- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1540 Courses
TCP/IP Protocol Suite Complete Training
By Study Plex
Recognised Accreditation This course is accredited by continuing professional development (CPD). CPD UK is globally recognised by employers, professional organisations, and academic institutions, thus a certificate from CPD Certification Service creates value towards your professional goal and achievement. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. What is CPD? Employers, professional organisations, and academic institutions all recognise CPD, therefore a credential from CPD Certification Service adds value to your professional goals and achievements. Benefits of CPD Improve your employment prospects Boost your job satisfaction Promotes career advancement Enhances your CV Provides you with a competitive edge in the job market Demonstrate your dedication Showcases your professional capabilities What is IPHM? The IPHM is an Accreditation Board that provides Training Providers with international and global accreditation. The Practitioners of Holistic Medicine (IPHM) accreditation is a guarantee of quality and skill. Benefits of IPHM It will help you establish a positive reputation in your chosen field You can join a network and community of successful therapists that are dedicated to providing excellent care to their client You can flaunt this accreditation in your CV It is a worldwide recognised accreditation What is Quality Licence Scheme? This course is endorsed by the Quality Licence Scheme for its high-quality, non-regulated provision and training programmes. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. Benefits of Quality License Scheme Certificate is valuable Provides a competitive edge in your career It will make your CV stand out Course Curriculum Start Here Introduction To The TCP/IP Course 00:04:00 The TCP/IP Suite Section The TCP/IP Suite 00:07:00 The TCP/IP And DoD Model 00:12:00 The Process Application Layer 00:13:00 The Host To Host Layer 00:10:00 The Internet Layer/Network Access 00:09:00 Summary Of Section 00:07:00 Introduction to IP Addressing Introduction To IP Addressing 00:01:00 IP Terminology 00:08:00 Hierarchical IP Addressing Scheme 00:05:00 Summary Of Section 00:01:00 Introduction to Network Addressing Introduction To Network Addressing 00:02:00 Network Address Ranges 00:06:00 Classes Of Addresses 00:10:00 Private IP Addresses (RFC 1918) 00:10:00 Summary Of Section 00:04:00 Summary of Course Summary Of Course 00:06:00 Assessment Assessment - TCP/IP Protocol Suite Complete Training 00:10:00 Obtain Your Certificate Order Your Certificate of Achievement 00:00:00 Get Your Insurance Now Get Your Insurance Now 00:00:00 Feedback Feedback 00:00:00

Register on the The Complete Ethical Hacking Course today and build the experience, skills and knowledge you need to enhance your professional development and work towards your dream job. Study this course through online learning and take the first steps towards a long-term career. The course consists of a number of easy to digest, in-depth modules, designed to provide you with a detailed, expert level of knowledge. Learn through a mixture of instructional video lessons and online study materials. Receive online tutor support as you study the course, to ensure you are supported every step of the way. Get an e-certificate as proof of your course completion. The The Complete Ethical Hacking Course is incredibly great value and allows you to study at your own pace. Access the course modules from any internet-enabled device, including computers, tablet, and smartphones. The course is designed to increase your employability and equip you with everything you need to be a success. Enrol on the now and start learning instantly! What You Get With The The Complete Ethical Hacking Course Receive a e-certificate upon successful completion of the course Get taught by experienced, professional instructors Study at a time and pace that suits your learning style Get instant feedback on assessments 24/7 help and advice via email or live chat Get full tutor support on weekdays (Monday to Friday) Course Design The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of Video lessons Online study materials Certification Upon successful completion of the course, you will be able to obtain your course completion e-certificate free of cost. Print copy by post is also available at an additional cost of £9.99 and PDF Certificate at £4.99. Who Is This Course For: The course is ideal for those who already work in this sector or are an aspiring professional. This course is designed to enhance your expertise and boost your CV. Learn key skills and gain a professional qualification to prove your newly-acquired knowledge. Requirements: The online training is open to all students and has no formal entry requirements. To study the The Complete Ethical Hacking Course, all your need is a passion for learning, a good understanding of English, numeracy, and IT skills. You must also be over the age of 16. Course Content Introduction to Ethical Hacking What is an Ethical Hacker 00:07:00 Terminology Crash Course pt. 1 00:09:00 Terminology Crash Course pt. 2 00:14:00 Terminology Crash Course pt. 3 00:08:00 Legal Considerations 00:11:00 Reconnaissance - Surveying the Attack Surface Surveying the Attack Surface 00:10:00 Recon Types 00:08:00 Passive Recon Part 1 00:07:00 Passive Recon Part 2 00:10:00 Active Recon 00:15:00 Recon Walkthrough Tools Summary 00:14:00 Maltego Demo 00:07:00 FOCA Demo 00:05:00 DEMO - Harvester 00:02:00 Scanning and Enumeration - Getting Down to Business Scanning & enumeration 00:08:00 Identifying Active Hosts pt. 1 00:10:00 Identifying Active Hosts pt. 2 00:13:00 Identifying Active Services 00:18:00 OS and Services Fingerprinting 00:15:00 Network Mapping 00:10:00 Final Thoughts 00:05:00 DEMO - Nmap Syntax pt. 1 00:14:00 DEMO - Nmap Syntax pt. 2 00:16:00 DEMO - Nmap Hosts Discovery 00:12:00 DEMO - Nmap Service Discovery 00:17:00 DEMO - Nmap Scripts 00:11:00 DEMO - Masscan 00:11:00 Network Presence Network Insecurity 00:04:00 Sniffing and Spoofing 00:13:00 Sniffing Tools 00:09:00 Spoofing, Crypto and Wifi 00:15:00 DEMO - tcpdump 00:11:00 DEMO - Wireshark 00:11:00 DEMO - Ettercap 00:13:00 DEMO - Burp Suite 00:15:00 DEMO - Scapy 00:10:00 Attacking Security Overview pt. 1: Windows Architecture 00:18:00 Security Overview pt. 2: Credentials Security 00:16:00 Security Overview pt. 3: Memory Corruption and Exploitation 00:16:00 Windows Hacking Basics 00:20:00 Local Access and Privilege Escalation 00:20:00 Dumping Hashes and Cracking Passwords 00:18:00 Linux Attacking Basics pt. 1 00:13:00 Linux Attacking Basics pt. 2 00:14:00 References 00:08:00 DEMO - Windows MSF Exploit pt. 1 00:13:00 DEMO - Windows MSF Exploit pt. 2 00:15:00 DEMO - Post Exploitation Activities 00:13:00 DEMO - Mimikatz 00:07:00 DEMO - Hashcat 00:08:00 DEMO - Konboot 00:13:00 DEMO - Post Exploitation Windows CMD 00:14:00 DEMO - Post Exploitation Windows Powershell 00:13:00 DEMO - Attacking Linux targets pt. 1aa 00:10:00 DEMO - Attacking Linux targets pt. 1 00:13:00 Web Hacking Introduction to Web Hacking 00:03:00 Web Security Architecture Overview pt. 1 00:17:00 Web Security Architecture Overview pt. 2 00:12:00 Attacking the Web Server pt. 1 00:10:00 Attacking the Web Server pt. 2 00:11:00 Attacking the Platform pt. 1 00:19:00 Attacking the Platform pt. 2 00:08:00 Attacking the Technology pt. 1 00:21:00 Attacking the Technology pt. 2 00:17:00 OWASP Top 10 pt. 1 00:09:00 OWASP Top 10 pt. 2 00:21:00 Attacking the Business Logic pt. 1 00:11:00 Attacking the Business Logic pt. 2 00:15:00 Tools and Methodology 00:20:00 References 00:05:00 DEMO - OWASP Mutillidae 00:09:00 SQLI 00:07:00 SQL Map Intro 00:08:00 SQL Map 00:25:00 DEMO - Burpsuite 00:37:00 DEMO - Burpsuite XSS Hunter 00:16:00 DEMO - mitmproxy 00:10:00 DEMO - Skipfish pt.1 00:05:00 DEMO - Skipfish pt.2 00:05:00 Social Engineering - Hacking Humans Social Engineering Basics 00:15:00 Social Engineering Methods 00:16:00 Tools and Techniques pt. 1 00:15:00 Tools and Techniques pt. 2 00:12:00 Tools and Techniques pt. 3 00:09:00 Physical Security Considerations 00:13:00 Final Thoughts99 00:11:00 DEMO - Credential harvesting 00:02:00 DEMO - Website cloning 00:06:00 DEMO - Automating an attack 00:03:00 DEMO - Anti-virus evasion pt. 1 00:08:00 DEMO - Anti-virus evasion pt. 2 00:12:00 Frequently Asked Questions Are there any prerequisites for taking the course? There are no specific prerequisites for this course, nor are there any formal entry requirements. All you need is an internet connection, a good understanding of English and a passion for learning for this course. Can I access the course at any time, or is there a set schedule? You have the flexibility to access the course at any time that suits your schedule. Our courses are self-paced, allowing you to study at your own pace and convenience. How long will I have access to the course? For this course, you will have access to the course materials for 1 year only. This means you can review the content as often as you like within the year, even after you've completed the course. However, if you buy Lifetime Access for the course, you will be able to access the course for a lifetime. Is there a certificate of completion provided after completing the course? Yes, upon successfully completing the course, you will receive a certificate of completion. This certificate can be a valuable addition to your professional portfolio and can be shared on your various social networks. Can I switch courses or get a refund if I'm not satisfied with the course? We want you to have a positive learning experience. If you're not satisfied with the course, you can request a course transfer or refund within 14 days of the initial purchase. How do I track my progress in the course? Our platform provides tracking tools and progress indicators for each course. You can monitor your progress, completed lessons, and assessments through your learner dashboard for the course. What if I have technical issues or difficulties with the course? If you encounter technical issues or content-related difficulties with the course, our support team is available to assist you. You can reach out to them for prompt resolution.

Register on the Cyber Security & Ethical Hacking today and build the experience, skills and knowledge you need to enhance your professional development and work towards your dream job. Study this course through online learning and take the first steps towards a long-term career. The course consists of a number of easy to digest, in-depth modules, designed to provide you with a detailed, expert level of knowledge. Learn through a mixture of instructional video lessons and online study materials. Receive online tutor support as you study the course, to ensure you are supported every step of the way. Get an e-certificate as proof of your course completion. The Cyber Security & Ethical Hacking is incredibly great value and allows you to study at your own pace. Access the course modules from any internet-enabled device, including computers, tablet, and smartphones. The course is designed to increase your employability and equip you with everything you need to be a success. Enrol on the now and start learning instantly! What You Get With The Cyber Security & Ethical Hacking Receive a e-certificate upon successful completion of the course Get taught by experienced, professional instructors Study at a time and pace that suits your learning style Get instant feedback on assessments 24/7 help and advice via email or live chat Get full tutor support on weekdays (Monday to Friday) Course Design The course is delivered through our online learning platform, accessible through any internet-connected device. There are no formal deadlines or teaching schedules, meaning you are free to study the course at your own pace. You are taught through a combination of Video lessons Online study materials Certification Upon successful completion of the course, you will be able to obtain your course completion e-certificate free of cost. Print copy by post is also available at an additional cost of £9.99 and PDF Certificate at £4.99. Who Is This Course For: The course is ideal for those who already work in this sector or are an aspiring professional. This course is designed to enhance your expertise and boost your CV. Learn key skills and gain a professional qualification to prove your newly-acquired knowledge. Requirements: The online training is open to all students and has no formal entry requirements. To study the Cyber Security & Ethical Hacking, all your need is a passion for learning, a good understanding of English, numeracy, and IT skills. You must also be over the age of 16. Course Content Introduction to Ethical Hacking Hacking Terms 00:07:00 VA vs PT and Rule of Engagement 00:09:00 Methodologies 00:07:00 Type of Pen Testing 00:06:00 Phases of Penetration Test 00:04:00 10 Steps to Follow 00:04:00 Setting up a Penetration Testing Lab What is Linux OS - Benefits 00:04:00 What is Kali Linux 00:03:00 Virtual Box Installation 00:06:00 Kali Linux Installation in VB 00:12:00 Install Metasploitable on Virtual Box 00:09:00 Install DVWA in Kali 00:18:00 Install TOR 00:09:00 Executing Basic Commands in Kali 00:12:00 Executing Advance Commands in Kali 00:14:00 Information Gathering What is Information Gathering 00:04:00 Maltego Part 1 00:07:00 Maltego Part 2 00:06:00 HTTrack 00:05:00 The Harvester 00:02:00 NSLookup 00:03:00 RedHawk 00:05:00 SHODAN 00:09:00 OSNIT Framework 00:05:00 Scanning and Enumeration What is Scanning 00:07:00 What is Nmap 00:05:00 Zenmap GUI 00:17:00 What is Enumeration 00:03:00 Types of Enumeration 00:03:00 Enumeration Using Hyena - 1 00:07:00 Enumeration Using Hyena - 2 00:06:00 VAPT What is Vulnerability Assessment 00:04:00 Phases of Vulnerability Assessment 00:08:00 Vulnerability Scoring Systems 00:09:00 Introduction to Nessus 00:05:00 Create and Configure Nessus Network Policy 00:08:00 Nessus Launch Scan and Analyse Result 00:08:00 Firewalls What is IDS 00:11:00 What Are Firewalls 00:10:00 What is DMZ 00:06:00 IDS Evasion Techniques 00:08:00 Firewall Evasion Techniques 00:09:00 Firewall Pentesting 00:02:00 WAPT Introduction to Web Servers 00:05:00 Types of Web Server Attacks 00:05:00 Web Server Penetration Testing 00:04:00 Countermeasures of Web Servers? 00:05:00 OWASP Top 10 Attacks Part 1 00:05:00 OWASP Top 10 Attacks Part 2 00:07:00 Website Foot Printing Part 1 00:05:00 Website Foot Printing Part 2 00:03:00 Command Execution Low 00:06:00 Command Execution Medium 00:07:00 Configuring Burp Suite 00:16:00 File Upload Low 00:10:00 File Upload Medium 00:07:00 File Upload High 00:08:00 SQL Injection 00:04:00 SQL Injection II 00:05:00 Manual SQL 00:17:00 Automating SQL 00:09:00 Countermeasures of SQL Injection 00:03:00 What Is XSS 00:03:00 Types of XSS 00:06:00 XSS Low 00:11:00 XSS Medium 00:05:00 XSS High 00:11:00 Countermeasures of XSS 00:04:00 What is CSRF 00:06:00 CSRF Practical 00:07:00 What is a Brute Force Attack? 00:05:00 Brute Force Political 00:18:00 Web Application Penetration Testing? 00:09:00 Web Application Countermeasures 00:06:00 Denial of Service What is Denial of Service (DOS)? 00:03:00 Types of DOS attack? 00:05:00 What is a BOTNET? 00:03:00 Malware Threats Introduction to Malware 00:09:00 Trojan 00:08:00 Types of Trojans 00:08:00 Viruses and Worms 00:07:00 Types of Viruses 00:10:00 Countermeasures 00:07:00 Social Engineering Introduction to Social Engineering 00:05:00 Social Engineering 00:06:00 Installing BeEF Framework 00:09:00 Getting User Credentials Using BeEF Framework 00:11:00 Cryptography Introduction to Cryptography 00:05:00 Symmetric Encryption 00:03:00 DES and AES 00:06:00 Asymmetric Encryption 00:03:00 RSA and Diffie 00:07:00 Hashing 00:07:00 Public Key Infrastructure (PKI) and Certificate Authority (CA) 00:10:00 Digital Signatures 00:09:00 Transport Layer Security (TLS) 00:04:00 Calculating One Way Hashes Using HashCal 00:04:00 Basic Data Encryption Advance and Decryption Package 00:05:00 Report Writing Introduction to Report Writing 00:08:00 Component of a Report 00:14:00 Bonus Section Why we need to fix vulnerabilities 00:05:00 Hacker Sponsored Security 00:03:00 Key Terms in Bug Bounty Program 00:05:00 Bug Bounty Definition 00:03:00 Public or Private Bug Bounty Program 00:04:00 What is HackerOne 00:05:00 Why Organizations will hire you 00:08:00

Explore the world of cybersecurity beyond firewalls and antivirus software in this micro-learning course. Discover the critical role employees play in safeguarding your organization's digital assets and learn about the motivations behind cybercrimes. Gain insights into the dynamic landscape of digital threats and the alarming growth of cybercrime. This course will equip you with essential knowledge to protect yourself and your company from security breaches, emphasizing the importance of vigilance and awareness. Learning Objectives Construct a dedicated and productive remote workspace, considering factors such as comfort, organization, and freedom from distractions, to enhance focus and work-life balance.;Develop effective time management skills and routines, including setting clear boundaries, prioritizing tasks, and scheduling breaks, to optimize productivity and prevent burnout in a hybrid work setting.;Enhance your communication and collaboration skills with the steps to accurately engage in virtual meetings, share ideas, and foster effective teamwork, ensuring successful interactions in the hybrid workspace.

It is estimated that 81% of security breaches take place because of weak or stolen passwords. This type of breach is therefore preventable, but only if employees understand how easy it can take place and what their role is in preventing them. This microlearning video covers the various ways that cyber criminals easily penetrate accounts via personal passwords and how to prevent them from doing so. Learning Objectives Assess your current password habits and identify actionable steps you can implement immediately to strengthen your online security and protect your organization against cybercrime.;Evaluate various methods employed by cybercriminals to obtain passwords in order to understand the vulnerabilities and risks associated with each approach.;Apply effective password security practices to enhance personal and organizational cybersecurity resilience.

In a world where so much of our commerce is focused online, it can be easy to forget the importance of physical security. However, physical breaches still take place and can lead to cyber-attacks, huge financial losses, damaged company reputation, and more. Cybercriminals who target businesses often look for the weak links in an organization's buildings, staff, and security protocol and are only successful if they can find them. This video outlines six different physical security protocols that you and your employees can take to ensure none of you are the weak link that may allow an attack. Learning Objectives Analyze the risks and consequences of physical security breaches, emphasizing the importance of maintaining a secure workplace environment.;Evaluate and implement best practices for physical security to reduce vulnerabilities and enhance workplace security.;Apply proactive measures to protect personal and organizational assets ensuring a stronger defense against physical security threats.

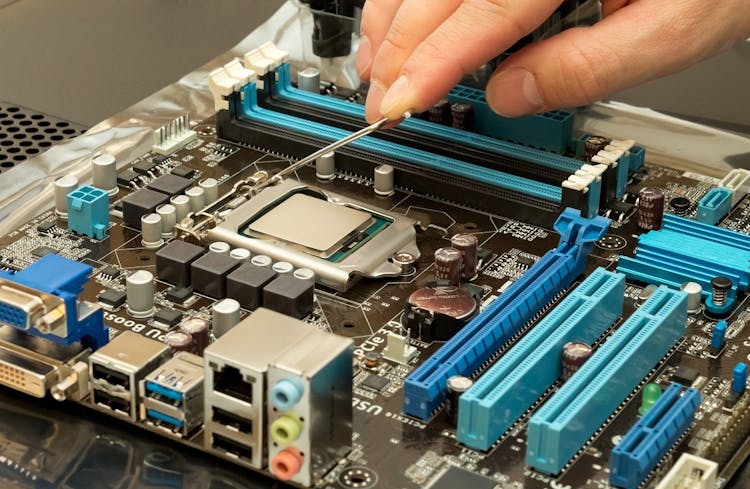
Overview Having a foundational understanding of IT components is essential. Did you know that by 2023, an estimated 2.5 million new IT positions will be available globally? The CompTIA A+ (220-1001) course offers a comprehensive dive into the world of computer technology. Designed to shape the professionals of tomorrow, this course meticulously covers the gamut of fundamental IT knowledge. Ranging from RAM technology to the vast world of cloud computing, the curriculum is structured to foster a comprehensive understanding. With modules such as 'Inside the PC' and 'Understanding Virtualization', learners will be adept at navigating the complex terrains of the modern IT environment. Ready to steer your career into the future of IT? Enrol now and become a part of the technological revolution! How will I get my certificate? You may have to take a quiz or a written test online during or after the course. After successfully completing the course, you will be eligible for the certificate. Who is This course for? There is no experience or previous qualifications required for enrolment on this CompTIA A+ (220-1001). It is available to all students, of all academic backgrounds. Requirements Our CompTIA A+ (220-1001) is fully compatible with PC's, Mac's, Laptop, Tablet and Smartphone devices. This course has been designed to be fully compatible with tablets and smartphones so you can access your course on Wi-Fi, 3G or 4G. There is no time limit for completing this course, it can be studied in your own time at your own pace. Career Path Learning this new skill will help you to advance in your career. It will diversify your job options and help you develop new techniques to keep up with the fast-changing world. This skillset will help you to- Open doors of opportunities Increase your adaptability Keep you relevant Boost confidence And much more! Course Curriculum 24 sections • 132 lectures • 17:30:00 total length •CompTIA A+ 2019 Core 1 (220-1001) Course Introduction: 00:02:00 •What is the CompTIA A+?: 00:02:00 •Why Get A+ Certified?: 00:03:00 •What is on the CompTIA A+ Core 1 (220-1001) Exam?: 00:09:00 •How to Pass the A+ Exam: 00:04:00 •How to Use This Video Course: 00:03:00 •Tools of the Trade: 00:06:00 •Troubleshooting Theory: 00:10:00 •Primary PC Connections: 00:05:00 •External Connections: 00:11:00 •Inside the PC: 00:08:00 •What is a Computer?: 00:07:00 •What is a CPU?: 00:15:00 •CPU Speeds and Cores: 00:12:00 •Caching: 00:07:00 •CPU Sockets: 00:12:00 •Installing a CPU: 00:11:00 •Liquid Cooling: 00:04:00 •RAM Technology: 00:11:00 •RAM Capacity: 00:08:00 •RAM Features: 00:07:00 •Installing RAM: 00:07:00 •What is the BIOS?: 00:06:00 •POST: 00:09:00 •System Setup: 00:09:00 •Troubleshooting Firmware: 00:12:00 •Form Factors: 00:06:00 •Chipsets: 00:05:00 •Touring the Motherboard: 00:14:00 •Touring the Case: 00:07:00 •Installing a Motherboard: 00:09:00 •The Power Supply: 00:09:00 •Mounting a Power Supply: 00:05:00 •Choosing a Power Supply: 00:08:00 •Cooling Your PC: 00:11:00 •Troubleshooting Power Supplies: 00:09:00 •Troubleshooting Core Components: 00:14:00 •Introduction to Mass Storage: 00:13:00 •Magnetic Disk Drives: 00:08:00 •Solid State Drives: 00:08:00 •SCSI: 00:03:00 •Boot Order: 00:07:00 •New Installation - First Drive: 00:05:00 •RAID: 00:11:00 •Hardware RAID: 00:07:00 •Mass Storage Troubleshooting: 00:08:00 •Optical Media: 00:10:00 •USB Standards: 00:10:00 •Understanding USB: 00:11:00 •Configuring USB: 00:07:00 •Thunder and Lightning: 00:06:00 •Keyboards and Mice: 00:08:00 •Sight and Sound: 00:07:00 •Readers and Scanners: 00:08:00 •Using Expansion Cards: 00:08:00 •The Right PC for the Job: 00:13:00 •Monitor Technologies: 00:08:00 •LCD Breakdown: 00:04:00 •Graphics Cards and Connections: 00:13:00 •Installing a Graphics Card: 00:07:00 •Projectors: 00:05:00 •Troubleshooting Monitors: 00:06:00 •Introduction to Networking: 00:08:00 •Hubs vs. Switches: 00:05:00 •Hexadecimal: 00:07:00 •WANs and Routers: 00:09:00 •Cables and Connectors: 00:11:00 •Crimping Cables: 00:10:00 •Structured Cabling: 00:11:00 •Introduction to TCP/IP: 00:14:00 •Network IDs and Subnet Masks: 00:05:00 •Special IP Addresses: 00:09:00 •NAT: 00:07:00 •Dynamic IP Addressing: 00:10:00 •IPv6: 00:07:00 •Port Numbers: 00:12:00 •TCP, UDP, and ICMP: 00:06:00 •Understanding DNS: 00:09:00 •Working with DNS: 00:07:00 •Windows Naming: 00:08:00 •Routers: 00:12:00 •Basic Router Configuration: 00:12:00 •Advanced Router Configuration: 00:06:00 •VLANs: 00:07:00 •Network Troubleshooting: 00:05:00 •Wireless Network Hardware: 00:11:00 •Wi-Fi Standards: 00:10:00 •Basic WAP Setup: 00:11:00 •Connecting to a Wi-Fi Network: 00:09:00 •It's a Huge Mesh: 00:04:00 •Beyond Wi-Fi: 00:07:00 •Troubleshooting Wireless Connections: 00:07:00 •Beyond the LAN: 00:03:00 •Internet Tiers: 00:06:00 •Dial-up Connections: 00:08:00 •Broadband Connections: 00:10:00 •Firewalls and Servers: 00:06:00 •FTP: 00:07:00 •E-Mail: 00:08:00 •Proxy Servers: 00:06:00 •Virtual Private Networks (VPNs): 00:08:00 •Internet of Things (IoT): 00:04:00 •Understanding Virtualization: 00:10:00 •Your First Virtual Machine: 00:11:00 •Advanced Virtualization Setup: 00:10:00 •Cloud Computing: 00:08:00 •Cloud Ownership: 00:03:00 •Cloud-Based Applications: 00:06:00 •Laptop Features: 00:08:00 •Laptop Hardware Troubleshooting - The Tools: 00:05:00 •Laptop Hardware - Core Hardware: 00:04:00 •Laptop Hardware - CPU and Motherboard: 00:07:00 •Touring Your Laptop Display: 00:04:00 •What is a Mobile Device?: 00:09:00 •Mobile Connections: 00:10:00 •Touring Android: 00:10:00 •Touring iOS: 00:08:00 •Virtual Reality: 00:03:00 •Maintaining Mobile Devices: 00:11:00 •Mobile Devices and E-mail: 00:10:00 •Mobile Synchronization: 00:08:00 •Laser Printers: 00:13:00 •Inkjet Printers: 00:08:00 •Impact Printers: 00:04:00 •Thermal Printers: 00:04:00 •Installing a Local Printer: 00:14:00 •Sharing Printers: 00:08:00 •Installing Wireless and Cloud Printers: 00:10:00 •Troubleshooting Printers: 00:10:00 •3D Printing: 00:07:00 •Dealing with Threats: 00:07:00 •Assignment - CompTIA A+ (220-1001): 00:00:00
Overview This comprehensive course on CompTIA IT Fundamentals ITF+ (FCO-U61) will deepen your understanding on this topic. After successful completion of this course you can acquire the required skills in this sector. This CompTIA IT Fundamentals ITF+ (FCO-U61) comes with accredited certification from CPD, which will enhance your CV and make you worthy in the job market. So enrol in this course today to fast track your career ladder. How will I get my certificate? You may have to take a quiz or a written test online during or after the course. After successfully completing the course, you will be eligible for the certificate. Who is This course for? There is no experience or previous qualifications required for enrolment on this CompTIA IT Fundamentals ITF+ (FCO-U61). It is available to all students, of all academic backgrounds. Requirements Our CompTIA IT Fundamentals ITF+ (FCO-U61) is fully compatible with PC's, Mac's, Laptop, Tablet and Smartphone devices. This course has been designed to be fully compatible with tablets and smartphones so you can access your course on Wi-Fi, 3G or 4G. There is no time limit for completing this course, it can be studied in your own time at your own pace. Career Path Learning this new skill will help you to advance in your career. It will diversify your job options and help you develop new techniques to keep up with the fast-changing world. This skillset will help you to- Open doors of opportunities Increase your adaptability Keep you relevant Boost confidence And much more! Course Curriculum 15 sections • 64 lectures • 04:55:00 total length •Introduction to IT Fundamentals: 00:03:00 •The Case for Computer Literacy: 00:03:00 •Features Common to Every Computing Device: 00:02:00 •Common General-Purpose Computing Devices: 00:02:00 •Networks of Computing Devices: 00:04:00 •Remotely-Accessed Computer Systems: 00:04:00 •Specialized Computer Systems: 00:02:00 •Specialty I/O Devices: 00:01:00 •CPUs: 00:03:00 •Passive and Active Cooling: 00:03:00 •RAM and Active Memory: 00:05:00 •Motherboards: 00:03:00 •Power Supplies: 00:03:00 •AMA - Ask Me Anything about System Hardware: 00:07:00 •Ports and Connectors: 00:03:00 •General Use I/O Devices: 00:02:00 •AMA - Ask Me Anything about I/O, Ports and Peripherals: 00:07:00 •Basics of Binary: 00:04:00 •Storage Technologies: 00:04:00 •Mass Storage Variation: 00:03:00 •AMA - Ask Me Anything about Data Storage and Sharing: 00:07:00 •Operating System Functions: 00:04:00 •Operating System Interfaces: 00:05:00 •AMA - Ask Me Anything about Understanding OS's: 00:05:00 •Preparing the Work Area: 00:02:00 •Setting up a Desktop PC: 00:01:00 •Completing PC Setup: 00:04:00 •AMA - Ask Me Anything about Setting up and Configuring a PC: 00:09:00 •Personalizing a Tablet: 00:08:00 •AMA - Ask Me Anything about Mobile Devices Part 1: 00:07:00 •AMA - Ask Me Anything about Mobile Devices Part 2: 00:07:00 •File Management Tools: 00:02:00 •File Manipulation: 00:06:00 •Backups: 00:03:00 •AMA - Ask Me Anything about Managing Files: 00:08:00 •Walking Survey of Applications: 00:03:00 •Managing Applications: 00:03:00 •Applications and Extensions: 00:04:00 •AMA - Ask Me Anything about Working with Applications: 00:07:00 •Wi-Fi Setup: 00:06:00 •Going High Speed: 00:03:00 •Setting Up and Sharing Printers: 00:05:00 •AMA - Ask Me Anything about Networks and Internet Connectivity Part 1: 00:07:00 •AMA - Ask Me Anything about Networks and Internet Connectivity Part 2: 00:05:00 •Physical Security: 00:05:00 •Dealing with Malware: 00:03:00 •Password Management: 00:03:00 •Clickworthy: 00:03:00 •Perils of Public Internet: 00:02:00 •AMA - Ask Me Anything about IT Threat Mitigation Part 1: 00:07:00 •AMA - Ask Me Anything about IT Threat Mitigation Part 2: 00:08:00 •Power Management: 00:02:00 •Cleaning and Maintaining Computers: 00:02:00 •Trash it or Stash it?: 00:02:00 •AMA - Ask Me Anything about Computer Maintenance and Management: 00:11:00 •Troubleshooting 101: 00:03:00 •AMA - Ask Me Anything about Troubleshooting Computers Part 1: 00:10:00 •AMA - Ask Me Anything about Troubleshooting Computers Part 2: 00:11:00 •Introduction to Databases: 00:06:00 •Database Details: 00:06:00 •AMA - Ask Me Anything about Databases: 00:06:00 •Introduction to Programming: 00:04:00 •Programming with a PBJ Sandwich: 00:08:00 •AMA - Ask Me Anything about Programming: 00:04:00

Overview This comprehensive course on CompTIA A+ (220-1002) will deepen your understanding on this topic. After successful completion of this course you can acquire the required skills in this sector. This CompTIA A+ (220-1002) comes with accredited certification from CPD, which will enhance your CV and make you worthy in the job market. So enrol in this course today to fast track your career ladder. How will I get my certificate? You may have to take a quiz or a written test online during or after the course. After successfully completing the course, you will be eligible for the certificate. Who is This course for? There is no experience or previous qualifications required for enrolment on this CompTIA A+ (220-1002). It is available to all students, of all academic backgrounds. Requirements Our CompTIA A+ (220-1002) is fully compatible with PC's, Mac's, Laptop, Tablet and Smartphone devices. This course has been designed to be fully compatible with tablets and smartphones so you can access your course on Wi-Fi, 3G or 4G. There is no time limit for completing this course, it can be studied in your own time at your own pace. Career Path Course Curriculum 22 sections • 106 lectures • 14:51:00 total length •CompTIA A+ 2019 Core 2 (220-1002) Course Introduction: 00:02:00 •What is the CompTIA A+: 00:02:00 •Why Get A+ Certified?: 00:03:00 •What is on the CompTIA A+ Core 2 (220-1002) Exam?: 00:04:00 •How to Pass the CompTIA A+ Exam: 00:04:00 •How to use this Video Course: 00:03:00 •Professional Communication Part 1: 00:06:00 •Professional Communication Part 2: 00:07:00 •Physical Safety: 00:07:00 •What is an Operating System?: 00:09:00 •Users and Super Users: 00:05:00 •Why Windows?: 00:08:00 •Windows Editions and Versions: 00:12:00 •Touring the macOS: 00:06:00 •Touring Linux: 00:08:00 •32-Bit vs. 64-Bit Processing: 00:12:00 •Virtual Memory: 00:06:00 •Power Protection: 00:10:00 •Understanding Partitioning: 00:04:00 •MBR Partitioning: 00:12:00 •GPT Partitioning: 00:09:00 •Understanding File Systems: 00:12:00 •Popular File Systems: 00:07:00 •Formatting in Action: 00:11:00 •Dynamic Disks: 00:09:00 •Software RAID in Storage Spaces: 00:10:00 •Encrypting Mass Storage: 00:09:00 •Boot from Everything: 00:12:00 •Installing Windows: 00:12:00 •Post-Installation Tasks: 00:12:00 •Windows Installation options: 00:07:00 •What is the Registry?: 00:11:00 •Processes: 00:07:00 •Services: 00:04:00 •Your Windows Toolset: 00:08:00 •Windows 7 Task Manager: 00:09:00 •Windows 10 Task Manager: 00:06:00 •Information and Configuration Tools: 00:11:00 •Performance Monitor: 00:12:00 •Event Viewer: 00:07:00 •Tools for Programmers: 00:08:00 •Introduction to Users and Groups: 00:06:00 •Managing Users and Groups: 00:12:00 •NTFS Permissions: 00:08:00 •Linux and macOS Permissions: 00:05:00 •File Explorer: 00:14:00 •Sharing Resources: 00:11:00 •Security Policies: 00:08:00 •Patch Management: 00:11:00 •Working with Disks: 00:06:00 •Working with Applications: 00:07:00 •System Restore: 00:05:00 •Backing up Your Files: 00:07:00 •Task Scheduler: 00:07:00 •Understanding the CLI: 00:11:00 •Navigating the CLI: 00:14:00 •Working with Folders: 00:07:00 •Working with Files: 00:11:00 •Working with Drives: 00:13:00 •Super Copy Commands: 00:09:00 •Advanced Windows Command Line: 00:08:00 •Advanced Linux Commands: 00:13:00 •Command-Line Permissions: 00:08:00 •Introduction to Scripting: 00:10:00 •Interpreted Languages: 00:12:00 •Windows Recovery Environment: 00:05:00 •Advanced Windows Startup Options: 00:07:00 •Troubleshooting Boot Problems: 00:10:00 •Troubleshooting at the GUI: 00:11:00 •Troubleshooting Applications: 00:07:00 •Kernel Panic: 00:05:00 •Resolutions and Aspect Ratios: 00:06:00 •Multiple Monitors: 00:05:00 •Network Card Troubleshooting: 00:09:00 •Working with Connections: 00:09:00 •Working with Workgroups: 00:08:00 •Working with Active Directory: 00:14:00 •Windows Sharing with Mac and LInux: 00:07:00 •Net Command: 00:04:00 •Firewall Configuration: 00:11:00 •Windows Firewall: 00:08:00 •Port Forwarding: 00:07:00 •Wireless Encryption: 00:11:00 •Enterprise Wireless: 00:16:00 •Telnet and SSH: 00:07:00 •Remote Desktop Connections: 00:06:00 •The World Wide Web: 00:09:00 •Troubleshooting Internet Connections: 00:07:00 •Power Management: 00:11:00 •Mobile Device Security: 00:08:00 •Mobile Security Troubleshooting: 00:06:00 •Mobile Device Troubleshooting: 00:10:00 •Threats: 00:10:00 •Physical Security: 00:08:00 •Passwords and Authentication: 00:14:00 •Malware: 00:14:00 •Anti-Malware: 00:11:00 •Social Engineering: 00:06:00 •Licensing: 00:10:00 •Incident Response: 00:05:00 •Environmental Controls: 00:06:00 •Documents You Need to Know: 00:09:00 •Data You Need to Know: 00:04:00 •Change Management: 00:06:00 •The Zen of Backup: 00:11:00 •Recycling and Data Destruction: 00:07:00
Level 7 Diploma in Cyber Security Law Online Course
By Kingston Open College
QLS Endorsed + CPD QS Accredited - Dual Certification | Instant Access | 24/7 Tutor Support | All-Inclusive Cost

Search By Location
- Network Security Courses in London
- Network Security Courses in Birmingham
- Network Security Courses in Glasgow
- Network Security Courses in Liverpool
- Network Security Courses in Bristol
- Network Security Courses in Manchester
- Network Security Courses in Sheffield
- Network Security Courses in Leeds
- Network Security Courses in Edinburgh
- Network Security Courses in Leicester
- Network Security Courses in Coventry
- Network Security Courses in Bradford
- Network Security Courses in Cardiff
- Network Security Courses in Belfast
- Network Security Courses in Nottingham