- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1081 Courses
How to Conduct and Write Systematic Literature Reviews
By Research'Kraft Consulting
Workshop objectives 1-Introduction to Systematic Reviews 2- Formulating the Research Question 3- Developing a Protocol 4- Literature Search 5- Study Selection 6- Data Extraction 7- Quality Assessment: 8- Data Synthesis 9- Reporting and Publication: 10- How to write a scoping review A certificate from Research'Kraft will be given after successful completion.

18th edition course Bromley
By MJ Electrical Training
City & Guilds 18th edition course with 2382-22 final exam only £234.00. Exams available every week across the UK, same day results, quick certificate, best prices..

Mental Health and Learning Disability
By BBO Training
Introduction to Mental Health and Learning Disability in Primary Care (2-Day Course)This course is designed for Nurse Associates, Practice Nurses, Nurse Practitioners (NP's), Emergency Nurse Practitioners (ENP's), Paramedics, and Pharmacists who aim to enhance their knowledge and skills in mental health and learning disability care within the primary care setting.Day 1: Mental HealthLearning Objectives:1. Understand the concept of mental health and its importance in overall well-being.2. Identify common mental health disorders, their signs, symptoms, and risk factors.3. Explore different approaches to mental health assessment and diagnosis.4. Learn evidence-based interventions for various mental health conditions.5. Develop effective communication skills when interacting with individuals experiencing mental health challenges.6. Gain knowledge of available resources and support systems for mental health.Introduction to Performing Annual Reviews for Mental Health Patients:- Understand the significance of performing annual reviews for individuals with mental health conditions.- Explore the assessment tools and methods required for annual reviews in mental health.- Begin to develop skills in conducting annual reviews for mental health patients.Day 2: Learning DisabilitiesLearning Objectives:1. Define learning disabilities and recognize their impact on individuals' lives.2. Identify common types of learning disabilities, their characteristics, and associated challenges.3. Understand the importance of early detection and screening for learning disabilities.4. Learn strategies for supporting individuals with learning disabilities in various settings.5. Explore the rights and legislation related to individuals with learning disabilities.6. Enhance communication and collaboration skills when working with individuals with learning disabilities.Introduction to Performing Annual Reviews for Learning Disability Patients:- Understand the significance of performing annual reviews for individuals with learning disabilities.- Learn the specific assessment tools and methods required for annual reviews in learning disabilities.- Begin to develop skills in conducting annual reviews for learning disability patients.Join us for this informative and interactive 2-day course via Zoom, led by Dr. Tamara Cunningham, and equip yourself with the knowledge and skills necessary to provide comprehensive care for individuals with mental health and learning disability conditions in a primary care setting.

Penetration testing training course description An advanced technical hands on course focusing on hacking and counter hacking. The course revolves around a series of exercises based on "hacking" into a network (pen testing the network) and then defending against the hacks. What will you learn Perform penetration tests. Explain the technical workings of various penetration tests. Produce reports on results of penetration tests. Defend against hackers. Penetration testing training course details Who will benefit: Technical support staff, auditors and security professionals. Staff who are responsible for network infrastructure integrity. Prerequisites: IP Security IP VPNs Duration 5 days Penetration testing training course contents Introduction Hacking concepts, phases, types of attacks, 'White hacking', What is penetration testing? Why use pen testing, black box vs. white box testing, equipment and tools, security lifecycles, counter hacking, pen testing reports, methodologies, legal issues. Physical security and social engineering Testing access controls, perimeter reviews, location reviews, alarm response testing. Request testing, guided suggestions, trust testing. Social engineering concepts, techniques, counter measures, Identity theft, Impersonation on social media, Footprints through social engineering Reconnaissance (discovery) Footprinting methodologies, concepts, threats and countermeasures, WHOIS footprinting, Gaining contacts and addresses, DNS queries, NIC queries, ICMP ping sweeping, system and server trails from the target network, information leaks, competitive intelligence. Scanning pen testing. Gaining access Getting past passwords, password grinding, spoofed tokens, replays, remaining anonymous. Scanning (enumeration) Gaining OS info, platform info, open port info, application info. Routes used, proxies, firewalking, Port scanning, stealth port scanning, vulnerability scanning, FIN scanning, Xmas tree scanning, Null scanning, spoofed scanning, Scanning beyond IDS. Enumeration concepts, counter measures and enumeration pen testing. Hacking Hacking webservers, web applications, Wireless networks and mobile platforms. Concepts, threats, methodology, hacking tools and countermeasures. Trojan, Backdoors, Sniffers, Viruses and Worms Detection, concepts, countermeasures, Pen testing Trojans, backdoors, sniffers and viruses. MAC attacks, DHCP attacks, ARP poisoning, DNS poisoning Anti-Trojan software, Malware analysis Sniffing tools. Exploiting (testing) vulnerabilities Buffer overflows,, simple exploits, brute force methods, UNIX based, Windows based, specific application vulnerabilities. DoS/DDoS Concepts, techniques, attack tools, Botnet, countermeasures, protection tools, DoS attack pen testing. SQL Injection Types and testing, Blind SQL Injection, Injection tools, evasion and countermeasures. Securing networks 'Hurdles', firewalls, DMZ, stopping port scans, IDS, Honeypots, Router testing, firewall testing, IDS testing, Buffer Overflow. Cryptography PKI, Encryption algorithms, tools, Email and Disk Encryption. Information security Document grinding, privacy.

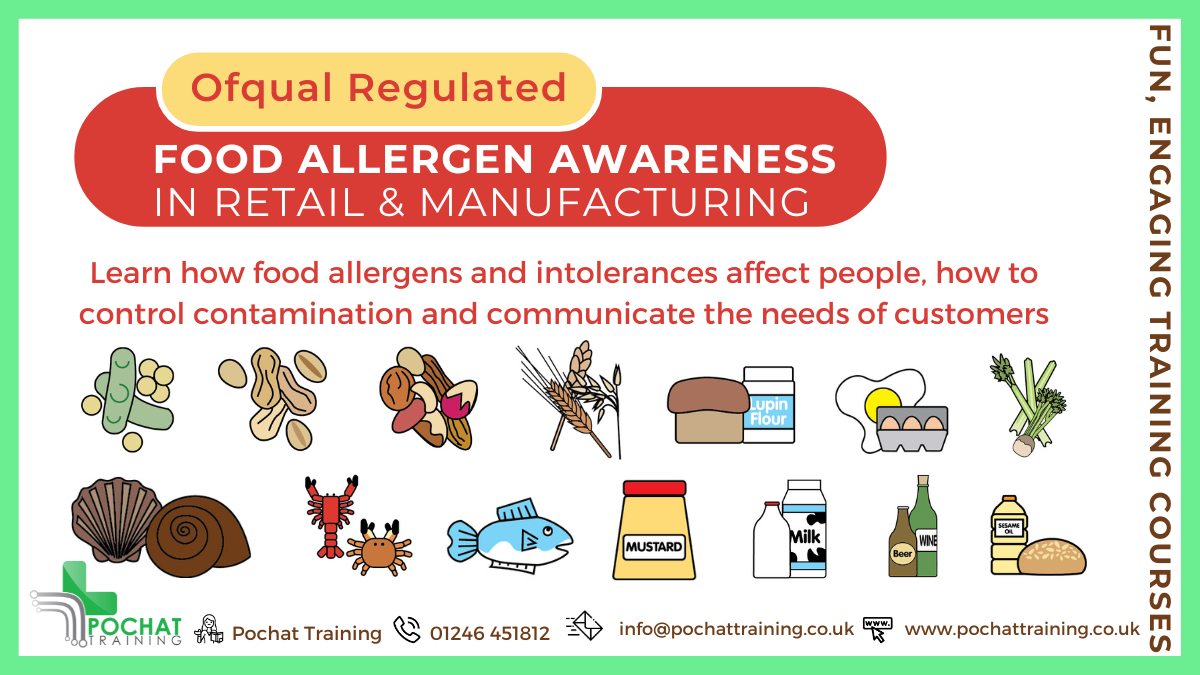
Qualsafe Food Allergen Awareness (RQF) Half day course This course gives learners the knowledge and understanding of food allergens and foods that commonly cause intolerances Teaches how to minimise the risk of cross-contamination from allergenic ingredients Benefits of this course: This qualification is aimed at food handlers and other staff involved in food preparation and services It provides knowledge and understanding of food allergens and foods that commonly cause intolerances Many people are allergic to foods, or have a food intolerance There is a duty in law for food handlers to ensure these people do not come to harm, either by going into anaphylactic shock and their potential death, or by making them feel really ill for a long period after consuming the food. Course Contents: The characteristics and consequences of food allergies and intolerances How to identify and control contamination from allergenic ingredients Ways to accurate communicate of allergen information to consumers Accredited, Ofqual regulated qualification: This Food Allergen Awareness training course is a nationally recognised, Ofqual regulated qualifications accredited by Qualsafe Awards. This means that you can be rest assured that your Food Allergen Awareness Certificate provides information for best practice to make a real difference to the lives of people who suffer from food allergies or intolerances. It also helps to stay on the right side of the law! The Ofqual Register number for this course is 610/0114/8 Classroom £95.00 pp Enquire about this course Half day course This course gives learners the knowledge and understanding of food allergens and food intolerances Teaches how to minimise the risk of cross-contamination from allergenic ingredients Enquire about this courseCourse ContentsUpcoming Dates Face to Face / Classroom Courses Would you like this course? Contact us and we'll set a date. We also run short, CPD Accredited training sessions in Food Allergens and Intolerances. Enquire about this courseCourse Contents Benefits of this course: This qualification is aimed at those who are working in, or preparing to work in a food handling, food retail or food manufacturing role It provides knowledge and understanding of food allergens and intolerances Many people are allergic to foods, or have a food intolerance There is a duty in law for food handlers to ensure these people do not come to harm, either by going into anaphylactic shock and their potential death, or by making them feel really ill for a long period after consuming the food. This is an Ofqual regulated qualification, showing your due diligence and care for your customers Enquire about this course Course Contents The characteristics of food allergens, food intolerance and coeliac disease The importance of, and procedures for identifying and controlling food allergen risks How to provide accurate food allergen information Enquire about this course Our Reviews Facebook 5.0 Rating READ FACEBOOK REVIEWS "Informative and very enjoyable!" Google Reviews 5.0 Rating READ GOOGLE REVIEWS Accredited, Ofqual regulated qualification This Food Allergen Awareness training course is a nationally recognised, Ofqual regulated qualifications accredited by Qualsafe Awards. This means that you can be rest assured that your Food Allergen Awareness Certificate provides information for best practice to make a real difference to the lives of people who suffer from food allergies or intolerances. It also helps to stay on the right side of the law! The Ofqual Register number for this course is 610/0114/8
This course examines the ability to plan and control the allocation of work within team members in order to maximise resources. Good delegation is based on clear objectives, regular reviews and sound feedback. It shows how delegation can provide a sound basis on which to improve productivity, engender ownership and responsibility whilst fostering individual growth and development.

Scrum Product Owner Workshop
By IIL Europe Ltd
Scrum Product Owner Workshop The Product Owner is responsible for maximizing the value of the product and the work of the Development Team. The Product Owner must be knowledgeable, available, and empowered to make decisions quickly in order for an Agile project to be successful. The Product Owner's key accountability is the Product Backlog. Managing, maintaining, and evolving the Product Backlog involves: Establishing a clear Vision that engages the Development Team and stakeholders Clearly expressing Product Backlog items Ordering the items in the Product Backlog to best achieve the Vision and goals Ensuring that the Product Backlog is visible, transparent, and clear to all Working with the Development Team throughout the project to create a product that fits the customer's needs The overall course goal is to support you in becoming an effective Product Owner. What you will Learn You'll learn how to: Differentiate between poor, good, and great Product Owner attributes, and their impact on the team, product, stakeholders, and the organization Engage your stakeholders by knowing your customers and market Develop an effective and value-driven Product Backlog Evaluate the Product Owner's role in Scrum's 5 events and team engagement Foundation Concepts Agile foundation Product owner role Product Ownership Product ownership Project vision Understanding your customers and market Personas Stakeholder management and engagement The Product Backlog Epics and user stories Preparing user stories for a sprint The product backlog Visualizing the product backlog Product backlog prioritization Technical debt Sprint Planning and Delivery Sprint planning The sprint Sprint Reviews, Retrospectives, and Closing Sprint reviews Key agile patterns Retrospectives Closing the project

Scrum Product Owner Workshop: In-House Training
By IIL Europe Ltd
Scrum Product Owner Workshop: In-House Training The Product Owner is responsible for maximizing the value of the product and the work of the Development Team. The Product Owner must be knowledgeable, available, and empowered to make decisions quickly in order for an Agile project to be successful. The Product Owner's key accountability is the Product Backlog. Managing, maintaining, and evolving the Product Backlog involves: Establishing a clear Vision that engages the Development Team and stakeholders Clearly expressing Product Backlog items Ordering the items in the Product Backlog to best achieve the Vision and goals Ensuring that the Product Backlog is visible, transparent, and clear to all Working with the Development Team throughout the project to create a product that fits the customer's needs The overall course goal is to support you in becoming an effective Product Owner. What you will Learn You'll learn how to: Differentiate between poor, good, and great Product Owner attributes, and their impact on the team, product, stakeholders, and the organization Engage your stakeholders by knowing your customers and market Develop an effective and value-driven Product Backlog Evaluate the Product Owner's role in Scrum's 5 events and team engagement Foundation Concepts Agile foundation Product owner role Product Ownership Product ownership Project vision Understanding your customers and market Personas Stakeholder management and engagement The Product Backlog Epics and user stories Preparing user stories for a sprint The product backlog Visualizing the product backlog Product backlog prioritization Technical debt Sprint Planning and Delivery Sprint planning The sprint Sprint Reviews, Retrospectives, and Closing Sprint reviews Key agile patterns Retrospectives Closing the project

Portfolio Management for Stakeholders: In-House Training
By IIL Europe Ltd
Portfolio Management for Stakeholders: In-House Training This course equips and enables project, program, and functional managers (line managers) to support and contribute to starting, restarting or sustaining the implementation and effectiveness of portfolio management in an organization. Emphasis is on improving collaboration and planning between functional business areas and project/program organizations responsible for delivering investments in business change through successful delivery of projects and programs. Good functional, project, and program managers become 'great' when they understand, advocate, and effectively contribute to achieving 'real' business value through portfolio management. What you Will Learn At the end of this program, you will be able to: Outline the benefits of portfolio management State the importance of linking the strategic objectives to the initiatives in the organization Chart the portfolio governance structure Assist in the inventory of ongoing and new initiatives Identify portfolio and sub-portfolio categories Support the PMO in the prioritization of initiatives using Multi-criteria Analysis and other selection tools Collaborate with the PMO in balancing the portfolio based on the optimal use of resources and priorities Participate in resource forecasting and planning Demonstrate thresholds and variance reporting criteria Describe the purpose of Stage Gate Funding Report status against a portfolio delivery plan Present your initiative in Stage Gate Reviews List the benefits that are being realized by the initiative Foundation Concepts Portfolio Life Cycles Portfolio Governance Prioritizing Initiatives Prioritize Foundation Multi-Criteria Analysis Analytical Hierarchy Process (AHP) Strategic Alignment Balancing the Portfolio Resources, Budgets, and Equipment Communicating Decisions Planning the Portfolio Planning Review Cycles Using Stage Gate Funding Setting Thresholds and Variance Reporting Tool Examples Portfolio Delivery 'Cycle' Project and Program Life Cycles Stage Gate Reviews Interaction with the Portfolio Delivery Board Project, Program, and Functional Managers Roles and Responsibilities

Portfolio Management for Stakeholders
By IIL Europe Ltd
Portfolio Management for Stakeholders This course equips and enables project, program, and functional managers (line managers) to support and contribute to starting, restarting or sustaining the implementation and effectiveness of portfolio management in an organization. Emphasis is on improving collaboration and planning between functional business areas and project/program organizations responsible for delivering investments in business change through successful delivery of projects and programs. Good functional, project, and program managers become 'great' when they understand, advocate, and effectively contribute to achieving 'real' business value through portfolio management. What you Will Learn At the end of this program, you will be able to: Outline the benefits of portfolio management State the importance of linking the strategic objectives to the initiatives in the organization Chart the portfolio governance structure Assist in the inventory of ongoing and new initiatives Identify portfolio and sub-portfolio categories Support the PMO in the prioritization of initiatives using Multi-criteria Analysis and other selection tools Collaborate with the PMO in balancing the portfolio based on the optimal use of resources and priorities Participate in resource forecasting and planning Demonstrate thresholds and variance reporting criteria Describe the purpose of Stage Gate Funding Report status against a portfolio delivery plan Present your initiative in Stage Gate Reviews List the benefits that are being realized by the initiative Foundation Concepts Portfolio Life Cycles Portfolio Governance Prioritizing Initiatives Prioritize Foundation Multi-Criteria Analysis Analytical Hierarchy Process (AHP) Strategic Alignment Balancing the Portfolio Resources, Budgets, and Equipment Communicating Decisions Planning the Portfolio Planning Review Cycles Using Stage Gate Funding Setting Thresholds and Variance Reporting Tool Examples Portfolio Delivery 'Cycle' Project and Program Life Cycles Stage Gate Reviews Interaction with the Portfolio Delivery Board Project, Program, and Functional Managers Roles and Responsibilities

Search By Location
- Reviews Courses in London
- Reviews Courses in Birmingham
- Reviews Courses in Glasgow
- Reviews Courses in Liverpool
- Reviews Courses in Bristol
- Reviews Courses in Manchester
- Reviews Courses in Sheffield
- Reviews Courses in Leeds
- Reviews Courses in Edinburgh
- Reviews Courses in Leicester
- Reviews Courses in Coventry
- Reviews Courses in Bradford
- Reviews Courses in Cardiff
- Reviews Courses in Belfast
- Reviews Courses in Nottingham