- Professional Development
- Medicine & Nursing
- Arts & Crafts
- Health & Wellbeing
- Personal Development
20596 Courses
Communication Skills 1 Day Training in Hamilton, UK
By Mangates
Communication Skills 1 Day Training in Hamilton, UK

Communication Skills 1 Day Training in Norwich
By Mangates
Communication Skills 1 Day Training in Norwich

Learn to craft top-notch videos for your business using your mobile phone in this interactive workshop. Enhance marketing, visibility, and attract more clients through video. All-in-one workshop for diving into the world of business videos. #VideoCreation #BusinessBoost

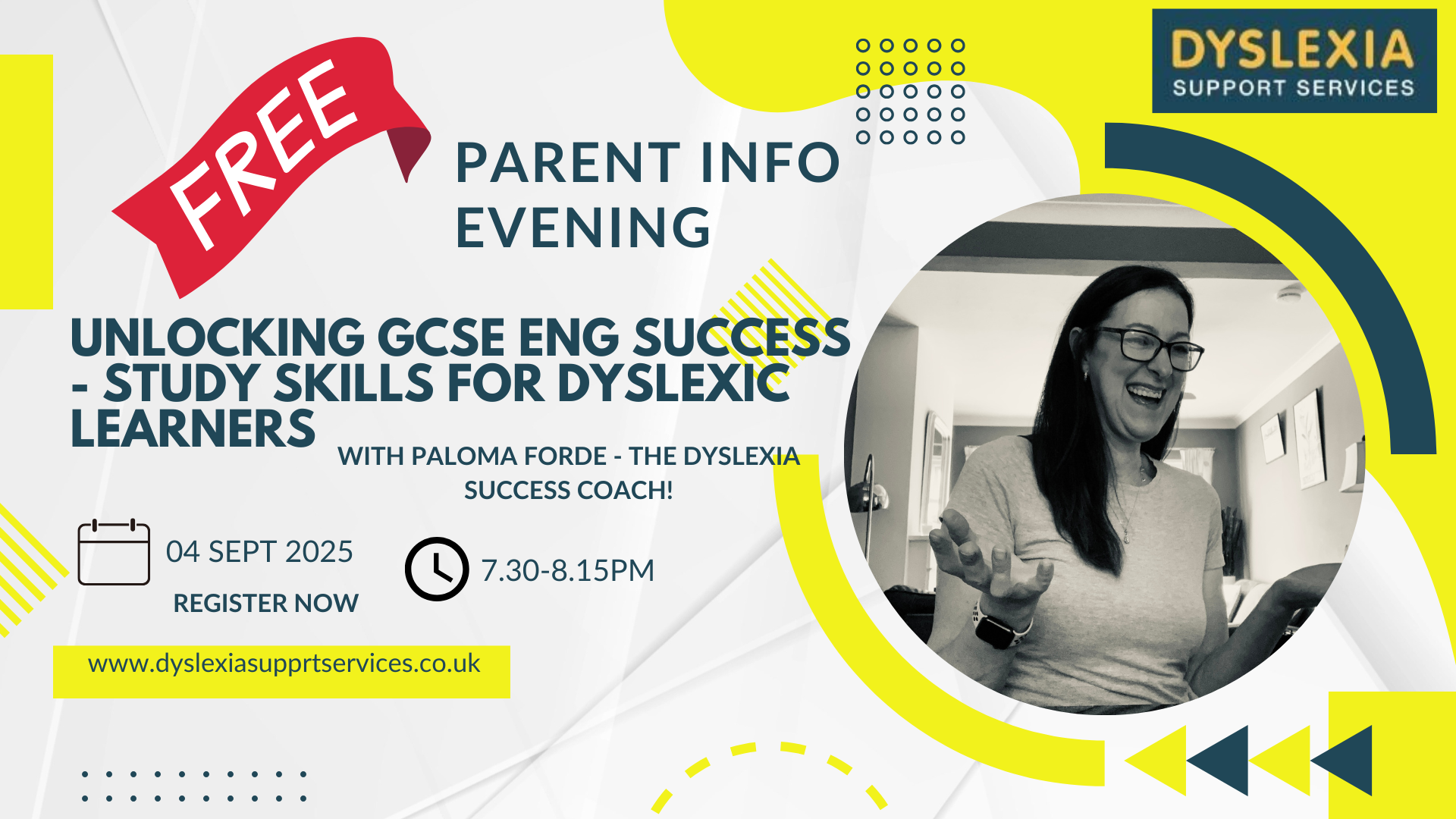
FREE! Unlocking English GCSE Success through Study Skills - Parents information Evening
5.0(113)By Dyslexia Support Services
Unlocking English GCSE Success for Dyslexic and neurodivergent learners FREE Parents information Evening 4th September at 7:30pm (UK time) | Hosted by Paloma Forde, Dyslexia & Neurodiversity Specialist Welcome to my Information Evening Being held Sept 4th at 7.30pm This event is specifically for parents with teens either Year 10 or 11 who are studying English Lit and Eng Lang GCSE who want to understand how my structured, targeted study skills can make all the difference and help their teen to unlock their full potential. In this free info session, I’ll be sharing exactly how I support dyslexic and neurodivergent teens through the challenges of GCSE English Language & Literature with a proven, structured Study Skills Programme. This event is for you if your teen: ✅ Is going into Year 10 or 11 ✅ Struggles to revise or stay organised ✅ Finds the GCSE English syllabus overwhelming ✅ Has tried traditional tutoring but still feels “behind” ✅ Needs strategies tailored to a neurodivergent brain In this free parents info session, I’ll be covering: Why traditional revision doesn’t work for many dyslexic learners Exactly what happens in our weekly study skills sessions How they’re specifically structured for dyslexic and neurodivergent learners How we use visualisation, structure and memory strategies to make content stick How I help students go from confused to confident An explanation of the 2 classroom levels which will be offered (Which you can access from as little as £20 per session) Plus you’ll get a sneak peek at all the resources included in my Google Classroom hub These sessions aren't English lessons. They're a game-changing support system for teens who learn differently - but deserve to thrive just the same. Click the BOOKING form to secure your place for the Parent Info Evening on 4th Sept at 7.30pm. This is for parents of students going into Year 10 or 11, who are struggling with GCSE English - or who just need a better, more structured way to revise that actually works for them. I know you want the best for your child. You don’t have to watch them fall behind. There is another way - and I can’t wait to show it to you. Join me live on Thursday 4th Sept at 7.30pm! Spots are limited so I can keep the session personal and interactive — don’t wait to sign up. Ps - By signing up your email will automatically be added to my mailing list. You can unsubscribe anytime. xx
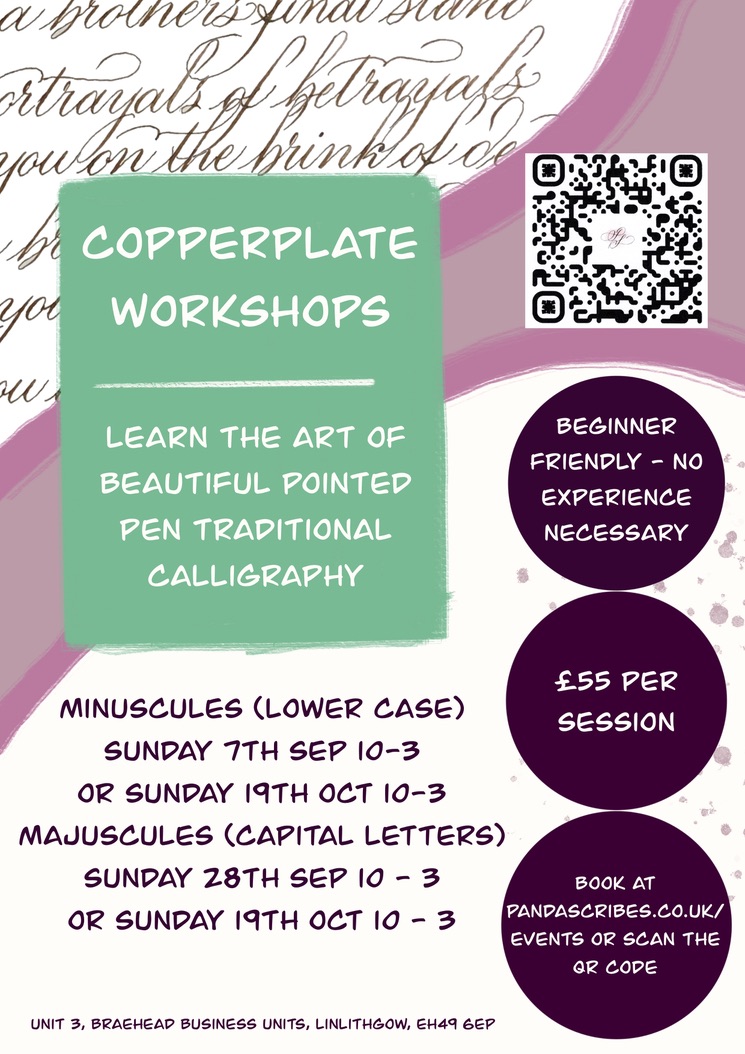
Copperplate Masterclass (Minuscules)
By Panda Scribes
Discover the beauty and rhythm of Copperplate script in this focused 4-hour workshop dedicated to minuscules (lowercase letters). Whether you're a complete beginner or looking to refine your foundational skills, this session will guide you through the elegant shapes, basic strokes, and consistent spacing that form the heart of traditional pointed pen calligraphy. This workshop pairs perfectly with the Copperplate Majuscules session, which runs separately in the same format. If you'd like to continue your Copperplate journey, a separate Majuscules session is also available to book.
Conflict Management 1 Day Training in Bath
By Mangates
Conflict Management 1 Day Training in Bath

Conflict Management 1 Day Training in Chichester
By Mangates
Conflict Management 1 Day Training in Chichester

Conflict Management 1 Day Training in London
By Mangates
Conflict Management 1 Day Training in London

Conflict Management 1 Day Training in Warrington
By Mangates
Conflict Management 1 Day Training in Warrington

Conflict Management 1 Day Training in Middlesbrough
By Mangates
Conflict Management 1 Day Training in Middlesbrough

Search By Location
- form Courses in London
- form Courses in Birmingham
- form Courses in Glasgow
- form Courses in Liverpool
- form Courses in Bristol
- form Courses in Manchester
- form Courses in Sheffield
- form Courses in Leeds
- form Courses in Edinburgh
- form Courses in Leicester
- form Courses in Coventry
- form Courses in Bradford
- form Courses in Cardiff
- form Courses in Belfast
- form Courses in Nottingham