- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Attachment courses delivered Online
We couldn't find any listings for your search. Explore our online options and related educators below to see if they help you.
Know someone teaching this? Help them become an Educator on Cademy.
Online Options
Show all 595Child Attachment Level 3
By The Teachers Training
Dive deep into understanding child attachment with our Level 3 Course. Gain comprehensive knowledge on the importance of secure attachment in child development. Explore theories, practical strategies, and interventions to promote healthy attachment bonds between children and caregivers. Whether you're a childcare professional, educator, or parent, this course equips you with essential skills to support emotional well-being and resilience in children. Enroll now and elevate your understanding of child attachment to positively impact the lives of young ones.

Attachment-Based Therapy focuses on understanding and improving attachment styles formed in early childhood. This therapy helps couples address how these attachment styles affect their current relationship, promoting secure and healthy bonds. Key areas: attachment styles, early childhood, secure bonds, healthy relationships, emotional attachment 3 x 1 hour sessions

ATTACHMENT DIFFICULTIES: INCLUDING CHILDREN
By Inclusive Solutions
This is a practical ‘non medical’ day for front line practitioners working with children and young people with serious attachment issues arising from loss, trauma and abuse. We look at what Psychology may help us in our understanding of children who have faced issues with love and attachment. Splitting, handling projected feelings, constancy and permanence are explored. Online Course now available via Teachable Platform – Understanding Attachment Learn at your own pace… lots of text and video support Course Category Meeting emotional needs Behaviour and Relationships Inclusion Teaching and Learning Description This is a practical ‘non medical’ day for front line practitioners working with children and young people with serious attachment issues arising from loss, trauma and abuse. Drawing from the international research and literature and our own experience over many years as educational psychologists of the challenges of children with major social and emotional needs, we will explore together what the best practice can and could look like. We explore the language of attachment and outline very practical classroom strategies. We look at what Psychology may help us in our understanding of children who have faced issues with love and attachment. We explore the feelings of being on a desolate island of relational poverty or to imagine swimming with sharks. We explore the themes of violence, anxiety and experience of being a victim as young people grow older. We look at telling lies and explore how we can respectfully understand this. We reveal the new and innovative compass of vulnerability – the cognitive errors to which some are much more vulnerable. We look at triggers, self regulation and unpack a range of strategies. Transference and counter transference are examined along with splitting, handling projected feelings, constancy and permanence. We explore what young people with these difficulties really need from us. We also spend time looking at the emotional impact on practitioners working with children with such needs and what helps at an personal and team level. We can all do something – we do not have to wait for expert therapists to arrive! Testimonials Very moving presentation I will always try and think behind the behaviour now It had a huge impact on all levels We all seem to need it Belonging and feelings are so important Very user friendly Excellent! Learning Objectives Increased confidence regarding developing inclusive practice for children with serious attachment needs in mainstream schools Simple understandable explanation of attachment understood Access to a wider range of practical strategies to impact on social and behavioural needs Deeper understanding of core values surrounding inclusion of emotionally disabled children Opportunity to reflect on professional attitudes and behaviour towards parents and pupils with complex emotional needs New skills, scripts and processes to make inclusion successful Who Is It For ? Practitioners working in schools and other settings with children and young people of all ages Key workers Teaching Assistants with support roles Heads and deputies SENCOs Advanced skills teachers Primary and secondary classroom teachers Parents Local authority support services Course Content The course explores the questions : How can we start to develop an understanding of children with attachment needs? What is the true impact of loss, trauma and abuse? What else can we do to go about including high profile children or young people with challenging emotional needs? What useful psychological constructs can we use to guide us? This course also explores practical strategies and language for key adults rebuilding relationships with individual pupils. This is a participative day that aims to be explorative and practical. Opportunities to develop empathy with the children of concern will be created.
Child Attachment Level 3
By The Teachers Training
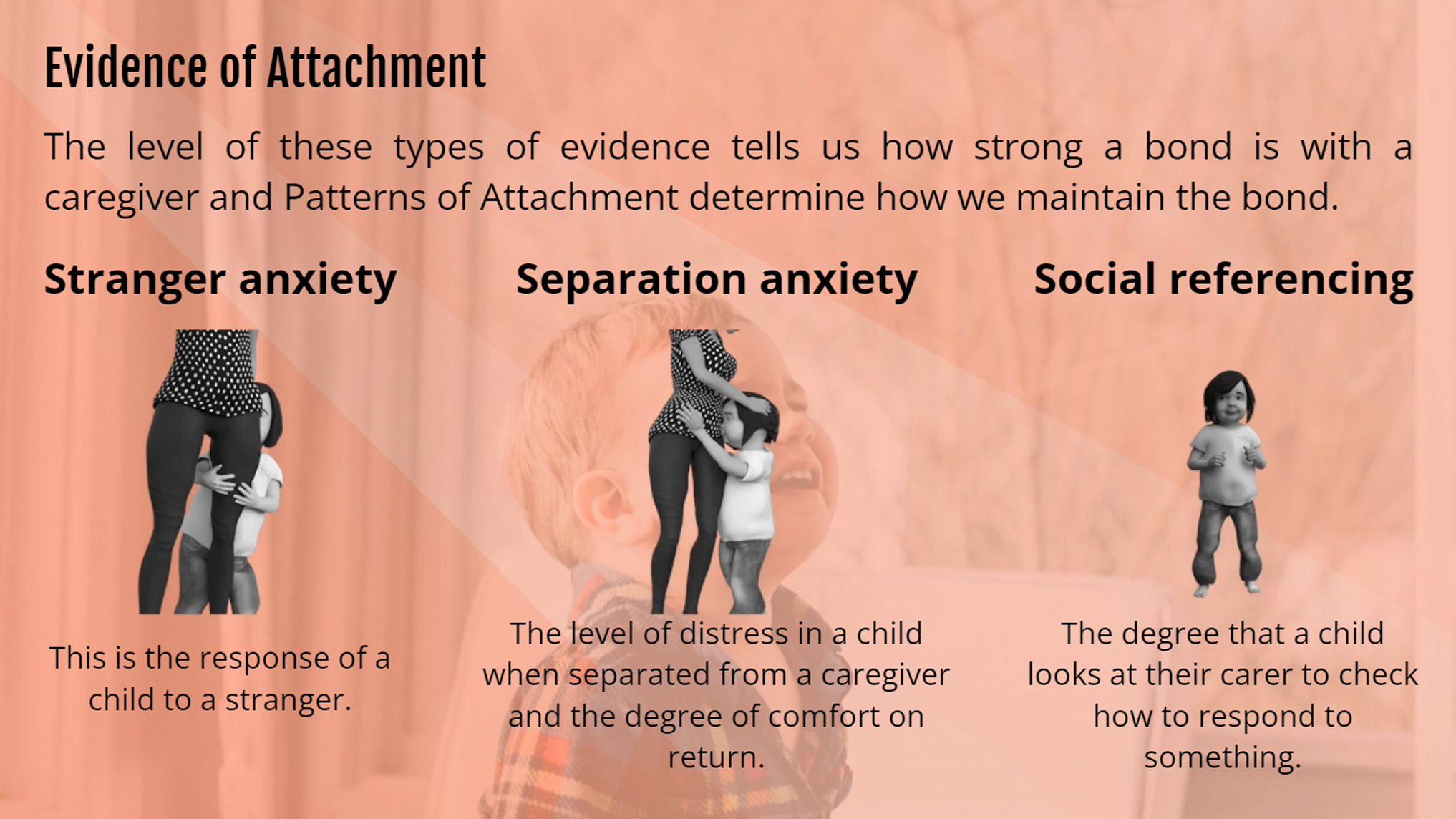
Child Attachment Level 3 Learn the secrets of child attachment and nurture lifelong bonds with our Child Attachment Level 3 course! This course is tailor-made for parents seeking to deepen their understanding of child attachment and create secure, nurturing bonds. It's also ideal for aspiring child psychologists eager to gain expertise in this vital field. At the beginning of the Child Attachment Level 3 course, you will gain in-depth knowledge of attachment and explore the fundamental needs for safety, security, and protection that shape a child's world. Here, you will discover the activation and termination of attachment behaviour and its significance-the four phases of attachment development, from infancy to adulthood. Besides, in this course, you will gain insights into child psychology and how environmental factors impact a child's growth. A good grasp of attachment theories will give you a better understanding of child attachment issues. Therefore, this course will educate you about Bowlby's groundbreaking insights and Ainsworth's 'Strange Situation' study. As you move deeper into the course, you will understand the role of attachment in shaping a child's personality and emotional development. Moreover, in this Child Attachment Level 3 course, you will learn how to assess attachment and recognize attachment disorders like Reactive Attachment Disorder (RAD) and Disinhibited Attachment Disorder (DAD). You will also learn to apply attachment-focused parenting techniques to build strong, lasting connections with your child. Finally, the Child Attachment Level 3 course finishes by introducing you to versatile intervention and support strategies like parent-infant & young-child interventions, enhancing parental sensitivity and responsiveness at the behavioural level, Join us and become a source of love, support, and guidance for the young minds that shape our future. Why Choose Teachers Training Some of our website features are: This is a dedicated website for teaching 24/7 tutor support Interactive Content Affordable price Courses accredited by the UK's top awarding bodies 100% online Flexible deadline Entry Requirements No formal entry requirements. You need to have: Passion for learning A good understanding of the English language Be motivated and hard-working Over the age of 16. Certification Successfully completing the MCQ exam of this course qualifies you for a CPD-accredited certificate from The Teachers Training. You will be eligible for both PDF copy and hard copy of the certificate to showcase your achievement however you wish. You can get your digital certificate (PDF) for £4.99 only Hard copy certificates are also available, and you can get one for only £10.99 You can get both PDF and Hard copy certificates for just £12.99! The certificate will add significant weight to your CV and will give you a competitive advantage when applying for jobs. Module 01: Introduction to Child Attachment Introduction to Child Attachment 00:21:00 Module 02: Introduction to Child Psychology Introduction to Child Psychology 00:28:00 Module 03: Fundamentals of Attachment Theory Fundamentals of Attachment Theory 00:21:00 Module 04: Assessments of Attachment Assessments of Attachment 00:16:00 Module 05: Attachment Disorder Attachment Disorder 00:17:00 Module 06: Attachment-Focused Parenting Attachment-Focused Parenting 00:22:00 Module 07: Emotions and Mind-Mindedness Emotions and Mind-Mindedness 00:13:00 Module 08: Interventions, Treatment and Support Interventions, Treatment and Support 00:15:00

48-Hour Knowledge Knockdown! Prices Reduced Like Never Before! In the UK, over 70% of children have secure attachments to their caregivers. However, around 30% of children have insecure attachments, which can lead to a range of problems, including mental health difficulties, behavioral problems, and relationship difficulties. This Certificate in Child Attachment Training at QLS Level 3 course is endorsed by The Quality Licence Scheme and accredited by CPDQS (with 120 CPD points) to make your skill development & career progression more accessible than ever! Child attachment is a critical aspect of emotional and social development. Secure attachments provide children with a foundation of safety and trust, which enables them to explore the world and learn new things with confidence. In contrast, insecure attachments can lead to a variety of problems, including anxiety, depression, and difficulty forming relationships. This Child Attachment is a course designed to equip learners with a profound understanding of child attachment, a fundamental aspect of child psychology. Throughout the eight modules, participants will delve into the core concepts of attachment theory, explore assessments of attachment, and gain insights into attachment disorders. The Child Attachment course goes beyond theory by emphasising practical aspects, including attachment-focused parenting, emotional intelligence, and interventions. Learning Outcomes of Child Attachment Course: Analyse and apply foundational concepts of attachment theory in professional practice. Conduct comprehensive assessments of attachment to inform tailored intervention strategies. Understand and manage attachment disorders, fostering healthy emotional development in children. Implement effective attachment-focused parenting strategies to enhance parent-child relationships. Promote emotional intelligence and mind-mindedness, contributing to overall well-being in children. Demonstrate proficiency in intervention techniques, providing meaningful support for children and families. Seize the opportunity in a growing job market, where professionals with expertise are in high demand, experiencing a remarkable 20% increase in job opportunities in the past year alone. Enrol now and become a sought-after specialist in nurturing healthy attachments for a brighter future. Why Choose Our Child Attachment Course? FREE Child Attachment certificate endorsed by the Quality Licence Scheme. Get a free student ID card with Child Attachment Training Get instant access to this Child Attachment course. Learn Child Attachment from anywhere in the world The Child Attachment is affordable and simple to understand The Child Attachment is an entirely online, interactive lesson with voiceover audio Lifetime access to the Child Attachment course materials The Child Attachment comes with 24/7 tutor support So enrol now in this Child Attachment Today to advance your career! Take a step toward a brighter future with our Child Attachment course! *** Course Curriculum *** Here is the curriculum breakdown of the Child Attachment at QLS Level 3 course: Module 01: Introduction to Child Attachment Module 02: Introduction to Child Psychology Module 03: Fundamentals of Attachment Theory Module 04: Assessments of Attachment Module 05: Attachment Disorder Module 06: Attachment-Focused Parenting Module 07: Emotions and Mind-Mindedness Module 08: Interventions, Treatment and Support Assessment Process of Certificate in Child Attachment Training at QLS Level 3: You have to complete the assignment questions given at the end of the course and score a minimum of 60% to pass each exam. After passing the Certificate in Child Attachment Training at QLS Level 3 exam, you will be able to request a certificate endorsed by the Quality Licence Scheme absolutely FREE of cost. CPD 120 CPD hours / points Accredited by CPD Quality Standards Who is this course for? This Child Attachment at QLS Level 3 course is perfect for highly motivated people who want to improve their technical skills and prepare for the career they want! Requirements Child Attachment at QLS Level 3 You will not need any prior background or expertise in this Child Attachment at QLS Level 3 course. Career path This Child Attachment at QLS Level 3 will allow you to kickstart or take your career to the next stage in the related sector such as: Child psychologist. Childcare counselor. School counselor. Family therapist. Social worker. Attachment specialist. Certificates Certificate in Child Attachment Training at QLS Level 3 Hard copy certificate - Included CPDQS Accredited PDF Certificate Digital certificate - Included

Description Attachment is the strong, long lasting bond that develops between a baby and his or her primary caregiver. This Child Attachment Diploma would be of value to anyone who works or lives with children and an ideal course for teachers wanting to get some background information on the psychological understanding of the 'Little people'. The course will teach you how to think like a true expert in the field of child attachment theory. You will be taught the signs to look out for when there are any issues in this field and there are tests that can be implemented along the way to better facilitate this. This course explains the main concepts and it cover all the fundamental points for you. By the end of the course, you will be able to apply the guiding principles of child attachment theory with relative ease. Assessment: This course does not involve any MCQ test. Students need to answer assignment questions to complete the course, the answers will be in the form of written work in pdf or word. Students can write the answers in their own time. Once the answers are submitted, the instructor will check and assess the work. Certification: After completing and passing the course successfully, you will be able to obtain an Accredited Certificate of Achievement. Certificates can be obtained either in hard copy at a cost of £39 or in PDF format at a cost of £24. Who is this Course for? Child Attachment Diploma is certified by CPD Qualifications Standards and CiQ. This makes it perfect for anyone trying to learn potential professional skills. As there is no experience and qualification required for this course, it is available for all students from any academic background. Requirements Our Child Attachment Diploma is fully compatible with any kind of device. Whether you are using Windows computer, Mac, smartphones or tablets, you will get the same experience while learning. Besides that, you will be able to access the course with any kind of internet connection from anywhere at any time without any kind of limitation. Career Path After completing this course you will be able to build up accurate knowledge and skills with proper confidence to enrich yourself and brighten up your career in the relevant job market. Module 01 Introduction to Child Attachment 00:30:00 Types of Attachment 00:30:00 Different Types of Attachment Styles 00:30:00 Attachment: The Dance of Relationship 00:30:00 Patterns of Attachment 00:30:00 Attachment Theory: The Importance of Early Emotional Bonds 00:30:00 Attachment and Emotional Resilience 00:15:00 How the Process of Attachment Works and Developmental Process 00:15:00 Models of Attachment: Internal Working Models 00:30:00 Module 02 Attachment and Bereavement 00:10:00 Influences of Attachment within the Cognitive Stage of Development 00:15:00 Caregiver and Child Influences on Attachment 00:30:00 Attachment Under Adversity 00:30:00 Understanding the Strange Situation Test 00:30:00 The Vulnerable Child 00:10:00 Developing Emotional Attachments in Adopted Children 00:30:00 Employment Opportunities in the Field of Child Attachment 00:10:00 Attachment Key Term Glossary 00:05:00 Certificate and Transcript Order Your Certificates and Transcripts 00:00:00

Child attachment is related to feelings of insecurity in children, where children their parent or primary caregiver as a safe base to explore. In the Child Attachment certificate, you will learn the key theories and main contributors in this field, deepening your understanding of the causes and development of child attachment. This online child attachment training course is ideal for parents and those who work with children. It is the perfect stepping stone for aspiring experts pursuing a career in child psychology who want to learn about the history and evolution of child attachment theory, including the different schools of thought. Gain the practical skills and knowledge to effectively deal with attachment issues in children, and learn about the influences of child attachment to overcome any challenges in this area effectively. Learning outcomes Deepen your understanding of child attachment and its key theories Learn about the internal working models that are applied in this field Understand the main contributors to this field and their schools of thought Gain the skills and practical knowledge to deal with issues of attachment effectively Learn about the concept of vulnerability in regard to child attachment Develop your knowledge of the ethical considerations of child attachment Gain an in-depth understanding of the key influences of child attachment Learn how child attachment stabilises in later childhood Description The Child Attachment Diploma training course is delivered through Janets' online learning platform. Access the Child Attachment Diploma content from any internet-enabled device whenever or wherever you want to. The Child Attachment Diploma course has no formal teaching deadlines, meaning you are free to complete the course at your own pace. Certificate of Achievement Endorsed Certificate of Achievement from the Quality Licence Scheme Once the course has been completed and the assessment has been passed, all students are entitled to receive an endorsed certificate. This will provide proof that you have completed your training objectives, and each endorsed certificate can be ordered and delivered to your address for only £69. Please note that overseas students may be charged an additional £10 for postage. CPD Certificate of Achievement from Janets Upon successful completion of the course, you will be able to obtain your course completion e-certificate free of cost. Print copy by post is also available at an additional cost of £9.99 and PDF Certificate at £4.99. Endorsement This course and/or training programme has been endorsed by the Quality Licence Scheme for its high-quality, non-regulated provision and training programmes. This course and/or training programme is not regulated by Ofqual and is not an accredited qualification. Your training provider will be able to advise you on any further recognition, for example progression routes into further and/or higher education. For further information please visit the Learner FAQs on the Quality Licence Scheme website. Method of Assessment To verify your enhanced skills in the subject, we recommend that you also complete the assignment questions. These can be completed at any time which is convenient for yourself and will be assessed by our in-house specialised tutors. Full feedback will then be given on your current performance, along with any further advice or support. Who is this Course for This course is ideal for parents, primary caregivers, and those who work with children. It is suitable for those looking to start a career in child psychology and wish to learn more about the different theories of attachment. There are no specific entry requirements for this course, which can be studied on a part-time or full-time basis. Requirements The Child Attachment Diploma is open to all students and has no formal entry requirements. To study the Child Attachment Diploma course, all your need is a passion for learning, a good understanding of English, numeracy, and IT skills. You must also be over the age of 16. Career Path On successful completion of this course, learners will have the practical and theoretical knowledge to understand the many different theories associated with child attachment. It will equip learners with the skills to explore the following related professions: Childminder/Nanny EYFS Teacher Child Psychologist Child Counsellor Course Content Module 01: Introduction to Child Attachment Introduction to Child Attachment 00:21:00 Module 02: Introduction to Child Psychology Introduction to Child Psychology 00:28:00 Module 03: Fundamentals of Attachment Theory Fundamentals of Attachment Theory 00:21:00 Module 04: Assessments of Attachment Assessments of Attachment 00:16:00 Module 05: Attachment Disorder Attachment Disorder 00:17:00 Module 06: Attachment-Focused Parenting Attachment-Focused Parenting 00:22:00 Module 07: Emotions and Mind-Mindedness Emotions and Mind-Mindedness 00:13:00 Module 08: Interventions, Treatment and Support Interventions, Treatment and Support 00:15:00 Assignment Assignment - Child Attachment Diploma 6 days, 3 hours Order Your Certificate Order your Certificate QLS 00:00:00 Frequently Asked Questions Are there any prerequisites for taking the course? There are no specific prerequisites for this course, nor are there any formal entry requirements. All you need is an internet connection, a good understanding of English and a passion for learning for this course. Can I access the course at any time, or is there a set schedule? You have the flexibility to access the course at any time that suits your schedule. Our courses are self-paced, allowing you to study at your own pace and convenience. How long will I have access to the course? For this course, you will have access to the course materials for 1 year only. This means you can review the content as often as you like within the year, even after you've completed the course. However, if you buy Lifetime Access for the course, you will be able to access the course for a lifetime. Is there a certificate of completion provided after completing the course? Yes, upon successfully completing the course, you will receive a certificate of completion. This certificate can be a valuable addition to your professional portfolio and can be shared on your various social networks. Can I switch courses or get a refund if I'm not satisfied with the course? We want you to have a positive learning experience. If you're not satisfied with the course, you can request a course transfer or refund within 14 days of the initial purchase. How do I track my progress in the course? Our platform provides tracking tools and progress indicators for each course. You can monitor your progress, completed lessons, and assessments through your learner dashboard for the course. What if I have technical issues or difficulties with the course? If you encounter technical issues or content-related difficulties with the course, our support team is available to assist you. You can reach out to them for prompt resolution.

Overview Uplift Your Career & Skill Up to Your Dream Job - Learning Simplified From Home! Kickstart your career & boost your employability by helping you discover your skills, talents and interests with our special Child Attachment Diploma Course. You'll create a pathway to your ideal job as this course is designed to uplift your career in the relevant industry. It provides professional training that employers are looking for in today's workplaces. The Child Attachment Diploma Course is one of the most prestigious training offered at StudyHub and is highly valued by employers for good reason. This Child Attachment Diploma Course has been designed by industry experts to provide our learners with the best learning experience possible to increase their understanding of their chosen field. This Child Attachment Diploma Course, like every one of Study Hub's courses, is meticulously developed and well researched. Every one of the topics is divided into elementary modules, allowing our students to grasp each lesson quickly. At StudyHub, we don't just offer courses; we also provide a valuable teaching process. When you buy a course from StudyHub, you get unlimited Lifetime access with 24/7 dedicated tutor support. Why buy this Child Attachment Diploma? Unlimited access to the course for forever Digital Certificate, Transcript, student ID all included in the price Absolutely no hidden fees Directly receive CPD accredited qualifications after course completion Receive one to one assistance on every weekday from professionals Immediately receive the PDF certificate after passing Receive the original copies of your certificate and transcript on the next working day Easily learn the skills and knowledge from the comfort of your home Certification After studying the course materials of the Child Attachment Diploma there will be a written assignment test which you can take either during or at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £5.99. Original Hard Copy certificates need to be ordered at an additional cost of £9.60. Who is this course for? This Child Attachment Diploma course is ideal for Students Recent graduates Job Seekers Anyone interested in this topic People already working in the relevant fields and want to polish their knowledge and skill. Prerequisites This Child Attachment Diploma does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Child Attachment Diploma was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Career path As this course comes with multiple courses included as bonus, you will be able to pursue multiple occupations. This Child Attachment Diploma is a great way for you to gain multiple skills from the comfort of your home. Course Curriculum Module 01: Introduction to Child Attachment Introduction to Child Attachment 00:21:00 Module 02: Introduction to Child Psychology Introduction to Child Psychology 00:28:00 Module 03: Fundamentals of Attachment Theory Fundamentals of Attachment Theory 00:21:00 Module 04: Assessments of Attachment Assessments of Attachment 00:16:00 Module 05: Attachment Disorder Attachment Disorder 00:17:00 Module 06: Attachment-Focused Parenting Attachment-Focused Parenting 00:22:00 Module 07: Emotions and Mind-Mindedness Emotions and Mind-Mindedness 00:13:00 Module 08: Interventions, Treatment and Support Interventions, Treatment and Support 00:15:00 Assignment Assignment - Child Attachment Diploma 00:00:00