- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
43355 Courses
Dive into the world of sustainable architecture and environmental design with the 'LEED V4 - Diploma in Building Design and Construction at QLS Level 4.' This comprehensive course, meticulously structured over eleven units, offers a deep exploration of green building principles and practices. Starting with an introductory unit that sets the stage for a transformative learning journey, the course progresses through a series of meticulously crafted modules. Each unit, from the integrative process to regional priority considerations, is designed to enhance understanding and skills in creating environmentally responsible and resource-efficient buildings. The curriculum culminates with a completion unit, ensuring learners emerge with a holistic grasp of the subject matter. The diploma not only educates but inspires, focusing on critical areas such as location and transportation, sustainable site development, water efficiency strategies, energy and atmosphere considerations, and the use of sustainable materials and resources. It also delves into the nuances of indoor environmental quality and innovative approaches to building design and construction. This course is an invaluable resource for those aspiring to make a significant impact in the building and construction industry, equipping them with the knowledge to design and construct buildings that align with the advanced standards of LEED V4. Learning Outcomes Acquire comprehensive knowledge of sustainable building practices and principles. Develop expertise in optimizing water usage and energy efficiency in construction. Gain skills in selecting and utilizing sustainable materials and resources. Understand the significance of indoor environmental quality in building design. Master innovative strategies for building design and construction with a focus on regional priorities. Why choose this LEED V4 - Diploma in Building Design and Construction at QLS Level 4 course? Unlimited access to the course for a lifetime. Opportunity to earn a certificate accredited by the CPD Quality Standards after completing this course. Structured lesson planning in line with industry standards. Immerse yourself in innovative and captivating course materials and activities. Assessments are designed to evaluate advanced cognitive abilities and skill proficiency. Flexibility to complete the course at your own pace, on your own schedule. Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience. Who is this LEED V4 - Diploma in Building Design and Construction at QLS Level 4 course for? Aspiring architects and designers keen on specializing in sustainable construction. Professionals in the construction industry aiming to enhance their eco-friendly building skills. Environmental consultants seeking to deepen their knowledge of green building practices. Urban planners interested in incorporating sustainable strategies in city designs. Project managers in the construction sector aiming to adopt LEED V4 standards. Career path Sustainable Architect: £30,000 - £50,000 Green Building Consultant: £35,000 - £55,000 Environmental Design Coordinator: £32,000 - £48,000 Urban Sustainability Planner: £28,000 - £45,000 Resource Efficiency Manager: £34,000 - £52,000 Eco-friendly Construction Project Manager: £36,000 - £60,000 Prerequisites This LEED V4 - Diploma in Building Design and Construction at QLS Level 4 does not require you to have any prior qualifications or experience. You can just enrol and start learning. This course was made by professionals and it is compatible with all PC's, Mac's, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection. Certification After studying the course materials, there will be a written assignment test which you can take at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £4.99 Original Hard Copy certificates need to be ordered at an additional cost of £8. Endorsed Certificate of Achievement from the Quality Licence Scheme Learners will be able to achieve an endorsed certificate after completing the course as proof of their achievement. You can order the endorsed certificate for only £95 to be delivered to your home by post. For international students, there is an additional postage charge of £10. Endorsement The Quality Licence Scheme (QLS) has endorsed this course for its high-quality, non-regulated provision and training programmes. The QLS is a UK-based organisation that sets standards for non-regulated training and learning. This endorsement means that the course has been reviewed and approved by the QLS and meets the highest quality standards. Please Note: Studyhub is a Compliance Central approved resale partner for Quality Licence Scheme Endorsed courses. Course Curriculum Unit 01: Introduction Introduction 00:01:00 Getting Started 00:04:00 Minimum Program Requirements 00:07:00 Rating System Selection 00:07:00 Unit 02: Integrative Process Integrative Process 00:04:00 Integrative Project Planning and Design 00:02:00 Unit 03: Location & Transportation Overview 00:03:00 Neigbourhoud Development 00:03:00 Sensitive Land 00:02:00 Surrounding Density & Diverse Uses 00:07:00 High Priority Site 00:02:00 Access to Quality Transit 00:06:00 Bicycle Facilities 00:06:00 Reduced Parking Footprint 00:04:00 Green Vehicles 00:04:00 Unit 04: Sustainable Sites Overview 00:02:00 Construction Activity Pollution Prevention 00:03:00 Environmental Site Assessment 00:03:00 Restore or Protect Habitat 00:04:00 Open Space 00:03:00 Rainwater Management 00:03:00 Heat Island Reduction 00:04:00 Light Pollution Reduction 00:05:00 Site Master Plan 00:02:00 Tenant Design and Construction Guidelines 00:02:00 Places of Respite 00:03:00 Direct Exterior Access 00:02:00 Joint Use Facilities 00:03:00 Unit 05: Water Efficiency Overview 00:01:00 Prereq Outdoor Water Use 00:03:00 Prereq Indoor Water Use 00:04:00 Prereq Building Water Metering 00:02:00 Credit Outdoor Water Use 00:02:00 Credit Indoor Water Use 00:03:00 Cooling Tower Water use 00:03:00 Building Water Metering Credit 00:02:00 Unit 06: Energy & Atmosphere Overview 00:02:00 Fundamental Commissioning & Verification 00:04:00 Minimum Energy Performance 00:05:00 Prereq Building Level Energy Metering 00:02:00 Fundamental Refrigerant Management 00:02:00 Enhanced Commissioning 00:05:00 Minimum Energy Performance 00:04:00 Advanced Energy Metering 00:02:00 Demand Response 00:03:00 Renewable Energy Production 00:02:00 Enhanced Refrigerant Management 00:03:00 Green Powerand Carbon Offsets 00:02:00 Unit 07: Materials & Resources Overview 00:02:00 Storage and Collection of Recyclables 00:03:00 Construction and Demolition Waste Management Planning 00:02:00 Preq PBT Source Reduction - Mercury 00:03:00 Building Life Cycle Impact Reduction 00:05:00 BPDO Environmental Product Declaration 00:04:00 BPDO Sourcing of Raw Materials (2020 Update Web) 00:03:00 BPDO Material Ingredients 00:05:00 PBT Source Reduction - Mercury Credit 00:02:00 PBT Source Reduction - Lead Cadmium Copper 00:03:00 Furniture and Medical Furnishings 00:04:00 Design for Flexibilty 00:02:00 Construction and Demolition Waste Management 00:03:00 Unit 08: Indoor Environment Quality Overview 00:01:00 Min Indoor Air Quality Performance 00:06:00 Environmental Tobacco Smoke Control 00:03:00 Minimum Accoustic Performance 00:03:00 Enhanced Indoor Air Quality Strategies 00:02:00 Low Emitting Materials 00:03:00 Construction Indoor Air Quality Management Plan 00:04:00 Indoor Air Quality Assessment 00:03:00 Thermal Comfort 00:04:00 Interior Lighting 00:06:00 Daylight 00:06:00 Quality Views 00:03:00 Accoustic Performance 00:03:00 Unit 09: Innovation Innovation Credit 00:03:00 Innovation LEED AP 00:01:00 Unit 10: Regional Priority Regional Priority Overview 00:01:00 Regional Priority Credit 00:02:00 Unit 11: Completion Completion 00:01:00 Assignment Assignment - LEED V4 - Diploma in Building Design and Construction at QLS Level 4 02:00:00 Order your QLS Endorsed Certificate Order your QLS Endorsed Certificate 00:00:00
CBT Tools and Strategies
By NextGen Learning
*** A Better Pathway for Rapid Growth! Limited Time Opportunity; Hurry Up! *** Ignite your dynamic career and strengthen your deep insight knowledge by signing up for CBT Tools and Strategies. This cours is the ideal approach for you to obtain a thorough understanding and knowledge of the subject. We are concerned about the progression of your career. Therefore, after conducting extensive studies and consulting with experienced personnel, we formulated this outstanding course to improve your pertinent skills. In this easy-to-digest course, you will get exclusive training, which will enable you to stand out in this competitive market. However, the CBT Tools and Strategies course covers all of the recent materials in order to keep you up to date with the job market and make you a good fit for your career. This top-notch course curriculum comprises basic to advanced levels of modules that will increase your skillsets. After completing this Programme, you will attain the productivity to succeed in your organisation. So, if you are eager to see yourself in a gratifying CBT Tools and Strategies career, then enrol in our course today! What will make you stand out? On completion of this online course, you will gain: After successfully completing the Course, you will receive a FREE PDF Certificate as evidence of your newly acquired abilities. Lifetime access to the whole collection of CBT Tools and Strategies learning materials. The CBT Tools and Strategies course online test with immediate results Enroling in the Course has no additional costs. You can study and complete the CBT Tools and Strategies course at your own pace. Study for the course using any internet-connected device, such as a computer, tablet, or mobile device. The substantial CBT Tools and Strategies is designed to help you demonstrate the preliminary to in-depth level of learning regarding this topic. Moreover, you will be provided with the most knowledgeable and informative modules for your lifetime by enroling in this course just once. Furthermore, as you proceed through the modules of this course, you will discover the fundamentals of CBT Tools and Strategies and explore the key topics such as: CBT Tools and Strategies Module 01: Introduction to CBT Module 02: CBT Theories and Principles Module 03: CBT Tools and Strategies Module 04: CBT Process Module 05: CBT for Personal Growth Module 06: Overcoming Anxiety and Depression Module 07: CBT for Children with Autism Therefore, reinforce your knowledge and furnish your skills by enroling in our CBT Tools and Strategies course. Take one step closer to achieving your goal. Show off your new skills with a certificate of completion When you have finished all of the CBT Tools and Strategies course lectures, a digital certificate will be available for download. CPD 10 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Is This CBT Tools and Strategies Course the Right Option for You? This CBT Tools and Strategies course is recommended for anyone who is interested in learning more about this topic. Taking this course, you'll learn the fundamental ideas and gain a comprehensive understanding of the topic. This CBT Tools and Strategies course is open to everybody. You can access the course materials from any location in the world, and there are no requirements for enrolment. You should enrol in this course if you: Aspire to understand CBT Tools and Strategies better. Already working on CBT Tools and Strategies and eager to learn more. Is a student pursuing a relevant field of study? Trying to get a job in CBT Tools and Strategies-related fields. Requirements Without any formal requirements, you can delightfully enrol in this CBT Tools and Strategies course. Just get a device with internet connectivity and you are ready to start your learning journey. Thus, complete this CBT Tools and Strategies course at your own pace. Career path The aim of this exclusive CBT Tools and Strategies course is to help you toward your dream career. So, complete this CBT Tools and Strategies course and enhance your skills to explore opportunities in relevant areas.
Martial Arts Injuries and Treatment
By Compliance Central
Are you looking to enhance your Martial Arts Injuries and Treatment skills? If yes, then you have come to the right place. Our comprehensive course on Martial Arts Injuries and Treatment will assist you in producing the best possible outcome by mastering the Martial Arts Injuries and Treatment skills. The Martial Arts Injuries and Treatment course is for those who want to be successful. In the Martial Arts Injuries and Treatment course, you will learn the essential knowledge needed to become well versed in Martial Arts Injuries and Treatment. Our Martial Arts Injuries and Treatment course starts with the basics of Martial Arts Injuries and Treatment and gradually progresses towards advanced topics. Therefore, each lesson of this Martial Arts Injuries and Treatment course is intuitive and easy to understand. Why would you choose the Martial Arts Injuries and Treatment course from Compliance Central: Lifetime access to Martial Arts Injuries and Treatment course materials Full tutor support is available from Monday to Friday with the Martial Arts Injuries and Treatment course Learn Martial Arts Injuries and Treatment skills at your own pace from the comfort of your home Gain a complete understanding of Martial Arts Injuries and Treatment course Accessible, informative Martial Arts Injuries and Treatment learning modules designed by experts Get 24/7 help or advice from our email and live chat teams with the Martial Arts Injuries and Treatment Study Martial Arts Injuries and Treatment in your own time through your computer, tablet or mobile device A 100% learning satisfaction guarantee with your Martial Arts Injuries and Treatment Course Martial Arts Injuries and Treatment Curriculum Breakdown of the Martial Arts Injuries and Treatment Course Module 01: Introduction to Martial Arts First Aid Module 02: Initial Assessment Module 03: CPR & Recovery Position Module 04: Common Injuries Module 05: Major Injuries Module 06: Medical Emergencies Module 07: Injury Prevention Module 08: Things to Keep in Mind CPD 10 CPD hours / points Accredited by CPD Quality Standards Who is this course for? The Martial Arts Injuries and Treatment course helps aspiring professionals who want to obtain the knowledge and familiarise themselves with the skillsets to pursue a career in Martial Arts Injuries and Treatment. It is also great for professionals who are already working in Martial Arts Injuries and Treatment and want to get promoted at work. Requirements To enrol in this Martial Arts Injuries and Treatment course, all you need is a basic understanding of the English Language and an internet connection. Career path The Martial Arts Injuries and Treatment course will enhance your knowledge and improve your confidence. Sports Rehabilitation Specialist: £30,000 to £50,000 per year Physiotherapist specializing in Sports Injuries: £25,000 to £45,000 per year Sports Massage Therapist: £20,000 to £40,000 per year Athletic Trainer: £25,000 to £45,000 per year Sports Science Researcher: £25,000 to £50,000 per year Certificates CPD Accredited PDF Certificate Digital certificate - Included CPD Accredited PDF Certificate CPD Accredited Hard Copy Certificate Hard copy certificate - £10.79 CPD Accredited Hard Copy Certificate Delivery Charge: Inside the UK: Free Outside of the UK: £9.99 each

Reels Marketing on Instagram & TikTok Course Online
By Study Plex
What you will learn from this course? Gain comprehensive knowledge about digital marketing Understand the core competencies and principles of digital marketing Explore the various areas of digital marketing Know how to apply the skills you acquired from this course in a real-life context Become a confident and expert digital media marketer Course Highlights Course Type: Self-paced online course Duration: 13 hours 9 minute Tutor Support: Full tutor support is included Customer Support: 24/7 customer support is available Reels Marketing on Instagram & TikTok Course Online Master the skills you need to propel your career forward in digital marketing. This course will equip you with the essential knowledge and skillset that will make you a confident digital media marketer and take your career to the next level. This comprehensive f course is designed to help you surpass your professional goals. The skills and knowledge that you will gain through studying this reels marketing on Instagram & TikTok course online will help you get one step closer to your professional aspirations and develop your skills for a rewarding career. This comprehensive course will teach you the theory of effective digital marketing practice and equip you with the essential skills, confidence and competence to assist you in the digital marketing industry. You'll gain a solid understanding of the core competencies required to drive a successful career in digital marketing. This course is designed by industry experts, so you'll gain knowledge and skills based on the latest expertise and best practices. This extensive course is designed for digital media marketer or for people who are aspiring to specialize in digital marketing. Enroll in this reels marketing on Instagram & TikTok course today and take the next step towards your personal and professional goals. Earn industry-recognized credentials to demonstrate your new skills and add extra value to your CV that will help you outshine other candidates. Who is this Course for? This comprehensive reels marketing on Instagram & TikTok course is ideal for anyone wishing to boost their career profile or advance their career in this field by gaining a thorough understanding of the subject. Anyone willing to gain extensive knowledge on this reels marketing on Instagram & TikTok course can also take this course. Whether you are a complete beginner or an aspiring professional, this course will provide you with the necessary skills and professional competence, and open your doors to a wide number of professions within your chosen sector. Entry Requirements This reels marketing on Instagram & TikTok course has no academic prerequisites and is open to students from all academic disciplines. You will, however, need a laptop, desktop, tablet, or smartphone, as well as a reliable internet connection. Assessment This reels marketing on Instagram & TikTok course assesses learners through multiple-choice questions (MCQs). Upon successful completion of the modules, learners must answer MCQs to complete the assessment procedure. Through the MCQs, it is measured how much a learner could grasp from each section. In the assessment pass mark is 60%. Advance Your Career This reels marketing on Instagram & TikTok course will provide you with a fresh opportunity to enter the relevant job market and choose your desired career path. Additionally, you will be able to advance your career, increase your level of competition in your chosen field, and highlight these skills on your resume. Study Plex Subscription Study plex also provides a subscription option that allows you unlimited access to more than 700+ CPD courses for learning. You only need to spend £79 to take advantage of this fantastic offer, and you'll get an unlimited subscription for a full year. Additionally, you can cancel your membership from your account at any time by getting in touch with our friendly and devoted customer care team. Visit our subscriptions page for more details if you're interested. Why you should train with Study Plex? At Study Plex, you will have the chance to build social, technical and personal skills through a combination of extensive subjects tailored according to your interest. Along with receiving comprehensive knowledge and transferable skills, there are even more reasons o be involved with us, which include: Incredible Customer Support: We offer active customer service in the form of live chat, which you can access 24/7 Expert Tutor Support: You'll have access to our devoted and dedicated tutor support with all of our courses whenever you need it. Price Justified by Quality: We ensure that you will have the best experience possible for the price you are paying for the course. Money-back Guarantee: We provide a money-back guarantee if you are not satisfied with the course's quality. There is a 14-day time limit on this option (according to the terms and conditions). Instalment Facility: If your course costs more than £50, you can pay in three instalments using the instalment option. Satisfaction Guarantee: Our courses are designed to meet your demands and expectations by all means. Recognised Accreditation This course is accredited by continuing professional development (CPD). CPD UK is globally recognised by employers, professional organisations, and academic institutions, thus a certificate from CPD Certification Service creates value towards your professional goal and achievement. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. What is CPD? Employers, professional organisations, and academic institutions all recognise CPD, therefore a credential from CPD Certification Service adds value to your professional goals and achievements. Benefits of CPD Improve your employment prospects Boost your job satisfaction Promotes career advancement Enhances your CV Provides you with a competitive edge in the job market Demonstrate your dedication Showcases your professional capabilities What is IPHM? The IPHM is an Accreditation Board that provides Training Providers with international and global accreditation. The Practitioners of Holistic Medicine (IPHM) accreditation is a guarantee of quality and skill. Benefits of IPHM It will help you establish a positive reputation in your chosen field You can join a network and community of successful therapists that are dedicated to providing excellent care to their client You can flaunt this accreditation in your CV It is a worldwide recognised accreditation What is Quality Licence Scheme? This course is endorsed by the Quality Licence Scheme for its high-quality, non-regulated provision and training programmes. The Quality Licence Scheme is a brand of the Skills and Education Group, a leading national awarding organisation for providing high-quality vocational qualifications across a wide range of industries. Benefits of Quality License Scheme Certificate is valuable Provides a competitive edge in your career It will make your CV stand out Course Curriculum Welcome to the World of Marketing Where Short Video is King Modern Degital Marketing Strategies1.1 00:05:00 The role of short-form video in social media marketing1.2 00:08:00 Techniques to create strong short-form video1.3 00:08:00 Digging deeper TikTok1.4 00:08:00 Digging deeper Instagram Reels1.5 00:05:00 Effective Marketing Strategies for TikTok Videos Top strategies for creating effective TikToks2.1.mov 00:10:00 Understanding the TikTok algorithm2.2 00:08:00 Using hashtags effectively2.3 00:08:00 Capitalizing on trends and challenges2.4 00:08:00 Leveraging influencers2.5. 00:08:00 Creating ads2.6 00:07:00 Using other TikTok tools and techniques2.7.mov 00:07:00 Effective Marketing Strategies for Instagram reels Connections between Reels and TikTok strategies3.1.mov 00:07:00 Understanding the unique selling points of Instagram Reels.3.2 00:07:00 Implementing your social strategy for TikTok and Reels3.3 00:03:00 Instagram Profile Setup and Orientation Tour the Instagram user interface1.1 00:06:00 Convert to an Instagram professional account1.2 00:04:00 Optimizing your Professional Instagram Profile1.3.mov 00:04:00 Optimizing uploads of photos and videos1.4 00:05:00 Modify Instagram Settings1.5 00:04:00 Using Instagram on a Computer1.6 00:02:00 Get Started with Marketing on Instagram Explore models of business success2.1 00:04:00 Built-in tools for marketing2.2 00:04:00 Interact with the community to build trust2.3 00:05:00 Develop a Marketing strategy for Instagram Content ideas and strategies for Instagram3.1 00:05:00 Create a unique style on Instagram 3.2 00:04:00 Research your competition on Instagram 3.3 00:04:00 Utilize hashtags with a posting schedule3.4 00:05:00 Implement Your Instagram Marketing Campaign Marketing with Instagram Stories 4.1 00:04:00 Marketing with Instagram Reels 4.2 00:04:00 Marketing with IGTV4.3 00:05:00 Marketing with live video on Instagram4.4 00:05:00 Using Instagram Shopping posts4.5 00:04:00 Content marketing with Instagram Guides4.6 00:04:00 Leveraging Instagram paid ads4.7.mov 00:05:00 Optimize Your Marketing Strategy on Instagram Review Instagram Insights to optimize marketing strategy5.1 00:05:00 Run polls and ask questions on Instagram5.2 00:05:00 Saving Instagram Stories as Story Highlights5.3 00:04:00 Embedding Instagram photos into websites5.4 00:02:00 Useful Instagram enhancement platforms5.5 00:05:00 Additional resources5.6 00:02:00 Live Video Styles Live educational videos 1.1 00:04:00 Live interview videos 1.2 00:04:00 Live demo videos 1.3 00:04:00 Live video tours 1.4 00:04:00 Creating Live Video Content When to create live video 2.1 00:04:00 Different live video platforms 2.2 00:05:00 Preparing for your live video 2.3 00:03:00 Introductions and conclusions in your live video2.4 00:05:00 Creating engagement during live videos 2.5 00:03:00 Promoting Your Live Video Building your live video audience 3.1 00:05:00 Sharing your live video 3.2 00:05:00 Repurposing your live video 3.3 00:04:00 Launching Live Video Tools for live video 4.1 00:04:00 Visuals for live video 4.2 00:04:00 Start creating live videos 4.3 00:01:00 Good Understanding of Content Content means too much.1.1 00:03:00 Content is more than all blogs and articles 1.2 00:02:00 Content is more than a cost understanding 1.3 00:02:00 Understand Content Marketing Understand content marketing 2.1 00:04:00 Where did this content marketing come from 2.2 00:07:00 What is the main purpose of content marketing 2.3 00:04:00 Advanced goals of content marketing 2.4 00:04:00 Details for Successful Content Marketing How to grow the niche content audience 3.1 00:04:00 Understanding a different brand perspective 3.2 00:04:00 Presenting content experiments 3.3 00:05:00 Actively understanding content 3.4 00:03:00 Developing a Successful Content Marketing Strategy Forget what you know 4.1 00:04:00 Choosing the right audience 4.2 00:04:00 Our competitive analysis priority 4.3 00:04:00 understand your right to win 4.4 00:03:00 How We Can Create and Source Effective Content Creating content on the customer journey 5.1 00:05:00 Choosing content marketing formats and channels 5.2 00:04:00 Source from anywhere 5.3 00:04:00 Making content very effective 5.4 00:04:00 Grow Content Operations Choosing a content calendar 6.1 00:04:00 Understand content processes 6.2 00:04:00 Clarifying roles and responsibilities 6.3 00:05:00 Content operations that come to life 6.4 00:03:00 Create Advanced Intelligence for Content Selecting content KPIs 7.1 00:05:00 Monitoring content KPI data 7.2 00:05:00 Optimizing content performance regularly 7.3 00:06:00 Using Content Technology by Constantly Renewing it Finding content technology 8.1 00:03:00 Considering advanced content technology 8.2 00:04:00 Developing strategy for content technology 8.3 00:03:00 Seize Content Marketing Opportunities Scaling Content Marketing 9.1 00:03:00 Succeeding as a Small Business 9.2 00:03:00 Succeed as a Large or Corporate Business 9.3 00:03:00 Creating a Social Media Roadmap Set Your Goals 1.1 00:05:00 Define Your Target Audience.1.2 00:05:00 Choosing the Most Successful Social Network Invest in Smart Channels 2.1 00:05:00 The Most Successful Social Networks 2.2 00:05:00 Social Networks for Message and Chat 2.3 00:05:00 Very Important Niche Social Networks 2.4 00:05:00 Great Social Media Posting Models How We Can Create Great Messages 3.1 00:05:00 Manage by Setting a Great Calendar 3.2 00:05:00 Managing Ads on Social Media 3.3 00:05:00 Effective Sustainable Communication With Customers Achieve Success with the Masses by Building Communities 4.1 00:05:00 Importance of Customer Service in Social Media 4.2 00:05:00 How Can We Turn Social Media Into Sales Strengthen Sales by Directly Supporting 5.1 00:05:00 Developing Business by Partnering with Influencers 5.2 00:04:00 Measuring Social Media in the Most Efficient Way Connecting Social Networks with Goals 6.1 00:05:00 Constantly Marketing the Best Improvements to Social Media More Than Being Active 7.1 00:05:00 Bring Great Apps to Life 7.2 00:05:00 How to Create Tribes On Social Media Understanding Community Management 1.1 00:03:00 Why Should We Build Our Own Community 1.2 00:07:00 Create Online Tribes How to Create your Great Strategy 2.1 00:10:00 Using Social Media to Build Your Community 2.2 00:09:00 Best Practices for Community Building 2.3 00:07:00 Growing Your Tribes On Social Media Creating Content Keeps Your Tribes Alive 3.1 00:10:00 How to Increase Active Participation in Your Communities 3.2 00:07:00 How to Find Brand Ambassadors and Influencers 3.3 00:07:00 How to Promote Your Community 3.4 00:08:00 Measuring their Success and Performance How to Scale Your Community 4.1mov 00:08:00 How to Measure the Growth of Your Fans 4.2 00:07:00 Demonstrate your Influence in Communities as a Leader 4.3 00:05:00 Tools for Managing Audience and Communities Very Good use of Tools for Community Management 5.1 00:04:00 Story Basics How Stories Connect 1.1 00:06:00 Story Types to Grow 1.2 00:07:00 Good Story Qualities 1.3 00:07:00 Building a Story Finding Your Story 2.1 00:05:00 Your Audience 2.2 00:04:00 Call to Action 2.3 00:06:00 Telling a Story Story Structure 3.1 00:06:00 Grabbing Attention 3.2 00:05:00 Deep Engagement 3.3 00:08:00 Growing Community 3.4 00:04:00 Interactive Stories 3.5 00:05:00 More More Material 4.1 00:03:00 Interview 4.2 00:03:00 Core Values 4.3 00:03:00 Connect Before Convincing 4.4 00:03:00 Crowdfunding 4.5 00:03:00 How to Start Your Story 4.6 00:03:00 Tell Stories in Person 4.7 00:03:00 Tell Stories in Person 4.7 00:03:00 Obtain Your Certificate Order Your Certificate of Achievement 00:00:00 Get Your Insurance Now Get Your Insurance Now 00:00:00 Feedback Feedback 00:00:00

Do you want to understand your dog's behaviour better, or are you looking to help them with any behavioural problems they may have? If so, then the Dog Behaviour Level 3 course is for you! From evolution and intelligence to communication and emotions, this course will teach you everything you need to know about dog behaviour. You'll also learn how to recognise and handle typical behavioural issues. This training bridges the gap between dogs and people by providing light on the emotional depth and signs of suffering in dogs. After completing the course, you can also pursue different career paths where the annual salary ranges from £22,000 to £60,000. As a dog owner or professional, it's crucial to correctly read these signs to guarantee the safety of your pet or the dogs you work with. Our Dog Behaviour Level 3 course provides you with the knowledge and abilities needed to work effectively with dogs, making it a valuable resource for any dog lover or professional in the canine sector. Equip yourself with a deep understanding of dogs that goes beyond basic commands. Whether you're a professional dog trainer, a dog owner, or a potential adopter, this course offers a thorough understanding of canine behaviour to ensure happier, healthier interactions. Enrol in the Dog Behaviour Level 3 course today and become fluent in the language of dogs! Learning Outcome Upon completion of the Dog Behaviour Level 3 course, you will be able to: Understand the evolution and intelligence of canines for better interaction. Grasp the significance of socialisation in dog behaviour. Decode canine communication and body language for improved understanding. Deepen your knowledge of canine psychology to predict behaviour. Master communication techniques between dogs and humans. Identify canine emotions and signs of suffering effectively. Gain essential skills to be a responsible and aware dog owner. Equip yourself for a career in the canine industry with professional dog-handling skills. Why buy this Dog Behaviour Level 3 course? Unlimited access to the course forever Digital Certificate, Transcript, and student ID are all included in the price Absolutely no hidden fees Directly receive CPD accredited qualifications after course completion Receive one-to-one assistance when needed Immediately receive the PDF certificate after passing Receive the original copies of your certificate and transcript immediately Easily learn the skills and knowledge from the comfort of your home Who is this course for? This Dog Behaviour Level 3 course is perfect for: Aspiring dog trainers seeking to deepen their professional knowledge. Dog owners looking to better understand and train their pets. Animal care workers aiming to enhance their dog handling skills. Individuals considering adopting or fostering a dog. Any dog lover interested in learning more about canine behaviour. Certification After studying the course materials of the Dog Behaviour Level 3 course, there will be a written assignment test which you can take either during or at the end of the course. After passing the test, you will have a range of certification options. A CPD Accredited PDF Certificate - £4.99 A CPD Accredited Hardcopy Certificate - £8.00. A PDF Transcript - £4.99 A Hardcopy Transcript - £9.99. Select according to your needs, and we assure timely delivery of your chosen certificate. Requirements This professionally designed Dog Behaviour Level 3 course does not require you to have any prior qualifications or experience. It is open to everyone, and you can access the course from anywhere at any time. Just enrol and start learning! Career Path Upon completion of the Dog Behaviour Level 3 course, you will be well-prepared to progress in a wide range of careers within the canine industry. The course prepares you for roles such as dog trainer, animal behaviourist, or pet care specialist. Furthermore, it can help those looking to start their own dog-related business, such as a pet sitting or dog walking service. Course Curriculum Module 01: Introduction to Canine Evolution Introduction to Canine Evolution 00:28:00 Module 02: Introduction to Canine Intelligence Introduction to Canine Intelligence 00:12:00 Module 03: The Importance of Socialisation The Importance of Socialisation 00:40:00 Module 04: Canine Communication Canine Communication 00:41:00 Module 05: Canine Psychology Canine Psychology 00:17:00 Module 06: Dog Communication and Body Language Dog Communication and Body Language 00:16:00 Module 07: Communication Between Dogs and Human Communication Between Dogs and Human 00:16:00 Module 08: Canine Emotions and Signs of Suffering Canine Emotions and Signs of Suffering 00:27:00 Module 09: The Role of a Dog Owner The Role of a Dog Owner 00:23:00 Module 10: Essential Skills for Working With Dogs Essential Skills for Working With Dogs 00:20:00 Assignment Assignment - Dog Behaviour Level 3 00:00:00

Gua Sha Massage For Massage Therapist
By NextGen Learning
Ignite your dynamic career and strengthen your deep insight knowledge by signing up for Massage Therapist Course. This Massage Therapist Course is the ideal approach for you to obtain a thorough understanding and knowledge of the subject. We are concerned about the progression of your career. Therefore, after conducting extensive studies and consulting with experienced personnel, we formulated this outstanding course to improve your pertinent skills. In this easy-to-digest Massage Therapist Course, you will get exclusive training, which will enable you to stand out in this competitive market. However, the Massage Therapist Course covers all of the recent materials in order to keep you up to date with the job market and make you a good fit for your career. This top-notch course curriculum comprises basic to advanced levels of modules that will increase your skillsets. After completing this Programme, you will attain the productivity to succeed in your organisation. So, if you are eager to see yourself in a gratifying career, then enrol in our course today! What will make you stand out? On completion of this online course, you will gain: CPD QS Accredited After successfully completing the Course, you will receive a FREE PDF Certificate as evidence of your newly acquired abilities. Lifetime access to the whole collection of learning materials. The online test with immediate results You can study and complete the course at your own pace. Study for the course using any internet-connected device, such as a computer, tablet, or mobile device. The substantial Massage Therapist Course is designed to help you demonstrate the preliminary to in-depth level of learning regarding this topic. Moreover, you will be provided with the most knowledgeable and informative modules for your lifetime by enrolling in this course just once. Furthermore, as you proceed through the modules of this course, you will discover the fundamentals of Massage Therapist Course and explore the key topics such as: Massage Therapist Course Introduction Introduction How To Do Gua Sha A look at my box of Gua Sha tools and what each is used for. Contraindications To Gua Sha How Often Should We Treat? Cleaning your Gua Sha instruments Gua Sha-Self Treatment What we are going to go through in this section Self-treating on the head area The Face-An all natural non-surgical facelift treatment Self-treating the chest area Self-treating the shoulder area Self-treating the arms Self-treatments for the hands Self-treating the mid and lower back area Stomach area Self-treating the legs Self-treating the feet Self-treating for good health Specific Treatments For Ailments What we are going to do in the section. The stress-relieving points Self-treating headaches and migraine Self-treatment for sinus headaches, hay fever and generally stuffy nose symptoms Self-treating Insomnia Coughs, colds, flus and respiratory problems Treating painful conditions using Gua Sha What you are going to learn in this section The above, through and below rule Neck pain Rotator cuff/Shoulder pain/Biceps pain/Arm pain Tennis Elbow/Elbow pain Self-treating carpal tunnel and wrist pain Self-treating lower back pain, hip and sciatica pain Self-treating ankle pain Congratulations! Therefore, reinforce your knowledge and furnish your skills by enrolling in our course. Take one step closer to achieving your goal. Show off your new skills with a certificate of completion Once you complete the Massage Therapist Course, you will be eligible to request a digital certificate for free. For Printed Transcript & Hardcopy Certificate- 4.99 GBP (Inside the UK Postal Fee) 8.99 GBP (International Delivery Fee) CPD 10 CPD hours / points Accredited by CPD Quality Standards Who is this course for? Is This Massage Therapist Course Course the Right Option for You? This course is recommended for anyone who is interested in learning more about this topic. You'll learn the fundamental ideas and gain a comprehensive understanding of the topic by taking this Massage Therapist Course. Requirements Without any formal requirements, you can delightfully enrol in this course. Career path The aim of this exclusive Massage Therapist Course is to help you toward your dream career. So, complete this course and enhance your skills to explore opportunities in relevant areas.
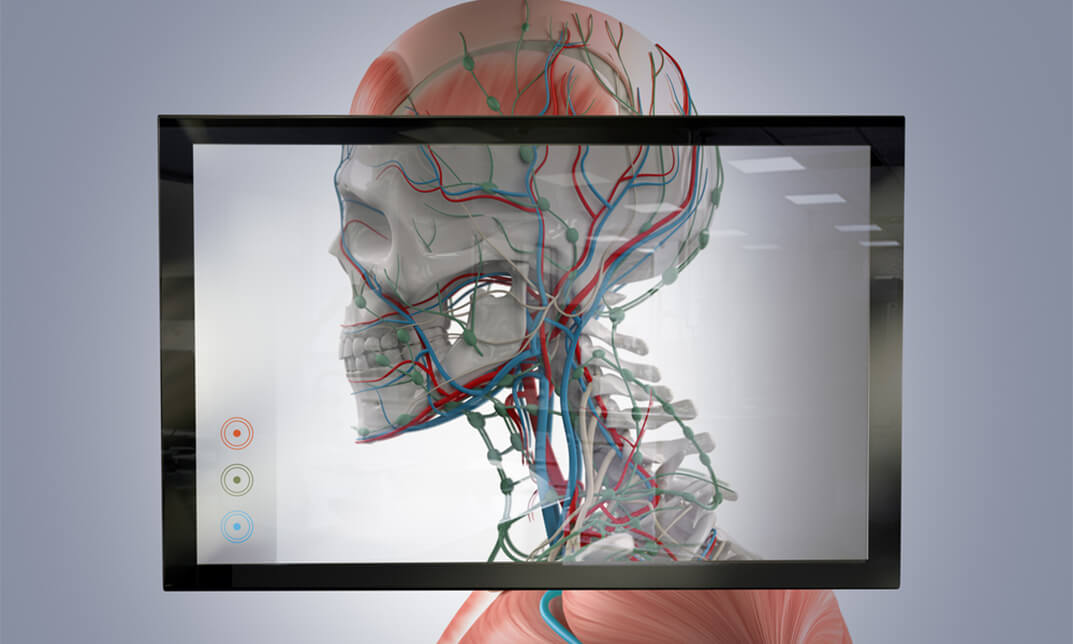
Overview Health careers are always in demand. And having sound knowledge of human anatomy and psychology is beneficial not only for healthcare jobs but also for your personal health. This Advanced Diploma in Anatomy and Physiology course will provide you with a comprehensive understanding of human anatomy and psychology. As a result, you can brace yourself with a promising career in the field of science. In this Advanced Diploma in Anatomy and Physiology course, you'll discover the theoretical and practical functionalities of the human body. The course will provide you with valuable insights into the major body systems and how they interact with each other. Furthermore, you'll get excellent information on the major levels of organisation in the body, such as molecules, cells, tissues and organs. By the end of the training, you will know how the human body develops and changes throughout life. Learning Outcomes Find a comprehensive overview of human psychology and anatomy Learn about the body systems and their functions Enrich your knowledge of the major level of organisations in the body Understand the chemical level of organisation Know the anatomy of the nervous system Determine the functions of the skeletal system Know the types of body movements Broaden your understanding of the cranial nerves Understand the anatomy of the heart Who is the Course for? This Advanced Diploma in Anatomy and Physiology course is suitable for anyone interested in understanding human anatomy and psychology. In addition, the training will open doors to various health career opportunities. Entry Requirement This course is available to all learners, of all academic backgrounds. Learners should be aged 16 or over to undertake the qualification. Good understanding of English language, numeracy, and ICT are required to attend this course. Assessment At the end of the course, you will be required to sit for an online multiple-choice test. Your test will be assessed automatically and immediately so that you will instantly know whether you have been successful. Before sitting for your final exam, you will have the opportunity to test your proficiency with a mock exam. Certification: After completing and passing the course successfully, you will be able to obtain an Accredited Certificate of Achievement. Certificates can be obtained either in hard copy at a cost of £39 or in PDF format at a cost of £24. Why Choose Us? Affordable, well-structured and high-quality e-learning study materials Engaging tutorial videos, materials from the industry-leading experts Opportunity to study in a user-friendly, advanced online learning platform Efficient exam systems for the assessment and instant result UK & internationally recognised accredited qualification Access the course content on mobile, tablet, or desktop from anywhere, anytime Excellent career advancement opportunities 24/7 student support via email. Career Path Advanced Diploma in Anatomy and Physiology Course provides useful skills to possess and would be beneficial for the following professionals: Medical laboratory technician. Physical therapist assistant. MRI technologist. Medical technologist Nurse. Personal trainer. Massage therapist Science teacher Updated Version-Advanced Diploma in Anatomy and Physiology Module 01: The Chemistry of Cells The Chemistry of Cells 00:27:00 Module 02: Cells Cells 00:16:00 Module 03: Cell Division Cell Division 00:19:00 Module 04: Replication and Metabolism Replication and Metabolism 00:20:00 Module 05: Human Tissues Human Tissues 00:25:00 Module 06: Skin Skin 00:16:00 Module 07: Human Skeletal System Human Skeletal System 00:21:00 Module 08: The Muscular System The Muscular System 00:17:00 Module 09: Skeletal Muscle Fibre Skeletal Muscle Fibre 00:23:00 Module 10: Nervous System Nervous System 00:31:00 Module 11: The Brain The Brain 00:25:00 Module 12: Nervous System-Spinal Cord and Spinal Nerves Nervous System-Spinal Cord and Spinal Nerves 00:15:00 Module 13: Nervous System - Autonomic Nervous System and Cranial Nerves Nervous System - Autonomic Nervous System and Cranial Nerves 00:21:00 Module 14: Nervous System-The Eyes Nervous System-The Eyes 00:15:00 Module 15: Nervous System-The Ears, Hearing, and Equilibrium Nervous System-The Ears, Hearing, and Equilibrium 00:14:00 Module 16: Nervous System-Memory Nervous System-Memory 00:19:00 Module 17: Sensory Systems Sensory Systems 00:23:00 Module 18: Cardiovascular System Cardiovascular System 00:25:00 Module 19: Blood Blood 00:27:00 Module 20: Lymphatics Lymphatics 00:20:00 Module 21: Immune System Immune System 00:26:00 Module 22: Digestive System Digestive System 00:22:00 Module 23: Respiratory System Respiratory System 00:19:00 Module 24: Urinary System Urinary System 00:16:00 Module 25: Male Reproductive System Male Reproductive System 00:31:00 Module 26: Female Reproductive System Female Reproductive System 00:31:00 Order Your Certificate Order Your Certificates and Transcripts 00:00:00 Old Version-Advanced Diploma in Anatomy and Physiology Introduction to the Human Body Overview of Anatomy and Physiology 00:20:00 Structural Organization of the Human Body 00:15:00 Functions of Human Life 00:15:00 Requirements for Human Life 00:15:00 Homeostasis 00:15:00 Anatomical Terminology 00:15:00 Medical Imaging 00:15:00 The Chemical Level Elements and Atoms: The Building Blocks of Matter 00:25:00 Chemical Bonds 00:25:00 Chemical Reactions 00:20:00 Inorganic Compounds Essential to Human Functioning 00:15:00 Organic Compounds Essential to Human Functioning 00:20:00 The Cellular Level The Cell Membrane 00:20:00 The Cytoplasm and Cellular Organelles 00:15:00 The Nucleus and DNA Replication 00:15:00 Protein Synthesis 00:15:00 Cell Growth and Division 00:20:00 Cellular Differentiation 00:10:00 The Tissue Level Types of Tissues 00:15:00 Epithelial Tissue 00:20:00 Muscle Tissue and Motion 00:05:00 Nervous Tissue Mediates Perception and Response 00:05:00 Tissue Injury and Aging 00:15:00 The Integumentary System Layers of the Skin 00:20:00 Accessory Structures of the Skin 00:15:00 Functions of the Integumentary System 00:10:00 Diseases, Disorders, and Injuries of the Integumentary System 00:15:00 Bone Tissue and the Skeletal System The Functions of the Skeletal System 00:10:00 Bone Classification 00:10:00 Bone Structure 00:20:00 Bone Formation and Development 00:10:00 Fractures: Bone Repair 00:05:00 Exercise, Nutrition, Hormones, and Bone Tissue 00:15:00 Calcium Homeostasis: Interactions of the Skeletal System and Other Organ Systems 00:10:00 Axial Skeleton Divisions of the Skeletal System 00:05:00 The Skull 00:45:00 The Vertebral Column 00:20:00 The Thoracic Cage 00:05:00 Embryonic Development of the Axial Skeleton 00:10:00 Joints Classification of Joints 00:10:00 Fibrous Joints 00:10:00 Cartilaginous Joints 00:05:00 Synovial Joints 00:20:00 Types of Body Movements 00:20:00 Anatomy of Selected Synovial Joints 00:25:00 Development of Joints 00:05:00 Muscle Tissue Introduction to Muscle Tissue 00:05:00 Skeletal Muscle 00:15:00 Muscle Fiber Contraction and Relaxation 00:20:00 Nervous System Control of Muscle Tension 00:20:00 Types of Muscle Fibers 00:05:00 Exercise and Muscle Performance 00:10:00 Cardiac Muscle Tissue 00:05:00 Smooth Muscle 00:15:00 Development and Regeneration of Muscle Tissue 00:05:00 The Muscular System Interactions of Skeletal Muscles, Their Fascicle Arrangement, and Their Lever Systems 00:10:00 Naming Skeletal Muscles 00:10:00 Axial Muscles of the Head, Neck, and Back 00:20:00 Axial Muscles of the Abdominal Wall and Thorax 00:25:00 Muscles of the Pectoral Girdle and Upper Limbs 00:30:00 Appendicular Muscles of the Pelvic Girdle and Lower Limbs 00:15:00 The Nervous System and Nervous Tissue Basic Structure and Function of the Nervous System 00:15:00 Nervous Tissue 00:15:00 The Function of Nervous Tissue 00:10:00 The Action Potential 00:15:00 Communication Between Neurons 00:15:00 Anatomy of the Nervous System The Embryologic Perspective 00:15:00 The Central Nervous System 00:25:00 Circulation and the Central Nervous System 00:15:00 The Peripheral Nervous System 00:15:00 The Brain and Cranial Nerves Sensory Perception 00:30:00 Central Processing 00:30:00 Motor Responses 00:15:00 The Autonomic Nervous System Divisions of the Autonomic Nervous System 00:15:00 Autonomic Reflexes and Homeostasis 00:20:00 Central Control 00:10:00 Drugs that Affect the Autonomic System 00:15:00 The Endocrine System Introduction to Endocrine System 00:05:00 Hormones 00:15:00 The Pituitary Gland and Hypothalamus 00:15:00 The Thyroid Gland 00:15:00 The Parathyroid Glands 00:05:00 The Adrenal Glands 00:10:00 Gonadal and Placental Hormones 00:05:00 The Endocrine Pancreas 00:10:00 Organs with Secondary Endocrine Functions 00:05:00 Development and Aging of the Endocrine System 00:10:00 The Cardiovascular System: Blood Overview of Blood 00:20:00 Production of the Formed Elements 00:10:00 Erythrocytes 00:30:00 Leukocytes and Platelets 00:15:00 Hemostasis 00:20:00 Blood Typing 00:10:00 The Cardiovascular System: The Heart Heart Anatomy 00:50:00 Cardiac Muscle and Electrical Activity 00:30:00 Cardiac Cycle 00:20:00 Cardiac Physiology 00:20:00 Development of the Heart 00:10:00 Mock Exam Mock Exam - Advanced Diploma in Anatomy and Physiology 00:20:00 Final Exam Final Exam - Advanced Diploma in Anatomy and Physiology 00:20:00 Order Your Certificates and Transcripts Order Your Certificates and Transcripts 00:00:00
Explore the essence of Good Manufacturing Practice (GMP) and its pivotal role in ensuring the quality, safety, and consistency of pharmaceuticals, food, and other regulated products. Learn the principles, regulations, and best practices that guide GMP standards, fostering trust and integrity in the manufacturing process. Elevate your understanding of GMP compliance for a seamless journey from production to market, prioritizing consumer well-being and industry excellence.

Food Safety in Health and Social Care and Early Years and Childcare Settings
By Training Tale
The purpose of this Food Safety in Health and Social Care and Early Years and Childcare Settings qualification is to help learners develop the knowledge and skills needed to work with food in health and social care settings, as well as in early years and childcare settings. The Food Safety in Health and Social Care and Early Years and Childcare Settings course includes food safety requirements, contributes to and/or promotes nutrition and hydration, and assists individuals in eating and drinking. This Food Safety in Health and Social Care and Early Years and Childcare Settings course will also assist learners in gaining an understanding of food safety in preparation for food hygiene qualifications. Learning Outcomes After completing this Food Safety in Health and Social Care and Early Years and Childcare Settings course, the learner will be able to: Gain a solid understanding of the importance of food safety measures when providing food and drink for individuals. Understand how to maintain hygiene when handling food and drink. Understand how to meet safety requirements when preparing and serving food and drink to individuals. Understand the safety requirements when clearing away food and drink. Gain a thorough understanding of how to store food and drink safely. Understand how to access additional advice or support about food safety. Why Choose Food Safety in Health and Social Care and Early Years and Childcare Settings Course from Us Self-paced course, access available from anywhere. Easy to understand, high-quality study materials. This course developed by industry experts. MCQ quiz after each module to assess your learning. Automated and instant assessment results. 24/7 support via live chat, phone call or email. Free PDF certificate as soon as completing the course. ***Courses are included in this Food Safety in Health and Social Care and Early Years and Childcare Settings Bundle Course*** Course 01: Food Safety in Health and Social Care and Early Years and Childcare Settings Course 02: Level 5 Nutritional Therapy Course Course 03: Mental Health Support Worker ***Other Benefits of this Course*** Free 3 PDF Certificate Access to Content - Lifetime Exam Fee - Totally Free Free Retake Exam [ Note: Free PDF certificate as soon as completing the Food Safety in Health and Social Care and Early Years and Childcare Settings course] Detailed course curriculum of *** Food Safety in Health and Social Care and Early Years and Childcare Settings *** Module 1: Principles of Food Safety When Providing Food and Drink for Individuals Understand the importance of food safety measures when providing food and drink for individuals Know how to maintain hygiene when handling food and drink Know how to meet safety requirements when preparing and serving food and drink for individuals Know the safety requirements when clearing away food and drink Know how to store food and drink safely Know how to access additional advice or support about food safety -------------------- Assessment Method After completing each module of the Food Safety in Health and Social Care and Early Years and Childcare Settings Course, you will find automated MCQ quizzes. To unlock the next module, you need to complete the quiz task and get at least 60% marks. Certification After completing the MCQ/Assignment assessment for this Food Safety in Health and Social Care and Early Years and Childcare Settings course, you will be entitled to a Certificate of Completion from Training Tale. The certificate is in PDF format, which is completely free to download. A printed version is also available upon request. It will also be sent to you through a courier for £13.99. Who is this course for? This Food Safety in Health and Social Care and Early Years and Childcare Settings course is ideal for anyone preparing for a new role or working in a role that involves handling food safely and supporting an individual with their nutrition and hydration needs. Requirements There are no specific requirements for this Food Safety in Health and Social Care and Early Years and Childcare Settings course because it does not require any advanced knowledge or skills. Certificates Certificate of completion Digital certificate - Included

Language and Speech Therapy - CPD Certified
By Training Tale
Language and Speech Therapy: Language and Speech Therapy Course This exclusive Language and Speech Therapy: Language and Speech Therapy Course provides learners with a comprehensive overview of the role of a Speech and Language Therapist, equipping you with the essential skills to advance your career. It includes speech science, speech anatomy, and the characteristics of speech in detail. This Language and Speech Therapy: Language and Speech Therapy Course will teach you how Speech and Language Therapists help children and adults with speech and language disorders, including swallowing, eating, and drinking issues. It covers the fundamentals of the speech chain model and walks you through the key stages of literacy and language development. This Language and Speech Therapy: Language and Speech Therapy Course includes case studies and practical exercises that will teach you how to assess your clients' needs, set long-term goals, and support them every step of the way to recovery using a variety of communication techniques. In addition, you will gain in-demand professional skills that will help you start your career successfully. Special Offers of this Language and Speech Therapy: Language and Speech Therapy Course This Language and Speech Therapy: Language and Speech Therapy Course includes a FREE PDF Certificate. Lifetime access to this Language and Speech Therapy: Language and Speech Therapy Course Instant access to this Language and Speech Therapy: Language and Speech Therapy Course Get FREE Tutor Support from Monday to Friday in this Language and Speech Therapy: Language and Speech Therapy Course Main Course: Language and Speech Therapy Course Courses are Included in this Language and Speech Therapy: Language and Speech Therapy Course: Course 01: ADHD Awareness Course 02: Autism Diploma Course 03: Dyslexia [ Note: Free PDF certificate as soon as completing the Language and Speech Therapy: Language and Speech Therapy Course] Language and Speech Therapy: Language and Speech Therapy Course Industry Experts Designed this Language and Speech Therapy: Language and Speech Therapy Course into 04 detailed modules. Course curriculum Language and Speech Therapy Module 1: Speech & Language Therapy Module 2: Study of Communication Module 3: Components of Normal Speech, Language & Voice and Communication Disorders Module 4: Eating, Drinking and Swallowing Disorders Assessment Method of Language and Speech Therapy Course After completing each module of the Language and Speech Therapy: Language and Speech Therapy Course, you will find automated MCQ quizzes. To unlock the next module, you need to complete the quiz task and get at least 60% marks. Certification of Language and Speech Therapy Course After completing the MCQ/Assignment assessment for this Language and Speech Therapy: Language and Speech Therapy Course, you will be entitled to a Certificate of Completion from Training Tale. The certificate is in PDF format, which is completely free to download. A printed version is also available upon request. It will also be sent to you through a courier for £13.99. Who is this course for? Language and Speech Therapy: Language and Speech Therapy Course This Language and Speech Therapy: Language and Speech Therapy Course is for anyone who wants to: Gain the skills needed to work in the teaching and child care profession. Improve their speech therapy and language therapy skills. Make a career change and explore new career opportunities. Gain a formal, accredited qualification to improve their career opportunities. Requirements Language and Speech Therapy: Language and Speech Therapy Course Students who intend to enrol in this Language and Speech Therapy: Language and Speech Therapy Course must meet the following requirements: Language and Speech Therapy: Good command of the English language Language and Speech Therapy: Must be vivacious and self-driven. Language and Speech Therapy: Basic computer knowledge Language and Speech Therapy: A minimum of 16 years of age is required. Career path Language and Speech Therapy: Language and Speech Therapy Course Compete High provides the most expedient path to learning about Language and Speech Therapy: Language and Speech Therapy Course, as well as the opportunity to practice your skills in a corporate setting. Certificates Certificate of completion Digital certificate - Included

Search By Location
- training, Courses in London
- training, Courses in Birmingham
- training, Courses in Glasgow
- training, Courses in Liverpool
- training, Courses in Bristol
- training, Courses in Manchester
- training, Courses in Sheffield
- training, Courses in Leeds
- training, Courses in Edinburgh
- training, Courses in Leicester
- training, Courses in Coventry
- training, Courses in Bradford
- training, Courses in Cardiff
- training, Courses in Belfast
- training, Courses in Nottingham