- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
Computer Networking Course Online
By Hi-Tech Training
Computer Networking Online Virtual Classroom course is designed to enable participants to install, configure and test a fundamental computer network. The opportunities for employment within the area of network support are enormous as businesses continue to grow and utilise the new technology available to them. This is a vital role to ensure the smooth running of businesses reliant on their network and IT systems. This course provides learners with both the practical and theoretical knowledge of networks. During the course, participants will learn about the different components used to create a network including hardware, software and topologie

Fire Alarm Foundation Course
By Hi-Tech Training
The Fire Alarm Foundation course is designed to give participants a practical knowledge of the operation and installation of Fire Alarm Systems at a foundation level. During this practical and theory-based course students will gain the skills and knowledge to install and wire up a Fire Alarm Control Panel to typical auxiliary equipment such as Break Glass Units, Smoke Detectors, Heat Detectors, Bells, and Sirens.

Digital, Text & Voice Communicators Course
By Hi-Tech Training
The Hi-Tech Training Digital Text & Voice Communicator Course is designed to provide participants with the skills required to connect Digital, Text & Voice Communicators to an Alarm Control Panel for transmission of Digital status signals via the telephone line, GSM Network or IP network to a central monitoring station. The Digital Communicator Course’s practical application and our highly experienced trainers ensure that this course is second to none. The course is technical and practical in nature and is suitable for participants who have successfully completed the Hi-Tech Training Intruder Alarm Installation Course or equivalent.
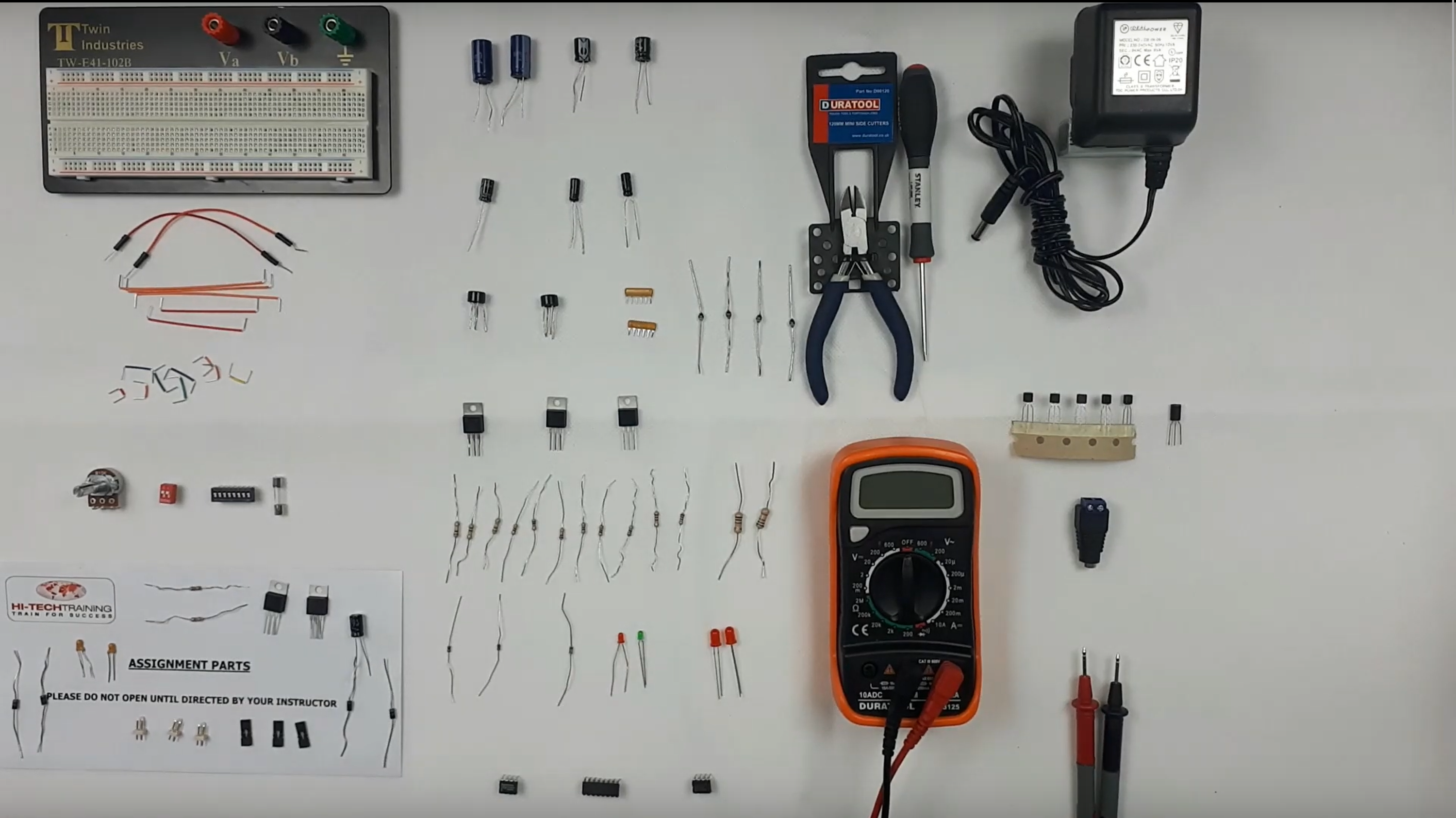
Electronics Repair 2 Course
By Hi-Tech Training
Electronics Equipment Repair 2 (Online Virtual Classroom) is a follow on course to Electronics Equipment Repair 1. This course builds on the skills gained and enables participants to build, test and fault-find more complex Analogue Electronic circuits
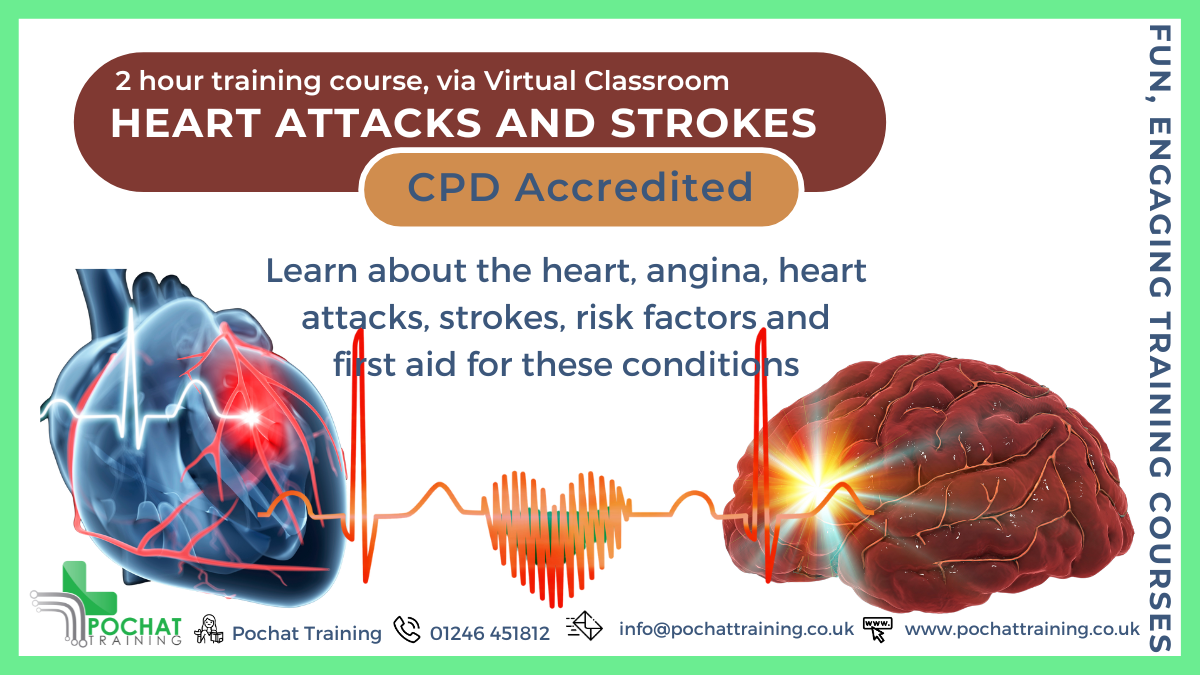
CPD Accredited, Interactive Short Course 2 hr session Do you know what a heart attack or a stroke really is? Would you know what to do to ensure the best possible outcome? Course Contents: How the Heart Functions (overview) Coronary Arteries and Collateral Circulation Atherosclerosis Angina Pectoris Myocardial Infarction (Heart Attack) Treatments and First Aid Treatments Stroke Haemorraghic Stroke, Ischaemic Stroke, Transient Iscaemic Attacks Signs & Symptoms of strokes First Aid Treatment Risk Factors for Angina, Heart Attacks and Strokes Benefits of this Short Course: Learning from home is a good way to keep one's skills and knowledge up to date Over 900,000 people in the UK live with heart failure In the UK, there are more than 100,000 hospital admissions each year due to heart attacks There are also more than 100,000 strokes in the UK each year Would you know what to do to save their life? You can make a huge difference, so join our webinar to find out how
FinTech and Big Data Analytics
By NextGen Learning
Course Overview: The "FinTech and Big Data Analytics" course provides an in-depth exploration of the dynamic intersection between financial technology (FinTech) and big data. Learners will gain essential knowledge about the innovative solutions disrupting the financial services industry, such as cryptocurrencies, insurtech, and regtech. The course offers insights into the tools, technologies, and trends shaping the future of finance, with a specific focus on how big data analytics is transforming business models and decision-making. By the end of the course, learners will have a comprehensive understanding of FinTech's growth and its applications, enabling them to make informed decisions in this rapidly evolving field. Course Description: This course delves deeper into the core concepts of financial technology and big data, exploring the impact of FinTech innovations on traditional financial systems. Topics covered include the rise of cryptocurrencies, regulatory technology (RegTech), the development of insurance technologies (InsurTech), and the use of big data in reshaping business strategies. Learners will explore the key technologies that drive FinTech, such as blockchain, artificial intelligence (AI), and machine learning, and learn how they enable data-driven decision-making in finance. The course prepares learners for the evolving future of FinTech, equipping them with the necessary skills to understand and navigate this transformative landscape. Course Modules: Module 01: Introduction to Financial Technology – FinTech Module 02: Exploring Cryptocurrencies Module 03: RegTech Module 04: Rise of InsurTechs Module 05: Big Data Basics: Understanding Big Data Module 06: The Future of FinTech (See full curriculum) Who is this course for? Individuals seeking to understand the financial technology landscape. Professionals aiming to advance their careers in the rapidly evolving FinTech sector. Beginners with an interest in emerging financial technologies and data analytics. Entrepreneurs looking to innovate within the financial services industry. Career Path: Financial Analyst FinTech Specialist Data Analyst in Financial Services Blockchain Developer RegTech Consultant InsurTech Specialist Big Data Analyst in Finance

LTE Airside training course description This course provides a concise insight into the LTE airside. Key parts of the course are detailed looks at the air interface protocol stack, cell acquisition, transmission and reception of data and of he layer 1 procedures along with layer 2 procedures. What will you learn Explain the RF optimisation flowchart. Describe the importance of Reference Signal Received Power (RSRP). List many of the 3GPP recommended KPIs. Describe the concept of APN AMBR and UE AMBR within LTE. Describe the use of planning and optimisation computer tools. LTE Airside training course details Who will benefit: Anyone working with LTE. Prerequisites: Essential LTE Duration 2 days LTE Airside training course contents Introduction and review of LTE This section describes the requirements of LTE and key technical features, and reviews the system architecture. LTE Architecture, UE, E-UTRAN and EPC. Specifications. OFDMA, SC-FDMA and MIMO antennas This section describes the techniques used in the LTE air interface, notably orthogonal frequency division multiple access (OFDMA) and multiple input multiple output (MIMO) antennas. Communication techniques for fading multipath channels. OFDMA, FFT processing and cyclic prefix insertion. SC-FDMA in the LTE uplink. Multiple antenna techniques including transmit & receive diversity and spatial multiplexing. Introduction to the air interface This section covers the operation of the air interface, the channels that it uses, and the mapping to the time and frequency domains of OFDMA and SC-FDMA. Air interface protocol stack. Logical, transport and physical channels. Frame and slot structure, the resource grid. Resource element mapping of the physical channels and physical signals. LTE spectrum allocation. Cell acquisition This is the first of three sections covering the air interface physical layer. Here, we cover mobile procedures to start low-level communications with the cell, and base station transmission of the corresponding information. Primary/secondary synchronisation signals. Downlink reference signals. The master information block. Physical control format indicator channel. Organisation and transmission of the system information. Data transmission and reception In this section, we cover procedures used for data transmission and reception on the shared channels, and describe in detail the individual steps. Data transmission and reception on the uplink and downlink. Scheduling commands and grants on the PDCCH. DL-SCH and UL-SCH. Physical channel processing of the PDSCH and PUSCH. Hybrid ARQ indicators on the PHICH. Uplink control information on the PUCCH. Uplink demodulation and sounding reference signals. Additional physical layer procedure This section concludes our discussion of the air interface physical layer, by discussing a number of procedures that support its operation. Transmission of the physical random access channel. Contention and non-contention based random access procedures. Discontinuous transmission in idle and connected modes. Uplink power control and timing advance. Air interface layer 2 This section describes the architecture and operation of layer 2 of the air interface protocol stack. MAC protocol, interactions with the physical layer, use for scheduling. RLC protocol, transparent, unacknowledged and acknowledged modes. PDCP, including header compression, security functions and recovery from handover.

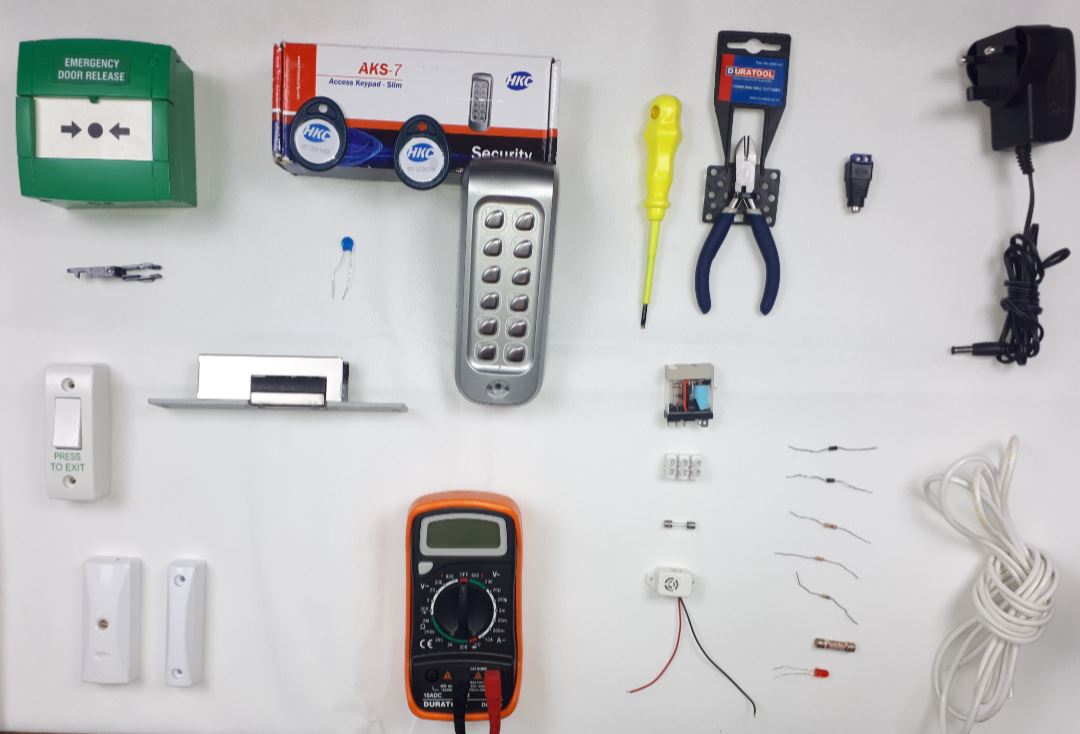
Access Control Course
By Hi-Tech Training
An effective Access Control System can form an integral part of an effective security system. At Hi-Tech Training our course is designed to give participants a practical knowledge of the operation and installation of Access Control Systems. Our experience has taught us that in order to gain the required skills an installer needs to learn through as much practical training as possible. This course involves 50% “Hands-On” training which involves building, setting up, testing and troubleshooting faults using core elements of modern Access Control Systems. At the end of the course, an interested and hardworking participant will have a good solid foundation of knowledge of what access control is all about.
Securing UNIX systems training course description This course teaches you everything you need to know to build a safe Linux environment. The first section handles cryptography and authentication with certificates, openssl, mod_ssl, DNSSEC and filesystem encryption. Then Host security and hardening is covered with intrusion detection, and also user management and authentication. Filesystem Access control is then covered. Finally network security is covered with network hardening, packet filtering and VPNs. What will you learn Secure UNIX accounts. Secure UNIX file systems. Secure UNIX access through the network. Securing UNIX systems course details Who will benefit: Linux technical staff needing to secure their systems. Prerequisites: Linux system administration (LPIC-1) Duration 5 days Securing UNIX systems course contents Cryptography Certificates and Public Key Infrastructures X.509 certificates, lifecycle, fields and certificate extensions. Trust chains and PKI. openssl. Public and private keys. Certification authority. Manage server and client certificates. Revoke certificates and CAs. Encryption, signing and authentication SSL, TLS, protocol versions. Transport layer security threats, e.g. MITM. Apache HTTPD with mod_ssl for HTTPS service, including SNI and HSTS. HTTPD with mod_ssl to authenticate users using certificates. HTTPD with mod_ssl to provide OCSP stapling. Use OpenSSL for SSL/TLS client and server tests. Encrypted File Systems Block device and file system encryption. dm-crypt with LUKS to encrypt block devices. eCryptfs to encrypt file systems, including home directories and, PAM integration, plain dm-crypt and EncFS. DNS and cryptography DNSSEC and DANE. BIND as an authoritative name server serving DNSSEC secured zones. BIND as an recursive name server that performs DNSSEC validation, KSK, ZSK, Key Tag, Key generation, key storage, key management and key rollover, Maintenance and resigning of zones, Use DANE. TSIG. Host Security Host Hardening BIOS and boot loader (GRUB 2) security. Disable useless software and services, sysctl for security related kernel configuration, particularly ASLR, Exec-Shield and IP / ICMP configuration, Exec-Shield and IP / ICMP configuration, Limit resource usage. Work with chroot environments, Security advantages of virtualization. Host Intrusion Detection The Linux Audit system, chkrootkit, rkhunter, including updates, Linux Malware Detect, Automate host scans using cron, AIDE, including rule management, OpenSCAP. User Management and Authentication NSS and PAM, Enforce password policies. Lock accounts automatically after failed login attempts, SSSD, Configure NSS and PAM for use with SSSD, SSSD authentication against Active Directory, IPA, LDAP, Kerberos and local domains, Kerberos and local domains, Kerberos tickets. FreeIPA Installation and Samba Integration FreeIPA, architecture and components. Install and manage a FreeIPA server and domain, Active Directory replication and Kerberos cross-realm trusts, sudo, autofs, SSH and SELinux integration in FreeIPA. Access Control Discretionary Access Control File ownership and permissions, SUID, SGID. Access control lists, extended attributes and attribute classes. Mandatory Access Control TE, RBAC, MAC, DAC. SELinux, AppArmor and Smack. etwork File Systems NFSv4 security issues and improvements, NFSv4 server and clients, NFSv4 authentication mechanisms (LIPKEY, SPKM, Kerberos), NFSv4 pseudo file system, NFSv4 ACLs. CIFS clients, CIFS Unix Extensions, CIFS security modes (NTLM, Kerberos), mapping and handling of CIFS ACLs and SIDs in a Linux system. Network Security Network Hardening FreeRADIUS, nmap, scan methods. Wireshark, filters and statistics. Rogue router advertisements and DHCP messages. Network Intrusion Detection ntop, Cacti, bandwidth usage monitoring, Snort, rule management, OpenVAS, NASL. Packet Filtering Firewall architectures, DMZ, netfilter, iptables and ip6tables, standard modules, tests and targets. IPv4 and IPv6 packet filtering. Connection tracking, NAT. IP sets and netfilter rules, nftables and nft. ebtables. conntrackd Virtual Private Networks OpenVPN server and clients for both bridged and routed VPN networks. IPsec server and clients for routed VPN networks using IPsec-Tools / racoon. L2TP.

