- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
1130 Courses
Managing Stress and Building Resilience: Virtual In-House Training
By IIL Europe Ltd
Managing Stress and Building Resilience: Virtual In-House Training Stress has an impact on all of us at some point in our professional lives. Learning how to manage stress and build resilience will result in higher professional productivity, better health, and more sustainable living habits. It will also help us create a physical - and emotional - work-life balance. In this one-day workshop, you will learn practical solutions to sustain behavior change that can positively impact your life on both a professional and personal level. When you are able to reduce the level of negative stress that affects you, your performance improves, along with your health and happiness. The objective of this course is therefore not only to create awareness around emotional well-being in a work context, but also to help participants create a better overall balance between the investment they make in their personal and professional lives. This course covers how our perceptions affect our beliefs and how our beliefs affect our actions. You will learn a host of stress-reduction techniques, while exploring your own stress triggers and responses. Highly interactive, the sessions cover a blend of theory, discussions, and exercises. You will explore concepts with fellow participants within a safe environment where skills and habits can be developed, sharpened, and improved. What You Will Learn At the end of this program, you will be able to: Identify what stress feels like and what the typical symptoms and reactions are to stress Analyze your own responses to stressful events and the consequences of those reactions Organize your work structure to reduce stress and build resilience Recognize activities that drain you and those that give you energy Generate relief from stressful events Cultivate a mindset of resilience Better manage your time, work commitments, and personal boundaries in order to be most effective at your job Getting Started What is stress? Beliefs and thinking errors Work-life balance Drainers and energizers Stress reduction techniques Time management Summary and Next Steps

Managing Stress and Building Resilience: In-House Training
By IIL Europe Ltd
Managing Stress and Building Resilience: In-House Training Stress has an impact on all of us at some point in our professional lives. Learning how to manage stress and build resilience will result in higher professional productivity, better health, and more sustainable living habits. It will also help us create a physical - and emotional - work-life balance. In this one-day workshop, you will learn practical solutions to sustain behavior change that can positively impact your life on both a professional and personal level. When you are able to reduce the level of negative stress that affects you, your performance improves, along with your health and happiness. The objective of this course is therefore not only to create awareness around emotional well-being in a work context, but also to help participants create a better overall balance between the investment they make in their personal and professional lives. This course covers how our perceptions affect our beliefs and how our beliefs affect our actions. You will learn a host of stress-reduction techniques, while exploring your own stress triggers and responses. Highly interactive, the sessions cover a blend of theory, discussions, and exercises. You will explore concepts with fellow participants within a safe environment where skills and habits can be developed, sharpened, and improved. What You Will Learn At the end of this program, you will be able to: Identify what stress feels like and what the typical symptoms and reactions are to stress Analyze your own responses to stressful events and the consequences of those reactions Organize your work structure to reduce stress and build resilience Recognize activities that drain you and those that give you energy Generate relief from stressful events Cultivate a mindset of resilience Better manage your time, work commitments, and personal boundaries in order to be most effective at your job Getting Started What is stress? Beliefs and thinking errors Work-life balance Drainers and energizers Stress reduction techniques Time management Summary and Next Steps

Pasta From Scratch
By Personal Chef Edinburgh
Discover the secrets of the Italian pasta with this online cooking class. Learn how to make pasta according to tradition without the pasta machine.

Podcasting Essentials
By iStudy UK
Description Would you like to start and host your podcast show? This course will explain exactly what you need to do to start your own podcast show! We look at what equipment to get, what software to use, recording your show, show format, editing your podcasts, choosing music, legal issues, your hosting options, how to upload and submit your podcast to itunes and the best directories out there and how to monetise and market your show. We start right from the very beginning. No previous experience of any of the above is assumed. We look at what a podcast is, the history of podcasting, the benefits of getting into podcasting and how to do it. Every step of the way is broken down. We don't just 'tell' you, we show you. The videos are clear, step by step, right from your podcast idea right up until submission and promoting your show. Podcasting is an amazing way to promote your brand and for you to promote yourself and become a leading authority in your chosen niche. There are far more blogs on the internet then they are podcasts. As a marketing medium and a direct channel of communication to your target audience, in terms of price comparison, and effectiveness of audience attention - very little measures up to a podcast! You have the undivided attention of your listener, they subscribe to your show, you have the opportunity to literally 'talk' to them ... what other medium or method can compare to this? A podcast can open new doors and opportunities unlike any other. This course looks at the most cost effective methods to achieve a podcast - your host has done all of the legwork and research for you. Save yourself a lot of time effort and energy by taking this course and learning exactly what to do and let us walk you through it. You don't need expensive editing equipment. You don't need to be in a recording studio and you don't need to spend a small fortune on voice over recording artists. You can can start your own podcast show this week (literally) with exactly what you have right now. We do look at different microphones on the market, and we look at which one to go for. We completely demystify and break down the process. If you want to start your own podcast show - this course will show you exactly what to do.... step-by-step. There is an extensive editing section - so you know how to edit your podcast and we look at the various means of monetising your work. Your course tutor is the host of The Authors Podcast which can be found on iTunes and she shows you step-by-step how to host your show, upload your show, name your show, edit your show and submit your show for acceptance. Progressive people, self-starters, those who want to get somewhere in life - achievers! Who is the target audience? Interested in starting your own podcast show What Will I Learn? Start your own podcast show Record and edit your own podcast Submit your podcast show to itunes and other directories Ways to market and promote your show Requirements No prerequisites Introduction to the course and your tutor Introduction to the course FREE 00:05:00 A brief history FREE 00:09:00 Why do you want to start a podcast? 00:18:00 Preparing for your podcast 00:06:00 Preparation 00:14:00 Equipment needed 00:19:00 Microphones 00:14:00 Software to edit your podcast 00:09:00 How to prepare 00:11:00 Editing your podcast How to create an interlude with music 00:14:00 Editing a podcast with Audacity - part 1 00:17:00 Editing a podcast with Audacity - part 2 00:16:00 Inserting an interlude 00:10:00 More editing to finish - part 1 00:15:00 More editing to finish - part 2 00:17:00 Ending the podcast - adding an outro 00:08:00 Editing 00:02:00 Editing masterclass tips 00:13:00 Replacing one interlude with another 00:14:00 Legal issues 00:06:00 Publishing your podcast How to publish 00:13:00 Join the podbean affiliate program 00:06:00 Why podbean? 00:05:00 Publish a podcast on podbean 00:11:00 Publishing - part 1 00:18:00 Publishing - part 2 00:17:00 Unmuting a file on audacity 00:03:00 Podbean - final publishing 00:19:00 Downloading itunes 00:03:00 Installing itunes and logging in 00:02:00 Testing your feed 00:07:00 Validate your feed 00:12:00 Itunes store submission 00:10:00 Marketing Directories 00:09:00 Itunes accepted and social media promotion 00:19:00 Stitcher and other submissions 00:24:00 Marketing tips 00:06:00 Show Me The Money! Podcasting Tips 00:05:00 Monetizing Your Podcast 00:16:00 Budget 00:06:00 Conclusion and Next Steps Conclusion and Next Steps 00:04:00

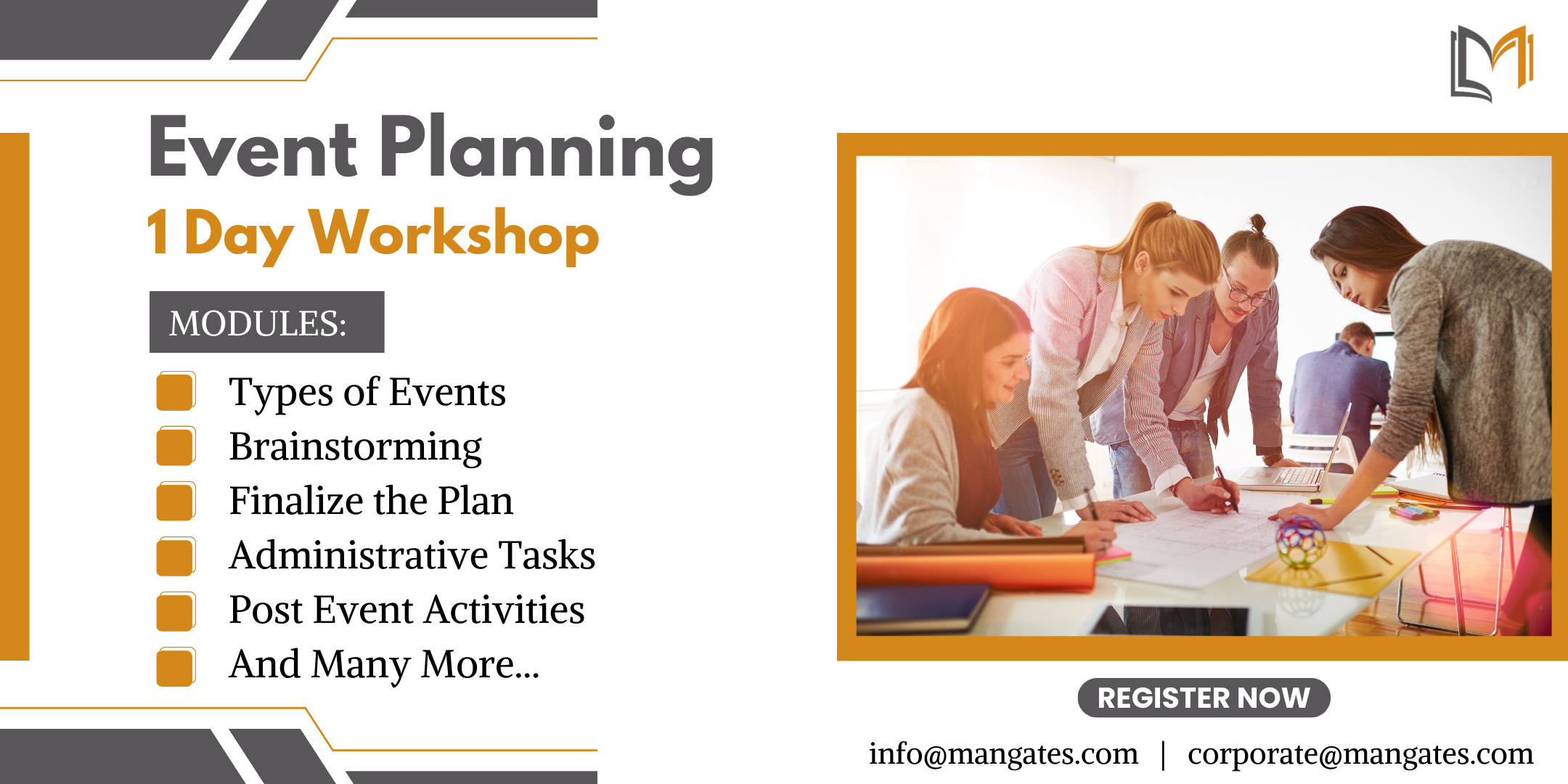
The Ultimate Guide to Event Planning - 1 Day Workshop in Bolton
By Mangates
Event Planning 1 Day Training in Bolton
AZ-801T00 Configuring Windows Server Hybrid Advanced Services
By Nexus Human
Duration 4 Days 24 CPD hours This course is intended for This four-day course is intended for Windows Server Hybrid Administrators who have experience working with Windows Server and want to extend the capabilities of their on-premises environments by combining on-premises and hybrid technologies. Windows Server Hybrid Administrators who already implement and manage on-premises core technologies want to secure and protect their environments, migrate virtual and physical workloads to Azure Iaas, enable a highly available, fully redundant environment, and perform monitoring and troubleshooting. This course teaches IT Professionals to configure advanced Windows Server services using on-premises, hybrid, and cloud technologies. The course teaches IT Professionals how to leverage the hybrid capabilities of Azure, how to migrate virtual and physical server workloads to Azure IaaS, and how to secure Azure VMs running Windows Server. The course also teaches IT Professionals how to perform tasks related to high availability, troubleshooting, and disaster recovery. The course highlights administrative tools and technologies including Windows Admin Center, PowerShell, Azure Arc, Azure Automation Update Management, Microsoft Defender for Identity, Azure Security Center, Azure Migrate, and Azure Monitor. Prerequisites An understanding of the following concepts as related to Windows Server technologies: High availability and disaster recovery Automation Monitoring Troubleshooting 1 - Secure Windows Server user accounts Configure user account rights Protect user accounts with the Protected Users group Describe Windows Defender Credential Guard Block NTLM authentication Locate problematic accounts 2 - Hardening Windows Server Describe Local Password Administrator Solution Configure Privileged Access Workstations Secure domain controllers Analyze security configuration with Security Compliance Toolkit Secure SMB traffic 3 - Windows Server update management Explore Windows Update Outline Windows Server Update Services server deployment options Define Windows Server Update Services update management process Describe the process of Update Management 4 - Secure Windows Server DNS Implement split-horizon DNS Create DNS policies Implement DNS policies Secure Windows Server DNS Implement DNSSEC 5 - Implement Windows Server IaaS VM network security Implement network security groups and Windows IaaS VMs Implement adaptive network hardening Implement Azure Firewall and Windows IaaS VMs Implement Windows firewall with Windows Server IaaS VMs Choose the appropriate filtering solution Deploy and configure Azure firewall using the Azure portal Capture network traffic with network watcher Log network traffic to and from a VM using the Azure portal 6 - Audit the security of Windows Server IaaS Virtual Machines Describe Azure Security Center Enable Azure Security Center in hybrid environments Implement and assess security policies Protect your resources with Azure Security Center Implement Azure Sentinel 7 - Manage Azure updates Describe update management Enable update management Deploy updates View update assessments Manage updates for your Azure Virtual Machines 8 - Create and implement application allowlists with adaptive application control Describe adaptive application control Implement adaptive application control policies 9 - Configure BitLocker disk encryption for Windows IaaS Virtual Machines Describe Azure Disk Encryption and server-side encryption Configure Key Vault for Azure Disk Encryption Encrypt Azure IaaS Virtual Machine hard disks Back up and recover data from encrypted disks Create and encrypt a Windows Virtual Machine 10 - Implement change tracking and file integrity monitoring for Windows IaaS VMs Implement Change Tracking and Inventory Manage Change Tracking and Inventory Manage tracked files Implement File Integrity Monitoring Select and monitor entities Use File Integrity Monitoring 11 - Introduction to Cluster Shared Volumes Determine the functionality of Cluster Shared Volumes Explore the architecture and components of Cluster Shared Volumes Implement Cluster Shared Volumes 12 - Implement Windows Server failover clustering Define Windows Server failover clustering Plan Windows Server failover clustering Implement Windows Server failover clustering Manage Windows Server failover clustering Implement stretch clusters Define cluster sets 13 - Implement high availability of Windows Server VMs Select high-availability options for Hyper-V Consider network load balancing for Hyper-V VMs Implement Hyper-V VM live migration Implement Hyper-V VMs storage migration 14 - Implement Windows Server File Server high availability Explore the Windows Server File Server high-availability options Define Cluster Shared Volumes Implement Scale-Out File Server Implement Storage Replica 15 - Implement scale and high availability with Windows Server VM Describe virtual machine scale sets Implement scaling Implement load-balancing VMs Create a virtual machine scale set in the Azure portal Describe Azure Site Recovery Implement Azure Site Recovery 16 - Implement Hyper-V Replica Define Hyper-V Replica Plan for Hyper-V Replica Configure and implement Hyper-V Replica Define extended replication Define Azure Site Recovery Implement Site Recovery from on-premises site to Azure Implement Site Recovery from on-premises site to on-premises site 17 - Protect your on-premises infrastructure from disasters with Azure Site Recovery Azure Site Recovery overview Workloads supported for protection with Azure Site Recovery Run a disaster recovery drill Failover and failback 18 - Implement hybrid backup and recovery with Windows Server IaaS Describe Azure Backup Implement recovery vaults Implement Azure Backup policies Recover Windows IaaS Virtual Machines Perform file and folder recovery Perform backup and restore of on-premises workloads Manage Azure Virtual Machine backups with Azure Backup service 19 - Protect your Azure infrastructure with Azure Site Recovery What is Azure Site Recovery Prepare for disaster recovery with Azure Site Recovery Run a disaster recovery drill Failover and failback using Azure Site Recovery 20 - Protect your virtual machines by using Azure Backup Azure Backup features and scenarios Back up an Azure virtual machine by using Azure Backup Restore virtual machine data 21 - Active Directory Domain Services migration Examine upgrade vs. migration Upgrade a previous version of Active Directory Domain Services to Windows Server 2022 Migrate to Active Directory Domain Services in Windows Server 2022 from a previous version Explore the Active Directory Migration Tool 22 - Migrate file server workloads using Storage Migration Service Storage Migration Service overview and usage scenarios Storage migration requirements Migrate a server with Storage migration Evaluate storage migration considerations 23 - Migrate Windows Server roles Describe the Windows Server Migration Tools Install the Migration Tools Migrate roles using the Migration Tools 24 - Migrate on-premises Windows Server instances to Azure IaaS virtual machines Plan your migration Describe Azure Migrate Perform server assessment Assess physical servers with Azure Migrate Migrate Windows Server workloads by using Azure Migrate 25 - Upgrade and migrate Windows Server IaaS virtual machines Describe Azure Migrate Migrate Windows Server workloads by using Azure Migrate Describe storage migration Migrate file servers by using Storage Migration Service 26 - Containerize and migrate ASP.NET applications to Azure App Service Azure Migrate App Containerization overview 27 - Monitor Windows Server performance Use Performance Monitor to identify performance problems Use Resource Monitor to review current resource usage Review reliability with Reliability Monitor Implement a performance monitoring methodology Use Data Collector Sets to analyze server performance Monitor network infrastructure services Monitor virtual machines running Windows Server Monitor performance with Windows Admin Center Use System Insights to help predict future capacity issues Optimize the performance of Windows Server 28 - Manage and monitor Windows Server event logs Describe Windows Server event logs Use Windows Admin Center to review logs Use Server Manager to review logs Use custom views Implement event log subscriptions 29 - Implement Windows Server auditing and diagnostics Describe basic auditing categories Describe advanced categories Log user access Enable setup and boot event collection 30 - Troubleshoot Active Directory Recover objects from the AD recycle bin Recover the AD DS database Recover SYSVOL Troubleshoot AD DS replication Troubleshoot hybrid authentication issues 31 - Monitor Windows Server IaaS Virtual Machines and hybrid instances Enable Azure Monitor for Virtual Machines Monitor an Azure Virtual Machine with Azure Monitor Enable Azure Monitor in hybrid scenarios Collect data from a Windows computer in a hybrid environment Integrate Azure Monitor with Microsoft Operations Manager 32 - Monitor your Azure virtual machines with Azure Monitor Monitoring for Azure VMs Monitor VM host data Use Metrics Explorer to view detailed host metrics Collect client performance counters by using VM insights Collect VM client event logs 33 - Troubleshoot on-premises and hybrid networking Diagnose DHCP proble

Network fundamentals training course description An intensive hands on IP foundation leading to LINX Accredited Internet Technician stage 1. The course focuses on all parts of TCP/IP including layers 4 to 7 on end stations as well as layer 3 on routers. The TCP/IP protocols are also studied to enable delegates to be able to troubleshoot TCP/IP using Wireshark. Hands on sessions are used to reinforce the theory rather than teach specific manufacturer equipment. A multiple choice exam, leading to the LAIT I certification, is available after the course. The exam consists of 40 questions and lasts 1.5 hours. What will you learn Use ping, traceroute and other tools to diagnose faults on a network. Configure IP on PCs and routers. Plan IP addresses and subnets. Analyse IP and TCP packets using an analyser. Troubleshoot TCP/IP. Network fundamentals training course details Who will benefit: Network engineers. Prerequisites: None Duration 5 days Network fundamentals training course contents What is TCP/IP? TCP and IP are protocols, 7 layer model, network layers, hardware/software layers, internetworking, protocols, What is IP? What is TCP? The internet, The IAB, RFCs. Ping and Wireshark Host configuration, IP addresses, subnet masks, default gateways, ping. Hands on Base configuration. Testing with ping. Analysing packets with Wireshark. Switches and Wireshark Switches versus hubs, layer 2 forwarding table, flooding, broadcasts. Hands on Building a switched based network. Configuring network devices Configuration options, console port, putty, telnet. Hands on Configuring switches, telnet. IP IP packet format, protocol field, TTL, DiffServ, fragments, ICMP. Hands on IP packet analysis. IP addressing 32 bits, dotted decimal, rules, networks, role of subnet masks, simple subnetting, prefix notation. Broadcasts, special use addresses. Hands on Planning and implementing addressing. IP and the lower layers ARP, media not supporting ARP. Hands on ARP. Routing What are routers? What routers do, default gateways, routing and addressing, routing tables, ways to update routing tables. Hands on Building a routed network, traceroute. Routing protocols IGPs and EGPs, RIP, RIPv2, Why not to use RIP, OSPF, OSPF metrics, convergence, distance vector protocols, link state protocols. Hands on OSPF, analysing routing tables, loopbacks. Network simulators Network simulators, EVE-NG, GNS3, CML. Hands on Using EVE-NG. Subnetting Subnetting to the bit level, ranges, how prefixes are used. Hands on Subnetting. VLANS and IP addressing What are VLANs, tagging, 802.1Q, Inter VLAN routing. Hands on Inter VLAN routing. TCP and UDP Layer 4, port numbers, client ports, broadcasts multicasts and layer 4, UDP header, TCP header, connections, ACK, sliding windows, options, connection states. Sockets. Hands on Analysing TCP packets. IPv4 address configuration Private addresses, NAT, NAPT, dynamic addressing, DHCP, link local addresses. Hands on DHCP, NAT. IPv6 What is IPv6, 128 bit addresses, address formats, IPv6 address allocation, header format, migration, dual stack, tunnelling, NAT64, DNS64. Hands on IPv6 setup troubleshooting. IPv6 address configuration Static addressing, EUI-64 addresses, IPv6 address order, SLAAC, DHCPv6. Hands on SLAAC. Applications Clients, servers, HTTP, Email, resource sharing, VoIP, video, terminal emulation, remote desktop. Network management and SNMP. Hands on Servers, TFTP, VoIP packet analysis. DNS Names and addresses, hosts file, how DNS works. FQDNs, DNS client configuration. Hands on Troubleshooting DNS. Security Firewalls, firewall architectures, DMZ, how firewalls work, proxy servers, filtering, ACLs, IDS, VPNs, authentication, encryption, tunnels, secure protocols. Hands on Firewalls, SSH Troubleshooting Methods, tools. Using the 7 layer model. Troubleshooting toolkits. Hands on Fixing the network.

LINX 1 training course description An intensive hands on IP foundation leading to LINX Accredited Internet Technician stage 1. The course focuses on all parts of TCP/IP including layers 4 to 7 on end stations as well as layer 3 on routers. The TCP/IP protocols are also studied to enable delegates to be able to troubleshoot TCP/IP using Wireshark. Hands on sessions are used to reinforce the theory rather than teach specific manufacturer equipment. A multiple choice exam, leading to the LAIT I certification, is available after the course. The exam consists of 40 questions and lasts 1.5 hours. What will you learn Use ping, traceroute and other tools to diagnose faults on a network. Configure IP on PCs and routers. Plan IP addresses and subnets. Analyse IP and TCP packets using an analyser. Troubleshoot TCP/IP. LINX 1 training course details Who will benefit: Network engineers. Prerequisites: None. Duration 5 days LINX 1 training course contents What is TCP/IP? TCP and IP are protocols, 7 layer model, network layers, hardware/software layers, internetworking, protocols, What is IP? What is TCP? The internet, The IAB, RFCs. Ping and Wireshark Host configuration, IP addresses, subnet masks, default gateways, ping. Hands on Base configuration. Testing with ping. Analysing packets with Wireshark. Switches and Wireshark Switches versus hubs, layer 2 forwarding table, flooding, broadcasts. Hands on Building a switched based network. Configuring network devices Configuration options, console port, putty, telnet. Hands on Configuring switches, telnet. IP IP packet format, protocol field, TTL, DiffServ, fragments, ICMP. Hands on IP packet analysis. IP addressing 32 bits, dotted decimal, rules, networks, role of subnet masks, simple subnetting, prefix notation. Broadcasts, special use addresses. Hands on Planning and implementing addressing. IP and the lower layers ARP, media not supporting ARP. Hands on ARP. Routing What are routers? What routers do, default gateways, routing and addressing, routing tables, ways to update routing tables. Hands on Building a routed network, traceroute. Routing protocols IGPs and EGPs, RIP, RIPv2, Why not to use RIP, OSPF, OSPF metrics, convergence, distance vector protocols, link state protocols. Hands on OSPF, analysing routing tables, loopbacks. Network simulators Network simulators, EVE-NG, GNS3, CML. Hands on Using EVE-NG. Subnetting Subnetting to the bit level, ranges, how prefixes are used. Hands on Subnetting. VLANS and IP addressing What are VLANs, tagging, 802.1Q, Inter VLAN routing. Hands on Inter VLAN routing. TCP and UDP Layer 4, port numbers, client ports, broadcasts multicasts and layer 4, UDP header, TCP header, connections, ACK, sliding windows, options, connection states. Sockets. Hands on Analysing TCP packets. IPv4 address configuration Private addresses, NAT, NAPT, dynamic addressing, DHCP, link local addresses. Hands on DHCP, NAT. IPv6 What is IPv6, 128 bit addresses, address formats, IPv6 address allocation, header format, migration, dual stack, tunnelling, NAT64, DNS64. Hands on IPv6 setup troubleshooting. IPv6 address configuration Static addressing, EUI-64 addresses, IPv6 address order, SLAAC, DHCPv6. Hands on SLAAC. Applications Clients, servers, HTTP, Email, resource sharing, VoIP, video, terminal emulation, remote desktop. Network management and SNMP. Hands on Servers, TFTP, VoIP packet analysis. DNS Names and addresses, hosts file, how DNS works. FQDNs, DNS client configuration. Hands on Troubleshooting DNS. Security Firewalls, firewall architectures, DMZ, how firewalls work, proxy servers, filtering, ACLs, IDS, VPNs, authentication, encryption, tunnels, secure protocols. Hands on Firewalls, SSH Troubleshooting Methods, tools. Using the 7 layer model. Troubleshooting toolkits. Hands on Fixing the network.

TCP/IP training course description An intensive hands on IP foundation leading to LINX Accredited Internet Technician stage 1. The course focuses on all parts of TCP/IP including layers 4 to 7 on end stations as well as layer 3 on routers. The TCP/IP protocols are also studied to enable delegates to be able to troubleshoot TCP/IP using Wireshark. Hands on sessions are used to reinforce the theory rather than teach specific manufacturer equipment. A multiple choice exam, leading to the LAIT I certification, is available after the course. The exam consists of 40 questions and lasts 1.5 hours. What will you learn Use ping, traceroute and other tools to diagnose faults on a network. Configure IP on PCs and routers. Plan IP addresses and subnets. Analyse IP and TCP packets using an analyser. Troubleshoot TCP/IP. TCP/IP training course details Who will benefit: Network engineers. Prerequisites: None Duration 5 days TCP/IP training course contents What is TCP/IP? TCP and IP are protocols, 7 layer model, network layers, hardware/software layers, internetworking, protocols, What is IP? What is TCP? The internet, The IAB, RFCs. Ping and Wireshark Host configuration, IP addresses, subnet masks, default gateways, ping. Hands on Base configuration. Testing with ping. Analysing packets with Wireshark. Switches and Wireshark Switches versus hubs, layer 2 forwarding table, flooding, broadcasts. Hands on Building a switched based network. Configuring network devices Configuration options, console port, putty, telnet. Hands on Configuring switches, telnet. IP IP packet format, protocol field, TTL, DiffServ, fragments, ICMP. Hands on IP packet analysis. IP addressing 32 bits, dotted decimal, rules, networks, role of subnet masks, simple subnetting, prefix notation. Broadcasts, special use addresses. Hands on Planning and implementing addressing. IP and the lower layers ARP, media not supporting ARP. Hands on ARP. Routing What are routers? What routers do, default gateways, routing and addressing, routing tables, ways to update routing tables. Hands on Building a routed network, traceroute. Routing protocols IGPs and EGPs, RIP, RIPv2, Why not to use RIP, OSPF, OSPF metrics, convergence, distance vector protocols, link state protocols. Hands on OSPF, analysing routing tables, loopbacks. Network simulators Network simulators, EVE-NG, GNS3, CML. Hands on Using EVE-NG. Subnetting Subnetting to the bit level, ranges, how prefixes are used. Hands on Subnetting. VLANS and IP addressing What are VLANs, tagging, 802.1Q, Inter VLAN routing. Hands on Inter VLAN routing. TCP and UDP Layer 4, port numbers, client ports, broadcasts multicasts and layer 4, UDP header, TCP header, connections, ACK, sliding windows, options, connection states. Sockets. Hands on Analysing TCP packets. IPv4 address configuration Private addresses, NAT, NAPT, dynamic addressing, DHCP, link local addresses. Hands on DHCP, NAT. IPv6 What is IPv6, 128 bit addresses, address formats, IPv6 address allocation, header format, migration, dual stack, tunnelling, NAT64, DNS64. Hands on IPv6 setup troubleshooting. IPv6 address configuration Static addressing, EUI-64 addresses, IPv6 address order, SLAAC, DHCPv6. Hands on SLAAC. Applications Clients, servers, HTTP, Email, resource sharing, VoIP, video, terminal emulation, remote desktop. Network management and SNMP. Hands on Servers, TFTP, VoIP packet analysis. DNS Names and addresses, hosts file, how DNS works. FQDNs, DNS client configuration. Hands on Troubleshooting DNS. Security Firewalls, firewall architectures, DMZ, how firewalls work, proxy servers, filtering, ACLs, IDS, VPNs, authentication, encryption, tunnels, secure protocols. Hands on Firewalls, SSH Troubleshooting Methods, tools. Using the 7 layer model. Troubleshooting toolkits. Hands on Fixing the network.

Search By Location
- host Courses in London
- host Courses in Birmingham
- host Courses in Glasgow
- host Courses in Liverpool
- host Courses in Bristol
- host Courses in Manchester
- host Courses in Sheffield
- host Courses in Leeds
- host Courses in Edinburgh
- host Courses in Leicester
- host Courses in Coventry
- host Courses in Bradford
- host Courses in Cardiff
- host Courses in Belfast
- host Courses in Nottingham
