 4 Module 05: Lesson 5 Module 06: Lesson 6 Module 07: Lesson 7 Module 08: Lesson 8 Module 09: Lesson 9 (See full curriculum) Who is this course for? Individuals seeking to learn Italian for travel, relocation, or cultural interest. Professionals aiming to add basic Italian language skills to enhance career prospects. Beginners with an interest in European languages and cultures. Students preparing for further language study or international education opportunities. Language enthusiasts wishing to expand their multilingual abilities. Career Path Customer Service Representative in international companies Hospitality and Tourism Sector Roles Administrative Support in multinational organisations Language Teaching Assistant (Entry-level) Cultural Exchange Programme Coordinator

VMware Carbon Black Cloud:Advanced Operations and Troubleshooting
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Experienced security administrators and security analysts who are already familiar with VMware Carbon Black Cloud Overview By the end of the course, you should be able to meet the following objectives: Describe and determine use cases for integrating with VMware Carbon Black Cloud Configure, automate, and troubleshoot the VMware Carbon Black Cloud Syslog Integration Use VMware Carbon Black Cloud APIs to pull data with Postman Install and use the VMware Carbon Black Cloud Python SDK Automate operations using the VMware Carbon Black Cloud SDK and APIs Identify and troubleshoot VMware Carbon Black Cloud sensor installations Gather troubleshooting data within the browser to remediate or escalate problems Identify and resolve sensor usage, networking, and performance problems with the VMware Carbon Black Cloud sensor This two-day, hands-on training course provides you with the advanced knowledge, skills, and tools to achieve competency in performing advanced operations and troubleshooting of VMware Carbon Black Cloud. This course will go into integrating VMware Carbon Black Cloud with other third-party components and utilizing the API and the SDK to automate operations within the product and your security stack. This course will also enable you to troubleshoot common problems during sensor installation, operations, and within the VMware Carbon Black Cloud console with hands-on lab problems. Course Introduction Introductions and course logistics Course objectives VMware Carbon Black Cloud Integrations Describe the integration capabilities with VMware Carbon Black Cloud Determine integration use cases for VMware Carbon Black Cloud Identify required components for integrating VMware Carbon Black Cloud Differentiate VMware Carbon Black Cloud integration vendors VMware Carbon Black Cloud Syslog Integration Describe the function of the Syslog Connector Generate API and SIEM keys from the Cloud console Validate a successful Syslog integration Describe how to automate the Syslog Connector Troubleshoot problems with the Syslog integration Using Postman Explain the concept and purpose of an API Interpret common REST API Status codes Recognize the difference between platform and product APIs Using the Postman Client to initiate API calls Create a custom access level and respective API key Create a valid API request Using the VMware Carbon Black Cloud Python SDK Install the VMware Carbon Black Cloud Python SDK Describe the different authentication methods Evaluate the best authentication method for a given task Automating Operations Automate basic Incident Response tasks using the VMware Carbon Black Cloud SDK and API Automate basic watchlist interactions using the VMware carbon Black Cloud SDK and API Sensor Installation Troubleshooting Describe sensor install log collection process Identify sensor install log parameters Create a detailed sensor install log Locate sensor install logs on an endpoint Interpret sensor install success from an install log Determine likely cause for install failure using sensor logs Propose resolution steps for a given sensor install failure VMware Carbon Black Cloud Console Troubleshooting Identify sensor bypass status reasons Simplify console data exports using search Describe differences in Audit Log detail levels Locate built-in browser tools Gather console diagnostics logs from a browser Review console diagnostics logs Sensor Operations Troubleshooting Identify available types of diagnostic logs Gather appropriate diagnostic logs for a given issue Identify steps for resolving software interoperability problems Identify steps for resolving resource problems Identify steps for resolving network problems Additional course details:Notes Delivery by TDSynex, Exit Certified and New Horizons an VMware Authorised Training Centre (VATC) Nexus Humans VMware Carbon Black Cloud:Advanced Operations and Troubleshooting training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the VMware Carbon Black Cloud:Advanced Operations and Troubleshooting course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Mastering JEE Web Development (TT5100)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This is an introductory- level Java programming course, designed for experienced developers who wish to get up and running with JEE, or who need to reinforce sound Java for Web / JEE coding practices. Attendees should have a working knowledge of developing basic Java software applications. Overview Students who attend Mastering JEE Web Application Development will leave the course armed with the required skills to design and build scalable, secure, maintainable web applications - leveraging our extensive experience in the delivery of scalable enterprise applications with complex web interfaces based on JEE technologies. Throughout this training, you will be confronted with common web application design problems and given the tools you will need to solve them, such as JEE design patterns. You will also be exposed to a range of JEE and web technologies such as Servlets, JSPs, JSF, JNDI, CDI and advice on when and how to use them. Students will also learn about the capabilities of servlets, their advantages, servlet architecture, and session management. Developers will also learn about managing resources, deployment, and application models, how to use custom tags, and how to build robust and capable web applications using servlets and other components. The course begins with a discussion of web application architecture. A major part of the course is spent on the various web components that are used to implement dynamic web applications. Students will learn not only specific topics and APIs but also how to fit the pieces together into a complete application. Working within in an engaging, hands-on learning environment, guided by our expert team, attendees will learn to: Design and build web applications from both business and technical requirements Build web interfaces with JSF, JSPs and Servlets, using the latest technologies in JEE. Write maintainable web applications that separate HTML and Java Understand the design and development of web applications using Servlets, JSPs, web fragments, and JSF Work JEE's version of dependency injection (CDI) Make Servlets cooperate and share data Store and process session information Deal with concurrency issues Access databases with JPA Work with annotations included in JEE Work with WebSockets as well as asynchronous servlets Use Java Bean validation in a web application Properly handle various types of exceptions This course is for experienced Java developers who are new to JEE and need to get up and running with essential dynamic web development skills. You will gain core JEE knowledge and skills that can be used as the foundation for developing production-quality web applications to a basic level. Developing Java EE applications Enterprise Development Java EE Core Components JEE Dynamic Web Applications Introduction to Servlets Form processing using Servlets Java Server Pages Implementing MVC in JEE Session Management JEE Servlet Filters and Listeners Servlet Filters Expression Language 3.0 (EL) Overview of EL The EL language Custom Tags Introduction to Custom Tags The Java Standard Tag Library Contexts and Dependency Injection (CDI) Introduction to CDI Using CDI CDI and Java EE Using Resources JEE DataSources Overview of JPA Java API for WebSocket Introduction to WebSocket Implementing WebSocket Endpoint Extending WebSockets Java Bean Validation (JSR 349) Introduction to Bean Validation Bean Validation Managing Web Applications Web Fragments Error Handling Asynchronous Servlets Web Security Introduction to Java Server Faces Introduction to JSF JSF Components Facelets Facelets Facelets Templating and Resources Additional course details: Nexus Humans Mastering JEE Web Development (TT5100) training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the Mastering JEE Web Development (TT5100) course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.

Essential Adobe InDesign Training Course
By ATL Autocad Training London
Who is this for? Essential Adobe InDesign Training Course. Acquire Adobe InDesign basics from certified instructors. Master layout design, typography, and core design concepts. Opt for in-person or live online sessions. Receive a Certificate of Completion and lifelong email assistance. Lean desktop publishing skills and quality layouts. Click here for more info: Website Duration: 5 hours Approach: Individualized 1-on-1 training with customized content. Schedule: Flexible sessions, available Monday to Saturday from 9 am to 7 pm. Course Outline: Module 1: Introduction to Adobe InDesign (1 hour) Familiarize with workspace and tools Create new documents with appropriate page size and margins Effectively format text and images Customize the interface for efficient workflow Module 2: Text Formatting and Styles (1 hour) Apply consistent character and paragraph styles Manage text flow using frames Organize lists with bullets and numbering Master special characters for precise typography Module 3: Working with Images (1 hour) Import and position images in documents Adjust image size and alignment within frames Create professional layouts with text wrapping around images Enhance visuals with image frames and effects Module 4: Layout Design (1 hour) Create precise grids and guides for alignment Arrange objects for balanced layouts Streamline work with layers Maintain consistency using master pages and templates Module 5: Printing and Exporting (1 hour) Understand color modes and print principles Export to PDF and other formats for diverse outputs Ensure print readiness through preflighting Efficiently archive and manage InDesign files Through practical exercises, solidify your grasp of each module, enabling you to design visually appealing layouts, craft documents for various purposes, and manage InDesign projects adeptly. Adobe InDesign's potential is vast, and this fundamentals course opens doors for you to explore diverse design projects. Seize this opportunity to unleash your creative prowess with InDesign! Upon completing the Adobe InDesign Fundamentals course, participants will be able to: Master InDesign Tools: Demonstrate proficiency in utilizing InDesign's essential tools, workspace, and interface for effective design workflows. Layout Design Skills: Create visually appealing layouts using grids, guides, and balanced object arrangements, ensuring professional-quality design. Text Formatting Mastery: Apply consistent character and paragraph styles, manage text flow, and enhance typography with special characters. Image Manipulation Expertise: Import, position, and enhance images within frames, integrating them seamlessly into layouts. Printing and Exporting Proficiency: Understand color modes, print principles, and export documents to various formats, ensuring print readiness and diverse output options. Efficient Project Management: Utilize layers, master pages, and templates for streamlined project organization and management in InDesign. Book Recommendations: "InDesign CC Classroom in a Book" by Kelly Kordes Anton and John Cruise: This official Adobe guide provides hands-on lessons and practical techniques for mastering InDesign's core features. "InDesign Type: Professional Typography with Adobe InDesign" by Nigel French: Explore advanced typography techniques, layout principles, and typographic finesse specific to Adobe InDesign. "Real World Adobe InDesign CC" by Olav Martin Kvern, David Blatner, and Bob Bringhurst: A comprehensive guide offering practical insights, tips, and real-world techniques for InDesign users of all levels. "The Adobe InDesign CS6 Book for Digital Photographers" by Scott Kelby: Focused on integrating photography with InDesign, this book provides valuable insights into creating visually stunning layouts with images. "InDesign Secrets" by David Blatner and Anne-Marie Concepción: This book is packed with expert tips, tricks, and techniques that can significantly enhance your efficiency and creativity in InDesign. 1-on-1 InDesign Courses: Personalized Learning: Tailored 1-on-1 courses designed to meet your specific learning needs and goals. Expert Instructors: Learn from industry professionals with extensive experience in animation and design. Flexible Scheduling: Schedule sessions at your convenience, allowing you to balance learning with your busy lifestyle. Comprehensive Curriculum: Dive deep into animation techniques, software mastery, and creative skills through our comprehensive courses. Hands-On Training: Get practical, hands-on experience with real-world animation projects, enhancing your skills effectively. Individual Attention: Benefit from personalized attention and detailed feedback from instructors, ensuring your progress and understanding. Professional Development: Acquire skills relevant to the industry, empowering you for career advancement in animation and related fields. Portfolio Enhancement: Develop a strong portfolio with the guidance of experts, showcasing your newfound skills and creativity. Post-Course Support: Enjoy continued support even after the course completion, ensuring you have resources for ongoing learning and growth. Certification: Receive a certificate upon course completion, validating your expertise and enhancing your professional credentials. Course Highlights: Master Adobe InDesign's key features for layout, text, images, and graphics. Learn design principles and typography techniques for visually appealing documents. Efficiently handle multi-page projects like magazines and brochures. Utilize styles, templates, and libraries for streamlined design and consistency. Explore advanced techniques for interactive PDFs and digital publishing. Earn a Certificate of Completion for your Adobe InDesign proficiency. Flexible learning options: in-person or live online sessions. Lifetime email support for ongoing assistance after the course. Adobe InDesign Learn & Support https://helpx.adobe.com ⺠support ⺠indesign Get started with Adobe InDesign. Find tutorials, the user guide, answers to common questions, and help from the community forum.

CL207 IBM Db2 11.1 Administration Workshop for Linux
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This is an intermediate level course for students that will perform Database Administration tasks, who plan, implement, and maintain D22 11.1 databases. Overview These skills can be developed by taking: DB2 SQL Workshop DB2 Fundamentals This course teaches database administrators to perform basic database administrative tasks using Db2 11.1. These tasks include creating database objects like tables, indexes and views, and loading data into the database with Db2 utilities like LOAD and INGEST. Various diagnostic methods will be presented, including using db2pd command options, and monitoring with SQL statements that reference Db2 monitor functions. Students will learn how to implement automatic archival for database logs and how to recover a database to a specific point in time using the archived logs. The course covers using EXPLAIN tools to review the access plans for SQL statements and adding indexes to improve SQL performance. We will cover the locking performed by Db2 and the effect the application isolation level has on locking and lock wait conditions. Students will learn how to implement database security, including adding a security administrator, SECADM user, and implement database roles to simplify security management. We will also describe implementing Db2 native encryption for a database. Overview of Db2 11.1Db2 Command Line Processor (CLP) and GUI toolsThe Db2 database manager instanceCreating Databases and Data PlacementCreating Database ObjectsMoving DataBackup and RecoveryDatabase Maintenance, Monitoring and Problem DeterminationLocking and concurrencySecurity

Food Hygiene Awareness
By Prima Cura Training
The Food Hygiene Regulations 2006 are considered to be the most important food safety and hygiene regulations in the UK. These regulations go one step further than the Food Safety Act 1990 as they specify that ALL food businesses have a legal obligation to make sure that food they prepare and serve to the public is safe and hygienic.

JIR - Junos Intermediate Routing
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Network engineers, technical support personnel, reseller support engineers, and others responsible for implementing and/or maintaining the Juniper Networks products covered in this course. Overview Describe typical uses of static, aggregate, and generated routes. Configure and monitor static, aggregate, and generated routes. Explain the purpose of Martian routes and add new entries to the default list. This two-day course provides students with intermediate routing knowledge and configuration examples. The course includes an overview of protocol independent routing feature. Chapter 1: Course Introduction Course Introduction Chapter 2: Protocol-Independent Routing Static Routes Aggregated Routes Generated Routes Martian Addresses Routing Instances Chapter 3: Load Balancing and Filter-Based Forwarding Overview of Load Balancing Configuring and Monitoring Load Balancing Overview of Filter-Based Forwarding Configuring and Monitoring Filter-Based Forwarding Chapter 4: Open Shortest Path First Overview of OSPF Adjacency Formation and the Designated Router Election OSPF Scalability Configuring and Monitoring OSPF Basic OSPF Troubleshooting Chapter 5: Border Gateway Protocol Overview of BGP BGP Attributes IBGP Versus EBGP Configuring and Monitoring BGP Chapter 6: IP Tunneling Overview of IP Tunneling GRE and IP-IP Tunnels Implementing GRE and IP-IP Tunnels Chapter 7: High Availability Overview of High Availability Networks GR Graceful RE Switchover Nonstop Active Routing BFD VRRP Appendix A

Cisco Programming for Network Engineers v2.0 (PRNE)
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This course is intended for: Network administrators Network engineers with little or no programming or Python experience Network managers Systems engineers Overview After taking this course, you should be able to: Create a Python script Describe data types commonly used in Python coding Describe Python strings and their use cases Describe Python loops, conditionals, operators, and their purposes and use cases Describe Python classes, methods, functions, namespaces, and scopes Describe the options for Python data manipulation and storage Describe Python modules and packages, their uses, and their benefits Explain how to manipulate user input in Python Describe error and exception management in Python Describe Python code debugging methods The Programming for Network Engineers (PRNE) v2.0 course is designed to equip you with fundamental skills in Python programming. Through a combination of lectures and lab experience in simulated network environments, you will learn to use Python basics to create useful and practical scripts with Netmiko to retrieve data and configure network devices. Upon completion of this course, you should have a basic understanding of Python, including the knowledge to create, apply, and troubleshoot simple network automation scripts. Course Outline Introducing Programmability and Python for Network Engineers Scripting with Python Examining Python Data Types Manipulating Strings Describing Conditionals, Loops, and Operators Exploring Classes, Methods, Functions, Namespaces, and Scopes Exploring Data Storage Options Exploring Python Modules and Packages Gathering and Validating User Input Analyzing Exceptions and Error Management Examining Debugging Methods

Studio Health and Safety for Potters - managing dust, fumes, poisons, ...
By Tim Thornton
Studio Health and Safety for Potters - an online course by Tim Thornton. This covers the risks of dust, fumes, toxic materials and more, and how to deal with them
