- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
57804 Courses
Certified Kubernetes Security Specialist (CKS)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Security Professionals working with Kubernetes Clusters Container Orchestration Engineers DevOps Professionals Overview In this course, students will learn and practice essential Kubernetes concepts and tasks in the following sections: Cloud Security Fundamentals Cluster Hardening System Hardening Minimize Microservice Vulnerabilities Supply Chain Security Disaster Recovery Secure Back-up and Restore This class prepares students for the Certified Kubernetes Security Specialist (CKS) exam. Kubernetes is a Cloud Orchestration Platform providing reliability, replication, and stabilitywhile maximizing resource utilization for applications and services. By the conclusion of this hands-on, vendor agnostic training you will be equipped with a thorough understanding ofcloud security fundamentals, along with the knowledge, skills and abilities to secure a Kubernetes cluster, detect threats, and properly resolve a security catastrophe. This courseincludes hands-on instruction which develops skills and knowledge for securing container-based applications and Kubernetes platforms, during build, deployment, and runtime. We prioritizecovering all objectives and concepts necessary for passing the Certified Kubernetes Security Specialist (CKS) exam. You will be provided the components necessary to assemble your ownhigh availability Kubernetes environment and harden it for your security needs. Learning Your Environment Underlying Infrastructure Using Vim Tmux Cloud Security Primer Basic Principles Threat Analysis Approach CIS Benchmarks Securing your Kubernetes Cluster Kubernetes Architecture Pods and the Control Plane Kubernetes Security Concepts Install Kubernetes using kubeadm Configure Network Plugin Requirements Kubeadm Basic Cluster Installing Kubeadm Join Node to Cluster Kubeadm Token Manage Kubeadm Tokens Kubeadm Cluster Upgrade Securing the kube-apiserver Configuring the kube-apiserver Enable Audit Logging Falco Deploy Falco to Monitor System Calls Enable Pod Security Policies Encrypt Data at Rest Encryption Configuration Benchmark Cluster with Kube-Bench Kube-Bench Securing ETCD ETCD Isolation ETCD Disaster Recovery ETCD Snapshot and Restore Purge Kubernetes Purge Kubeadm 3Purge Kubeadm Image Scanning Container Essentials Secure Containers Creating a Docker Image Scanning with Trivy Trivy Snyk Security Manually Installing Kubernetes Kubernetes the Alta3 Way Deploy Kubernetes the Alta3 Way Validate your Kubernetes Installation Sonobuoy K8s Validation Test Kubectl (Optional) Kubectl get and sorting kubectl get kubectl describe Labels (Optional) Labels Labels and Selectors Annotations Insert an Annotation Securing your Application Scan a Running Container Tracee Security Contexts for Pods Understanding Security Contexts AppArmor Profiles AppArmor Isolate Container Kernels gVisor Pod Security Pod Security Policies Deploy a PSP Pod Security Standards Enable PSS Open Policy Agent (OPA) Admission Controller Create a LimitRange Open Policy Agent Policy as Code Deploy Gatekeeper User Administration Contexts Contexts Authentication and Authorization Role Based Access Control Role Based Access Control RBAC Distributing Access Service Accounts Limit Pod Service Accounts Securing Secrets Secrets Create and Consume Secrets Hashicorp Vault Deploy Vault Securing the Network Networking Plugins NetworkPolicy Deploy a NetworkPolicy mTLS Linkerd mTLS with istio istio Threat Detection Active Threat Analysis Host Intrusion Detection Deploy OSSEC Network Intrusion Detection Deploy Suricata Physical Intrusion Detection Disaster Recovery Harsh Reality of Security Deploy a Response Plan Kasten K10 Backups Deploy K10

Data Engineering on Google Cloud
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This class is intended for experienced developers who are responsible for managing big data transformations including: Extracting, loading, transforming, cleaning, and validating data. Designing pipelines and architectures for data processing. Creating and maintaining machine learning and statistical models. Querying datasets, visualizing query results and creating reports Overview Design and build data processing systems on Google Cloud Platform. Leverage unstructured data using Spark and ML APIs on Cloud Dataproc. Process batch and streaming data by implementing autoscaling data pipelines on Cloud Dataflow. Derive business insights from extremely large datasets using Google BigQuery. Train, evaluate and predict using machine learning models using TensorFlow and Cloud ML. Enable instant insights from streaming data Get hands-on experience with designing and building data processing systems on Google Cloud. This course uses lectures, demos, and hand-on labs to show you how to design data processing systems, build end-to-end data pipelines, analyze data, and implement machine learning. This course covers structured, unstructured, and streaming data. Introduction to Data Engineering Explore the role of a data engineer. Analyze data engineering challenges. Intro to BigQuery. Data Lakes and Data Warehouses. Demo: Federated Queries with BigQuery. Transactional Databases vs Data Warehouses. Website Demo: Finding PII in your dataset with DLP API. Partner effectively with other data teams. Manage data access and governance. Build production-ready pipelines. Review GCP customer case study. Lab: Analyzing Data with BigQuery. Building a Data Lake Introduction to Data Lakes. Data Storage and ETL options on GCP. Building a Data Lake using Cloud Storage. Optional Demo: Optimizing cost with Google Cloud Storage classes and Cloud Functions. Securing Cloud Storage. Storing All Sorts of Data Types. Video Demo: Running federated queries on Parquet and ORC files in BigQuery. Cloud SQL as a relational Data Lake. Lab: Loading Taxi Data into Cloud SQL. Building a Data Warehouse The modern data warehouse. Intro to BigQuery. Demo: Query TB+ of data in seconds. Getting Started. Loading Data. Video Demo: Querying Cloud SQL from BigQuery. Lab: Loading Data into BigQuery. Exploring Schemas. Demo: Exploring BigQuery Public Datasets with SQL using INFORMATION_SCHEMA. Schema Design. Nested and Repeated Fields. Demo: Nested and repeated fields in BigQuery. Lab: Working with JSON and Array data in BigQuery. Optimizing with Partitioning and Clustering. Demo: Partitioned and Clustered Tables in BigQuery. Preview: Transforming Batch and Streaming Data. Introduction to Building Batch Data Pipelines EL, ELT, ETL. Quality considerations. How to carry out operations in BigQuery. Demo: ELT to improve data quality in BigQuery. Shortcomings. ETL to solve data quality issues. Executing Spark on Cloud Dataproc The Hadoop ecosystem. Running Hadoop on Cloud Dataproc. GCS instead of HDFS. Optimizing Dataproc. Lab: Running Apache Spark jobs on Cloud Dataproc. Serverless Data Processing with Cloud Dataflow Cloud Dataflow. Why customers value Dataflow. Dataflow Pipelines. Lab: A Simple Dataflow Pipeline (Python/Java). Lab: MapReduce in Dataflow (Python/Java). Lab: Side Inputs (Python/Java). Dataflow Templates. Dataflow SQL. Manage Data Pipelines with Cloud Data Fusion and Cloud Composer Building Batch Data Pipelines visually with Cloud Data Fusion. Components. UI Overview. Building a Pipeline. Exploring Data using Wrangler. Lab: Building and executing a pipeline graph in Cloud Data Fusion. Orchestrating work between GCP services with Cloud Composer. Apache Airflow Environment. DAGs and Operators. Workflow Scheduling. Optional Long Demo: Event-triggered Loading of data with Cloud Composer, Cloud Functions, Cloud Storage, and BigQuery. Monitoring and Logging. Lab: An Introduction to Cloud Composer. Introduction to Processing Streaming Data Processing Streaming Data. Serverless Messaging with Cloud Pub/Sub Cloud Pub/Sub. Lab: Publish Streaming Data into Pub/Sub. Cloud Dataflow Streaming Features Cloud Dataflow Streaming Features. Lab: Streaming Data Pipelines. High-Throughput BigQuery and Bigtable Streaming Features BigQuery Streaming Features. Lab: Streaming Analytics and Dashboards. Cloud Bigtable. Lab: Streaming Data Pipelines into Bigtable. Advanced BigQuery Functionality and Performance Analytic Window Functions. Using With Clauses. GIS Functions. Demo: Mapping Fastest Growing Zip Codes with BigQuery GeoViz. Performance Considerations. Lab: Optimizing your BigQuery Queries for Performance. Optional Lab: Creating Date-Partitioned Tables in BigQuery. Introduction to Analytics and AI What is AI?. From Ad-hoc Data Analysis to Data Driven Decisions. Options for ML models on GCP. Prebuilt ML model APIs for Unstructured Data Unstructured Data is Hard. ML APIs for Enriching Data. Lab: Using the Natural Language API to Classify Unstructured Text. Big Data Analytics with Cloud AI Platform Notebooks What's a Notebook. BigQuery Magic and Ties to Pandas. Lab: BigQuery in Jupyter Labs on AI Platform. Production ML Pipelines with Kubeflow Ways to do ML on GCP. Kubeflow. AI Hub. Lab: Running AI models on Kubeflow. Custom Model building with SQL in BigQuery ML BigQuery ML for Quick Model Building. Demo: Train a model with BigQuery ML to predict NYC taxi fares. Supported Models. Lab Option 1: Predict Bike Trip Duration with a Regression Model in BQML. Lab Option 2: Movie Recommendations in BigQuery ML. Custom Model building with Cloud AutoML Why Auto ML? Auto ML Vision. Auto ML NLP. Auto ML Tables.

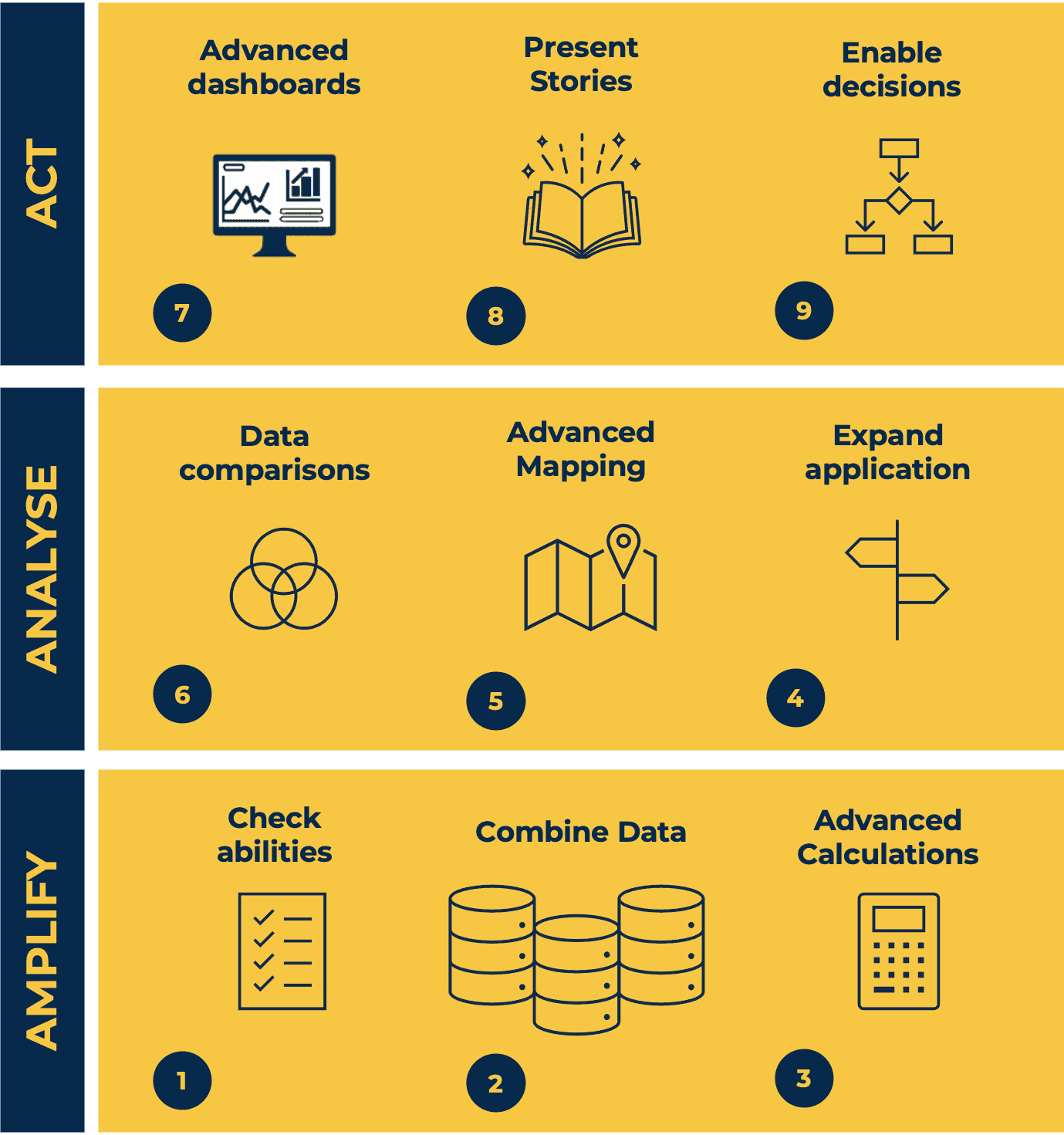
Tableau Desktop Training - Analyst
By Tableau Training Uk
This Tableau Desktop Training intermediate course is designed for the professional who has a solid foundation with Tableau and is looking to take it to the next level. For Private options, online or in-person, please send us details of your requirements: This Tableau Desktop training intermediate course is designed for the professional who has a solid foundation with Tableau and is looking to take it to the next level. Attendees should have a good understanding of the fundamental concepts of building Tableau worksheets and dashboards typically achieved from having attended our Tableau Desktop Foundation Course. At the end of this course you will be able to communicate insights more effectively, enabling your organisation to make better decisions, quickly. The Tableau Desktop Analyst training course is aimed at people who are used to working with MS Excel or other Business Intelligence tools and who have preferably been using Tableau already for basic reporting. The course is split into 3 phases and 9 modules: Phase 1: AMPLIFY MODULE 1: CHECK ABILITIES Revision – What I Should Know What is possibleHow does Tableau deal with dataKnow your way aroundHow do we format chartsHow Tableau deals with datesCharts that compare multiple measuresCreating Tables MODULE 2: COMBINE DATA Relationships Joining Tables – Join Types, Joining tables within the same database, cross database joins, join calculations Blending – How to create a blend with common fields, Custom defined Field relationships and mismatched element names, Calculated fields in blended data sources Unions – Manual Unions and mismatched columns, Wildcard unions Data Extracts – Creating & Editing Data extracts MODULE 3: ADVANCED CALCULATIONS Row Level v Aggregations Aggregating dimensions in calculations Changing the Level of Detail (LOD) of calculations – What, Why, How Adding Table Calculations Phase 2: ANALYSE MODULE 4: EXPAND APPLICATION Making things dynamic with parameters Sets Trend Lines How do we format charts Forecasting MODULE 5: ADVANCED MAPPING Using your own images for spatial analysis Mapping with Spatial files MODULE 6: DATA COMPARISONS Advanced Charts Bar in Bar charts Bullet graphs Creating Bins and Histograms Creating a Box & Whisker plot Phase 3: ACT MODULE 7: ADVANCED DASHBOARDS Using the dashboard interface and Device layout Dashboard Actions and Viz In tooltips Horizontal & Vertical containers Navigate between dashboards MODULE 8: PRESENT STORIES Telling data driven stories MODULE 9: ENABLE DECISIONS What is Tableau Server Publishing & Permissions How can your users engage with content This training course includes over 25 hands-on exercises and quizzes to help participants “learn by doing” and to assist group discussions around real-life use cases. Each attendee receives a login to our extensive training portal which covers the theory, practical applications and use cases, exercises, solutions and quizzes in both written and video format. Students must bring their own laptop with an active version of Tableau Desktop 2018.2 (or later) pre-installed. What People Are Saying About This Course “Course was fantastic, and completely relevant to the work I am doing with Tableau. I particularly liked Steve’s method of teaching and how he applied the course material to ‘real-life’ use-cases.”Richard W., Dashboard Consulting Ltd “This course was extremely useful and excellent value. It helped me formalise my learning and I have taken a lot of useful tips away which will help me in everyday work.” Lauren M., Baillie Gifford “I would definitely recommend taking this course if you have a working knowledge of Tableau. Even the little tips Steve explains will make using Tableau a lot easier. Looking forward to putting what I’ve learned into practice.”Aron F., Grove & Dean “Steve is an excellent teacher and has a vast knowledge of Tableau. I learned a huge amount over the two days that I can immediately apply at work.”John B., Mporium “Steve not only provided a comprehensive explanation of the content of the course, but also allowed time for discussing particular business issues that participants may be facing. That was really useful as part of my learning process.”Juan C., Financial Conduct Authority “Course was fantastic, and completely relevant to the work I am doing with Tableau. I particularly liked Steve’s method of teaching and how he applied the course material to ‘real-life’ use-cases.”Richard W., Dashboard Consulting Ltd “This course was extremely useful and excellent value. It helped me formalise my learning and I have taken a lot of useful tips away which will help me in everyday work.” Lauren M., Baillie Gifford “I would definitely recommend taking this course if you have a working knowledge of Tableau. Even the little tips Steve explains will make using Tableau a lot easier. Looking forward to putting what I’ve learned into practice.”Aron F., Grove & Dean “Steve is an excellent teacher and has a vast knowledge of Tableau. I learned a huge amount over the two days that I can immediately apply at work.”John B., Mporium
(9-10yrs) Ballet develops posture, strength, musicality and grace. Each dancer is unique and each body is unique and we teach the children to work within ones own body. Our Ballet classes include some set structured technical work from the Imperial Society of Teachers of Dance syllabus, along with some creative movement. All children have the opportunity to take ISTD Ballet exams when they are ready to be entered. TRIAL BOOKINGS: Of course you are welcome to watch the trial class but following the trial, WhizzDancers are expected to be independent in the room. TERM BOOKINGS: You are welcome to watch the first class but following this your WhizzDancer will be expected to go in the class independently. You will be expected to provide full uniform. Details will be sent following. We have lots of opportunities ahead for your WhizzDancer including exams and shows. We look forward to meeting them in the studio :) Upstairs Dance Studio Please bring: - Comfortable clothes to move in (no zips or demin) - A teddy - No ballet shoes required for the trial Please contact info@whizzdance.com for more information on how to book your free trial.

Level 1 Award in Fire Safety Awareness (RQF)
By NR Medical Training
This nationally recognised and regulated qualification is the perfect opportunity for businesses to invest in the safety of their employees. Enhance their fire safety knowledge and equip them with the necessary skills to ensure a safe working environment at all times. With its foundation in National Occupational Standards for fire safety awareness and alignment with the Health and Safety Executive's guidelines for good practice, this is the ideal choice for businesses looking to make a proactive step in promoting workplace safety.

Veeam Certified Architect v11 (VMCE11-A)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for This course is suitable for anyone responsible for configuring, managing or supporting a Veeam Availability Suite v11 environment. This includes Senior Engineers and Architects responsible for creating architectures for Veeam environments. Overview After completing this course, attendees should be able to: Describe Veeam Availability Suite components usage scenarios and relevance to your environment. Effectively manage data availability in on-site, off-site, cloud and hybrid environments. Ensure both Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs) are met. Configure Veeam Availability Suite to ensure data is protected effectively. Adapt with an organization's evolving technical and business data protection needs. Ensure recovery is possible, effective, efficient, secure and compliant with business requirements. Provide visibility of the business data assets, reports and dashboards to monitor performance and risks. Design and architect a Veeam solution in a real-world environment Describe best practices, review an existing infrastructure and assess business/project requirements Identify relevant infrastructure metrics and perform component (storage, CPU, memory) quantity sizing Provide implementation and testing guidelines in line with designs Innovatively address design challenges and pain points, matching appropriate Veeam Backup & Replication features with requirements Veeam Certified Architect is the highest level of Veeam technical certifications. Engineers who complete both Veeam Availability Suite v11: Configuration and Management and Veeam Backup & Replication V11: Architecture and Design programs (courses + exams) will be granted with the 'Veeam Certified Architect' (VMCA) title by Veeam. Introduction Veeam Availability Suite v11: Configuration and Management Describe RTOs and RPOs, what they mean for your business, how to manage and monitor performance against them The 3-2-1 Rule and its importance in formulating a successful backup strategy Identify key Veeam Availability Suite components and describe their usage scenarios and deployment types Building backup capabilities Backup methods, the appropriate use cases and impact on underlying file systems Create, modify, optimize and delete backup jobs, including Agents and NAS Backup jobs. Explore different tools and methods to maximize environment performance Ensure efficiency by being able to select appropriate transport modes while being aware of the impact of various backup functions on the infrastructure Building replication capabilities Identify and describe the options available for replication and impacts of using them Create and modify replication jobs, outline considerations to ensure success Introduce the new Continuous Data Protection (CDP) policy Secondary backups Simple vs. advanced backup copy jobs, how to create and modify them using best practices to ensure efficient recovery Discuss using tapes for backups Advanced repository capabilities Ensure repository scalability using a capability such as SOBR on-premises and off-site including integration with cloud storage Ensure compatibility with existing deduplication appliances Introduce the new hardened repository Protecting data in the cloud Review how Veeam can protect the data of a cloud native application Review how Veeam Cloud Connect enables you to take advantage of cloud services built on Veeam Review how Veeam can be used to protect your Office 365 data Restoring from backup Ensure you have the confidence to use the correct restore tool at the right time for restoring VMs, bare metal and individual content such as files and folders Utilize Secure Restore to prevent the restoration of malware Describe how to use Staged Restore to comply with things like General Data Protection Regulation (GDPR) before releasing restores to production Identify, describe and utilize the different explores and instant recovery tools and features Recovery from replica Identify and describe in detail, failover features and the appropriate usage Develop, prepare and test failover plans to ensure recovery Disaster recovery from replica to meet a variety of real-world recovery needs Testing backup and replication Testing backups and replicas to ensure you can recover, what you need, when you need to Configure and setup virtual sandbox environments based on backup, replicas and storage snapshots Veeam Backup Enterprise Manager and Veeam ONE Introduce the concept of monitoring your virtual, physical and cloud environments with Veeam Backup Enterprise Manager and Veeam ONE? Configuration backup Locate, migrate or restore backup configuration Introduction Veeam Backup & Replication v11: Architecture and Design Review the architecture principles Explore what a successful architecture looks like Review Veeam?s architecture methodology Discovery Analyze the existing environment Uncover relevant infrastructure metrics Uncover assumptions and risks Identify complexity in the environment Conceptual design Review scenario and data from discovery phase Identify logical groups of objects that will share resources based on requirements Create a set of detailed tables of business and technical requirements, constraints, assumptions and risks Review infrastructure data with each product component in mind Create high level design and data flow Logical design Match critical components and features of VBR with requirements Create logical groupings Determine location of components and relationship to logical grouping Aggregate totals of component resources needed per logical grouping Calculate component (storage, CPU, memory) quantity sizing Physical/tangible design Convert the logical design into a physical design Physical hardware sizing Create a list of physical Veeam backup components Implementation and Governance Review physical design and implantation plan Review Veeam deployment hardening Describe the architect?s obligations to the implementation team Provide guidance on implementation specifics that relate to the design Validation and Iteration Provide framework for how to test the design Further develop the design according to a modification scenario

EXIN Cloud Computing Foundation
By Nexus Human
Duration 2 Days 12 CPD hours This course is intended for Diese Zertifizierung richtet sich an Experten aus Geschäftsbetrieben aller Branchen, die mit der Cloud-Technologie arbeiten oder an dieser Technologie und ihrem Nutzen für Unternehmen interessiert sind: Alle Mitarbeiter von internen oder externen Service Providern, Ihre Kunden Manager, Auditoren Overview Die Zertifizierung EXIN Cloud Computing Foundation validiert das Wissen von Kandidaten in folgenden Bereichen: Cloud - Prinzipien Implementierung von Management des Cloud Computing Nutzung von Cloud Computing Sicherheit, Identität und Privatsphäre im Cloud Computing Bewertung des Cloud Computing Unter Cloud Computing versteht man die Implementierung und Nutzung der Cloud - Technologie um IT - Services bereitzustellen, die an einem andren Standort gehostet werden. Cloud-Prinzipien Das Cloud - Konzept Entwicklung des Cloud Computing Cloud - Architektur Vorteile und Beschrânkungen des Cloud Computing Implementierung und Management des Cloud Computing Aufbau lokaler Cloud - Umgebungen Management - Prinzipien fÂr Cloud - Services Nutzung von Cloud Computing Zugriff auf die Cloud UnterstÂtzung von Business - Prozessen durch Cloud Computing Cloud - Nutzung durch Service Provider Sicherheit, Identitât und Privatsphâre im Cloud Computing Sicherheit im Cloud Computing Identitâts- und Privatsphârenmanagement Bewertung des Cloud Computing Business Cas fÂr das Cloud Computing Bewertung von Cloud - Implementierungen

(6-8yrs) Jazz and modern is perfect for the kids who just can't stop moving when One Direction and Beyonce come on the telly! Using a range of music from the latest pop songs to great musical theatre songs (old and new!) JazzPops offers a range of dance throughout the term with a dash of some musical games. We also sneak in some dance technique from the ISTD Modern Theatre Syllabus. But don't tell the children that, they are having too much fun! TRIAL BOOKINGS: Of course you are welcome to watch the trial class but following the trial, WhizzDancers are expected to be independent in the room. TERM BOOKINGS: You are welcome to watch the first class but following this your WhizzDancer will be expected to go in the class independently. You will be expected to provide full uniform. Details will be sent following. We have lots of opportunities ahead for your WhizzDancer including exams and shows. We look forward to meeting them in the studio :) Upstairs Dance Studio Please bring: - Comfortable clothes to move in (no zips or demin) - No ballet shoes required for the trial Please contact info@whizzdance.com for more information on how to book your free trial.

Cisco ASA Essentials (ASAE)
By Nexus Human
Duration 5 Days 30 CPD hours This course is intended for Students who need to know how to implement and manage Cisco ASA 5500-X. Overview Upon successful completion of this course, students should be able to do the following:? Technology and features of the Cisco ASA? Cisco ASA product family? How ASAs protect network devices from attacks? Bootstrap the security appliance? Prepare the security appliance for configuration via the Cisco Adaptive Security Device Manager (ASDM)? Launch and navigate ASDM? Essential security appliance configuration using ASDM and the command-line interface (CLI)? Configure dynamic and static address translations? Configure access policy based on ACLs? Use object groups to simplify ACL complexity and maintenance? Use the Modular Policy Framework to provide unique policies to specific data flows? Handle advanced protocols with application inspection? Troubleshoot with syslog and tcp ping? Configure the ASA to work with Cisco Secure ACS 5.2 for RADIUS-based AAA of VPNs? Implement site-to-site IPsec VPN? Implement remote access IPsec and SSL VPNs using the Cisco AnyConnect 3.0 Secure Mobility Client? Work with the 5.x Legacy Cisco IPsec VPN client and Anyconnect VPN client? Deploy clientless SSL VPN access, including smart tunnels, plug-ins, and web-type ACLs? Configure access control policies to implement your security policy across all classes of VPN? Configure Active/Standby failover for both firewall and VPN high availability Student will gain the essential skills required to configure, maintain, and operate Cisco ASA 5500-X Series Adaptive Security Appliances based on ASA Software v9.x. Cisco ASA Essentials ? Lesson 1: Evaluating Cisco ASA Technologies ? Lesson 2: Identifying Cisco ASA Families Basic Connectivity and Device Management ? Lesson 1: Preparing the Cisco ASA for Network Integration ? Lesson 2: Managing Basic Cisco ASA Network Settings ? Lesson 3: Configuring Cisco ASA Device Management Features Network Integration ? Lesson 1: Configuring Cisco ASA NAT Features ? Lesson 2: Configuring Cisco ASA Basic Access Control Features Cisco ASA Policy Control ? Lesson 1: Cisco ASA Modular Policy Framework ? Lesson 2: Configuring Cisco ASA Connection Policy Cisco ASA VPN Architecture and Common Components ? Lesson 1: Implementing Profiles, Group Policies, and User Policies ? Lesson 2: Implementing PKI Services Cisco ASA Clientless Remote Access SSL VPN Solutions ? Lesson 1: Deploying Basic Clientless VPN Solutions ? Lesson 2: Deploying Advanced Application Access for Clientless SSL VPNs Cisco AnyConnect Remote Access SSL Solutions ? Lesson 1: Deploying a Basic Cisco AnyConnect Full-Tunnel SSL VPN Solution Cisco ASA Remote Access IPsec VPNs ? Lesson 1: Deploying Cisco Remote Access VPN Clients ? Lesson 2: Deploying Basic Cisco Remote Access IPsec VPN Solutions Cisco ASA Site-to-Site IPsec VPN Solutions ? Lesson 1: Deploying Basic Site-to-Site IPsec VPNs ? Lesson 2: Deploying Advanced Site-to-Site IPsec VPNs Cisco ASA High Availability and Virtualization ? Lesson 1: Configuring Cisco ASA Active/Standby High Availability Labs Lab 1: Prepare the ASA for Administration Lab 2: Fundamental ASA Configuration Lab 3: Network Address Translation (NAT) Lab 4: Basic Access Control Lab 5: Basic Protocol Inspection Lab 6: Licensing, ACS, and Public CA Lab 7: Basic Clientless SSL VPN Lab 8: Clientless SSL VPN - Thin Apps Lab 9: Basic AnyConnect Full Tunnel SSL VPN Lab 10: Remote Access IPSec VPN Lab 11: IPSec Site-to-Site VPN Lab 12: Active/Standby Failover

Cyber Awareness
By Global Risk Alliance Ltd
This course aims to increase and enhance delegates’ understanding of the various cyber threats which impact upon them and the organisations, sectors and regions in which they operate and provide them with the tools necessary to mitigate those threats at both a personal and organisational level. It assumes no prior knowledge of the subject but ensures through a high level of interactivity that delegates with any level of experience in the field will be able share and receive the collective knowledge of the group.

Search By Location
- Course Courses in London
- Course Courses in Birmingham
- Course Courses in Glasgow
- Course Courses in Liverpool
- Course Courses in Bristol
- Course Courses in Manchester
- Course Courses in Sheffield
- Course Courses in Leeds
- Course Courses in Edinburgh
- Course Courses in Leicester
- Course Courses in Coventry
- Course Courses in Bradford
- Course Courses in Cardiff
- Course Courses in Belfast
- Course Courses in Nottingham