- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
347 Audit courses in Cardiff delivered Live Online
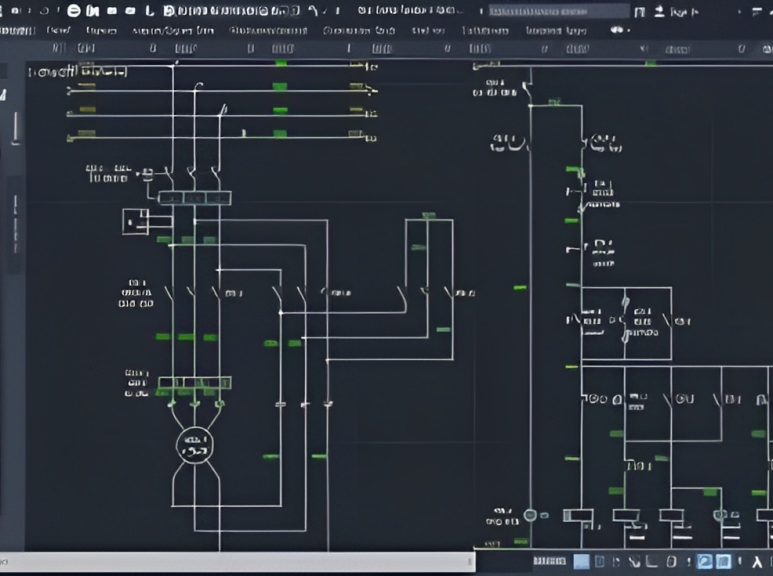
AutoCAD Training Course for Electrical
By ATL Autocad Training London
Exclusive to AutoCAD subscribers, the AutoCAD Electrical toolset simplifies electrical system creation. Click here for more info: Website Our course provides a strong foundation in 2D electrical design, covering essential tools. Flexible one-on-one sessions from 9 a.m. to 7 p.m., Monday to Saturday. Call 02077202581 or book online. The 16-hour course offers flexibility, divide hours across days. Benefit from individualized attention and tailored content. Enroll for in-person or Zoom sessions to excel in AutoCAD Electrical. AutoCAD Electrical Course Content: Introduction to AutoCAD Electrical Software: Overview and features of AutoCAD Electrical Understanding the software interface and tools Project file structure and management Layout and Navigation: Navigating the AutoCAD Electrical workspace Creating new project files and using attribute editors Understanding WDD, WDX, and WDF project files Exploring the Project Manager interface and attribute editors Electrical Diagram Drawing: Numbering and titling wires in diagrams Labelling components Utilizing diagram symbol libraries Creating and editing Electrical Control Circuits (ECC) Component dialog box and Circuit Scale dialog box Introduction to Programmable Logic Controllers (PLCs) and Integrated Systems: PLC Symbols and Concepts Inserting Programmable Logic Controllers (PLCs) into diagrams Adding PLC Units to diagrams Working with PLC Input and Output points and circuits Understanding PLC-based classification Using the Spreadsheet to PLC Input and Output Points utility Custom and Bespoke Symbols: Creating custom symbols for Switches, Wires, Contactors, Motors, Transformers, etc. Specifying symbol conventions and standards Offline and online usage of AutoCAD Electrical databases Drawing for Terminals and Plans: Implementing Terminal symbols in diagrams Handling terminal plans and locations Working with compound level terminals and locations Utilizing the Component command for single and multiple components Managing Jumpers and wiring Modifying Terminal Strips and Dual In-Line Packages (DIP) Understanding DIN Rail, Electrical Enclosure, Circuit Breakers, and Electrical Equipment Generating PDFs and Reports: Exporting drawings to PDF format Organizing report templates Automating the generation of reports Creating Electrical Audit Reports This AutoCAD Electrical course provides comprehensive knowledge of the software, focusing on electrical diagram drawing, symbol creation, PLC integration, terminal planning, and report generation. Participants will gain the skills needed to efficiently design electrical systems using AutoCAD Electrical software. Upon completion, participants will proficiently use AutoCAD Electrical to create precise electrical diagrams, integrate PLCs, design custom symbols, plan terminals, and generate reports efficiently. They will possess the skills needed to confidently design electrical systems and enhance their expertise in electrical design and drawing. AutoCAD Electrical Training Course: Master precision in specialized electrical design skills. Optimize your design process with streamlined workflows. Ensure compliance with industry standards consistently. Boost productivity in electrical design tasks. Facilitate seamless collaboration with fellow professionals. Benefit from recorded lessons for convenient review. Enjoy continuous support with lifetime email assistance. Unleash the complete power of AutoCAD for your electrical design needs. Enroll today and craft precise, professional electrical drawings confidently. Select between in-person and live online sessions to suit your preference. Flexible Evening Sessions: Learn AutoCAD at your own pace with evening sessions designed for busy individuals. Boost your career opportunities in computer-aided design. Comprehensive Skill Development: Gain a strong foundation in AutoCAD's core features and advance to 3D modeling and rendering techniques, enhancing your design capabilities. Industry-Standard Knowledge: Become proficient in AutoCAD, a widely used CAD software in architecture, engineering, and construction fields, making you highly sought after by employers. Practical Application: Apply AutoCAD skills to real-world design scenarios, creating detailed plans for professional projects in architecture, engineering, and mechanical fields. Recorded Lessons for Review: Access lesson recordings to reinforce learning and review specific topics or techniques whenever needed. Lifetime Email Support: Enjoy ongoing support with lifetime email assistance, even after completing the course, for guidance and clarification.
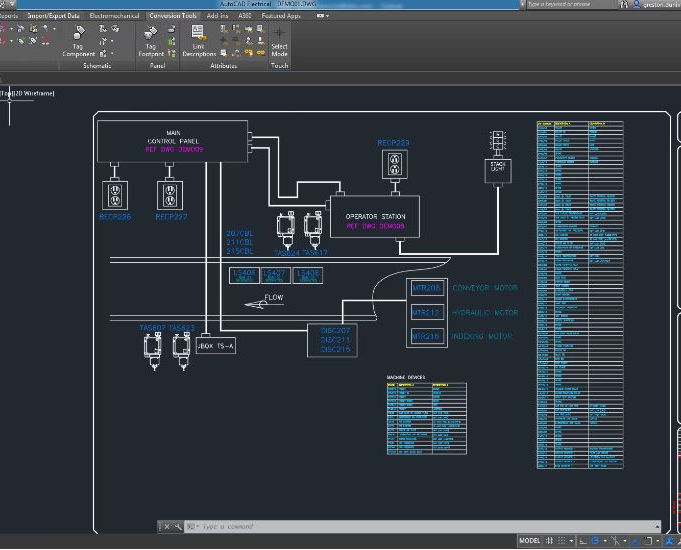
AutoCAD Electrical Training Course | Bespoke
By London Design Training Courses
Why Choose AutoCAD Electrical Training Course | Bespoke? Course Link Master electrical drawings, schematics, and layouts. Utilize symbol libraries and automated circuit design. Access recorded lessons and lifetime email support. "Say goodbye to group classes and hello to 1-on-1 Courses. Dial 02077202581 or WhatsApp 07970325184 to reserve your dates. Duration: 16 hrs. Method: 1-on-1, Personalized attention. Schedule: Tailor your own hours of your choice, available from Mon to Sat between 9 am and 7 pm. AutoCAD Electrical Training Course: Specialized electrical CAD design skills with precision. Streamlined workflows for efficient design. Consistent adherence to industry standards. Increased productivity in electrical design. Enhanced collaboration with other professionals. Access to recorded lessons for review. Lifetime email support for ongoing assistance. Learn AutoCAD for electrical design. Enroll now and create accurate and professional electrical drawings with confidence. Choose in-person or live online sessions. AutoCAD Electrical Training Course: Specialized electrical CAD design skills with precision. Streamlined workflows for efficient design. Consistent adherence to industry standards. Increased productivity in electrical design. Enhanced collaboration with other professionals. Access to recorded lessons for review. Lifetime email support for ongoing assistance. Learn AutoCAD for electrical design. Enroll now and create accurate and professional electrical drawings with confidence. Choose in-person or live online sessions. AutoCAD Electrical Course Content: Introduction to AutoCAD Electrical Software: Overview and features of AutoCAD Electrical Understanding the software interface and tools Project file structure and management Layout and Navigation: Navigating the AutoCAD Electrical workspace Creating new project files and using attribute editors Understanding WDD, WDX, and WDF project files Exploring the Project Manager interface and attribute editors Electrical Diagram Drawing: Numbering and titling wires in diagrams Labelling components Utilizing diagram symbol libraries Creating and editing Electrical Control Circuits (ECC) Component dialog box and Circuit Scale dialog box Introduction to Programmable Logic Controllers (PLCs) and Integrated Systems: PLC Symbols and Concepts Inserting Programmable Logic Controllers (PLCs) into diagrams Adding PLC Units to diagrams Working with PLC Input and Output points and circuits Understanding PLC-based classification Using the Spreadsheet to PLC Input and Output Points utility Custom and Bespoke Symbols: Creating custom symbols for Switches, Wires, Contactors, Motors, Transformers, etc. Specifying symbol conventions and standards Offline and online usage of AutoCAD Electrical databases Drawing for Terminals and Plans: Implementing Terminal symbols in diagrams Handling terminal plans and locations Working with compound level terminals and locations Utilizing the Component command for single and multiple components Managing Jumpers and wiring Modifying Terminal Strips and Dual In-Line Packages (DIP) Understanding DIN Rail, Electrical Enclosure, Circuit Breakers, and Electrical Equipment Generating PDFs and Reports: Exporting drawings to PDF format Organizing report templates Automating the generation of reports Creating Electrical Audit Reports This AutoCAD Electrical course provides comprehensive knowledge of the software, focusing on electrical diagram drawing, symbol creation, PLC integration, terminal planning, and report generation. Participants will gain the skills needed to efficiently design electrical systems using AutoCAD Electrical software. Upon completing the AutoCAD Electrical course, participants will master the intricacies of the software. They will adeptly create accurate electrical diagrams, seamlessly integrate PLCs, design personalized symbols, strategize terminal layouts, and produce reports with precision and efficiency. Armed with these skills, graduates will possess the expertise to confidently design complex electrical systems. This proficiency opens avenues in various job roles such as Electrical Design Engineer, CAD Technician, Control Systems Designer, or even Project Manager in industries like manufacturing, automation, and engineering consultancy.
Good Laboratory Practice Refresher and Hot Topics
By Research Quality Association
Course Information Join us for a comprehensive refresher focusing on crucial Good Laboratory Practice (GLP) requirements, including an emphasis on data integrity, recent developments, and emerging trends gleaned from MHRA inspections. The programme dives into specific domains such as risk assessment, OECD guidance on sponsor influence, and the advisory from OECD on QA. Additionally, delegates can benefit from a dedicated GLP clinic, facilitating discussions on understanding and upholding GLP compliance. Is this course for you? This course is tailored for study directors, principal investigators, test facility management, and QA professionals seeking to refresh their knowledge and responsibilities within the GLP framework. Tutors Tutors will be comprised of (click the photos for biographies): Vanessa Grant -, - Tim Stiles Consultant, Qualogy Ltd Programme Please note timings may be subject to alteration. Day 1 09:00 Registration, Welcome and Introduction 09:20 Development of Good Laboratory Practice A reminder of the history of GLP, its current scope and application, with a synopsis of current UK, European and international standards. 09:50 Roles and Responsibilities of Study Director, Test Facility Management, Principal Investigator, Test Site Management, Study Staff and QA A reminder of the roles and responsibilities with regard to the GLP management and oversight of the Test Facility and the management and control of the study, as defined by GLP. 10:30 Break 10:45 Workshop 1 Workshop 1 Roles and responsibilities 11:15 Influence of Sponsors The published OECD Position Paper No. 21 regarding Possible Influence of Sponsors on conclusions of GLP Studies is reviewed and discussed. 11:45 Data Integrity The fundamentals of data integrity according to the OECD Guidance No. 22 on Data Integrity is discussed along with the responsibilities of Study Director, Test Facility Management, and study staff in ensuring the integrity of the GLP study data. 12:30 Lunch 13:15 Quality Assurance and GLP OECD Advisory No. 23 (Revision of OECD No.4)- A walk through of the changes to the OECD Guidance on the role and activities of Quality Assurance 13:45 Quality Improvement Tools and GLP The tools that might be considered for GLP and their role and operation when used in Test Facilities- OECD Position Paper No.24 published July 2022 14:15 Workshop 2 Workshop 2 Change control 14:30 Risk Assessment How should we assess risk and how can we use the process to assist in evaluation audit findings? 15:00 Break 15:15 Current hot topics in GLP Explore the current issues in Industry and trends /types of Regulatory inspection findings 15:50 GLP Clinic An opportunity to discuss any other issues regarding understanding and maintaining GLP Compliance. 16:30 Close of Course Extra Information Course Material This course will be run completely online. You will receive an email with a link to our online system, which will house your licensed course materials and access to the remote event. Please note this course will run in UK timezone. The advantages of this include: Ability for delegates to keep material on a mobile device Ability to review material at any time pre and post course Environmental benefits – less paper being used per course Access to an online course group to enhance networking. You will need a stable internet connection, a microphone and a webcam. CPD Points 7 Points Development Level Learn

ACCA Courses | ACCA Distance Learning Online | Accounting Courses
By Osborne Training
ACCA Qualification is designed to provide the accounting knowledge, skills and professional values which will deliver finance professionals who are capable of building successful careers across all sectors, whether they are working in the public or private sectors, practicing in accounting firms, or pursuing a career in business. The ACCA Qualification is your route to professional status. Making a decision to study ACCA courses at Osborne Training will be one of the biggest decision you would make for your career. Assessment is by external examination. You must pass all the exams to be ACCA qualified. Once you finish all exams successfully, you will be awarded with ACCA certificate. Paper F1 Accountant in Business Paper F2 Management Accounting Paper F3 Financial Accounting (INT) Paper F4 Corporate and Business Law (UK) Paper F5 Performance Management Paper F6 Taxation (UK) Paper F7 Financial Reporting (INT) Paper F8 Audit and Assurance (INT) Paper F9 Financial Management

Total SAGE Training (Sage 50 Accounts + Sage Payroll Training)
By Osborne Training
Total SAGE Training (Sage 50 Accounts + Sage Payroll Training) Want to open the door to working in Finance and Accountancy Industry? Starting our Total Sage Training courses will enhance your career potentials and give you the skills and knowledge you need to get started in Finance and Accountancy Industry. Total Sage Training courses are combined with Sage 50 Accounts and Sage Payroll Training. You will receive a CPD Completion Certificate from Osborne Training once you finish the course. You also have an Option to attain Certificate from SAGE(UK) subject to passing the exams. What qualification will I gain for Sage Training Courses? CERTIFICATION FROM SAGE (UK) As Osborne Training is a Sage (UK) Approved training provider, you could gain the following qualifications provided that you book and register for exams and pass the exams successfully: Sage 50c Computerised Accounting Course (Level 1) Sage 50c Computerised Accounting Course (Level 2) Sage 50c Computerised Accounting Course (Level 3) Sage 50c Computerised Payroll Course (Level 1) Sage 50c Computerised Payroll Course (Level 2) Sage 50c Computerised Payroll Course (Level 3) Level 1 Working with Sage 50 Accounts Program Basics. Creating Account names, Numbers & Bank Payments Financials Bank Reconciliations Generating Customers Invoices Monitoring Customer Activity Generating Product Invoices & Credit Notes Compiling & Sending Customer Statements Creating Customer Receipts & Purchase Invoices Supplier Payments Managing Recurring Entries Generating Reports & Information The Active Set-Up Wizard VAT Changes. Level 2 An overview of the Sage program Entering opening balances, preparing and printing a trial balance Creating customer records Creating supplier records Setting up opening assets, liabilities and capital balances, Producing routine reports Checking data, Entering supplier invoices Posting error corrections, amending records Invoicing, generating customer letters, entering new products, checking communication history Banking and payments, producing statements, petty cash Audit trails, correcting basic entry errors, reconciling debtors and creditors Creating sales credit notes, Processing purchase credit notes Preparing journals Verifying Audit Trail Purchase orders, processing sales orders Processing Trial Balance Creating Backups Restoring data Writing-off bad debts Level 3 Creating a Chart of Accounts to Suit Company Requirements Sole Trader Accounts preparation The Trial Balance preparation Errors in the Trial Balance Disputed Items Use of the Journal Prepare and Process Month End Routine Contra Entries The Government Gateway and VAT Returns Bad Debts and Provision for Doubtful Debts Prepare and Produce Final Accounts Management Information Reports Making Decisions with Reports Using Sage The Fixed Asset Register and Depreciation Accruals and Prepayments Cash Flow and Forecast Reports Advanced Credit Control

CCSP Certification Prep Course
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Anyone whose position requires CCSP certificationIndividuals whose responsibilities involve procuring, securing, and managing cloud environments or purchased cloud services Overview In-depth coverage of the six domains required to pass the CCSP exam:Architectural concepts and design requirementsCloud data securityCloud platform and infrastructure securityCloud application securityOperationsLegal and compliance This course is the most comprehensive review of cloud security concepts and industry best practices covering the six domains of the CCSP Common Body of Knowledge (CBK). You will gain knowledge in identifying the types of controls necessary to administer various levels of confidentiality, integrity, and availability, with regard to securing data in the cloud. You will identify the virtual and physical components of the cloud infrastructure with regard to risk management analysis, including tools and techniques necessary for maintaining a secure cloud infrastructure. You will gain an understanding in cloud software assurance and validation, utilizing secure software, and the controls necessary for developing secure cloud environments. You will identify privacy issues and audit processes utilized within a cloud environment, including auditing controls, assurance issues, and the specific reporting attributes. Architectural Concepts and Design Requirements Cloud Data SecurityCloud Platform and Infrastucture Security Cloud Application SecurityOperations Legal and compliance

Overview This training course will empower you to recognize the root causes of fraud and white-collar crime in the current economy, understand the categories of fraud, equip you with methodologies of fraud detection and prevention, and heighten your ability to detect potential fraudulent situations. In addition to the fundamentals of fraud investigation and detection in a digital environment; profit-loss evaluation, analysis of accounting books, legal concepts, and quantification of financial damages are also examined in this course

Sage Line 50 Accounting / Bookkeeping Training - Fast Track
By Osborne Training
Sage Line 50 Accounting / Bookkeeping Training - Fast Track If you're looking to gain competency in the world's most popular bookkeeping software, the Sage 50 Computerised Accounting course will teach everything you need to know, while helping you gain a recognised qualification. This Course is designed to provide individuals from beginner to advanced knowledge of bookkeeping and Sage 50 accounts. It is intended for individuals who aim to improve career prospects and to be able to better financial management and control of business. This course covers Level 1-3 of Sage 50 Bookkeeping/Accounting Training. Every business, no matter how large or small, is required by law to 'keep books'. Therefore, Bookkeepers play a vital role within organisations; ensuring records of individual financial transactions are accurate, orderly, up to date and comprehensive. If you are organised and methodical, like working through documents and enjoy seeing a set of figures add up properly, then bookkeeping is the career for you. What qualification will I gain? You have the choice to gain certification from one of the following awarding bodies. CERTIFICATION FROM SAGE (UK) As Osborne Training is a Sage (UK) Approved training provider, you could gain the following qualifications provided that you book and register for exams and pass the exams successfully: Sage 50c Computerised Accounting Course (Level 1) Sage 50c Computerised Accounting Course (Level 2) Sage 50c Computerised Accounting Course (Level 3) Level 1 Working with Sage 50 Accounts Program Basics. Creating Account names, Numbers & Bank Payments Financials Bank Reconciliations Generating Customers Invoices Monitoring Customer Activity Generating Product Invoices & Credit Notes Compiling & Sending Customer Statements Creating Customer Receipts & Purchase Invoices Supplier Payments Managing Recurring Entries Generating Reports & Information The Active Set-Up Wizard VAT Changes. Level 2 An overview of the Sage program Entering opening balances, preparing and printing a trial balance Creating customer records Creating supplier records Setting up opening assets, liabilities and capital balances, Producing routine reports Checking data, Entering supplier invoices Posting error corrections, amending records Invoicing, generating customer letters, entering new products, checking communication history Banking and payments, producing statements, petty cash Audit trails, correcting basic entry errors, reconciling debtors and creditors Creating sales credit notes, Processing purchase credit notes Preparing journals Verifying Audit Trail Purchase orders, processing sales orders Processing Trial Balance Creating Backups Restoring data Writing-off bad debts Level 3 Creating a Chart of Accounts to Suit Company Requirements Sole Trader Accounts preparation The Trial Balance preparation Errors in the Trial Balance Disputed Items Use of the Journal Prepare and Process Month End Routine Contra Entries The Government Gateway and VAT Returns Bad Debts and Provision for Doubtful Debts Prepare and Produce Final Accounts Management Information Reports Making Decisions with Reports Using Sage The Fixed Asset Register and Depreciation Accruals and Prepayments Cash Flow and Forecast Reports Advanced Credit Control

Oracle Data Integrator 19c Configuration and Administration (TTOR30319)
By Nexus Human
Duration 3 Days 18 CPD hours This course is intended for This intermediate-level hands-on course is geared for experienced Administrators, Analysts, Architects, Data Scientists, Database Administrators and Implementers Overview This course is approximately 50% hands-on, combining expert lecture, real-world demonstrations and group discussions with machine-based practical labs and exercises. Working in a hands-on learning environment led by our Oracle Certified expert facilitator, students will learn how to: Administer ODI resources and setup security with ODI Apply ODI Topology concepts for data integration Describe ODI Model concepts Describe architecture of Oracle Data Integrator Design ODI Mappings, Procedures, Packages, and Load Plans to perform ELT data transformations Explore, audit data, and enforce data quality with ODI Implement Changed Data Capture with ODI Oracle Data Integrator is a comprehensive data integration platform that covers all data integration requirements from high-volume, high-performance batch loads, to event-driven integration processes and SOA-enabled data services. Oracle Data Integrator's Extract, Load, Transform (E-LT) architecture leverages disparate RDBMS engines to process and transform the data - the approach that optimizes performance, scalability and lowers overall solution costs. Throughout this course participants will explore how to centralize data across databases, performing integration, designing ODI Mappings, and setting up ODI security. In addition, Oracle Data Integrator can interact with the various tools of the Hadoop ecosystem, allowing administrators and data scientists to farm out map-reduce operations from established relational databases to Hadoop. They can also read back into the relational world the results of complex Big Data analysis for further processing. Working in a hands-on learning environment led by our Oracle Certified expert facilitator, students will learn how to: Administer ODI resources and setup security with ODI Apply ODI Topology concepts for data integration Describe ODI Model concepts Describe architecture of Oracle Data Integrator Design ODI Mappings, Procedures, Packages, and Load Plans to perform ELT data transformations Explore, audit data, and enforce data quality with ODI Implement Changed Data Capture with ODI Introduction to Integration and Administration Oracle Data Integrator: Introduction Oracle Data Integrator Repositories Administering ODI Repositories Create and connect to the Master Repository Export and import the Master Repository Create, connect, and set a password to the Work Repository ODI Topology Concepts ODI Topology: Overview Data Servers and Physical Schemas Defining Topology Agents in Topology Planning a Topology Describing the Physical and Logical Architecture Topology Navigator Creating Physical Architecture Creating Logical Architecture Setting Up a New ODI Project ODI Projects Using Folders Understanding Knowledge Modules Exporting and Importing Objects Using Markers Oracle Data Integrator Model Concepts Understanding the Relational Model Understanding Reverse-Engineering Creating Models Organizing ODI Models and Creating ODI Datastores Organizing Models Creating Datastores Constraints in ODI Creating Keys and References Creating Conditions Exploring Your Data Constructing Business Rules ODI Mapping Concepts ODI Mappings Expressions, Join, Filter, Lookup, Sets, and Others Behind the Rules Staging Area and Execution Location Understanding Knowledge Modules Mappings: Overview Designing Mappings Multiple Sources and Joins Filtering Data Overview of the Flow in ODI Mapping Selecting a Staging Area Configuring Expressions Execution Location Selecting a Knowledge Module Mappings: Monitoring and Troubleshooting Monitoring Mappings Working with Errors Designing Mappings: Advanced Topics 1 Working with Business Rules Using Variables Datasets and Sets Using Sequences Designing Mappings: Advanced Topics 2 Partitioning Configuring Reusable Mappings Using User Functions Substitution Methods Modifying Knowledge Modules Using ODI Procedures Procedures: Overview Creating a Blank Procedure Adding Commands Adding Options Running a Procedure Using ODI Packages Packages: Overview Executing a Package Review of Package Steps Model, Submodel, and Datastore Steps Variable Steps Controlling the Execution Path Step-by-Step Debugger Starting a Debug Session New Functions Menu Bar Icons Managing ODI Scenarios Scenarios Managing Scenarios Preparing for Deployment Using Load Plans What are load plans? Load plan editor Load plan step sequence Defining restart behavior Enforcing Data Quality with ODI Data Quality Business Rules for Data Quality Enforcing Data Quality with ODI Working with Changed Data Capture CDC with ODI CDC implementations with ODI CDC implementation techniques Journalizing Results of CDC Advanced ODI Administration Setting Up ODI Security Managing ODI Reports ODI Integration with Java

MS-102T00 Microsoft 365 Administrator Essentials
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is designed for persons aspiring to the Microsoft 365 Administrator role and have completed at least one of the Microsoft 365 role-based administrator certification paths. This course covers the following key elements of Microsoft 365 administration: Microsoft 365 tenant management, Microsoft 365 identity synchronization, and Microsoft 365 security and compliance. In Microsoft 365 tenant management, you learn how to configure your Microsoft 365 tenant, including your organizational profile, tenant subscription options, component services, user accounts and licenses, security groups, and administrative roles. You then transition to configuring Microsoft 365, with a primary focus on configuring Office client connectivity. Finally, you explore how to manage user-driven client installations of Microsoft 365 Apps for enterprise deployments. The course then transitions to an in-depth examination of Microsoft 365 identity synchronization, with a focus on Microsoft Entra Connect and Connect Cloud Sync. You learn how to plan for and implement each of these directory synchronization options, how to manage synchronized identities, and how to implement password management in Microsoft 365 using multifactor authentication and self-service password management. In Microsoft 365 security management, you begin examining the common types of threat vectors and data breaches facing organizations today. You then learn how Microsoft 365?s security solutions address each of these threats. You are introduced to the Microsoft Secure Score, as well as to Microsoft Entra ID Protection. You then learn how to manage the Microsoft 365 security services, including Exchange Online Protection, Safe Attachments, and Safe Links. Finally, you are introduced to the various reports that monitor an organization?s security health. You then transition from security services to threat intelligence; specifically, using Microsoft 365 Defender, Microsoft Defender for Cloud Apps, and Microsoft Defender for Endpoint. Once you have this understanding of Microsoft 365?s security suite, you then examine the key components of Microsoft 365 compliance management. This begins with an overview of all key aspects of data governance, including data archiving and retention, Microsoft Purview message encryption, and data loss prevention (DLP). You then delve deeper into archiving and retention, paying particular attention to Microsoft Purview insider risk management, information barriers, and DLP policies. You then examine how to implement these compliance features by using data classification and sensitivity labels. Prerequisites Completed a role-based administrator course such as Messaging, Teamwork, Security, Compliance, or Collaboration. A proficient understanding of DNS and basic functional experience with Microsoft 365 services. A proficient understanding of general IT practices. A working knowledge of PowerShell. 1 - Configure your Microsoft 365 experience Explore your Microsoft 365 cloud environment Configure your Microsoft 365 organizational profile Manage your tenant subscriptions in Microsoft 365 Integrate Microsoft 365 with customer engagement apps Complete your tenant configuration in Microsoft 365 2 - Manage users, licenses, and mail contacts in Microsoft 365 Determine the user identity model for your organization Create user accounts in Microsoft 365 Manage user account settings in Microsoft 365 Manage user licenses in Microsoft 365 Recover deleted user accounts in Microsoft 365 Perform bulk user maintenance in Microsoft Entra ID Create and manage guest users Create and manage mail contacts 3 - Manage groups in Microsoft 365 Examine groups in Microsoft 365 Create and manage groups in Microsoft 365 Create dynamic groups using Azure rule builder Create a Microsoft 365 group naming policy Create groups in Exchange Online and SharePoint Online 4 - Add a custom domain in Microsoft 365 Plan a custom domain for your Microsoft 365 deployment Plan the DNS zones for a custom domain Plan the DNS record requirements for a custom domain Create a custom domain in Microsoft 365 5 - Configure client connectivity to Microsoft 365 Examine how automatic client configuration works Explore the DNS records required for client configuration Configure Outlook clients Troubleshoot client connectivity 6 - Configure administrative roles in Microsoft 365 Explore the Microsoft 365 permission model Explore the Microsoft 365 admin roles Assign admin roles to users in Microsoft 365 Delegate admin roles to partners Manage permissions using administrative units in Microsoft Entra ID Elevate privileges using Microsoft Entra Privileged Identity Management Examine best practices when configuring administrative roles 7 - Manage tenant health and services in Microsoft 365 Monitor the health of your Microsoft 365 services Monitor tenant health using Microsoft 365 Adoption Score Monitor tenant health using Microsoft 365 usage analytics Develop an incident response plan Request assistance from Microsoft 8 - Deploy Microsoft 365 Apps for enterprise Explore Microsoft 365 Apps for enterprise functionality Explore your app compatibility by using the Readiness Toolkit Complete a self-service installation of Microsoft 365 Apps for enterprise Deploy Microsoft 365 Apps for enterprise with Microsoft Configuration Manager Deploy Microsoft 365 Apps for enterprise from the cloud Deploy Microsoft 365 Apps for enterprise from a local source Manage updates to Microsoft 365 Apps for enterprise Explore the update channels for Microsoft 365 Apps for enterprise Manage your cloud apps using the Microsoft 365 Apps admin center 9 - Analyze your Microsoft 365 workplace data using Microsoft Viva Insights Examine the analytical features of Microsoft Viva Insights Explore Personal insights Explore Team insights Explore Organization insights Explore Advanced insights 10 - Explore identity synchronization Examine identity models for Microsoft 365 Examine authentication options for the hybrid identity model Explore directory synchronization 11 - Prepare for identity synchronization to Microsoft 365 Plan your Microsoft Entra deployment Prepare for directory synchronization Choose your directory synchronization tool Plan for directory synchronization using Microsoft Entra Connect Plan for directory synchronization using Microsoft Entra Connect cloud sync 12 - Implement directory synchronization tools Configure Microsoft Entra Connect prerequisites Configure Microsoft Entra Connect Monitor synchronization services using Microsoft Entra Connect Health Configure Microsoft Entra Connect cloud sync prerequisites Configure Microsoft Entra Connect cloud sync 13 - Manage synchronized identities Manage users with directory synchronization Manage groups with directory synchronization Use Microsoft Entra Connect Sync Security Groups to help maintain directory synchronization Configure object filters for directory synchronization Explore Microsoft Identity Manager Troubleshoot directory synchronization 14 - Manage secure user access in Microsoft 365 Manage user passwords Enable pass-through authentication Enable multifactor authentication Enable passwordless sign-in with Microsoft Authenticator Explore self-service password management Explore Windows Hello for Business Implement Microsoft Entra Smart Lockout Implement conditional access policies Explore Security Defaults in Microsoft Entra ID Investigate authentication issues using sign-in logs 15 - Examine threat vectors and data breaches Explore today's work and threat landscape Examine how phishing retrieves sensitive information Examine how spoofing deceives users and compromises data security Compare spam and malware Examine account breaches Examine elevation of privilege attacks Examine how data exfiltration moves data out of your tenant Examine how attackers delete data from your tenant Examine how data spillage exposes data outside your tenant Examine other types of attacks 16 - Explore the Zero Trust security model Examine the principles and components of the Zero Trust model Plan for a Zero Trust security model in your organization Examine Microsoft's strategy for Zero Trust networking Adopt a Zero Trust approach 17 - Explore security solutions in Microsoft 365 Defender Enhance your email security using Exchange Online Protection and Microsoft Defender for Office 365 Protect your organization's identities using Microsoft Defender for Identity Protect your enterprise network against advanced threats using Microsoft Defender for Endpoint Protect against cyber attacks using Microsoft 365 Threat Intelligence Provide insight into suspicious activity using Microsoft Cloud App Security Review the security reports in Microsoft 365 Defender 18 - Examine Microsoft Secure Score Explore Microsoft Secure Score Assess your security posture with Microsoft Secure Score Improve your secure score Track your Microsoft Secure Score history and meet your goals 19 - Examine Privileged Identity Management Explore Privileged Identity Management in Microsoft Entra ID Configure Privileged Identity Management Audit Privileged Identity Management Control privileged admin tasks using Privileged Access Management 20 - Examine Azure Identity Protection Explore Azure Identity Protection Enable the default protection policies in Azure Identity Protection Explore the vulnerabilities and risk events detected by Azure Identity Protection Plan your identity investigation 21 - Examine Exchange Online Protection Examine the anti-malware pipeline Detect messages with spam or malware using Zero-hour auto purge Explore anti-spoofing protection provided by Exchange Online Protection Explore other anti-spoofing protection Examine outbound spam filtering 22 - Examine Microsoft Defender for Office 365 Climb the security ladder from EOP to Microsoft Defender for Office 365 Expand EOP protections by using Safe Attachments and Safe Links Manage spoofed intelligence Configure outbound spam filtering policies Unblock users from sending email 23 - Manage Safe Attachments Protect users from malicious attachments by using Safe Attachments Create Safe Attachment policies using Microsoft Defender for Office 365 Create Safe Attachments policies using PowerShell Modify an existing Safe Attachments policy Create a transport rule to bypass a Safe Attachments policy Examine the end-user experience with Safe Attachments 24 - Manage Safe Links Protect users from malicious URLs by using Safe Links Create Safe Links policies using Microsoft 365 Defender Create Safe Links policies using PowerShell Modify an existing Safe Links policy Create a transport rule to bypass a Safe Links policy Examine the end-user experience with Safe Links 25 - Explore threat intelligence in Microsoft 365 Defender Explore Microsoft Intelligent Security Graph Explore alert policies in Microsoft 365 Run automated investigations and responses Explore threat hunting with Microsoft Threat Protection Explore advanced threat hunting in Microsoft 365 Defender Explore threat analytics in Microsoft 365 Identify threat issues using Microsoft Defender reports 26 - Implement app protection by using Microsoft Defender for Cloud Apps Explore Microsoft Defender Cloud Apps Deploy Microsoft Defender for Cloud Apps Configure file policies in Microsoft Defender for Cloud Apps Manage and respond to alerts in Microsoft Defender for Cloud Apps Configure Cloud Discovery in Microsoft Defender for Cloud Apps Troubleshoot Cloud Discovery in Microsoft Defender for Cloud Apps 27 - Implement endpoint protection by using Microsoft Defender for Endpoint Explore Microsoft Defender for Endpoint Configure Microsoft Defender for Endpoint in Microsoft Intune Onboard devices in Microsoft Defender for Endpoint Manage endpoint vulnerabilities with Microsoft Defender Vulnerability Management Manage device discovery and vulnerability assessment Reduce your threat and vulnerability exposure 28 - Implement threat protection by using Microsoft Defender for Office 365 Explore the Microsoft Defender for Office 365 protection stack Investigate security attacks by using Threat Explorer Identify cybersecurity issues by using Threat Trackers Prepare for attacks with Attack simulation training 29 - Examine data governance solutions in Microsoft Purview Explore data governance and compliance in Microsoft Purview Protect sensitive data with Microsoft Purview Information Protection Govern organizational data using Microsoft Purview Data Lifecycle Management Minimize internal risks with Microsoft Purview Insider Risk Management Explore Microsoft Purview eDiscovery solutions 30 - Explore archiving and records management in Microsoft 365 Explore archive mailboxes in Microsoft 365 Enable archive mailboxes in Microsoft 365 Explore Microsoft Purview Records Management Implement Microsoft Purview Records Management Restore deleted data in Exchange Online Restore deleted data in SharePoint Online 31 - Explore retention in Microsoft 365 Explore retention by using retention policies and retention labels Compare capabilities in retention policies and retention labels Define the scope of a retention policy Examine the principles of retention Implement retention using retention policies, retention labels, and eDiscovery holds Restrict retention changes by using Preservation Lock 32 - Explore Microsoft Purview Message Encryption Examine Microsoft Purview Message Encryption Configure Microsoft Purview Message Encryption Define mail flow rules to encrypt email messages Add organizational branding to encrypted email messages Explore Microsoft Purview Advanced Message Encryption 33 - Explore compliance in Microsoft 365 Plan for security and compliance in Microsoft 365 Plan your beginning compliance tasks in Microsoft Purview Manage your compliance requirements with Compliance Manager Examine the Compliance Manager dashboard Analyze the Microsoft Compliance score 34 - Implement Microsoft Purview Insider Risk Management Explore insider risk management Plan for insider risk management Explore insider risk management policies Create insider risk management policies Investigate insider risk management activities and alerts Explore insider risk management cases 35 - Implement Microsoft Purview Information Barriers Explore Microsoft Purview Information Barriers Configure information barriers in Microsoft Purview Examine information barriers in Microsoft Teams Examine information barriers in OneDrive Examine information barriers in SharePoint 36 - Explore Microsoft Purview Data Loss Prevention Examine Data Loss Prevention Explore Endpoint data loss prevention Examine DLP policies View DLP policy results Explore DLP reports 37 - Implement Microsoft Purview Data Loss Prevention Plan to implement Microsoft Purview Data Loss Protection Implement Microsoft Purview's default DLP policies Design a custom DLP policy Create a custom DLP policy from a template Configure email notifications for DLP policies Configure policy tips for DLP policies 38 - Implement data classification of sensitive information Explore data classification Implement data classification in Microsoft 365 Explore trainable classifiers Create and retrain a trainable classifier View sensitive data using Content explorer and Activity explorer Detect sensitive information documents using Document Fingerprinting 39 - Explore sensitivity labels Manage data protection using sensitivity labels Explore what sensitivity labels can do Determine a sensitivity label's scope Apply sensitivity labels automatically Explore sensitivity label policies 40 - Implement sensitivity labels Plan your deployment strategy for sensitivity labels Examine the requirements to create a sensitivity label Create sensitivity labels Publish sensitivity labels Remove and delete sensitivity labels Additional course details: Nexus Humans MS-102T00: Microsoft 365 Administrator training program is a workshop that presents an invigorating mix of sessions, lessons, and masterclasses meticulously crafted to propel your learning expedition forward. This immersive bootcamp-style experience boasts interactive lectures, hands-on labs, and collaborative hackathons, all strategically designed to fortify fundamental concepts. Guided by seasoned coaches, each session offers priceless insights and practical skills crucial for honing your expertise. Whether you're stepping into the realm of professional skills or a seasoned professional, this comprehensive course ensures you're equipped with the knowledge and prowess necessary for success. While we feel this is the best course for the MS-102T00: Microsoft 365 Administrator course and one of our Top 10 we encourage you to read the course outline to make sure it is the right content for you. Additionally, private sessions, closed classes or dedicated events are available both live online and at our training centres in Dublin and London, as well as at your offices anywhere in the UK, Ireland or across EMEA.
